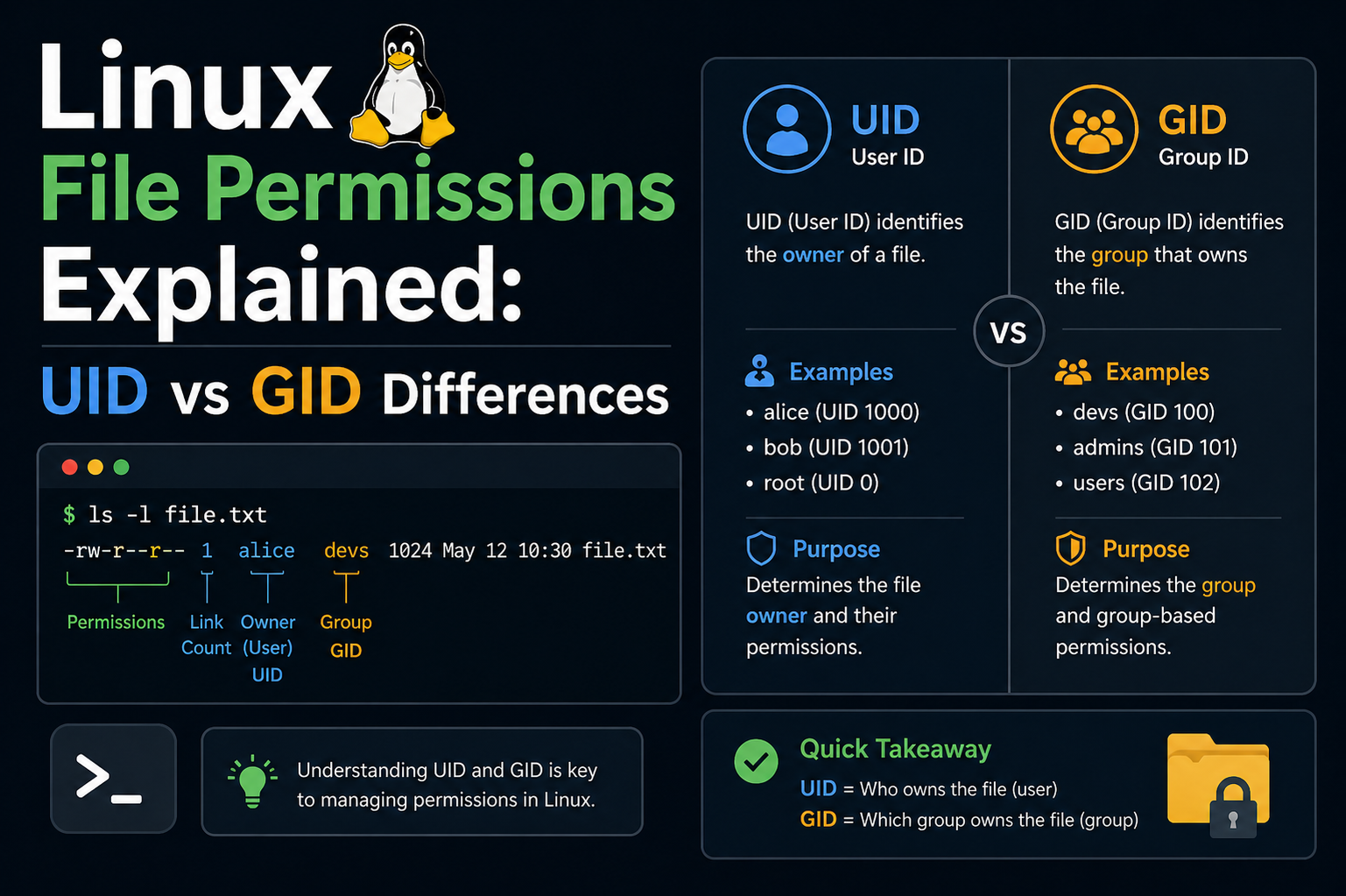
In Linux operating systems, every interaction between users, files, and processes is governed by a structured identity system. This system is built on two fundamental […]
post
Is It Worth Listing Microsoft Office on Your Resume?
There was a time when listing proficiency in Microsoft Office on a resume instantly made a candidate appear more capable and prepared than others. Knowing […]
43 Verified Help Desk Technician Salaries You Should Know
If you are considering a role as a help desk technician or are already working in one, salary expectations are likely one of your top […]
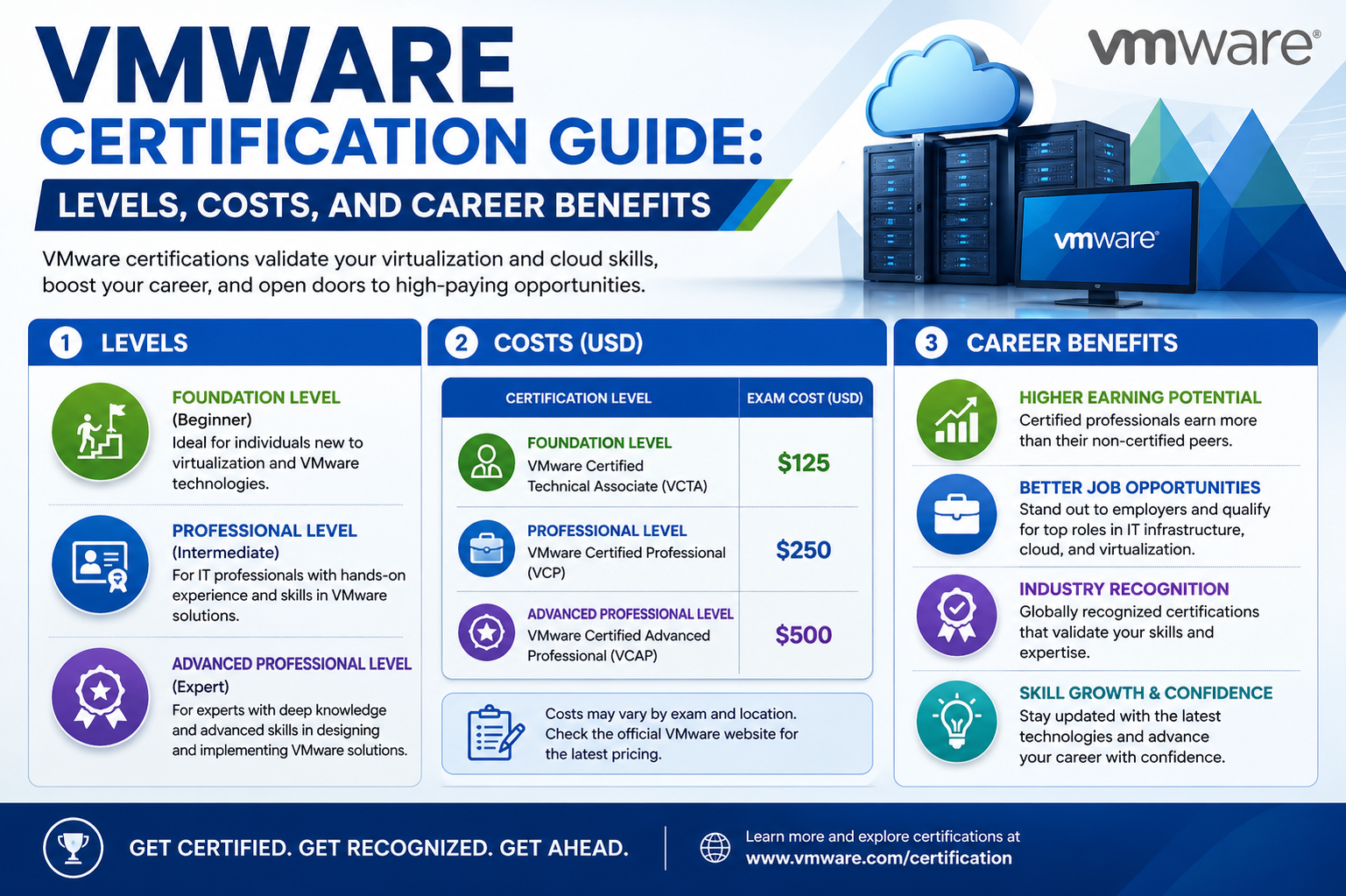
VMware Certification Guide: Levels, Costs, and Career Benefits
VMware has established itself as a global leader in virtualization and cloud infrastructure technologies, playing a critical role in modern IT environments. Organizations across industries […]
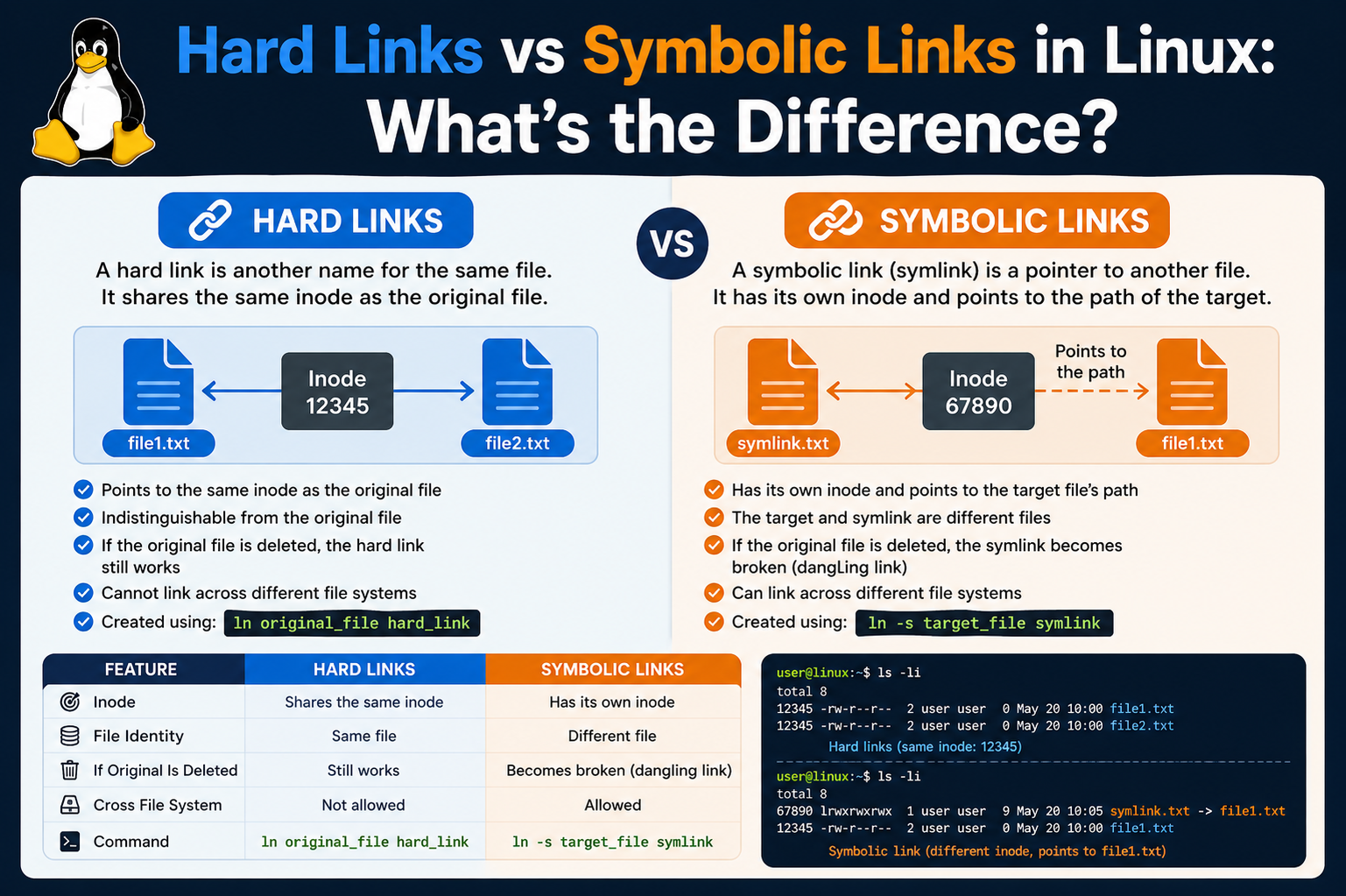
Hard Links vs Symbolic Links in Linux: What’s the Difference?
When working within a Linux environment, one of the most important concepts to grasp is how the system organizes and references files. Unlike some operating […]
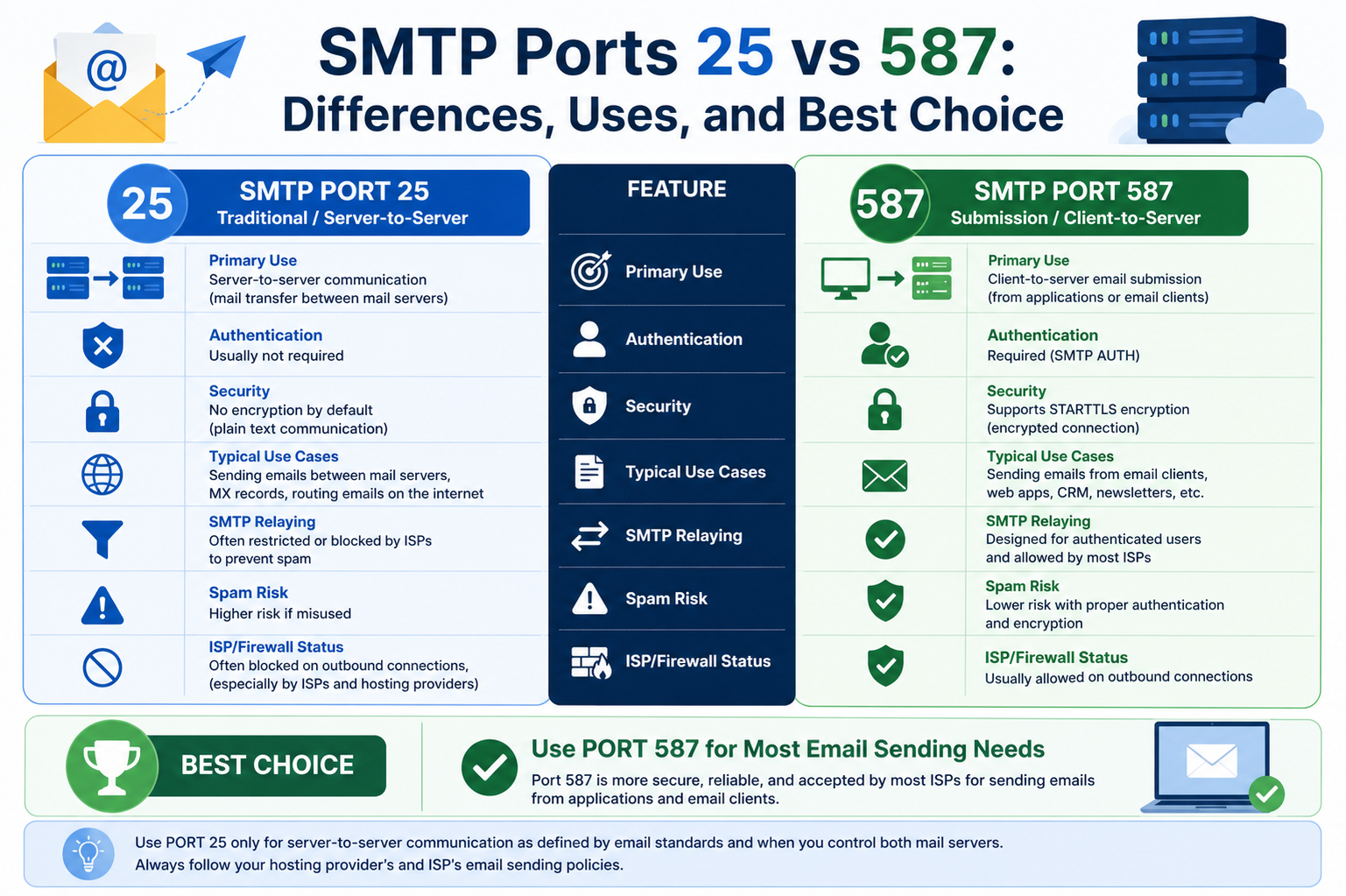
SMTP Ports 25 vs 587: Differences, Uses, and Best Choice
When discussing email delivery on the internet, the concept of ports becomes unavoidable. Ports act as logical channels that allow different types of network traffic […]
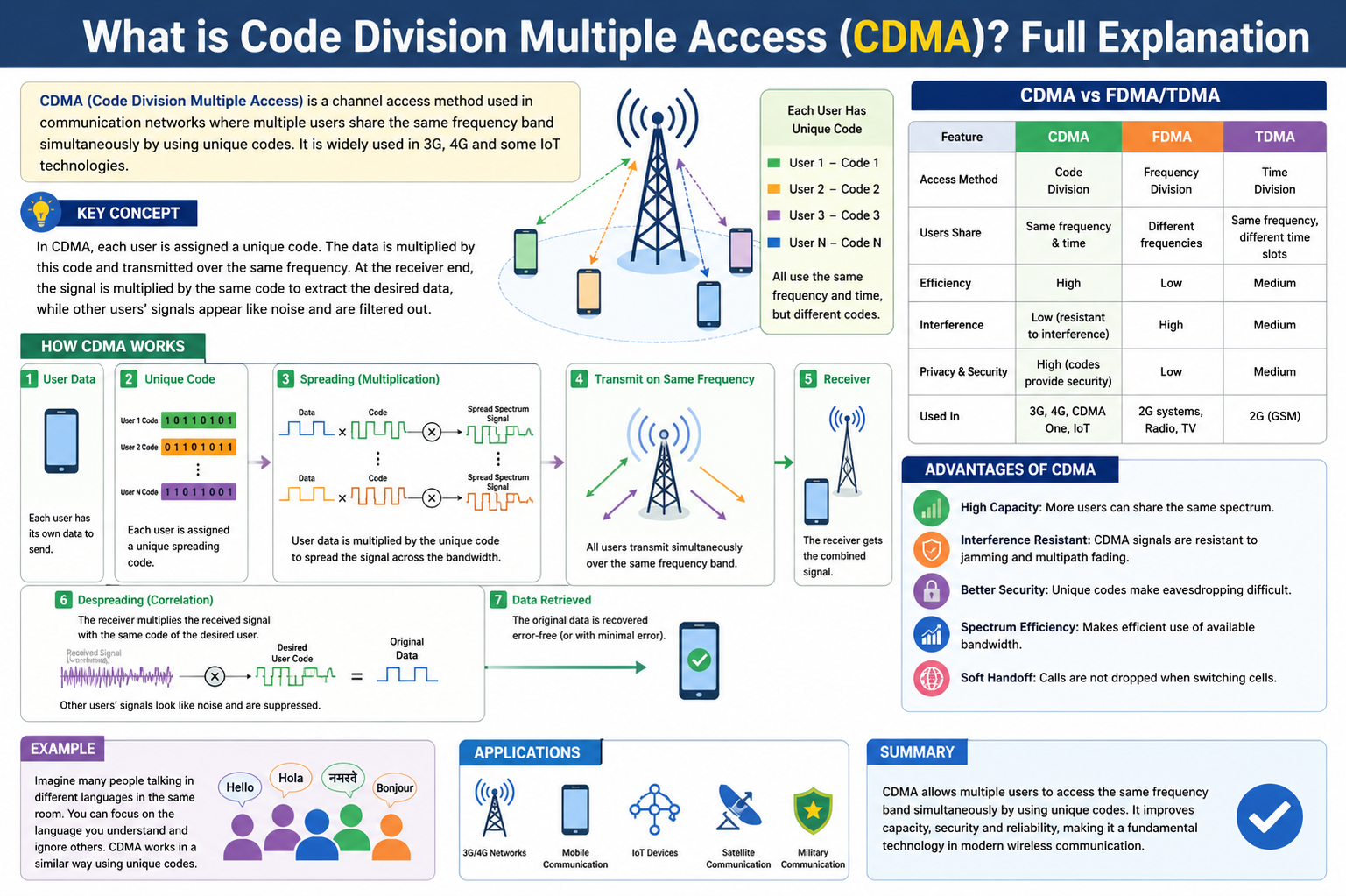
What is Code Division Multiple Access (CDMA)? Full Explanation
Code-Division Multiple Access, commonly referred to as CDMA, is a wireless communication technology that allows multiple users to share the same frequency spectrum at the […]
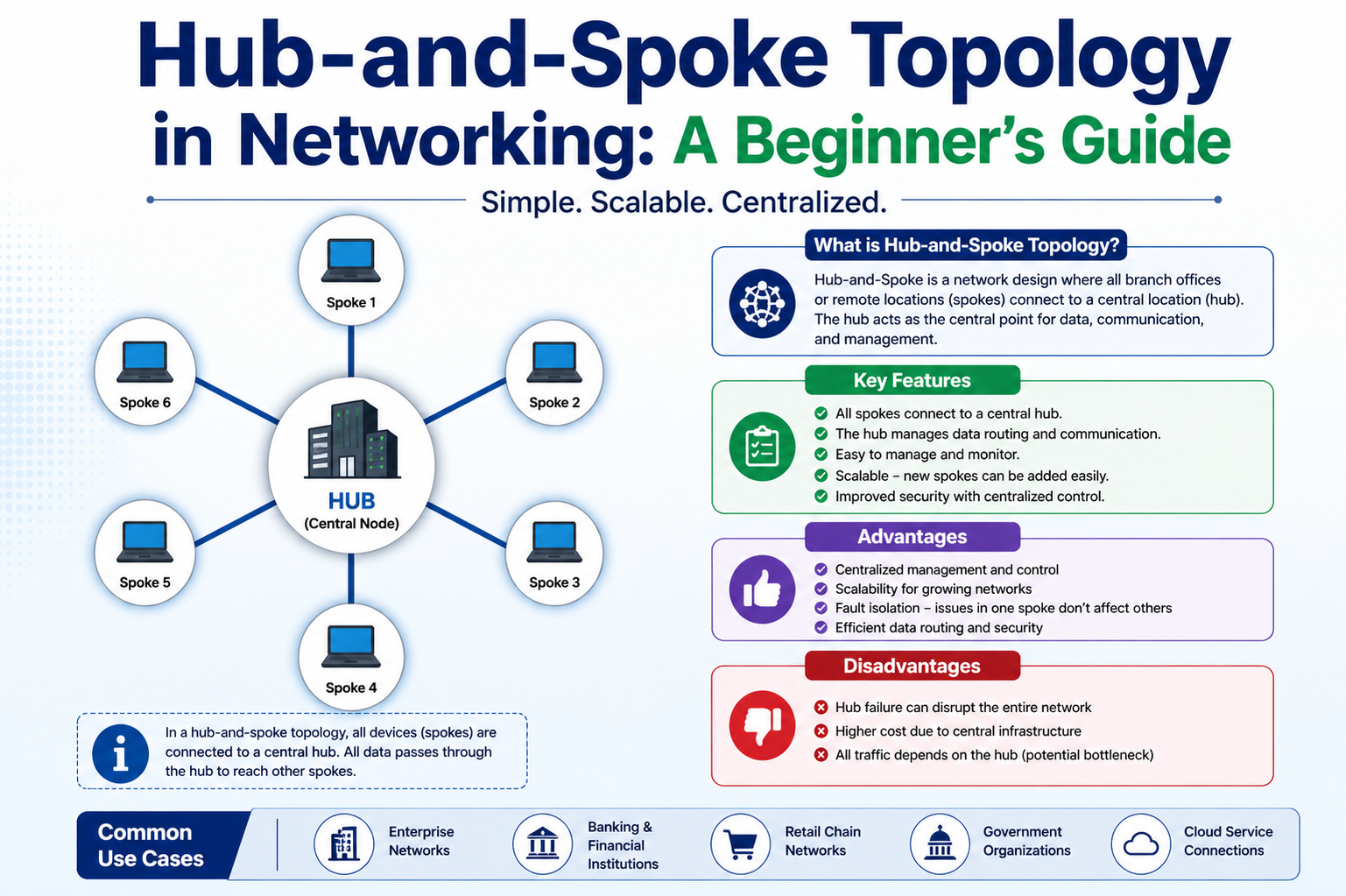
Hub-and-Spoke Topology in Networking: A Beginner’s Guide
Hub and spoke topology is a network design model in which all devices, also known as nodes, are connected to a single central device called […]
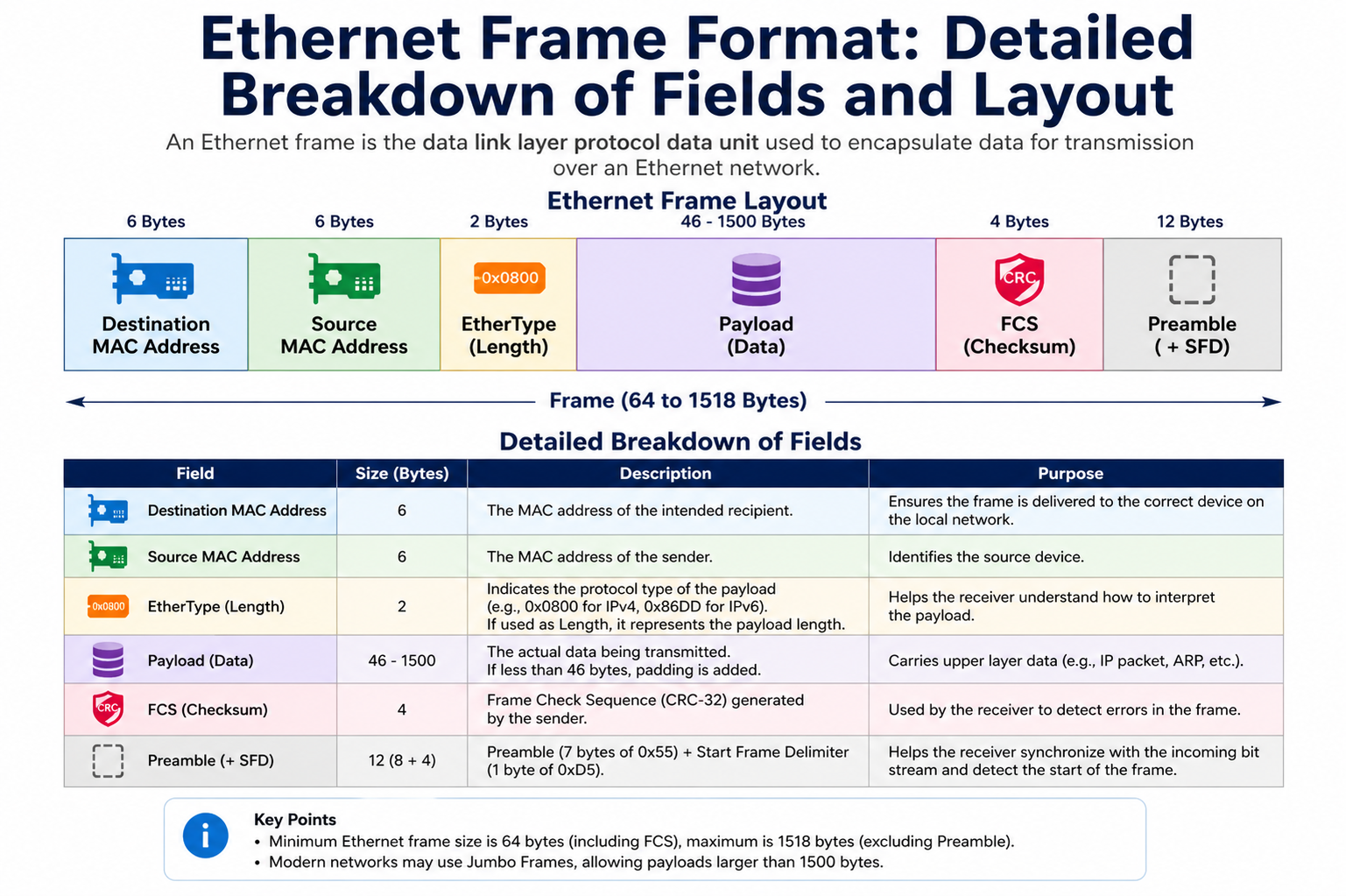
Ethernet Frame Format: Detailed Breakdown of Fields and Layout
Ethernet frame format refers to the standardized structure used to package and transmit data across Ethernet-based networks. This structure ensures that all devices participating in […]
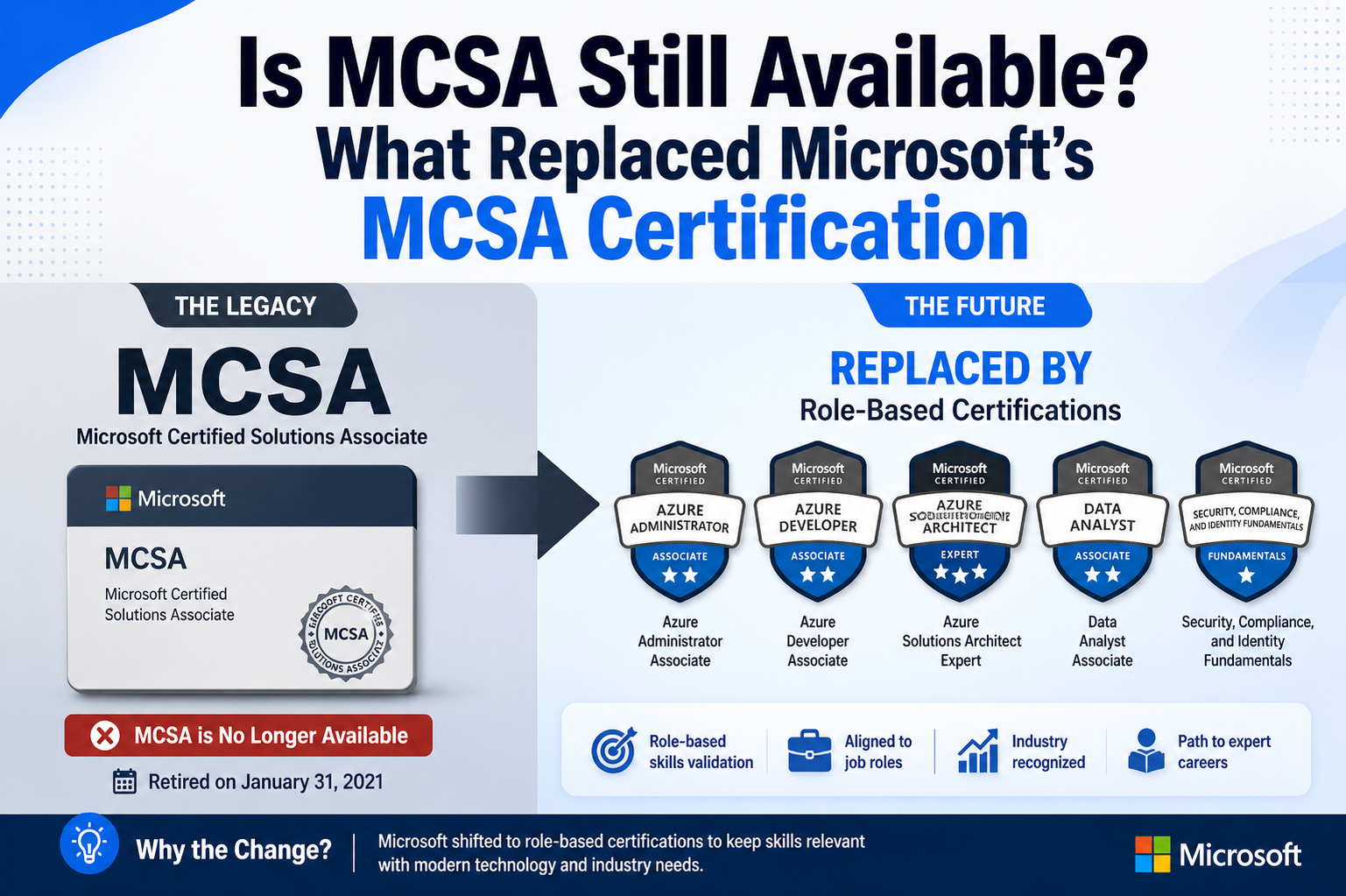
Is MCSA Still Available? What Replaced Microsoft’s MCSA Certification
Microsoft has long been one of the most influential technology companies in the world, shaping how businesses operate and how IT professionals build their careers. […]
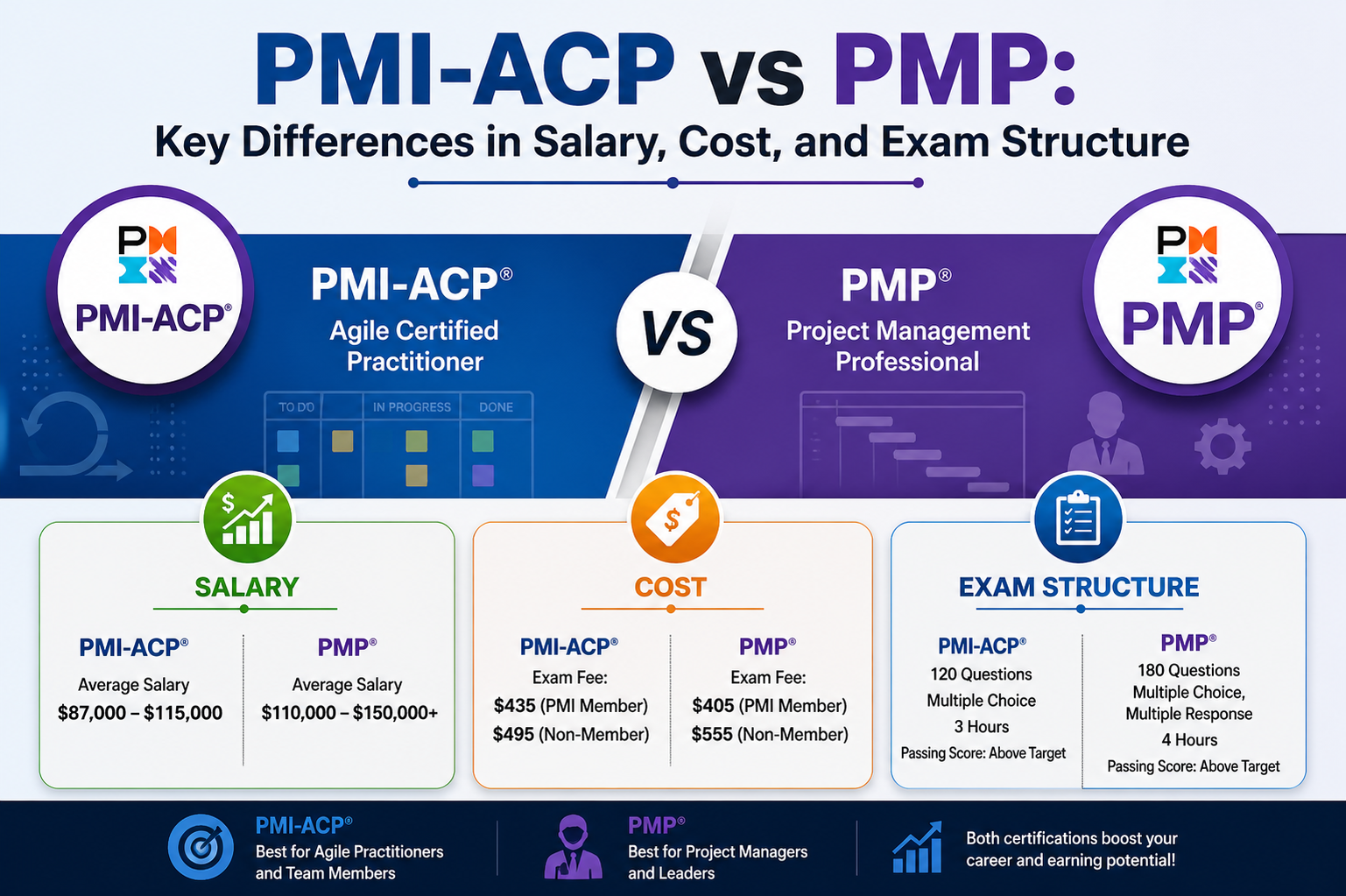
PMI-ACP vs PMP: Key Differences in Salary, Cost, and Exam Structure
Project management has evolved into a highly strategic discipline, shaping how organizations deliver value, manage resources, and achieve business objectives. Among the most recognized certifications […]
What Is COBOL Programming? Industries That Still Rely on It
COBOL, short for Common Business-Oriented Language, is one of the oldest high-level programming languages still in active use today. Created in 1959 during an era […]
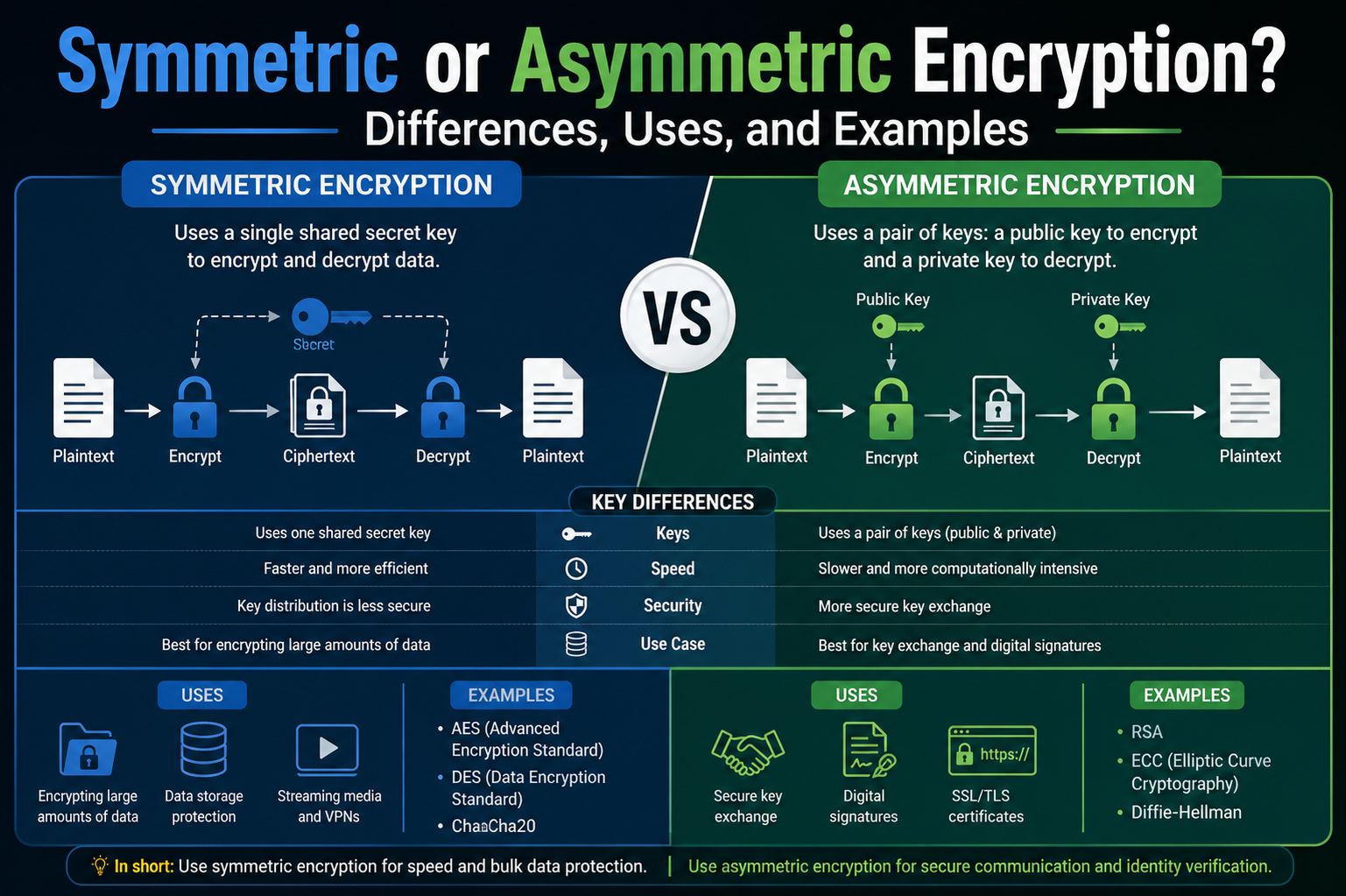
Symmetric or Asymmetric Encryption? Differences, Uses, and Examples
Encryption plays a central role in protecting digital information, whether it’s personal messages, financial transactions, or sensitive business data. At its core, encryption transforms readable […]
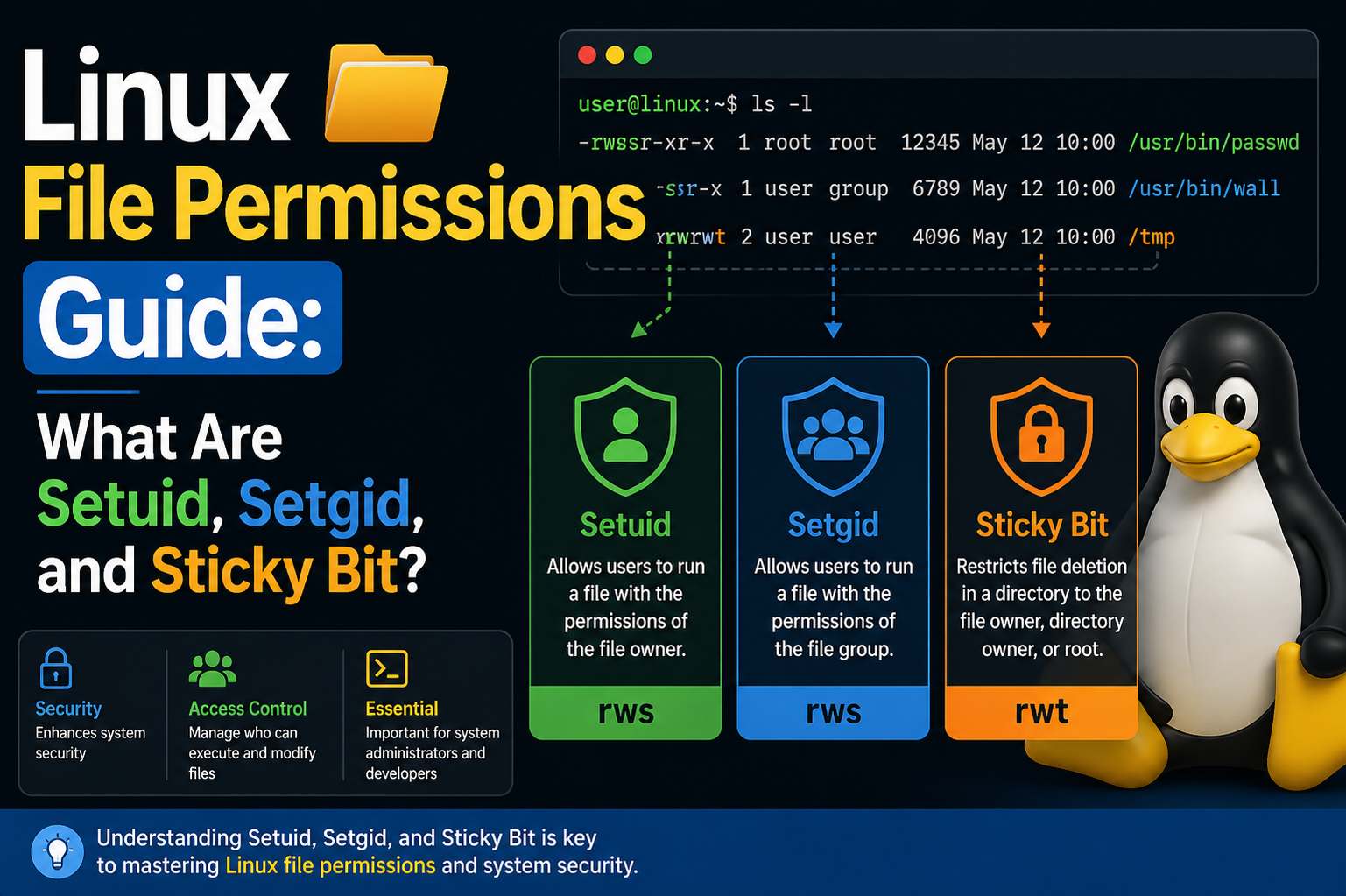
Linux File Permissions Guide: What Are Setuid, Setgid, and Sticky Bit?
Linux file permissions form the backbone of system security and access control, shaping how users interact with files and directories across a system. Among these […]
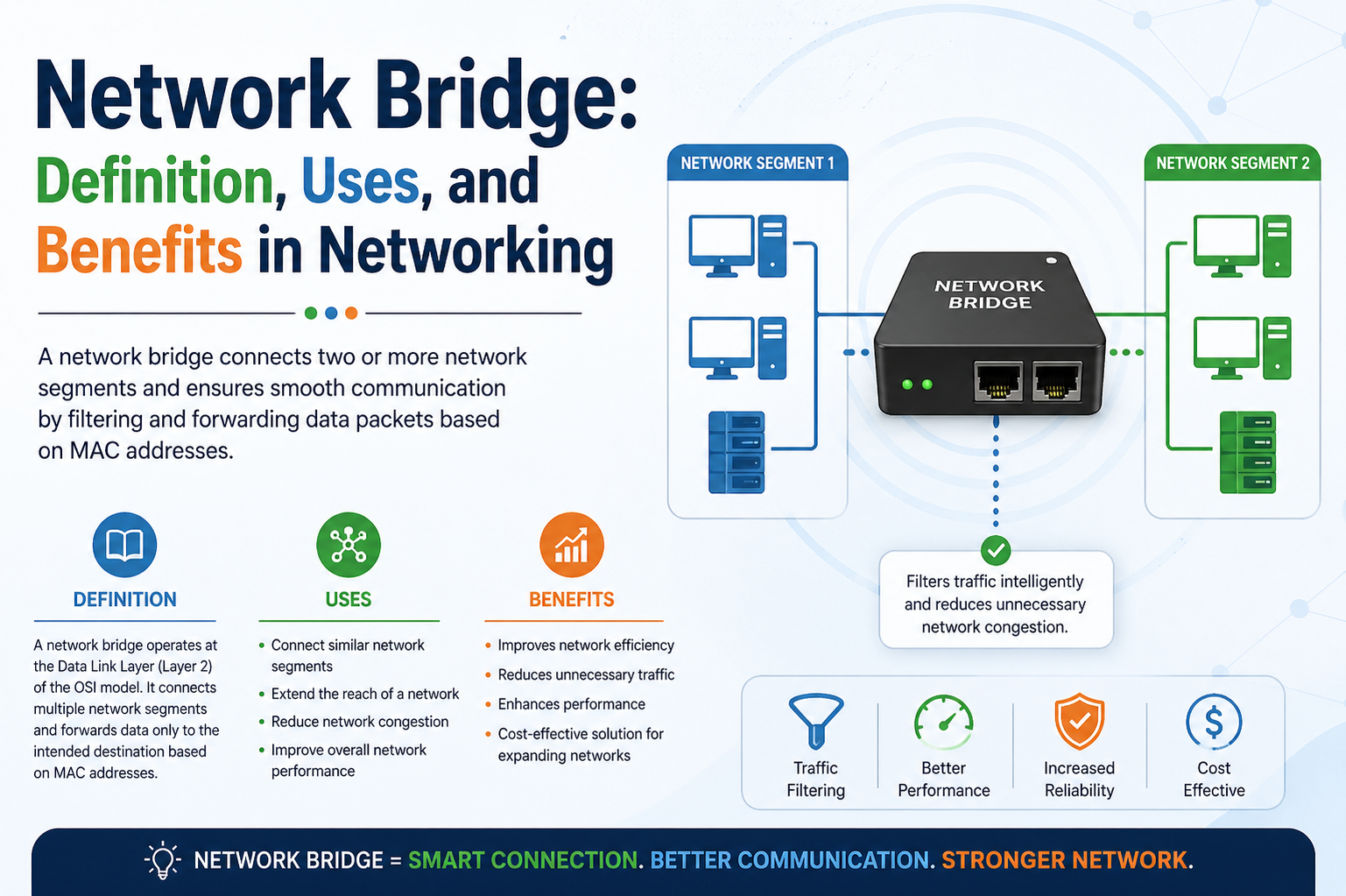
Network Bridge: Definition, Uses, and Benefits in Networking
A network bridge is a fundamental networking device designed to connect multiple segments of a local area network while intelligently managing the flow of data […]