Encryption plays a central role in protecting digital information, whether it’s personal messages, financial transactions, or sensitive business data. At its core, encryption transforms readable information into an unreadable format so that only authorized parties can access it. Among the many encryption techniques available today, two primary approaches stand out: symmetric encryption and asymmetric encryption. Each method has its own strengths, limitations, and ideal use cases. Understanding how they differ is essential for making informed decisions about data security in any environment.
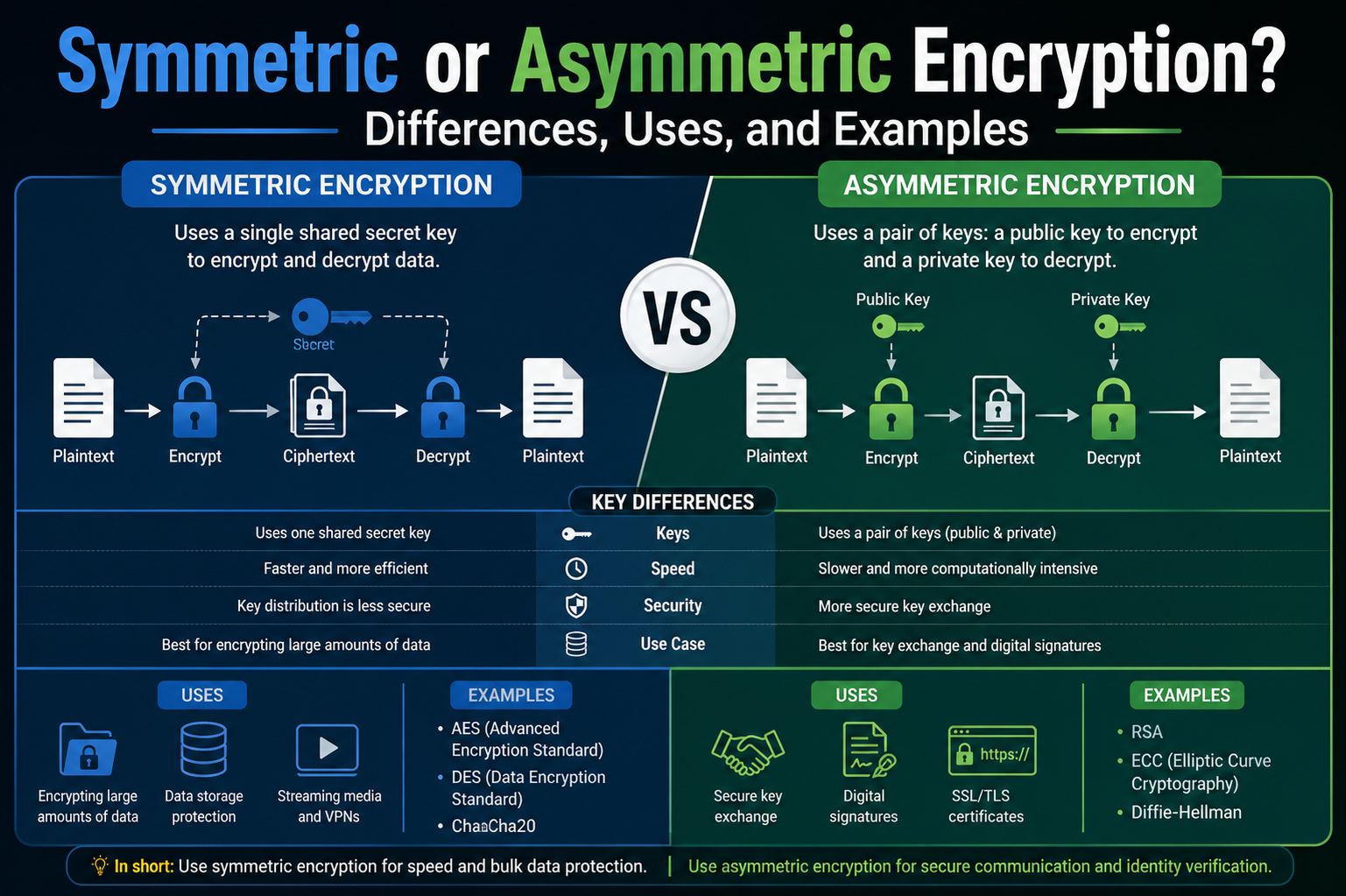
Symmetric encryption relies on a single shared key, which is used for both encrypting and decrypting data. This means that the same key must be securely distributed to all parties involved in the communication. On the other hand, asymmetric encryption uses a pair of keys—one public and one private. The public key can be shared openly, while the private key remains confidential. Data encrypted with one key can only be decrypted with the other, creating a more flexible and secure system for certain applications.
While both methods serve the same purpose of protecting information, they approach the problem from different angles. Symmetric encryption prioritizes speed and efficiency, making it ideal for handling large volumes of data. Asymmetric encryption, although slower, provides enhanced security features such as secure key exchange and identity verification. These differences shape how each method is used in real-world scenarios and why they are often combined rather than used independently.
Why Encryption Matters in Modern Digital Systems
In today’s interconnected world, data is constantly being transmitted across networks, stored in databases, and processed by applications. Without proper protection, this data is vulnerable to interception, theft, and misuse. Encryption acts as a safeguard, ensuring that even if data is accessed by unauthorized parties, it remains unreadable and useless to them.
The importance of encryption extends across various industries. Financial institutions rely on it to secure transactions and protect customer information. Healthcare systems use encryption to maintain patient confidentiality. Businesses depend on it to protect intellectual property and sensitive communications. Even everyday activities such as sending messages or browsing websites involve encryption working behind the scenes.
As cyber threats continue to evolve, the need for strong encryption becomes even more critical. Attackers are constantly developing new methods to exploit vulnerabilities, making it essential to use encryption techniques that are both robust and appropriate for the task at hand. Choosing between symmetric and asymmetric encryption is not just a technical decision—it directly impacts the security and performance of systems.
The Simplicity of Symmetric Encryption Explained
Symmetric encryption is often described as straightforward because it uses a single key for both encryption and decryption. This simplicity makes it easy to implement and highly efficient in terms of processing speed. When two parties want to communicate securely using symmetric encryption, they must first agree on a shared key. Once this key is established, it can be used to encrypt messages before sending them and decrypt them upon receipt.
The process itself is relatively simple. A piece of plaintext data is passed through an encryption algorithm along with the secret key, producing ciphertext. This ciphertext appears as random data and cannot be understood without the key. When the recipient receives the ciphertext, they use the same key with the decryption algorithm to convert it back into its original form.
This approach works exceptionally well in environments where secure key distribution is not a major concern. For example, systems within a controlled network can share keys securely during setup and then use symmetric encryption for fast and efficient communication. The simplicity of the method also reduces the likelihood of errors during implementation, which can be a significant advantage in maintaining security.
Common Symmetric Encryption Algorithms and Their Role
Several well-established algorithms are used in symmetric encryption, each designed to provide a balance between security and performance. These algorithms have been tested extensively and are widely trusted for protecting sensitive data.
One of the most widely used symmetric algorithms is Advanced Encryption Standard (AES). It is known for its strong security and efficiency, making it suitable for a wide range of applications. AES is commonly used in securing data at rest, such as files stored on a device, as well as data in transit, such as information sent over networks. Its ability to handle large amounts of data بسرعة makes it a preferred choice for modern systems.
Another algorithm, Triple Data Encryption Standard (3DES), was once widely used but is now considered outdated. While it provided improved security over its predecessor, it is slower and less efficient compared to newer algorithms. As a result, many systems are gradually phasing it out in favor of more advanced options.
ChaCha20 is a newer addition to the family of symmetric algorithms. It is designed to perform efficiently on devices with limited processing power, such as smartphones and embedded systems. Its ability to deliver strong security without consuming excessive resources makes it particularly useful in mobile and IoT environments.
These algorithms demonstrate how symmetric encryption continues to evolve, adapting to the changing demands of technology while maintaining its core advantage of speed.
Performance Advantages of Symmetric Encryption
One of the most significant benefits of symmetric encryption is its speed. Because it uses a single key and relatively simple mathematical operations, it can process data much faster than asymmetric encryption. This performance advantage becomes especially important when dealing with large volumes of data or real-time applications.
In practical terms, symmetric encryption can handle massive amounts of information in a very short time. Whether it’s encrypting entire databases, securing video streams, or processing financial transactions, the efficiency of symmetric encryption ensures that operations run smoothly without noticeable delays.
This speed is not just a convenience—it is often a necessity. In applications such as online banking or streaming services, even minor delays can impact user experience. Symmetric encryption allows these systems to maintain high performance while still providing strong security.
Another factor contributing to its efficiency is the availability of hardware acceleration. Many modern processors include built-in support for symmetric encryption algorithms, allowing them to execute encryption tasks even faster. This integration further enhances the performance benefits and makes symmetric encryption a practical choice for a wide range of applications.
The Challenge of Key Distribution in Symmetric Encryption
Despite its advantages, symmetric encryption has a significant challenge: securely sharing the key. Since the same key is used for both encryption and decryption, it must be transmitted to all parties involved without being intercepted by unauthorized individuals. This is known as the key distribution problem.
If the key is compromised during transmission, the entire security of the system is at risk. An attacker who obtains the key can decrypt all encrypted data, rendering the protection ineffective. This makes key management a critical aspect of using symmetric encryption.
Various methods have been developed to address this issue. In some cases, keys are exchanged through secure channels before communication begins. In others, additional encryption techniques are used to protect the key during transmission. However, these solutions can add complexity and may not always be practical, especially in large or dynamic systems.
The difficulty of key distribution is one of the main reasons why symmetric encryption is often combined with asymmetric encryption. By using asymmetric methods to securely exchange keys, systems can take advantage of the speed of symmetric encryption without compromising security.
Real-World Applications of Symmetric Encryption
Symmetric encryption is widely used in everyday technology, often without users even realizing it. One common example is file encryption on personal devices. When you lock your phone or computer, symmetric encryption is used to protect the data stored on it. This ensures that even if the device is lost or stolen, the information remains secure.
In addition to device security, symmetric encryption is used in database protection. Organizations store large amounts of sensitive data, such as customer information and financial records. Encrypting this data ensures that it cannot be accessed without proper authorization, even if the database is compromised.
Another important application is in real-time communication. Messaging apps, video conferencing platforms, and streaming services rely on symmetric encryption to secure data as it is transmitted. The speed of symmetric encryption makes it ideal for these scenarios, where delays must be minimized.
Financial systems also depend heavily on symmetric encryption. When processing transactions, systems must encrypt and decrypt data بسرعة to ensure both security and efficiency. This allows users to complete transactions seamlessly while maintaining the integrity of their information.
Why Symmetric Encryption Remains Essential
Despite the emergence of more advanced encryption techniques, symmetric encryption continues to play a vital role in modern cybersecurity. Its combination of speed, efficiency, and simplicity makes it indispensable for many applications.
The ability to handle large volumes of data quickly ensures that systems can operate at scale without compromising performance. At the same time, the strength of modern symmetric algorithms provides a high level of security, making them suitable for protecting sensitive information.
While the challenge of key distribution cannot be ignored, it is often addressed through complementary technologies. By integrating symmetric encryption with other security measures, organizations can create robust systems that balance performance and protection.
In essence, symmetric encryption forms the backbone of many security solutions. It is not a standalone answer to all security challenges, but it is a critical component that works alongside other methods to უზრუნველ comprehensive protection.
Understanding the Foundation of Asymmetric Encryption
Asymmetric encryption introduces a more advanced approach to securing information by using two separate but mathematically linked keys. Unlike symmetric encryption, which depends on a single shared secret, asymmetric encryption divides responsibilities between a public key and a private key. This separation creates a system where data can be encrypted without exposing the means to decrypt it, significantly improving security in open and untrusted environments.
The public key is designed to be shared freely. Anyone can use it to encrypt data intended for the key owner. The private key, however, is kept strictly confidential and is the only key capable of decrypting that data. This structure eliminates the need to exchange secret keys beforehand, solving one of the most difficult problems in cryptography.
This method is especially useful in situations where two parties have never interacted before. They can still communicate securely without needing a pre-established secure channel. The trust is built into the mathematical relationship between the keys rather than relying on a shared secret. This makes asymmetric encryption a foundational element of modern digital security systems.
How Public and Private Keys Work Together
The strength of asymmetric encryption lies in how its key pair functions as a coordinated system. Although the keys are different, they are generated together in such a way that anything encrypted with one key can only be decrypted with the other. This relationship is what enables secure communication and verification processes.
When someone wants to send a secure message, they use the recipient’s public key to encrypt it. Once encrypted, the message becomes unreadable to anyone except the holder of the corresponding private key. Even the sender cannot decrypt the message after it has been encrypted, which ensures that only the intended recipient has access to the information.
This mechanism also supports a reversed process used for authentication. A sender can encrypt a piece of data using their private key, effectively creating a digital signature. Anyone with access to the sender’s public key can verify that the data was indeed created by that sender and has not been altered. This dual functionality—confidentiality and authentication—makes asymmetric encryption incredibly versatile.
Because of this design, asymmetric encryption enables secure communication over public networks like the internet. It allows users to exchange sensitive information without worrying about eavesdroppers gaining access to private data.
Key Advantages That Make Asymmetric Encryption Powerful
One of the most important advantages of asymmetric encryption is that it removes the need for secure key distribution. Since public keys can be shared openly, there is no risk in transmitting them across insecure channels. This simplifies the process of establishing secure communication between parties who may not have any prior relationship.
Another significant benefit is support for digital signatures. These signatures provide a way to verify the identity of the sender and ensure that the data has not been tampered with. This is crucial in scenarios such as software distribution, legal documentation, and secure communications, where trust and authenticity are essential.
Asymmetric encryption also allows for better control over key management. If a private key is compromised, it can be revoked and replaced without affecting other users. This flexibility makes it easier to maintain security over time, especially in large systems with many participants.
Additionally, asymmetric encryption supports scalable systems. Since each user only needs a single key pair, the complexity of managing keys does not grow exponentially as more users are added. This makes it practical for use in global networks where millions of users need to communicate securely.
Common Asymmetric Encryption Algorithms in Practice
Several well-known algorithms implement asymmetric encryption, each with its own characteristics and use cases. These algorithms rely on complex mathematical problems that are difficult to solve without the appropriate key, ensuring a high level of security.
RSA is one of the most widely recognized asymmetric algorithms. It has been used for decades and remains a standard in many systems. RSA is particularly effective for encrypting small amounts of data and creating digital signatures. Its reliability and widespread adoption make it a trusted choice in many applications.
Elliptic Curve Cryptography (ECC) is a more modern approach that offers similar security with smaller key sizes. This efficiency makes it especially suitable for environments where processing power and storage are limited, such as mobile devices and embedded systems. ECC has gained popularity due to its ability to provide strong security without the overhead associated with larger keys.
Diffie-Hellman is another important technique, although it is not used for direct encryption. Instead, it enables two parties to generate a shared secret over an insecure channel. This shared secret can then be used for symmetric encryption, combining the strengths of both approaches. Diffie-Hellman plays a critical role in establishing secure connections in many modern protocols.
These algorithms highlight the versatility of asymmetric encryption and its ability to adapt to different security requirements. Each algorithm serves a specific purpose, contributing to a comprehensive security strategy.
Performance Limitations and Trade-offs
While asymmetric encryption provides powerful security features, it comes with a trade-off in performance. The mathematical operations involved are more complex and require significantly more processing power than those used in symmetric encryption. As a result, asymmetric encryption is much slower, especially when handling large amounts of data.
This difference in speed becomes more noticeable as the volume of data increases. Encrypting a large file using asymmetric methods would take considerably longer and consume more resources compared to symmetric encryption. For this reason, asymmetric encryption is rarely used on its own for bulk data processing.
Instead, it is typically reserved for tasks that involve small amounts of data but require high levels of security. Examples include encrypting passwords, exchanging keys, and creating digital signatures. By limiting its use to these specific tasks, systems can take advantage of its strengths without suffering from its performance limitations.
The slower speed of asymmetric encryption also affects energy consumption. Devices with limited resources, such as smartphones or IoT devices, may experience reduced battery life if asymmetric operations are used excessively. This further reinforces the need to use asymmetric encryption strategically rather than universally.
Practical Uses of Asymmetric Encryption in Everyday Systems
Asymmetric encryption is deeply integrated into many technologies that people use every day. One of the most common examples is secure web browsing. When you access a secure website, asymmetric encryption is used to establish a safe connection between your browser and the server. This ensures that any data exchanged during the session remains confidential.
Email security is another area where asymmetric encryption plays a vital role. It allows users to send encrypted messages and verify the identity of the sender. This is particularly important in professional and organizational settings, where sensitive information is frequently exchanged عبر email systems.
Software distribution also يعتمد heavily on asymmetric encryption. Developers use digital signatures to verify that their software has not been altered since it was released. When users download and install software, their systems can check these signatures to ensure authenticity and integrity.
Virtual private networks (VPNs) use asymmetric encryption during the initial setup phase. It helps establish a secure channel through which data can be transmitted safely. Once the connection is established, other encryption methods may take over for efficiency, but asymmetric encryption is essential for creating that initial trust.
The Role of Asymmetric Encryption in Identity Verification
One of the most powerful applications of asymmetric encryption is identity verification. In a digital environment, it is often necessary to confirm that a person or system is who they claim to be. Asymmetric encryption provides a reliable way to achieve this through digital signatures and certificates.
When a document is signed using a private key, it creates a unique signature that can be verified using the corresponding public key. This ensures that the document has not been altered and that it originates from the claimed source. This process is widely used in legal, financial, and governmental systems.
Certificates further enhance this process by linking public keys to verified identities. These certificates are issued by trusted authorities and serve as proof that a particular key belongs to a specific entity. This system forms the basis of trust for many online interactions, including secure websites and online transactions.
By enabling both confidentiality and authentication, asymmetric encryption addresses two critical aspects of security. It not only protects data from unauthorized access but also ensures that users can trust the source of the information they receive.
Why Asymmetric Encryption Is Indispensable in Modern Security
Despite its slower performance, asymmetric encryption remains an essential component of modern cybersecurity. Its ability to facilitate secure communication without prior key exchange makes it uniquely suited for today’s interconnected world.
The flexibility it offers in managing keys and verifying identities ensures that systems can adapt to changing security requirements. Whether it is securing online transactions, protecting communications, or verifying digital content, asymmetric encryption provides capabilities that cannot be achieved with symmetric methods alone.
Rather than replacing symmetric encryption, it complements it. By handling tasks that require high security and leaving bulk data processing to faster methods, asymmetric encryption fits into a larger ecosystem of security technologies.
Its continued evolution, along with advancements in computing and cryptographic research, ensures that it will remain a cornerstone of digital security for years to come.
Comparing Performance and Efficiency Between Both Encryption Types
When evaluating encryption methods, performance is often one of the first factors that comes into consideration. Symmetric and asymmetric encryption differ significantly in how efficiently they process data, and this difference directly impacts how they are used in real-world systems. Symmetric encryption is designed for speed, allowing it to handle large volumes of data with minimal delay. In contrast, asymmetric encryption prioritizes security features over speed, which results in slower processing times.
The difference in performance is not minor—it is substantial. Symmetric encryption can process data hundreds or even thousands of times faster than asymmetric encryption. This efficiency allows it to encrypt large files, continuous data streams, and high-frequency transactions without creating bottlenecks. On the other hand, asymmetric encryption involves complex mathematical computations that require more processing power and time, making it less suitable for handling large datasets.
Because of this contrast, systems are designed to use each method where it performs best. Symmetric encryption handles the bulk of data processing, while asymmetric encryption is used selectively for tasks that require secure key exchange or identity verification. This division of responsibilities ensures that systems remain both secure and efficient without sacrificing performance.
How Speed Influences Real-World Encryption Decisions
The speed difference between symmetric and asymmetric encryption shapes how developers and organizations design their security systems. In environments where large amounts of data are constantly being processed, such as cloud services or streaming platforms, using a slow encryption method would result in noticeable delays and reduced performance. Symmetric encryption provides the speed needed to maintain smooth and responsive operations in these scenarios.
For example, when transferring large files or streaming high-definition video, encryption must occur in real time without interrupting the user experience. Symmetric encryption enables this by processing data quickly and efficiently. If asymmetric encryption were used instead, the delay would be significant enough to disrupt the service.
At the same time, there are situations where speed is less important than security. When establishing a secure connection or verifying identity, the system can afford to spend extra time performing complex operations. This is where asymmetric encryption becomes valuable. By using it only when necessary, systems can balance performance and security effectively.
This strategic use of both methods allows organizations to optimize their systems for different tasks, ensuring that each operation is handled in the most efficient way possible.
Security Features and Strengths of Each Approach
While performance is important, security remains the primary purpose of encryption. Both symmetric and asymmetric encryption offer strong protection, but they achieve it in different ways. Understanding these differences helps in selecting the right method for specific security requirements.
Symmetric encryption is known for its strength per key length. Because it uses simpler mathematical operations, it can provide a high level of security with relatively smaller keys. This efficiency makes it resistant to many types of attacks while maintaining fast performance. Additionally, its simplicity reduces the likelihood of implementation errors, which can often be a source of vulnerabilities.
Asymmetric encryption, on the other hand, offers features that go beyond basic data protection. It enables secure key exchange, allowing two parties to establish a shared secret without prior contact. It also supports digital signatures, which provide authentication and data integrity. These capabilities make asymmetric encryption essential for building trust in digital communications.
Another advantage of asymmetric encryption is the ability to revoke and replace keys if they are compromised. This flexibility allows systems to maintain security even in the face of potential breaches. Symmetric encryption does not offer the same level of flexibility, as changing a key often requires updating it across all systems that use it.
Together, these strengths highlight why both encryption types are necessary. Each one addresses different aspects of security, and their combined use creates a more comprehensive protection strategy.
Key Management Differences and Their Impact
One of the most significant distinctions between symmetric and asymmetric encryption lies in how keys are managed. Key management is a critical component of any encryption system, as the security of the entire system depends on how well keys are generated, stored, distributed, and replaced.
In symmetric encryption, key management can quickly become complex as the number of users increases. Each pair of users requires a unique shared key, which means the number of keys grows rapidly in larger systems. Managing these keys securely becomes a challenging task, especially when they need to be distributed without being intercepted.
Additionally, updating or replacing a key in a symmetric system can be difficult. Every instance where the key is used must be updated simultaneously to avoid communication failures. This process can be time-consuming and prone to errors, particularly in large-scale environments.
Asymmetric encryption simplifies key management by reducing the number of keys required. Each user only needs a single key pair, consisting of a public key and a private key. Public keys can be shared openly, eliminating the need for secure distribution channels. This makes it easier to scale systems and manage keys efficiently.
If a private key is compromised, it can be revoked and replaced without affecting other users. This ability to isolate and address security issues makes asymmetric encryption more adaptable in dynamic environments. However, it also requires careful handling of private keys to ensure they remain secure at all times.
Choosing the Right Method Based on Use Case
Selecting between symmetric and asymmetric encryption is not about determining which one is better overall. Instead, it is about understanding the specific requirements of a given situation and choosing the method that best meets those needs.
For tasks that involve processing large amounts of data, symmetric encryption is the preferred choice. Its speed and efficiency make it ideal for encrypting files, securing databases, and handling real-time communications. Once a secure key has been established, it can be used repeatedly to protect data without causing performance issues.
Asymmetric encryption is better suited for scenarios that require secure communication between unknown parties or identity verification. It is commonly used for establishing secure connections, exchanging keys, and creating digital signatures. These tasks involve smaller amounts of data but require a higher level of trust and security.
In many cases, the decision is not about choosing one method over the other but about combining them effectively. By using asymmetric encryption to handle key exchange and symmetric encryption for data processing, systems can achieve both security and efficiency. This hybrid approach is widely used in modern security protocols and has become the standard for protecting digital communications.
How Hybrid Encryption Combines the Best of Both Worlds
Hybrid encryption is a practical solution that leverages the strengths of both symmetric and asymmetric encryption. Instead of relying on a single method, it uses each one for the tasks it handles best. This approach allows systems to overcome the limitations of each method while maximizing their advantages.
In a typical hybrid system, asymmetric encryption is used at the beginning of a communication session. It enables two parties to securely exchange a symmetric key without exposing it to potential attackers. Once the key is established, symmetric encryption takes over for the rest of the communication, ensuring fast and efficient data processing.
This process happens seamlessly and often goes unnoticed by users. For example, when accessing a secure website, the initial connection setup involves asymmetric encryption. After the connection is established, all subsequent data is encrypted using symmetric methods. This combination ensures both security and performance.
Hybrid encryption is also used in many other applications, including secure messaging, virtual private networks, and software updates. Its versatility and effectiveness make it a cornerstone of modern cybersecurity practices.
Real-World Systems That Rely on Hybrid Encryption
Many widely used technologies depend on hybrid encryption to function securely. Secure web communication is one of the most common examples. When a user connects to a secure website, the system uses asymmetric encryption to establish trust and exchange keys. After that, symmetric encryption is used to handle the actual data transfer.
Messaging applications also use hybrid encryption to protect user communications. When a conversation is initiated, keys are exchanged securely using asymmetric methods. Once the connection is established, messages are encrypted and decrypted using symmetric encryption, ensuring both security and speed.
Virtual private networks rely on a similar approach. During the initial connection phase, asymmetric encryption is used to authenticate the parties and establish a secure channel. Afterward, symmetric encryption is used to protect the data transmitted through the network.
Software update systems also benefit from hybrid encryption. Updates are signed using asymmetric encryption to verify their authenticity, while the actual data transfer may use symmetric encryption for efficiency. This ensures that updates are both secure and delivered quickly.
Benefits and Trade-offs of Using a Hybrid Approach
The hybrid approach offers several advantages that make it the preferred choice for many applications. By combining the strengths of symmetric and asymmetric encryption, it provides a balanced solution that addresses both performance and security needs.
One of the main benefits is improved efficiency. By using symmetric encryption for data processing, systems can handle large volumes of information بسرعة without sacrificing performance. At the same time, asymmetric encryption ensures that keys are exchanged securely and identities are verified.
Another advantage is flexibility. Hybrid systems can adapt to different requirements, using each encryption method where it is most effective. This adaptability makes it suitable for a wide range of applications, from personal communication to large-scale enterprise systems.
However, implementing hybrid encryption also introduces complexity. Managing both types of keys requires careful planning and robust security measures. Systems must ensure that keys are stored securely, rotated regularly, and protected from unauthorized access.
Despite these challenges, the benefits of hybrid encryption far outweigh its drawbacks. It provides a comprehensive solution that leverages the best aspects of both encryption methods, making it an essential part of modern cybersecurity strategies.
Understanding the Practical Challenges of Implementing Encryption
Implementing encryption in real-world systems involves far more than simply choosing an algorithm and generating keys. While both symmetric and asymmetric encryption provide strong theoretical security, their effectiveness depends heavily on how they are applied in practice. Poor implementation can undermine even the strongest encryption methods, leaving systems vulnerable to attacks.
One of the main challenges lies in integrating encryption into existing systems without disrupting performance or usability. Applications must continue to function smoothly while handling encryption and decryption processes in the background. This requires careful planning, testing, and optimization to ensure that security measures do not negatively impact user experience.
Another important factor is maintaining consistency across different components of a system. Encryption must be applied uniformly to avoid weak points where data might be exposed. This includes securing data at rest, data in transit, and sometimes even data in use. Achieving this level of coverage requires a comprehensive approach rather than isolated solutions.
Performance Impact and Resource Considerations
Encryption inevitably consumes system resources, including processing power, memory, and energy. While symmetric encryption is generally efficient, it still requires resources when applied at scale. Asymmetric encryption, with its more complex operations, demands even more computational power.
In high-performance environments, such as large-scale web services or cloud platforms, the cumulative effect of encryption can become significant. Systems handling millions of requests must allocate sufficient resources to manage encryption tasks without creating bottlenecks. This often involves optimizing algorithms, using hardware acceleration, and carefully balancing workloads.
Mobile devices and embedded systems face additional challenges بسبب limited resources. Excessive use of computationally intensive encryption can drain battery life and reduce overall performance. Developers must carefully select encryption methods that provide adequate security while remaining efficient enough for constrained environments.
Memory usage is another consideration. Encryption processes often require temporary storage for keys and intermediate data. In systems with many simultaneous connections, this can add up quickly. Efficient memory management is essential to ensure that encryption does not lead to instability or reduced performance.
The Complexity of Key Management and Storage
Keys are the foundation of any encryption system, and managing them securely is one of the most critical and challenging aspects of implementation. The strength of encryption is meaningless if keys are poorly protected or mishandled.
Secure storage is the first priority. Sensitive keys, especially private keys in asymmetric systems, must be protected from unauthorized access. Specialized hardware solutions, such as hardware security modules, are often used to store keys in highly secure environments. These devices are designed to prevent extraction or tampering, even in the event of physical attacks.
For less sensitive keys, encrypted storage within databases or secure software environments may be sufficient. However, even these methods require strict access controls and monitoring to prevent misuse. Backup copies of keys must also be handled carefully, as they can become a target for attackers if not properly secured.
Key rotation is another important aspect of management. Regularly changing keys reduces the risk of long-term exposure if a key is compromised. However, rotating keys introduces its own challenges. Systems must ensure that old data remains accessible while transitioning to new keys, and any errors during this process can result in data loss.
Effective key management requires well-defined policies, automation where possible, and continuous monitoring. Without these measures, even the most advanced encryption systems can fail to provide adequate security.
Compliance and Regulatory Requirements
Different industries are subject to various regulations that dictate how encryption must be implemented and managed. These requirements are designed to ensure that sensitive data is protected according to established standards.
Organizations handling financial data must adhere to strict security guidelines that define acceptable encryption methods, key lengths, and operational practices. Healthcare systems must protect patient information according to privacy regulations, which often include specific requirements for encryption and data handling. Government-related systems may need to follow additional standards that ensure compliance with national security policies.
Meeting these requirements involves more than just technical implementation. Organizations must also maintain detailed documentation, undergo regular audits, and demonstrate compliance to regulatory bodies. This adds an additional layer of complexity to encryption projects, requiring coordination between technical teams and compliance experts.
Failure to meet these standards can result in severe consequences, including financial penalties and reputational damage. As a result, organizations must treat compliance as an integral part of their encryption strategy rather than an afterthought.
Planning and Deployment Strategies for Effective Encryption
A successful encryption strategy begins with careful planning. Rather than attempting to secure everything at once, it is often more effective to start with smaller, manageable projects. This allows teams to identify potential issues and refine their approach before scaling up.
Testing environments play a crucial role in this process. By simulating real-world conditions, teams can evaluate how encryption affects performance, identify bottlenecks, and ensure that key management processes work as intended. These tests provide valuable insights that can prevent costly mistakes during full deployment.
Documentation is another essential component. Clear and detailed documentation ensures that all team members understand how encryption is implemented and how to handle keys securely. This is especially important in larger organizations যেখানে multiple teams may interact with encrypted systems.
Training is equally important. Employees who handle sensitive data or manage encryption systems must be aware of best practices and potential risks. Human error is one of the most common causes of security breaches, so proper training can significantly reduce this risk.
Regular auditing and monitoring help maintain the effectiveness of encryption over time. By continuously evaluating systems and processes, organizations can identify weaknesses and address them before they are exploited.
Balancing Security and Usability in Encryption Systems
One of the ongoing challenges in cybersecurity is finding the right balance between security and usability. While strong encryption provides protection, it can also introduce complexity that affects how users interact with systems.
For example, requiring frequent key changes or complex authentication processes can improve security but may also frustrate users. If systems become too difficult to use, users may look for ways to bypass security measures, which can create new vulnerabilities.
Designing user-friendly encryption systems involves minimizing friction while maintaining strong protection. This can include automating key management processes, integrating encryption seamlessly into applications, and providing clear guidance to users. The goal is to make security an invisible part of the user experience rather than a barrier.
Achieving this balance requires collaboration between security experts, developers, and user experience designers. By considering both technical and human factors, organizations can create systems that are both secure and practical.
The Future Direction of Encryption Technologies
Encryption continues to evolve as new technologies and threats emerge. Advances in computing power, including the development of quantum computing, are expected to influence how encryption methods are designed and implemented. Researchers are بالفعل exploring new algorithms that can resist potential future threats while maintaining efficiency.
At the same time, the growing number of connected devices is increasing the demand for lightweight encryption solutions. As more systems rely on real-time data processing, the need for fast and efficient encryption will continue to grow. This will likely drive further innovation in both symmetric and asymmetric techniques.
Integration with emerging technologies such as artificial intelligence and distributed systems may also shape the future of encryption. These advancements could lead to more adaptive and intelligent security solutions that respond dynamically to threats.
Despite these changes, the fundamental principles of encryption—protecting data and ensuring trust—will remain the same. The challenge will be to adapt these principles to new environments and evolving risks.
Final Thoughts
Selecting the right encryption approach requires a clear understanding of both the technical and practical aspects of security. Symmetric encryption offers unmatched speed and efficiency, making it ideal for handling large volumes of data. Asymmetric encryption provides essential features such as secure key exchange and identity verification, enabling trust in digital interactions.
In most cases, the best solution is not to choose one over the other but to use them together. A hybrid approach allows systems to benefit from the strengths of both methods while minimizing their weaknesses. This combination has become the standard for modern security systems and is widely used across industries.
However, encryption alone is not enough to guarantee security. Proper key management, regular monitoring, and user awareness are equally important. Without these elements, even the strongest encryption can be compromised.
By taking a thoughtful and strategic approach, organizations can build encryption systems that protect data effectively while maintaining performance and usability. This ensures that sensitive information remains secure in an increasingly complex digital landscape.