When discussing email delivery on the internet, the concept of ports becomes unavoidable. Ports act as logical channels that allow different types of network traffic to flow between devices in an organized way. Among these, SMTP ports play a critical role because they govern how emails are sent from one system to another. The debate between port 25 and port 587 is not simply about choosing one over the other; it reflects the evolution of email security, authentication, and modern networking practices. Understanding this difference is essential for anyone working with email systems, whether for personal use, business communication, or IT infrastructure management.
SMTP, or Simple Mail Transfer Protocol, has been the backbone of email transmission for decades. However, the way it operates has changed significantly over time. In earlier days, email systems relied heavily on simplicity rather than security, which made communication easier but also left systems vulnerable. As cyber threats evolved, so did the need for safer communication channels. This is where the distinction between port 25 and port 587 becomes meaningful, as each represents a different stage in the development of secure email communication.
Understanding the Role of SMTP in Email Communication
SMTP is essentially the language that email servers use to communicate with each other. Whenever you send an email, SMTP ensures that your message travels from your device to the recipient’s mail server. This process might appear instantaneous, but it involves multiple steps, including identifying the recipient’s server, transferring the message, and confirming delivery. Without SMTP, email as we know it would not function.
Initially, SMTP was designed without encryption because the internet itself was considered a relatively safe environment. Over time, this assumption proved incorrect. Cybercriminals began exploiting unprotected communications, leading to data breaches and unauthorized access to sensitive information. As a result, enhancements were introduced to make SMTP more secure, including encryption protocols and authentication mechanisms. These improvements are closely tied to the use of different ports, particularly port 587.
What a Network Port Really Represents
To understand the difference between port 25 and port 587, it is important to first grasp what a port actually is. In networking terms, a port is a virtual endpoint that allows software applications to communicate over a network. Unlike physical ports such as USB or HDMI, network ports exist within the operating system and are identified by numerical values ranging from 0 to 65535.
Each port is associated with a specific service or protocol. For example, web traffic typically uses port 80 or 443, while email transmission relies on SMTP ports like 25 and 587. When data is sent across the internet, it includes a port number that tells the receiving system which application should handle it. This system ensures that multiple services can operate simultaneously on a single device without interfering with each other.
Ports also play a role in security. By controlling which ports are open or closed, administrators can regulate the flow of traffic and reduce the risk of unauthorized access. This is particularly important for email systems, where sensitive information is often transmitted.
The Historical Significance of Port 25
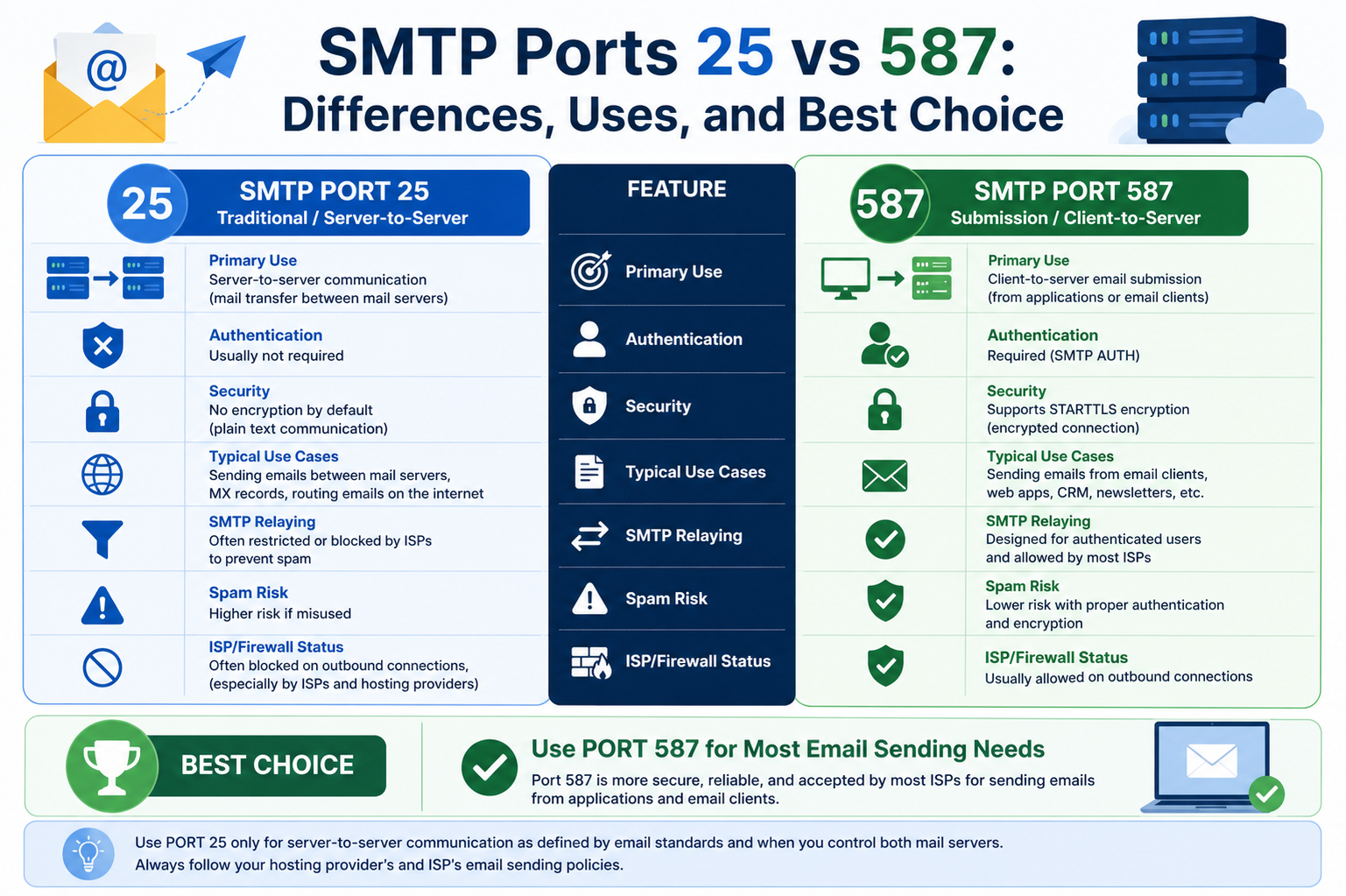
Port 25 holds a special place in the history of email communication. It was the original port designated for SMTP and served as the default channel for sending emails across the internet. For many years, all email traffic passed through this port, making it a fundamental component of early networking infrastructure.
In its original design, port 25 was intended for server-to-server communication. This means that when one email server needed to deliver a message to another server, it would use port 25 to complete the transfer. This function remains relevant today, as many servers still rely on port 25 for relaying messages between domains.
However, the widespread use of port 25 also made it a target for abuse. Spammers and malicious actors began exploiting this port to send large volumes of unsolicited emails. Because SMTP lacked built-in authentication, it was relatively easy to impersonate other users or domains. This led to a surge in spam and phishing attacks, prompting internet service providers to implement restrictions on port 25 traffic.
Why Port 25 Became Associated with Security Risks
One of the main reasons port 25 is considered less secure is its lack of encryption. When data is transmitted over this port, it is typically sent in plain text. This means that anyone with access to the network can potentially intercept and read the information being transmitted. For organizations handling sensitive data, this poses a significant risk.
Another issue is the absence of authentication. Port 25 does not inherently require users to verify their identity before sending emails. This makes it easier for attackers to exploit email servers and send messages that appear to come from legitimate sources. Such vulnerabilities have been widely used in phishing campaigns, where users are tricked into revealing personal or financial information.
Due to these risks, many modern networks restrict the use of port 25, especially for outbound email from client devices. Instead, they encourage the use of more secure alternatives like port 587, which offers better protection against unauthorized access and data interception.
The Emergence of Port 587 as a Secure Alternative
As the need for secure communication grew, port 587 was introduced as the preferred option for sending emails. Unlike port 25, this port is specifically designed for message submission from clients to servers. It incorporates modern security features that address the shortcomings of earlier SMTP implementations.
Port 587 supports encryption protocols such as TLS, which protect data during transmission. This ensures that even if the data is intercepted, it cannot be easily read or manipulated. Additionally, port 587 requires authentication, meaning users must provide valid credentials before they can send emails. This significantly reduces the risk of unauthorized access and spam.
The adoption of port 587 represents a shift toward more secure and reliable email communication. It aligns with current best practices and is widely supported by email service providers, making it the default choice for most modern applications.
How Encryption Enhances Email Security
Encryption is a key factor that differentiates port 587 from port 25. When encryption is enabled, the data being transmitted is converted into a coded format that can only be deciphered by the intended recipient. This process protects sensitive information such as login credentials, personal messages, and financial details.
One common method used with port 587 is STARTTLS, which upgrades an existing unencrypted connection to a secure one. This allows both the client and server to negotiate encryption parameters before transmitting data. The result is a secure communication channel that safeguards information from potential threats.
In contrast, emails sent over port 25 without encryption are vulnerable to interception. This makes them unsuitable for transmitting confidential data. As cybersecurity threats continue to evolve, the importance of encryption cannot be overstated. It is a fundamental requirement for protecting digital communication in today’s interconnected world.
The Role of Authentication in Modern Email Systems
Authentication is another critical feature that sets port 587 apart. By requiring users to verify their identity, email systems can ensure that only authorized individuals are allowed to send messages. This helps prevent misuse and reduces the likelihood of spam and phishing attacks.
Authentication methods can vary, ranging from simple username and password combinations to more advanced techniques such as token-based systems. Regardless of the method used, the goal is to establish trust between the client and the server. This trust is essential for maintaining the integrity of the email system.
Port 25, on the other hand, does not enforce authentication by default. This lack of verification has been a major contributor to its decline in popularity for client-to-server communication. While it still serves a purpose in server-to-server interactions, its limitations make it less suitable for modern email usage.
Why Multiple SMTP Ports Are Necessary
The existence of multiple SMTP ports may seem redundant at first, but it serves an important purpose. Different ports are designed to handle different types of communication, allowing for greater flexibility and efficiency. For example, port 25 is primarily used for relaying messages between servers, while port 587 is used for submitting messages from clients.
This separation helps optimize performance and enhances security. By dedicating specific ports to specific functions, network administrators can implement targeted security measures and reduce the risk of interference. It also allows for better management of email traffic, ensuring that messages are delivered reliably and efficiently.
In addition, having multiple ports provides a fallback option in case one port is blocked or restricted. This is particularly useful in environments where certain ports are filtered by firewalls or internet service providers. By using alternative ports, email systems can maintain functionality even under restrictive conditions.
The Evolution of Email Practices in Modern Networks
Email communication has come a long way since the early days of SMTP. What started as a simple method for exchanging messages has evolved into a complex system that prioritizes security, reliability, and scalability. The transition from port 25 to port 587 reflects this evolution, highlighting the need for continuous improvement in response to emerging threats.
Modern email systems are designed with security in mind. They incorporate encryption, authentication, and advanced filtering techniques to protect users from spam and malicious content. These measures are essential for maintaining trust in digital communication and ensuring that email remains a viable tool for both personal and professional use.
As technology continues to advance, the importance of understanding SMTP ports and their functions will only increase. Whether you are configuring an email server, troubleshooting network issues, or preparing for a certification exam, a solid grasp of these concepts is invaluable.
Deeper Insight into Port 25 and Its Functional Role
Port 25 continues to exist in modern networking environments primarily because of its foundational role in server-to-server communication. While its use has declined for client-based email submission, it remains essential for the transfer of messages between mail servers across the internet. When an email is sent, it does not travel directly from the sender’s device to the recipient’s inbox. Instead, it is handed off to a mail server, which then communicates with other servers until the message reaches its destination. This relay process relies heavily on port 25, making it a backbone component of global email infrastructure.
Despite its importance, the way port 25 is used today is far more controlled than in the past. Network administrators often configure strict rules to limit its exposure, ensuring that only trusted servers can communicate through it. This controlled usage helps maintain the reliability of email delivery while minimizing the risks associated with open, unauthenticated communication channels.
Server-to-Server Communication and Message Relaying
The primary strength of port 25 lies in its ability to facilitate seamless communication between email servers. When a mail server receives a message intended for a different domain, it must determine the correct destination server and establish a connection to deliver the message. This process involves querying domain records, identifying the appropriate mail exchange server, and transmitting the email using SMTP over port 25.
This relay mechanism is highly efficient and has been refined over decades of use. It allows emails to traverse multiple networks and reach recipients regardless of their location. However, because this process often occurs without direct user interaction, it must be carefully managed to prevent abuse. Unauthorized relaying, for example, can turn a server into a source of spam, which can damage its reputation and lead to blacklisting.
To address these concerns, modern servers implement safeguards such as relay restrictions and IP filtering. These measures ensure that only authorized systems can send messages through the server, reducing the likelihood of misuse while preserving the functionality of port 25 for legitimate communication.
The Decline of Port 25 for Client Email Submission
In earlier networking environments, users commonly relied on port 25 to send emails directly from their devices. This approach was simple but lacked the security measures needed to protect user data and prevent unauthorized access. As cyber threats became more sophisticated, this model proved inadequate.
Internet service providers began blocking outbound traffic on port 25 to combat spam and malicious activity. This shift forced users and organizations to adopt alternative ports that offered better security and accountability. As a result, port 587 emerged as the preferred option for client email submission, leaving port 25 primarily reserved for backend server operations.
This transition marked a significant change in how email systems are configured. It also highlighted the importance of separating different types of email traffic to improve both security and performance. By restricting port 25 to server-level communication, networks can better control the flow of messages and reduce the risk of abuse.
Understanding the Risks of Unencrypted Transmission
One of the most critical issues with port 25 is its association with unencrypted communication. When data is transmitted without encryption, it is sent in a readable format that can be intercepted by anyone with access to the network. This vulnerability is particularly concerning for email, which often contains sensitive or confidential information.
Attackers can use techniques such as packet sniffing to capture unencrypted data as it travels across the network. Once intercepted, this information can be analyzed and exploited for various malicious purposes, including identity theft and corporate espionage. The lack of encryption also makes it easier to alter messages in transit, potentially leading to misinformation or unauthorized actions.
These risks have made unencrypted email transmission increasingly unacceptable in modern environments. Organizations are now expected to implement strong security measures to protect user data, and relying on unprotected ports like 25 for client communication does not meet these expectations.
Spam, Abuse, and the Reputation of Port 25
The rise of spam has played a major role in shaping the perception of port 25. Because it does not require authentication, it became a convenient tool for spammers to distribute large volumes of unsolicited messages. Compromised systems could be used to send spam without the knowledge of their owners, contributing to widespread abuse of the port.
This misuse led to significant consequences for both individuals and organizations. Email servers associated with spam activity can be blacklisted, preventing them from sending messages to other networks. This can disrupt communication and damage the credibility of a business or service provider.
To combat spam, many networks now monitor traffic on port 25 and implement filtering mechanisms to detect suspicious activity. While these measures have reduced abuse, they have also reinforced the need for more secure alternatives, further driving the adoption of port 587 for authenticated email submission.
Transitioning Toward Secure Email Submission Practices
The shift from port 25 to port 587 represents a broader move toward secure email practices. This transition involves not only changing the port number but also adopting new technologies and protocols that enhance security. Encryption, authentication, and policy enforcement all play a role in this process.
Organizations that make this transition benefit from improved protection against cyber threats and greater control over their email systems. By requiring users to authenticate before sending messages, they can ensure that only authorized individuals have access to the system. Encryption further protects the data being transmitted, reducing the risk of interception.
This approach also aligns with industry standards and regulatory requirements, which increasingly emphasize the importance of data security. As a result, port 587 has become the default choice for modern email clients and services.
Exploring the Mechanics of Port 587 in Detail
Port 587 is specifically designed for message submission, making it the ideal choice for sending emails from client devices to mail servers. Unlike port 25, it is built with security in mind, incorporating features that address the vulnerabilities of earlier SMTP implementations.
When a user sends an email through port 587, the client establishes a connection with the mail server and initiates the SMTP process. Before the message is transmitted, the server typically requires authentication, ensuring that the user has the necessary permissions. Once authenticated, the connection can be secured using encryption protocols, protecting the data as it travels across the network.
This process not only enhances security but also improves accountability. Because each message is associated with an authenticated user, it is easier to track and manage email activity. This helps prevent abuse and ensures that the system is used responsibly.
The Importance of STARTTLS in Secure Communication
A key feature of port 587 is its support for STARTTLS, a protocol that enables encryption within an existing SMTP connection. Rather than requiring a separate secure channel, STARTTLS allows the client and server to upgrade an unencrypted connection to a secure one during the communication process.
This flexibility makes it easier to implement encryption without requiring significant changes to existing infrastructure. It also ensures compatibility with a wide range of systems, allowing organizations to adopt secure practices without disrupting their operations.
Once the connection is encrypted, all data transmitted between the client and server is protected from interception. This includes not only the email content but also authentication credentials and other sensitive information. The use of STARTTLS is a major reason why port 587 is considered a secure and reliable option for email submission.
Authentication Requirements and Their Impact on Security
Authentication is a defining characteristic of port 587 and a key factor in its effectiveness. By requiring users to verify their identity, the system can prevent unauthorized access and reduce the risk of abuse. This is particularly important in environments where multiple users share the same infrastructure.
Authentication mechanisms can include traditional methods such as usernames and passwords, as well as more advanced approaches like token-based systems. Regardless of the method used, the goal is to ensure that only legitimate users can send emails through the server.
This requirement also helps maintain the reputation of the email system. Because each message is linked to an authenticated user, it is easier to identify and address any issues that arise. This level of accountability is not possible with port 25, where messages can be sent without verification.
Why Modern Email Systems Favor Port 587
The preference for port 587 in modern email systems is driven by its combination of security, reliability, and compliance with industry standards. As organizations become more aware of the risks associated with unprotected communication, they are increasingly adopting solutions that prioritize data protection.
Port 587 meets these requirements by offering encrypted transmission, mandatory authentication, and compatibility with modern email clients. It also aligns with best practices recommended by security experts and regulatory bodies, making it a safe and practical choice for a wide range of applications.
In addition to its security benefits, port 587 supports efficient email delivery and integration with various technologies. Whether used in cloud-based services, enterprise environments, or personal devices, it provides a consistent and reliable method for sending emails securely.
Real-World Applications of Port 25 in Modern Infrastructure
Even though port 25 is often viewed as outdated for everyday email sending, it still plays a vital role behind the scenes. Large-scale email systems depend on it for routing messages between servers across different domains. When an organization sends emails to external recipients, the internal mail server typically hands off the message to another server using port 25. This process happens automatically and is rarely visible to end users, yet it is essential for global email delivery.
In enterprise environments, administrators often allow port 25 traffic only between trusted servers. This controlled setup ensures that email routing continues to function efficiently without exposing the network to unnecessary risks. It also allows organizations to maintain compatibility with legacy systems that still rely on traditional SMTP behavior. Despite its limitations, port 25 remains deeply embedded in the architecture of email communication.
Use of Port 25 in Automated Systems and Devices
Port 25 is not limited to traditional email servers. Many automated systems and devices still rely on it to send notifications and status updates. For example, monitoring tools can use SMTP over port 25 to alert administrators about system performance issues or security events. These messages are often generated automatically and sent without user interaction.
Devices such as printers, scanners, and embedded systems may also use port 25 for email functionality. A scanner might send a scanned document directly to an email address, while a printer could generate alerts about low ink levels or maintenance requirements. In many cases, these devices are configured with basic SMTP settings that default to port 25, making it a convenient option for simple implementations.
However, as security concerns grow, many organizations are reconfiguring these devices to use more secure ports. This transition can require firmware updates or changes to network settings, but it significantly improves the overall security posture of the system.
Challenges of Maintaining Legacy Compatibility
One of the reasons port 25 continues to exist is the need for backward compatibility. Many older systems were designed before modern security standards were established, and updating them is not always straightforward. Replacing or upgrading legacy infrastructure can be costly and time-consuming, especially for large organizations with complex networks.
As a result, administrators often need to strike a balance between maintaining compatibility and enhancing security. This may involve isolating legacy systems within secure network segments or implementing additional safeguards such as firewalls and intrusion detection systems. By doing so, they can continue to use port 25 where necessary while minimizing the associated risks.
This challenge highlights the broader issue of technological evolution. As new standards emerge, older systems must either adapt or be phased out. Port 25 represents a case where adaptation has been gradual, reflecting the complexity of global email infrastructure.
How Port 587 Supports Modern Email Clients
Port 587 has become the standard choice for email submission in modern applications. Email clients on desktops, laptops, and mobile devices are typically configured to use this port by default. This ensures that messages are sent securely and reliably, regardless of the user’s location or network environment.
When a user composes and sends an email, the client connects to the mail server عبر port 587 and initiates the SMTP process. Authentication is performed to verify the user’s identity, after which the message is transmitted using an encrypted connection. This process happens seamlessly, providing a smooth user experience while maintaining strong security.
Because port 587 is widely supported, it works well with a variety of email services and platforms. This compatibility makes it an ideal choice for both personal and professional use, ensuring consistent performance across different devices and environments.
The Role of Cloud-Based Email Services
Cloud computing has transformed the way email systems are deployed and managed. Instead of maintaining on-premises servers, many organizations now rely on cloud-based services to handle their email needs. These services are designed with security and scalability in mind, and they typically use port 587 for message submission.
Cloud platforms implement advanced security measures, including encryption, authentication, and spam filtering. By using port 587, they ensure that all outgoing messages are protected أثناء transmission. This approach not only safeguards user data but also helps maintain the reputation of the service by preventing unauthorized use.
In addition, cloud-based systems can بسهولة integrate with other applications and services, enabling features such as automated notifications, marketing campaigns, and workflow automation. Port 587 plays a key role in enabling these capabilities by providing a secure channel for email communication.
Security Advantages of Encrypted Email Transmission
The use of encryption with port 587 offers significant advantages over traditional methods. Encrypted communication ensures that sensitive information remains confidential, even if it is intercepted أثناء transmission. This is particularly important for businesses that handle personal data, financial information, or proprietary content.
Encryption also helps protect against tampering. When data is encrypted, any attempt to modify it أثناء transmission will be detected, preventing unauthorized changes. This ensures the integrity of the message and builds trust between the sender and the recipient.
Furthermore, encrypted email transmission supports compliance with data protection regulations. Many industries require organizations to implement strong security measures to protect user information. By using port 587 with encryption, businesses can meet these requirements and avoid potential legal or financial penalties.
Comparing Reliability Between Port 25 and Port 587
Reliability is another factor that differentiates port 25 and port 587. While both ports are capable of delivering emails, the conditions under which they operate can affect their performance. Port 25 is often subject to restrictions imposed by internet service providers, which can block or limit its use. This can lead to delivery failures or delays, especially for client-based email submission.
Port 587, on the other hand, is أقل likely to be blocked because it is recognized as the standard port for secure email submission. This makes it a more reliable option for sending messages from user devices. By using port 587, organizations can reduce the risk of delivery issues and ensure that their emails reach their intended recipients.
Reliability also extends to system monitoring and troubleshooting. Because port 587 requires authentication, it provides better visibility into email activity. Administrators can track usage patterns, identify potential issues, and اتخاذ corrective actions more effectively.
Best Practices for Configuring Email Systems
To maximize the benefits of both ports, it is important to follow best practices when configuring email systems. For most scenarios, port 587 should be used for client-to-server communication, while port 25 should be reserved for server-to-server relaying. This separation helps optimize performance and enhances security.
Encryption should always be enabled when using port 587. Protocols such as TLS provide a secure channel for data transmission, protecting sensitive information from unauthorized access. Authentication mechanisms should also be implemented to ensure that only authorized users can send emails.
For systems that עדיין rely on port 25, additional safeguards should be put in place. These may include restricting access to trusted IP addresses, monitoring traffic for suspicious activity, and implementing spam filtering solutions. By taking these steps, organizations can mitigate the risks associated with unencrypted communication.
Common Misconfigurations and How to Avoid Them
Misconfiguration is a common issue that can undermine the security and functionality of email systems. One frequent mistake is using port 25 for client email submission, which exposes data to potential interception and increases the risk of abuse. Another issue is failing to enable encryption on port 587, which negates its security advantages.
Incorrect authentication settings can also cause problems. If authentication is not properly configured, users may be unable to send emails, or unauthorized individuals may gain access to the system. Ensuring that credentials are securely managed and regularly updated is essential for maintaining system integrity.
Firewalls and network policies must also be carefully configured to allow the appropriate traffic while blocking unauthorized access. By regularly reviewing and updating these settings, administrators can prevent issues and maintain a secure and efficient email environment.
The Growing Importance of Secure Communication Standards
As digital communication continues to expand, the importance of secure standards becomes increasingly evident. Email remains one of the most widely used forms of communication, making it a prime target for cyber threats. Ensuring that messages are transmitted securely is essential for protecting both individuals and organizations.
The adoption of port 587 reflects a broader commitment to security in the digital age. By prioritizing encryption and authentication, modern email systems can provide a safer and more reliable communication experience. This shift not only protects users but also helps maintain trust in the technology that underpins global connectivity.
Understanding the differences between port 25 and port 587 is a key part of this process. By applying best practices and staying informed about evolving standards, users and administrators can ensure that their email systems remain secure, efficient, and resilient in the face of emerging challenges.
Evaluating Security Priorities in Email Communication
When deciding between port 25 and port 587, security should always be the central consideration. Email is no longer just a casual communication tool; it carries sensitive business data, personal information, authentication credentials, and confidential discussions. In such an environment, relying on unprotected transmission methods introduces unnecessary risk. Port 587 addresses this concern by enforcing encryption and authentication, ensuring that messages are protected أثناء transit.
Organizations today operate in a threat landscape where data interception, spoofing, and unauthorized access are common concerns. Choosing a secure port is not simply a technical decision but a strategic one that directly impacts data integrity and trust. Port 587 aligns with modern expectations of privacy and security, making it the preferred option for most use cases.
When Port 25 Still Makes Sense
Despite its limitations, port 25 is not entirely obsolete. It still serves a specific and গুরুত্বপূর্ণ purpose in server-to-server communication. When one mail server needs to transfer messages to another, port 25 remains the standard channel for this relay process. This function is deeply embedded in how email systems operate globally and cannot be easily replaced.
There are also controlled environments where port 25 may still be acceptable. For example, internal networks that do not expose traffic to the public internet might use port 25 for simplicity. In such cases, the risk is reduced because the communication occurs within a trusted boundary. However, even in these scenarios, many organizations are gradually transitioning toward encrypted alternatives to maintain consistency and future readiness.
When Port 587 Becomes Essential
Port 587 becomes essential whenever email is sent from a user device or application to a mail server. This includes everyday activities such as sending emails from a desktop client, a mobile device, or a web-based interface. In all these cases, the need for authentication and encryption makes port 587 the clear choice.
It is particularly important in environments where sensitive information is exchanged. Businesses dealing with financial transactions, healthcare data, or customer records cannot afford to risk unencrypted communication. Port 587 ensures that such data remains protected, meeting both security expectations and regulatory requirements.
Additionally, many internet service providers block port 25 for outbound traffic, making port 587 not just the safer option but also the more practical one. This widespread support reinforces its role as the standard for modern email submission.
Impact of Regulatory and Compliance Requirements
Regulatory frameworks around the world increasingly emphasize the importance of data protection. Organizations are required to implement measures that safeguard user information and prevent unauthorized access. Email systems are a critical part of this responsibility क्योंकि they often handle sensitive communications.
Using secure ports like 587 يساعد organizations meet these requirements by ensuring that data is encrypted and authenticated أثناء transmission. Failure to adopt such practices can result in compliance violations, financial penalties, and reputational damage. As a result, the shift toward secure email communication is not just a best practice but often a legal necessity.
Compliance also drives the adoption of additional security measures, such as logging, monitoring, and auditing. These practices are easier to implement with port 587 because it provides better visibility into user activity through authentication mechanisms.
Performance and Efficiency Considerations
While security is the primary concern, performance also plays a role in choosing the right SMTP port. Port 25, being older and less restricted in its original design, can sometimes appear faster in controlled environments. However, this advantage is often outweighed by the limitations imposed by modern networks, such as blocking and filtering.
Port 587, although slightly more complex due to encryption and authentication processes, offers more consistent performance in real-world scenarios. Because it is widely supported and rarely blocked, it обеспечивает reliable delivery across different networks and devices. This reliability is crucial for maintaining smooth communication, especially in business settings where delays can have significant consequences.
Modern hardware and optimized protocols have minimized the performance overhead associated with encryption, making port 587 both secure and efficient. As a result, the trade-off between security and speed is no longer a major concern.
Strategic Approach to Port Configuration
A well-designed email system uses both ports strategically rather than treating them as direct competitors. Port 587 should be configured for all client-to-server communication, ensuring that every message sent by users is authenticated and encrypted. Port 25, on the other hand, should be reserved for controlled server-to-server interactions where its functionality is required.
This approach allows organizations to leverage the strengths of each port while minimizing their weaknesses. By clearly defining their roles, administrators can create a more secure and efficient email infrastructure. Firewalls and network policies should be configured to enforce this separation, allowing only the necessary traffic on each port.
Regular audits and updates are also essential to maintain this configuration. As technology evolves, new vulnerabilities and best practices emerge, requiring continuous adaptation. A proactive approach ensures that the system remains secure and compliant over time.
Future Trends in Email Security and Protocols
The evolution of email communication is ongoing, with new technologies लगातार emerging to enhance security and performance. While SMTP remains the foundation, additional layers of protection are being developed to address modern challenges. These include advanced encryption standards, stricter authentication protocols, and improved spam detection mechanisms.
Port 587 is likely to remain a central component of this المستقبل because it بالفعل supports many of these advancements. Its design allows for integration with new security features, making it adaptable to changing requirements. Meanwhile, the role of port 25 may continue to diminish as alternative methods for server communication are explored.
The المستقبل of email will likely involve greater automation, smarter filtering, and more robust security frameworks. Understanding current standards, including the use of ports 25 and 587, provides a strong foundation for adapting to these changes.
Practical Decision-Making for Different Use Cases
Choosing the right port ultimately depends on the specific needs of the environment. For individual users and most organizations, port 587 is the default choice because it يوفر the necessary security and compatibility. It works seamlessly with modern email clients and services, ensuring a smooth and protected communication experience.
Port 25 should be used selectively, primarily for server-level operations where its functionality is ضروری. Even in these cases, additional safeguards should be implemented to reduce risk. By carefully evaluating the requirements of each scenario, administrators can make informed decisions that balance security, performance, and compatibility.
Understanding these use cases helps prevent common mistakes and ensures that email systems are configured correctly from the start. It also reduces the likelihood of issues related to blocked ports, failed deliveries, or security breaches.
Final Thoughts
The comparison between port 25 and port 587 reflects the broader evolution of email communication from simplicity to security. Port 25 represents the original approach, যেখানে functionality was prioritized over protection. Port 587, in contrast, embodies modern standards that emphasize encryption, authentication, and reliability.
For most practical purposes, port 587 is the right choice. It يوفر a secure and efficient way to send emails, meeting the demands of today’s دیجٹل landscape. Port 25 still has its place in specific scenarios, but its role is increasingly limited to backend operations.
A clear understanding of these differences allows users and administrators to build more secure and effective email systems. By adopting best practices and staying informed about emerging trends, it is possible to ensure that email communication remains both reliable and protected in an ever-changing technological environment.