Subnetting is a core concept in computer networking that plays a vital role in how modern networks are structured and managed. At its simplest, subnetting is the method of dividing a large network into smaller, more manageable pieces known as subnets. This division is not random but carefully planned to improve efficiency, conserve IP address space, and enhance security. When networks were first developed, IP addresses were assigned without much restriction, which led to rapid exhaustion of available addresses. Subnetting emerged as a solution to this problem, allowing administrators to use address space more intelligently while maintaining organized communication between devices.
In real-world networking environments, subnetting is used everywhere—from small office setups to large enterprise infrastructures. By breaking a network into smaller segments, administrators can control traffic flow, reduce congestion, and isolate issues more effectively. It also allows for better implementation of security policies, as each subnet can be treated as its own controlled environment. Understanding subnetting is essential for anyone involved in IT, networking, or cybersecurity because it forms the backbone of efficient network design.
The Structure of IPv4 Addresses
To fully understand subnetting, it is necessary to first grasp how IPv4 addresses are structured. An IPv4 address is a 32-bit numerical label assigned to each device connected to a network. This address is typically written in a human-readable format known as dotted decimal notation, which consists of four numbers separated by periods, such as 192.168.1.20. Each of these numbers represents an 8-bit segment called an octet.
Each octet can range from 0 to 255, which might seem arbitrary at first. However, this range exists because each octet is composed of 8 bits, and the maximum value that can be represented with 8 bits in binary is 255. When all bits in an octet are set to 1, the value becomes 255. This binary structure is fundamental to how subnetting works, as it allows network engineers to manipulate bits to create different subnet configurations.
The full IPv4 address, when expressed in binary form, consists of 32 ones and zeros. For example, the address 255.255.255.255 in binary appears as a continuous sequence of 32 ones. This binary representation is not typically used in everyday tasks, but it becomes crucial when calculating subnet masks and determining network boundaries.
Binary Basics and Their Role in Networking
Binary is the language of computers, and understanding it is essential for subnetting. Each bit in an octet represents a specific value based on its position. These values follow a pattern: 128, 64, 32, 16, 8, 4, 2, and 1. When a bit is set to 1, its corresponding value is included in the total; when it is set to 0, it is excluded.
For example, the binary number 10000001 represents the values 128 and 1. Adding these together gives a decimal value of 129. This process of converting binary to decimal is fundamental when working with IP addresses, as it helps in understanding how subnet masks operate.
When all bits in an octet are set to 1, the result is 255, which is the highest possible value for that octet. Conversely, when all bits are set to 0, the value is 0. By combining different patterns of ones and zeros, a wide range of values can be created, forming the basis of IP addressing and subnetting.
Network and Host Portions of an IP Address
An IP address is divided into two main parts: the network portion and the host portion. The network portion identifies the specific network to which a device belongs, while the host portion identifies the individual device within that network. This division is essential for routing data across networks, as it allows routers to determine where to send packets of information.
A helpful way to think about this is by comparing it to a postal address. The network portion is similar to the city, state, and postal code, which identify the general location. The host portion is like the street name and house number, which pinpoint the exact destination. Without this structure, it would be impossible to efficiently deliver data across complex networks.
The boundary between the network and host portions is defined by a subnet mask. This mask indicates how many bits of the IP address are used for the network and how many are reserved for hosts. By adjusting this boundary, network administrators can create subnets of varying sizes to meet specific needs.
Introduction to Subnet Masks and CIDR Notation
Subnet masks are used to define which part of an IP address represents the network and which part represents the host. A subnet mask is also a 32-bit number, typically written in dotted decimal format, such as 255.255.255.0. In this example, the first three octets are used for the network, while the last octet is used for hosts.
Another common way to represent subnet masks is through CIDR notation, which uses a slash followed by the number of bits allocated to the network portion. For instance, a subnet mask of 255.255.255.0 is equivalent to /24, meaning that 24 bits are used for the network. This notation is widely used because it is concise and easier to work with in many scenarios.
Different subnet masks allow for different numbers of hosts and subnets. A /8 mask uses only the first octet for the network, leaving a large number of bits available for hosts. A /16 mask uses two octets for the network, while a /24 mask uses three. These standard masks are commonly used because they provide a balance between network size and manageability.
How Subnetting Improves Network Efficiency
Subnetting significantly enhances the efficiency of a network by reducing unnecessary traffic. In a large network without subnets, every device receives broadcast messages, even if they are not relevant. This can lead to congestion and decreased performance. By dividing the network into smaller subnets, broadcast traffic is limited to each subnet, improving overall efficiency.
Another advantage of subnetting is better utilization of IP address space. Instead of assigning a large block of addresses to a single network, subnetting allows administrators to allocate smaller blocks based on actual needs. This prevents wastage and ensures that addresses are used more effectively.
Subnetting also improves security by isolating different parts of a network. For example, sensitive systems can be placed in a separate subnet, making it easier to control access and monitor activity. This segmentation is a key component of modern network security strategies.
Practical Example of Network and Host Allocation
Consider a network with the address 172.16.56.0 using a /24 subnet mask. In this case, the first three octets (172.16.56) represent the network portion, while the last octet is used for hosts. Devices within this network might have addresses such as 172.16.56.40, 172.16.56.55, or 172.16.56.100.
All these devices share the same network portion, which allows them to communicate directly with each other. The host portion differentiates each device, ensuring that data is delivered to the correct destination. With a /24 mask, there are 256 possible addresses in total, but two are reserved for network and broadcast purposes, leaving 254 usable addresses for devices.
This example illustrates how subnetting defines the structure of a network and determines how many devices can be connected. By adjusting the subnet mask, administrators can create networks that are tailored to specific requirements.
Expanding Beyond Default Subnet Masks
While standard subnet masks like /8, /16, and /24 are commonly used, they are not always sufficient for modern networking needs. Subnetting allows administrators to go beyond these defaults by borrowing bits from the host portion to create additional subnets. This process is often referred to as “bit borrowing.”
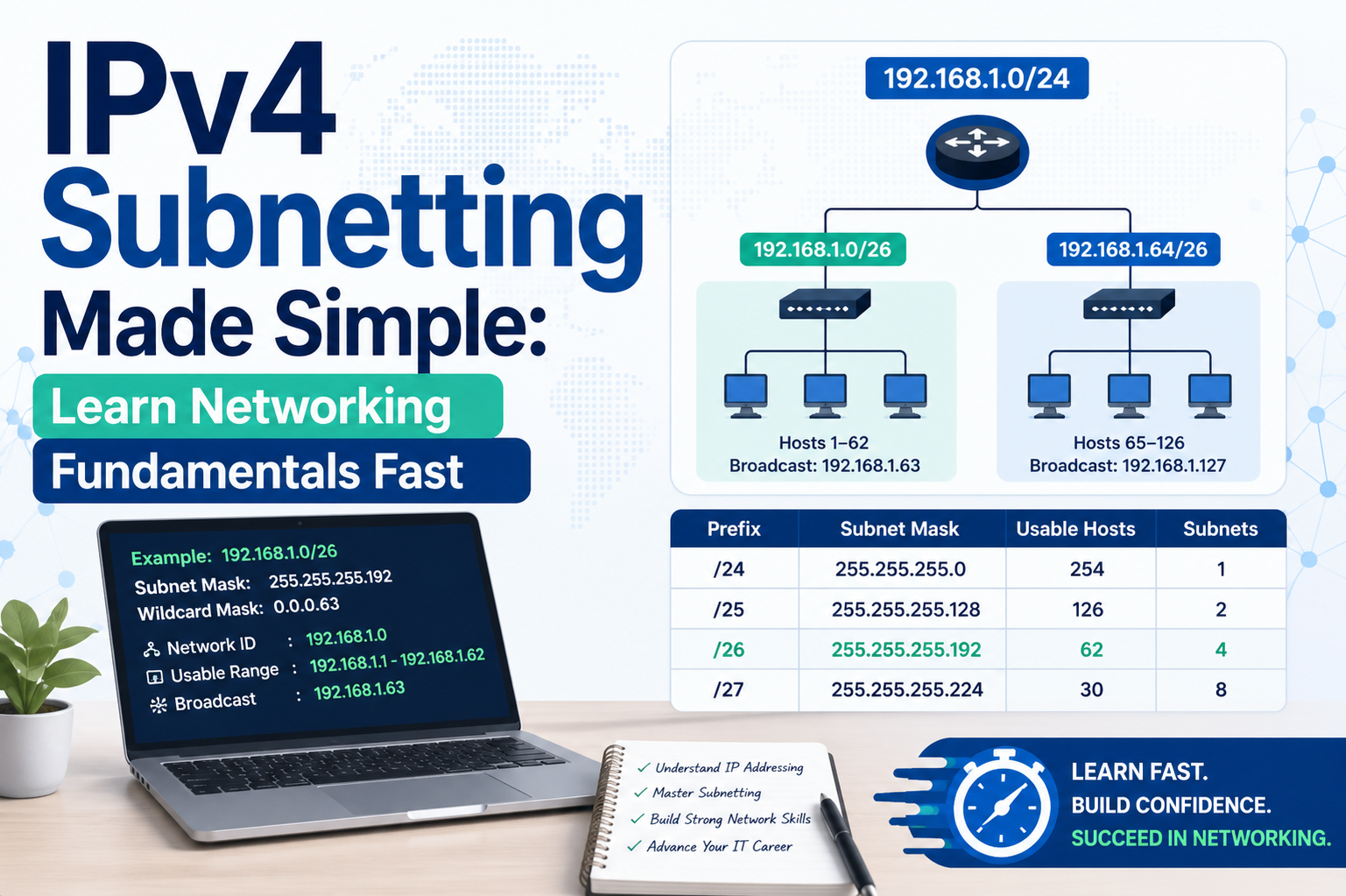
For instance, changing a /24 network to a /26 mask increases the number of subnets while reducing the number of hosts per subnet. This trade-off is a fundamental aspect of subnetting. By carefully choosing the number of network bits, administrators can balance the need for multiple subnets with the requirement for sufficient host addresses.
This flexibility is what makes subnetting such a powerful tool. It allows networks to be customized to fit a wide range of scenarios, from small local networks to large-scale enterprise systems. Understanding how to manipulate subnet masks is a critical skill for anyone working in networking.
Deeper Insight into Subnet Masks and Bit Allocation
Subnet masks are the foundation of subnetting, and understanding how they function at a deeper level is essential for mastering IPv4 networking. A subnet mask works by separating the network portion of an IP address from the host portion using binary values. In this binary structure, all bits set to 1 represent the network, while all bits set to 0 represent the host. This simple rule allows devices and routers to quickly determine which part of an address identifies the network and which part identifies a specific device.
When you look at a subnet mask like 255.255.255.0, what you are really seeing is a translation of binary values into decimal format. Each 255 corresponds to an octet of all ones in binary, while 0 corresponds to all zeros. This means that in a /24 subnet, the first 24 bits are reserved for the network, and the remaining 8 bits are used for hosts. The elegance of this system lies in its simplicity, as it allows network engineers to manipulate address boundaries by simply adjusting the number of bits allocated to each portion.
Understanding Bit Borrowing in Subnetting
Bit borrowing is a critical concept that explains how subnetting actually creates multiple smaller networks from a single larger one. When you borrow bits, you take bits from the host portion of an IP address and allocate them to the network portion. This increases the number of possible subnets but reduces the number of hosts available in each subnet.
For example, if you start with a /24 network and borrow one bit, you create a /25 subnet. This effectively splits the original network into two smaller subnets. Borrowing another bit creates a /26 subnet, resulting in four smaller subnets. Each time you borrow a bit, the number of subnets doubles, while the number of hosts per subnet is cut roughly in half.
This trade-off is central to subnetting design. Network administrators must carefully decide how many bits to allocate to the network portion based on the number of required subnets and the number of devices in each subnet. Too many subnets with too few hosts can limit scalability, while too few subnets can lead to inefficient address usage and increased broadcast traffic.
Calculating the Number of Subnets and Hosts
One of the most practical skills in subnetting is calculating how many subnets and hosts are available for a given subnet mask. This calculation is based on the number of bits used for subnetting and the number of bits remaining for hosts.
The number of subnets is determined by raising 2 to the power of the number of borrowed bits. For example, borrowing 3 bits results in 2³, or 8 subnets. On the other hand, the number of hosts per subnet is calculated by raising 2 to the power of the remaining host bits and then subtracting 2. The subtraction accounts for the network address and the broadcast address, which cannot be assigned to devices.
This mathematical relationship highlights the balance between subnets and hosts. As you increase the number of subnets, the number of hosts per subnet decreases. Understanding this balance is essential for designing efficient networks that meet both current and future needs.
The Concept of Network and Broadcast Addresses
Every subnet has two special addresses that cannot be assigned to devices: the network address and the broadcast address. The network address is the first address in the subnet and represents the subnet itself. It is used by routers to identify the network and is not assigned to any device.
The broadcast address, on the other hand, is the last address in the subnet. It is used to send data to all devices within the subnet simultaneously. When a broadcast message is sent, every device in the subnet receives it, which can be useful for certain types of communication but can also lead to increased traffic if not managed properly.
For example, in a /24 subnet, the network address might be 192.168.1.0, and the broadcast address would be 192.168.1.255. The usable host addresses would fall between these two values. Recognizing these special addresses is crucial when assigning IP addresses to devices, as using them incorrectly can cause network issues.
Exploring Variable Length Subnet Masking (VLSM)
Variable Length Subnet Masking, commonly known as VLSM, is an advanced subnetting technique that allows for even greater flexibility in network design. Instead of using a single subnet mask for an entire network, VLSM allows different subnets to have different masks based on their specific requirements.
This approach is particularly useful in real-world scenarios where different parts of a network have varying numbers of devices. For example, a department with many users might require a larger subnet, while a smaller department might only need a few IP addresses. By using VLSM, administrators can allocate address space more efficiently, ensuring that no addresses are wasted.
VLSM is widely used in modern networking because it supports hierarchical addressing and efficient route aggregation. It also plays a key role in optimizing the use of limited IPv4 address space, which has become increasingly important as the number of connected devices continues to grow.
Understanding Classful Addressing and Its Limitations
Before the introduction of CIDR and advanced subnetting techniques, IP addressing was based on a classful system. In this system, IP addresses were divided into classes A, B, and C, each with a fixed number of network and host bits. While this approach simplified address allocation, it was not very efficient.
Class A networks provided a massive number of host addresses but were limited in number, making them suitable only for very large organizations. Class B networks offered a moderate number of hosts, while Class C networks were designed for smaller networks. However, many organizations found that these fixed sizes did not match their actual needs, leading to wasted address space.
Subnetting and CIDR were introduced to overcome these limitations by allowing more flexible allocation of IP addresses. Instead of being restricted to predefined classes, administrators could define their own subnet sizes, making it possible to use address space more efficiently.
The Role of CIDR in Modern Networking
Classless Inter-Domain Routing, or CIDR, revolutionized the way IP addresses are allocated and routed. Unlike classful addressing, CIDR does not rely on fixed classes. Instead, it uses a prefix length to define the network portion of an address, allowing for more precise and efficient allocation.
CIDR notation, such as /24 or /27, indicates the number of bits used for the network portion of the address. This flexibility allows networks to be divided into subnets of virtually any size, making it easier to match address allocation with actual requirements. CIDR also enables route aggregation, which reduces the size of routing tables and improves overall network performance.
The adoption of CIDR has been instrumental in extending the lifespan of IPv4 by slowing the depletion of available addresses. It remains a fundamental concept in networking and is used extensively in both IPv4 and IPv6 environments.
Real-World Applications of Subnetting
Subnetting is not just a theoretical concept; it has practical applications in everyday networking scenarios. In corporate environments, subnetting is used to separate different departments, such as finance, human resources, and IT, into distinct networks. This separation improves security and makes it easier to manage network resources.
In educational institutions, subnetting allows different labs or departments to operate independently while still being part of a larger network. Internet service providers also rely heavily on subnetting to allocate IP addresses to customers efficiently and manage large-scale networks.
Introduction to Advanced Subnetting Concepts
As networking environments grow in complexity, subnetting evolves from a basic concept into a powerful design tool that enables scalability, performance optimization, and structured communication. In earlier discussions, subnetting was introduced as a way to divide networks and manage IP address space efficiently. At a more advanced level, subnetting becomes a strategic approach that influences how data flows, how networks are secured, and how systems scale over time.
Modern networks are rarely flat structures. Instead, they are layered and segmented, often spanning multiple geographic locations and supporting a wide range of devices. Subnetting helps create this structure by allowing administrators to logically group devices based on function, location, or security requirements. These groupings are not just convenient—they are essential for maintaining performance and ensuring that networks remain manageable as they grow.
The Importance of Block Size in Subnetting
One of the most practical concepts in advanced subnetting is understanding block size, sometimes referred to as the increment. Block size determines how IP addresses are grouped within a subnet and plays a key role in identifying subnet ranges. It is derived directly from the subnet mask and provides a quick way to calculate where each subnet begins and ends.
For example, when working with a /27 subnet mask, the last octet of the mask is 224. The block size can be calculated by subtracting this value from 256, resulting in a block size of 32. This means that subnets will start at intervals of 32 within the final octet, such as 0, 32, 64, 96, and so on. Each of these values represents the beginning of a new subnet.
Understanding block size allows network professionals to quickly determine the range of IP addresses within a subnet without performing complex binary calculations. It simplifies the process of identifying valid host ranges, network addresses, and broadcast addresses, making subnetting more efficient and less error-prone.
Determining Subnet Ranges and Boundaries
Once the block size is known, identifying subnet ranges becomes much easier. Each subnet begins at a multiple of the block size and extends up to the next multiple minus one. The first address in the range is the network address, and the last address is the broadcast address. All addresses in between are available for host assignment.
For instance, with a block size of 32, the subnet starting at 64 would include addresses from 64 to 95. In this range, 64 is the network address, 95 is the broadcast address, and the usable host addresses fall between these two values. This pattern repeats consistently across the entire address space, making it predictable and easy to work with once the concept is understood.
This method of identifying subnet boundaries is especially useful when analyzing IP addresses to determine which subnet they belong to. By comparing the address to the known block ranges, administrators can quickly identify the correct subnet without needing to convert the entire address into binary form.
Working with a Practical Subnetting Example
Consider the IP address 43.17.255.71 with a /27 subnet mask. From the mask, it is clear that 27 bits are used for the network portion, leaving 5 bits for hosts. This configuration results in a block size of 32 in the final octet.
To determine the subnet in which this IP address resides, focus on the last octet, which is 71. By examining the block size intervals—0, 32, 64, 96, and so on—it becomes evident that 71 falls between 64 and 96. Therefore, the subnet address is 43.17.255.64.
This approach demonstrates how subnetting can be applied in real scenarios to quickly identify network segments. It eliminates the need for lengthy calculations and provides a straightforward method for analyzing IP addresses in both small and large networks.
Subnetting and Network Hierarchy Design
Subnetting is not only about dividing networks but also about creating a logical hierarchy. In large organizations, networks are often structured in layers, such as core, distribution, and access layers. Subnetting supports this design by allowing each layer to have its own set of subnets tailored to its specific role.
For example, the core layer might use larger subnets to handle high volumes of traffic, while the access layer might use smaller subnets to connect individual devices. This hierarchical approach improves performance by reducing unnecessary traffic and ensures that each part of the network operates efficiently.
Hierarchy also simplifies troubleshooting and management. When a problem occurs, administrators can quickly isolate it to a specific subnet or layer, reducing downtime and improving overall reliability. This structured approach is essential for maintaining complex networks in enterprise environments.
Route Summarization and Its Relationship with Subnetting
Route summarization, also known as route aggregation, is closely related to subnetting and plays a crucial role in optimizing network performance. It involves combining multiple subnet routes into a single summary route, reducing the number of entries in routing tables.
For example, instead of listing multiple subnets individually, a router can use a summarized route that represents all of them. This reduces the amount of memory required for routing tables and speeds up the process of routing decisions. Subnetting makes this possible by allowing networks to be designed with contiguous address ranges that can be easily aggregated.
Efficient route summarization depends on careful subnet planning. If subnets are not organized properly, it may not be possible to aggregate them effectively, leading to larger routing tables and reduced performance. This highlights the importance of strategic subnetting in network design.
Subnetting in Large-Scale Enterprise Networks
In large-scale enterprise environments, subnetting becomes a critical component of network architecture. Organizations often have multiple departments, locations, and services that require separate network segments. Subnetting allows these segments to coexist within a unified addressing scheme while maintaining independence.
For instance, a company might assign different subnets to its finance, marketing, and IT departments. Each subnet can have its own security policies, access controls, and performance settings. This segmentation not only improves efficiency but also enhances security by limiting the scope of potential threats.
Additionally, subnetting supports scalability. As the organization grows, new subnets can be added without disrupting existing ones. This flexibility is essential for adapting to changing business needs and technological advancements.
Common Challenges and Mistakes in Subnetting
Despite its advantages, subnetting can be challenging, especially for beginners. One common mistake is miscalculating the number of hosts or subnets required, leading to inefficient address allocation. Another issue is incorrectly identifying network and broadcast addresses, which can cause connectivity problems.
Overlapping subnets are another frequent problem. This occurs when two subnets share the same address range, leading to conflicts and routing issues. Proper planning and careful calculation are necessary to avoid such situations.
Another challenge is maintaining consistency in subnet design. Without a clear plan, networks can become disorganized, making them difficult to manage and troubleshoot. Using standardized addressing schemes and documenting subnet allocations can help prevent these issues.
The Evolution Toward IPv6 and the Role of Subnetting
While IPv4 subnetting remains widely used, the transition to IPv6 is gradually changing the landscape of networking. IPv6 offers a vastly larger address space, reducing the need for strict address conservation. However, subnetting is still relevant, as it provides structure and organization within IPv6 networks.
In IPv6, subnetting is often simpler due to the abundance of available addresses, but the principles remain the same. Networks are divided into smaller segments to improve performance, security, and manageability. Understanding IPv4 subnetting provides a strong foundation for learning IPv6, as many of the concepts carry over.
As networks continue to evolve, subnetting will remain a fundamental skill for network professionals. Its ability to optimize address usage, enhance security, and support scalable design ensures its continued importance in both current and future networking environments.
Even in home networks, subnetting plays a role, although it is often handled automatically by routers. Understanding how subnetting works can help users troubleshoot connectivity issues and optimize their network performance.
Applying Subnetting Skills in Real Network Design
When subnetting moves from theory into real-world implementation, it becomes a practical tool that shapes how networks are built and maintained. Network designers rarely work with abstract numbers alone; instead, they plan addressing schemes that align with business needs, user distribution, and expected growth. Subnetting allows administrators to create structured environments where devices are grouped logically, making communication more efficient and predictable.
In a typical organization, different departments often require separate network segments. For example, administrative systems, employee workstations, and guest devices are usually placed in distinct subnets. This separation ensures that traffic remains controlled and that sensitive systems are not unnecessarily exposed. Subnetting also enables the use of access control mechanisms, where rules can be applied to limit or allow communication between subnets based on organizational policies.
Planning a subnetting scheme involves estimating how many devices will be connected in each segment and allocating address space accordingly. If a department is expected to grow, its subnet should include enough host addresses to accommodate future expansion. This forward-thinking approach prevents the need for frequent redesigns and ensures that the network remains stable over time.
Efficient Address Allocation Strategies
Efficient use of IPv4 address space is one of the primary reasons subnetting is so important. Because IPv4 addresses are limited, careful allocation is necessary to avoid waste. Instead of assigning large blocks of addresses that may never be fully used, subnetting allows administrators to divide address space into smaller, purpose-driven segments.
One common strategy is to allocate subnets based on actual requirements rather than fixed sizes. For example, a small office with only a few devices might use a subnet with a limited number of host addresses, while a larger department would receive a bigger subnet. This method ensures that addresses are not left unused while still providing enough capacity for each segment.
Another important consideration is address alignment. Keeping subnets aligned in a logical and sequential manner makes it easier to manage and troubleshoot the network. When subnets follow a predictable pattern, administrators can quickly identify issues and understand how different parts of the network are connected.
Troubleshooting Networks Using Subnet Knowledge
Subnetting knowledge becomes especially valuable when diagnosing network problems. Many connectivity issues can be traced back to incorrect IP configurations, such as mismatched subnet masks or devices assigned to the wrong subnet. By understanding how subnetting works, administrators can quickly identify and resolve these issues.
For example, if two devices are unable to communicate, one of the first things to check is whether they are in the same subnet. If they are not, a router is required to facilitate communication between them. Misconfigured subnet masks can also lead to situations where devices believe they are on the same network when they are not, causing data to be sent incorrectly.
Subnetting also helps in analyzing routing problems. Routers rely on network addresses to determine where to send data, and incorrect subnetting can lead to inefficient or failed routing. By examining subnet structures and address ranges, administrators can pinpoint where communication is breaking down and take corrective action.
Security Benefits of Network Segmentation
One of the most significant advantages of subnetting is its contribution to network security. By dividing a network into smaller segments, administrators can control how data flows between different parts of the system. This segmentation reduces the risk of unauthorized access and limits the spread of potential threats.
For instance, if a security breach occurs in one subnet, it can be contained within that segment rather than affecting the entire network. Sensitive systems, such as databases or financial applications, can be placed in isolated subnets with strict access controls. This layered approach to security is a fundamental principle in modern network design.
Subnetting also supports the implementation of firewalls and intrusion detection systems. These tools can be configured to monitor and filter traffic between subnets, providing an additional layer of protection. By combining subnetting with security technologies, organizations can create robust defenses against a wide range of threats.
Subnetting in Cloud and Virtualized Environments
As technology evolves, subnetting continues to play a crucial role in cloud computing and virtualized networks. In these environments, networks are often created and managed through software, but the underlying principles of subnetting remain the same. Virtual networks are divided into subnets to organize resources, control traffic, and enforce security policies.
Cloud service providers allow users to define their own subnet structures, giving them flexibility in how they design their networks. For example, a cloud-based application might use separate subnets for web servers, application servers, and databases. This separation improves performance and ensures that each component operates within its own controlled environment.
Virtualization also benefits from subnetting by enabling efficient resource allocation. Virtual machines can be grouped into subnets based on their roles, making it easier to manage communication and apply network policies. Despite the differences in implementation, the core concepts of subnetting remain consistent across physical and virtual environments.
Preparing for Advanced Networking Concepts
Mastering IPv4 subnetting provides a strong foundation for exploring more advanced networking topics. Concepts such as routing protocols, network address translation, and traffic engineering all rely on a solid understanding of how IP addresses are structured and divided. Subnetting is often one of the first major challenges for learners, but it is also one of the most rewarding skills to develop.
As networks become more complex, the ability to quickly analyze and design subnet structures becomes increasingly valuable. Professionals who are comfortable with subnetting can adapt to a wide range of scenarios, from configuring small local networks to managing large enterprise infrastructures. This skill also prepares learners for transitioning to newer technologies, including IPv6, where similar principles are applied on a larger scale.
Conclusion
IPv4 subnetting is far more than a technical exercise; it is a fundamental practice that underpins modern networking. By dividing networks into smaller, manageable segments, subnetting improves efficiency, enhances security, and ensures that IP address space is used effectively. From understanding binary structures to calculating subnet ranges and designing scalable architectures, each aspect of subnetting contributes to building reliable and organized networks.
Throughout this discussion, the progression from basic concepts to advanced applications highlights the versatility of subnetting. It begins with simple ideas like dividing an address into network and host portions and extends to complex strategies used in enterprise and cloud environments. This progression demonstrates how a strong grasp of fundamentals can lead to mastery of more sophisticated networking techniques.
Ultimately, subnetting empowers network professionals to take control of their infrastructure. It provides the tools needed to design networks that are not only functional but also efficient, secure, and adaptable. As technology continues to evolve, the principles of subnetting will remain a cornerstone of networking knowledge, guiding the development of future systems and ensuring that communication across networks remains seamless and effective.