Every digital interaction—sending an email, loading a website, or joining a video call—depends on a network quietly doing its job in the background. At the heart of every network, no matter its size or complexity, are three essential components: switches, routers, and firewalls. These are not just pieces of hardware with blinking lights; they are specialized systems that control how data flows, where it goes, and whether it should be allowed through at all. Understanding these components is the first real step toward mastering networking, whether for practical work, troubleshooting, or certifications from organizations like Cisco Systems.
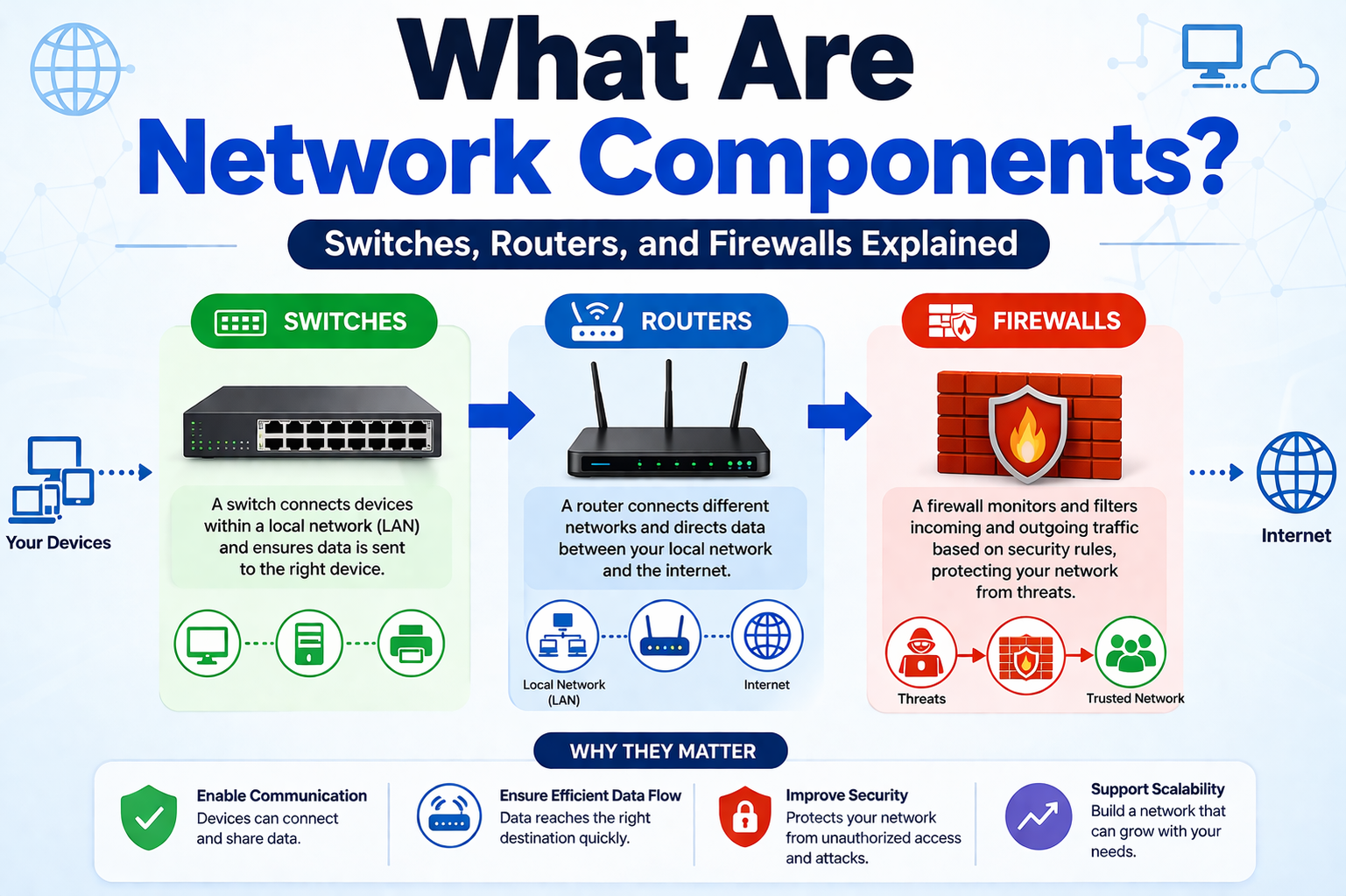
A network is essentially a structured environment where devices communicate. Without structure, communication would collapse into chaos. These three components provide that structure by dividing responsibilities: switches manage communication within a network, routers connect different networks, and firewalls enforce security. Each plays a unique role, but their real power comes from how they operate together.
Why Networks Rely on Specialized Components
It might seem tempting to imagine a single device handling everything in a network, but that approach would quickly become inefficient and insecure. Networks require specialization because the tasks involved—data forwarding, addressing, and security inspection—are fundamentally different. Switches excel at local communication because they operate quickly and efficiently using hardware-level identifiers. Routers are designed to make decisions about where data should go beyond the local environment. Firewalls, meanwhile, focus entirely on protecting the network by filtering and analyzing traffic.
By separating these responsibilities, networks become faster, more scalable, and far more secure. This layered design also makes troubleshooting easier. If something goes wrong, you can narrow the issue down to switching, routing, or security rather than guessing blindly.
How Data Moves Through a Network Environment
To understand why switches, routers, and firewalls matter, you need to think about how data actually travels. Every piece of information sent across a network is broken into small chunks called packets. These packets contain both the data and addressing information that tells the network where they should go.
When you send a request—like opening a website—your device creates packets and sends them into the network. Those packets first reach a switch, which determines where within the local network they should go. If the destination is outside the local network, the packets are forwarded to a router. The router then determines the best path to the destination network. Before leaving or entering your network, the packets are inspected by a firewall, which decides whether they are safe.
This journey happens in milliseconds, yet it involves multiple decisions and checks. Without switches, routers, and firewalls working together, this process would break down completely.
The Role of Switches in Local Communication
Switches are responsible for connecting devices within the same network. Think of them as coordinators that ensure messages reach the correct recipient inside a local environment, such as an office or home network. When a device connects to a switch, the switch learns its identity using something called a MAC address. This address is unique to each device and acts like a fingerprint on the network.
Instead of broadcasting data to every device, a switch sends it only to the intended recipient. This makes communication faster and reduces unnecessary traffic. The efficiency of switches is one of the main reasons modern networks can handle so many devices at once without slowing down.
Switches operate primarily at the data link layer of the OSI model, often referred to as Layer 2. This layer focuses on direct device-to-device communication within the same network. Because of this, switches are extremely fast—they rely on hardware-based processing rather than complex calculations.
Understanding MAC Addresses and Device Identification
Every device connected to a network has a MAC address embedded in its network interface card. This address is critical for switches because it allows them to identify where data should be sent. When a device first connects, the switch records its MAC address in a table. Over time, this table grows, enabling the switch to quickly match incoming packets with their destinations.
This process is automatic and continuous. If a device disconnects or moves, the switch updates its table accordingly. This dynamic behavior ensures that the network remains accurate and efficient without manual intervention.
MAC-based communication is highly reliable within a local network, but it has limitations. It cannot determine paths between different networks. That’s where routers come in, which will be explored more deeply later.
Full-Duplex Communication and Network Efficiency
One of the defining features of modern switches is full-duplex communication. This means devices can send and receive data at the same time without waiting. In older systems, communication was half-duplex, where devices had to take turns transmitting. This created delays and reduced overall performance.
Full-duplex communication eliminates these delays, allowing for smoother and faster data exchange. This is especially important in environments with high traffic, such as offices with multiple users or systems handling real-time applications like video calls and online collaboration.
The ability to handle simultaneous communication is one of the reasons switches are indispensable in modern networking. It ensures that data flows continuously without bottlenecks.
Managed and Unmanaged Switches Explained
Not all switches are created equal. Some are designed for simplicity, while others offer advanced control and monitoring capabilities. Unmanaged switches are the simplest type. They are plug-and-play devices that require no configuration. You connect them, and they start working immediately. This makes them ideal for small networks or home use.
Managed switches, on the other hand, provide a higher level of control. Network administrators can configure settings, monitor traffic, and optimize performance. Features like traffic prioritization, remote management, and diagnostics make managed switches essential for larger or more complex networks.
These advanced capabilities allow administrators to detect issues, balance loads, and ensure that critical applications receive the bandwidth they need. While unmanaged switches are convenient, managed switches are necessary for environments where performance and reliability are critical.
Monitoring and Control with Network Protocols
Managed switches often rely on monitoring protocols to provide insights into network performance. These protocols allow administrators to check whether ports are active, how much data is being transmitted, and whether any issues are occurring.
This visibility is crucial in professional environments. Without it, diagnosing problems would be guesswork. With proper monitoring, administrators can identify bottlenecks, detect unusual activity, and maintain optimal performance.
The ability to monitor and control a network in real time transforms switches from simple connectors into powerful management tools.
Layer 2 and Layer 3 Switching Capabilities
While traditional switches operate at Layer 2, some advanced switches can also function at Layer 3. These Layer 3 switches combine the speed of switching with some of the routing capabilities typically associated with routers.
Layer 2 switches rely entirely on MAC addresses, which limits them to local communication. Layer 3 switches, however, can use IP addresses to make more advanced decisions. This allows them to handle tasks like routing between different segments of a network.
Despite these capabilities, Layer 3 switches do not completely replace routers. Routers are still necessary for connecting different networks and managing traffic on a larger scale. However, Layer 3 switches can significantly improve performance within complex networks by handling certain routing tasks internally.
The Importance of Hardware Acceleration in Switching
Modern switches often use specialized hardware to achieve high performance. One key technology is the use of application-specific integrated circuits, or ASICs. These chips are designed specifically for processing network data, allowing switches to operate at extremely high speeds.
Unlike general-purpose processors, ASICs are optimized for a narrow set of tasks. This makes them incredibly efficient for switching operations. As a result, switches can handle large volumes of traffic with minimal delay.
This hardware-based approach is a major reason why switches can outperform software-based systems in terms of speed and reliability. It ensures that networks can scale to meet growing demands without sacrificing performance.
Why Switches Alone Are Not Enough
While switches are essential for local communication, they cannot handle everything a network requires. Their primary limitation is that they operate within a single network. They do not determine how data should travel between different networks or reach the internet.
This limitation highlights the need for routers. Without routers, networks would remain isolated, unable to communicate with external systems. Similarly, without firewalls, networks would be vulnerable to threats.
Understanding the boundaries of what switches can and cannot do is crucial. It reinforces the idea that networking is a collaborative system where each component plays a specific role.
Preparing for Deeper Networking Concepts
Grasping the fundamentals of switches lays the groundwork for understanding more advanced networking topics. Concepts like virtual LANs, routing protocols, and network security all build on this foundation.
For anyone pursuing networking knowledge—whether for career growth or personal interest—this foundational understanding is essential. It transforms abstract ideas into practical knowledge that can be applied in real-world scenarios.
As networks continue to evolve, the role of switches remains central. They are the starting point of every data journey, ensuring that devices can communicate efficiently within a local environment.
In the next part, the focus will shift toward routers and how they extend communication beyond local networks, enabling global connectivity and more complex data routing decisions.
Understanding the Purpose of Routers in Network Communication
While switches handle communication within a local network, routers take on a much broader responsibility. A router connects one network to another, making it possible for devices in your home or office to communicate with systems across the world. Without routers, networks would remain isolated islands with no way to exchange information beyond their immediate environment.
At its core, a router is responsible for directing traffic. It examines incoming data packets, determines their destination, and decides the most efficient path to send them on their way. This decision-making process is what enables the internet to function as a massive, interconnected system rather than a collection of disconnected networks. Routers operate at the network layer of the OSI model, often referred to as Layer 3, where logical addressing and path selection take place.
How Routers Use IP Addresses to Make Decisions
Unlike switches, which rely on MAC addresses, routers use IP addresses to identify devices and networks. An IP address acts like a mailing address for a device, providing information about both the network it belongs to and the specific device within that network.
When a packet reaches a router, the router reads the destination IP address and checks its routing table. This table contains information about known networks and the best paths to reach them. Based on this information, the router forwards the packet toward its destination. If the destination is not directly connected, the router sends the packet to another router, continuing the journey until it reaches its final endpoint.
This process happens extremely quickly and is repeated millions of times every second across the internet. The ability of routers to make rapid, accurate decisions is what keeps data flowing smoothly across vast distances.
Routing Tables and Path Selection Logic
A routing table is essentially the brain of a router. It contains a list of known destinations along with the best routes to reach them. These routes can be configured manually or learned automatically through routing protocols.
When a router receives a packet, it compares the destination IP address with the entries in its routing table. It then selects the most appropriate path based on factors like distance, cost, and network conditions. This ensures that data takes the most efficient route available.
Routing tables are constantly updated to reflect changes in the network. If a path becomes unavailable, the router can quickly switch to an alternative route. This adaptability is crucial for maintaining reliable communication in dynamic network environments.
Dynamic and Static Routing Explained
Routers can use two main types of routing: static and dynamic. Static routing involves manually configuring routes. This approach is simple and predictable but requires manual updates whenever the network changes. It is often used in smaller or more stable environments where changes are infrequent.
Dynamic routing, on the other hand, uses protocols to automatically discover and maintain routes. These protocols allow routers to share information with each other, creating a constantly updated view of the network. This makes dynamic routing more flexible and scalable, especially in large or complex networks.
The choice between static and dynamic routing depends on the size and complexity of the network. In many cases, a combination of both approaches is used to balance simplicity and adaptability.
The Role of DHCP in Network Configuration
Routers often provide additional services beyond basic packet forwarding. One of the most important is Dynamic Host Configuration Protocol, commonly known as DHCP. This service automatically assigns IP addresses to devices on the network, eliminating the need for manual configuration.
When a device connects to a network, it sends a request for an IP address. The router responds by assigning an available address from a predefined range. This process happens quickly and ensures that each device has a unique identifier.
DHCP simplifies network management and reduces the risk of configuration errors. Without it, administrators would need to assign IP addresses manually, which would be time-consuming and prone to mistakes.
Connecting Local Networks to the Internet
One of the primary functions of a router is to connect a local network to the internet. This connection allows devices to access websites, send emails, and use online services. The router acts as a gateway, managing all incoming and outgoing traffic.
When a device sends a request to access a website, the router forwards that request to the appropriate destination on the internet. When the response is received, the router sends it back to the requesting device. This process is seamless from the user’s perspective but involves multiple steps and decisions behind the scenes.
The router’s ability to handle this exchange efficiently is critical for maintaining a smooth and responsive user experience.
Understanding Network Address Translation (NAT)
Network Address Translation, or NAT, is one of the most important features of modern routers. It allows multiple devices on a local network to share a single public IP address when accessing the internet. This not only conserves IP addresses but also adds a layer of abstraction between internal and external networks.
When a device sends a request to the internet, the router replaces the device’s private IP address with its own public IP address. It keeps track of this translation so that when a response is received, it can forward it to the correct device.
Without NAT, each device would need a unique public IP address, which would be impractical given the limited number of available addresses. NAT makes efficient use of resources while maintaining connectivity.
Why NAT Is Essential for Modern Networks
The importance of NAT becomes clear when you consider the number of devices connected to networks today. Homes, offices, and even small businesses can have dozens or hundreds of devices. Assigning a public IP address to each one would quickly exhaust available resources.
NAT solves this problem by allowing multiple devices to share a single address. It also provides a basic level of security by hiding internal IP addresses from external networks. This makes it more difficult for unauthorized users to directly access devices within the network.
Although NAT is not a replacement for dedicated security measures, it plays a crucial role in both efficiency and protection.
Port Address Translation and Handling Multiple Devices
When many devices share a single public IP address, the router needs a way to distinguish between them. This is where Port Address Translation, or PAT, comes into play. PAT assigns a unique port number to each connection, allowing the router to track multiple sessions simultaneously.
For example, if several devices are accessing the internet at the same time, the router uses different port numbers to keep their traffic separate. When responses are received, the router uses these port numbers to send the data to the correct device.
This process allows hundreds or even thousands of connections to be managed efficiently using a single public IP address. It is a key feature that enables modern networks to scale without running into addressing limitations.
Access Control Lists and Traffic Filtering
Routers can also control traffic using Access Control Lists, or ACLs. An ACL is a set of rules that determines which traffic is allowed or denied based on criteria such as IP addresses or protocols.
For example, an administrator might configure an ACL to block traffic from a specific IP address or to prevent certain types of data from leaving the network. These rules are applied to incoming or outgoing traffic, providing a basic level of security and control.
ACLs are considered stateless, meaning they evaluate each packet independently without considering the context of previous packets. This makes them efficient but less sophisticated than other security mechanisms.
Limitations of Router-Based Security
While routers provide useful security features like NAT and ACLs, they are not designed to handle advanced threat detection. Their primary role is to route traffic efficiently, not to perform deep inspection or complex analysis.
Because of this limitation, routers are typically used in conjunction with firewalls, which are specifically designed for security. Firewalls provide more advanced capabilities, such as stateful inspection and protocol validation, which go beyond what routers can offer.
Understanding this distinction is important when designing or managing a network. Relying solely on a router for security can leave vulnerabilities that could be exploited by malicious actors.
The Relationship Between Routers and Other Network Components
Routers do not operate in isolation. They work closely with switches and firewalls to create a complete networking solution. Switches handle local communication, routers connect different networks, and firewalls protect the entire system.
In a typical setup, devices connect to a switch, which forwards traffic to a router when it needs to leave the local network. The router then determines the best path and forwards the traffic accordingly. Before the data exits or enters the network, it is often inspected by a firewall to ensure it is safe.
This layered approach ensures that each component can focus on its specific role while contributing to the overall functionality and security of the network.
Building a Strong Foundation for Advanced Networking
Understanding routers is a critical step in mastering networking concepts. Many advanced topics, such as routing protocols, network design, and performance optimization, build on the principles covered here.
Routers are the bridge between local and global communication. They enable devices to connect not just within a single network, but across the entire internet. Their ability to make intelligent decisions about data paths is what keeps the digital world connected.
In the next part, the focus will move toward firewalls, exploring how they protect networks by analyzing and controlling traffic with a level of detail that goes far beyond basic routing.
Understanding the Critical Role of Firewalls in Network Security
As networks expand and connect to the wider internet, the need for strong security becomes unavoidable. This is where firewalls step in as one of the most important components in any network architecture. While switches focus on internal communication and routers manage connectivity between networks, firewalls are responsible for protecting the network from unwanted or malicious traffic.
A firewall acts as a gatekeeper positioned between trusted and untrusted environments. Typically, it sits between a local network and the internet, inspecting every packet that attempts to enter or leave. Its job is not just to allow or block traffic, but to make intelligent decisions based on rules, behavior, and context. Without a firewall, a network would be exposed to a wide range of threats, including unauthorized access, malware, and denial-of-service attacks.
How Firewalls Analyze and Control Network Traffic
Firewalls operate by examining data packets and comparing them against a set of predefined security rules. These rules determine whether a packet should be allowed through or blocked. Unlike simpler filtering mechanisms, firewalls can analyze multiple aspects of a packet, including its source, destination, port number, and protocol type.
When a packet arrives at the firewall, it does not pass through immediately. Instead, the firewall inspects it carefully, checking whether it matches any allowed patterns or violates any security policies. If the packet meets the criteria, it is forwarded to its destination. If not, it is dropped or rejected.
This process happens continuously and in real time, ensuring that only legitimate traffic is allowed to flow through the network. The ability to enforce such control is what makes firewalls a cornerstone of network security.
Stateful vs Stateless Traffic Inspection
One of the defining characteristics of modern firewalls is their use of stateful inspection. This approach allows the firewall to keep track of active connections and understand the context of each packet. Instead of evaluating packets in isolation, the firewall considers the entire conversation between devices.
In contrast, stateless filtering—such as that used in basic Access Control Lists—evaluates each packet independently. While this method is faster, it lacks the depth needed to detect more sophisticated threats.
Stateful firewalls maintain a table of active sessions, allowing them to recognize whether a packet is part of an established connection or an unexpected attempt to communicate. This contextual awareness significantly improves both security and efficiency.
Deep Packet Inspection and Advanced Security Capabilities
Modern firewalls go beyond basic filtering by using deep packet inspection. This technique involves analyzing not just the header information of a packet, but also its contents. By examining the data itself, firewalls can detect hidden threats, suspicious patterns, and unauthorized activities.
For example, a firewall might identify malware embedded within a file transfer or detect unusual behavior that suggests an ongoing attack. It can also enforce rules based on application-level data, such as allowing secure web traffic while blocking unencrypted connections.
This level of inspection provides a much stronger defense against modern cyber threats, which often attempt to bypass traditional security measures.
Controlling Access Through Ports and Protocols
Firewalls use ports and protocols as part of their decision-making process. Ports act as communication endpoints for different types of services, while protocols define how data is transmitted. By controlling which ports and protocols are allowed, firewalls can regulate the types of traffic that enter or leave the network.
For instance, a firewall might allow secure web traffic while blocking less secure alternatives. It can also restrict access to certain services, ensuring that only authorized users can use them. This granular control helps reduce the attack surface and prevents unauthorized activities.
The ability to define detailed rules based on ports and protocols gives administrators precise control over network behavior, making firewalls highly adaptable to different security requirements.
Detecting and Preventing Network Attacks
Firewalls play a key role in identifying and stopping various types of attacks. One common example is a Distributed Denial of Service attack, where a network is overwhelmed with a flood of traffic. Firewalls can detect unusual spikes in activity and take action to mitigate the threat.
They can also identify repeated connection attempts from suspicious sources, which may indicate an attempt to gain unauthorized access. By blocking these attempts, firewalls help protect sensitive data and maintain network stability.
In addition to blocking known threats, firewalls can also detect anomalies—patterns of behavior that deviate from normal activity. This allows them to respond to new or evolving threats that may not yet be widely recognized.
Application Awareness and Intelligent Filtering
Advanced firewalls are capable of recognizing specific applications and enforcing rules based on their behavior. This means that instead of simply allowing or blocking traffic based on ports, the firewall can identify the actual application generating the traffic.
For example, it can distinguish between different types of web traffic and apply different rules accordingly. This level of awareness allows for more precise control and better security outcomes.
Application-aware filtering is particularly useful in environments where multiple services share the same ports or where traditional filtering methods are insufficient. It ensures that only legitimate applications are allowed to operate within the network.
Firewalls in Modern Network Architectures
In today’s networks, firewalls are often integrated into broader security systems. They may be combined with intrusion detection systems, virtual private networks, and other security tools to create a comprehensive defense strategy.
Firewalls can also be deployed in different forms, including hardware devices, software applications, and cloud-based solutions. Each type offers its own advantages, depending on the needs of the network.
Despite these variations, the core function of the firewall remains the same: to monitor, control, and protect network traffic. This consistency makes firewalls a fundamental part of any secure network design.
Balancing Security and Performance
While firewalls provide essential protection, they must also maintain high performance. Inspecting every packet can introduce delays, especially in high-traffic environments. To address this, modern firewalls use optimized algorithms and hardware acceleration to process data efficiently.
Balancing security and performance is a key challenge in network design. Too much restriction can slow down operations, while too little can expose the network to risks. Firewalls must be configured carefully to achieve the right balance.
Administrators often fine-tune firewall settings to ensure that critical services remain accessible while unnecessary or risky traffic is blocked. This ongoing process is essential for maintaining both security and usability.
The Importance of Firewall Policies and Configuration
A firewall is only as effective as the rules it enforces. Poorly configured policies can leave gaps in security or block legitimate traffic. This makes proper configuration and regular updates essential.
Administrators must define clear policies that reflect the needs of the organization. These policies determine which types of traffic are allowed, which are blocked, and how different situations are handled.
Regular reviews and updates are also necessary to adapt to changing threats and network conditions. As new vulnerabilities emerge, firewall rules must be adjusted to address them.
How Firewalls Complement Other Network Components
Firewalls do not replace switches or routers; they enhance them. Each component has a specific role, and together they create a complete networking solution.
Switches handle communication within the network, routers connect different networks, and firewalls protect the entire system from threats. This layered approach ensures that data flows efficiently while remaining secure.
By working together, these components create a robust and reliable network infrastructure capable of supporting modern digital activities.
Preparing for Integrated Network Design
Understanding firewalls is a crucial step toward mastering network security and design. As networks become more complex, the role of firewalls continues to grow. They are no longer optional components but essential elements of any network that connects to external systems.
With a solid grasp of how firewalls operate, it becomes easier to understand more advanced topics such as security policies, threat detection, and network segmentation. These concepts build on the foundation established by switches, routers, and firewalls working together.
In the next part, all three components will be brought together to show how they interact in real-world scenarios, forming a complete and functional network system that supports communication, connectivity, and security at every level.
How Switches, Routers, and Firewalls Work Together in Real Networks
Understanding each component individually is only part of the picture. Networks truly make sense when you see how switches, routers, and firewalls operate as a unified system. These components are not isolated tools; they are interconnected parts of a structured flow that ensures data moves efficiently, reaches the correct destination, and remains secure throughout its journey.
In a real-world network, every packet of data follows a path shaped by these three components. A device does not directly communicate with the internet or another network in a single step. Instead, its data passes through multiple checkpoints, each managed by a specific component with a clearly defined role.
The Journey of a Data Packet Across the Network
When a device sends data, the journey begins at the local level. The packet is first transmitted to a switch, which determines where within the local network it should go. If the destination is another device on the same network, the switch handles the entire process. This makes local communication fast and efficient.
If the destination lies outside the local network, the switch forwards the packet to a router. The router then takes over, analyzing the destination IP address and deciding where to send the packet next. This could involve passing it to another router or sending it directly toward its destination.
Before the packet leaves the network—or when incoming data arrives—it is inspected by a firewall. The firewall evaluates whether the traffic is safe and permitted based on predefined rules and real-time analysis. Only after passing this inspection is the packet allowed to continue its journey.
This sequence—switch to router to firewall—represents the fundamental flow of data in most network environments.
Breaking Down the Roles in a Unified Workflow
Each component contributes a specific function within this workflow. Switches manage internal communication, ensuring that devices within the same network can exchange data without unnecessary delays. Routers extend communication beyond the local environment, connecting different networks and enabling access to the internet. Firewalls enforce security policies, protecting the network from unauthorized access and malicious activity.
This division of responsibilities creates a system that is both efficient and secure. Instead of overloading a single device with multiple tasks, each component focuses on what it does best. This specialization is one of the key reasons modern networks can scale to support millions of devices and vast amounts of data.
A Practical Example of Network Interaction
Consider a typical scenario where a user opens a website on their computer. The request begins as a packet sent from the user’s device to the switch. The switch checks its MAC address table and determines that the destination is outside the local network, so it forwards the packet to the router.
The router examines the destination IP address and determines the best path to reach the web server. It may forward the packet through multiple intermediate routers across the internet. Before the packet leaves the local network, the firewall inspects it to ensure that the request is legitimate and complies with security policies.
When the response from the web server returns, the process happens in reverse. The firewall checks the incoming data, the router directs it back to the correct local network, and the switch delivers it to the user’s device. All of this occurs in fractions of a second, creating a seamless experience for the user.
Why Layered Design Improves Network Reliability
The collaboration between switches, routers, and firewalls is often referred to as a layered approach. Each layer handles a specific aspect of networking, allowing the system to function more effectively. This design improves reliability because issues can be isolated and resolved within a specific layer.
For example, if devices cannot communicate within the same network, the issue likely involves the switch. If the problem involves reaching external networks, the router may be the cause. If legitimate traffic is being blocked or suspicious activity is detected, the firewall may need to be adjusted.
This clear separation of responsibilities simplifies troubleshooting and reduces downtime, making networks more resilient and easier to manage.
Scalability and Growth in Network Design
As networks grow, the importance of these three components becomes even more apparent. A small home network might use a single device that combines switching, routing, and firewall functions. However, larger networks require dedicated devices for each role to handle increased traffic and complexity.
Switches can be added to support more devices, routers can be upgraded to handle higher data volumes, and firewalls can be enhanced to provide stronger security. This scalability ensures that networks can expand without losing performance or reliability.
The modular nature of this design allows organizations to adapt their infrastructure as their needs evolve. Whether adding new users, expanding to new locations, or integrating new technologies, the core components remain the same.
Security as a Continuous Process
Firewalls play a critical role in maintaining network security, but they are most effective when combined with the structured flow provided by switches and routers. Security is not a one-time setup; it is an ongoing process that requires monitoring, updates, and adjustments.
As new threats emerge, firewall rules must be updated to address them. Routers may need to implement additional controls, and switches may be configured to segment the network for better isolation. This continuous improvement ensures that the network remains protected against evolving risks.
The interaction between these components creates multiple layers of defense, making it more difficult for threats to penetrate the network.
Performance Optimization Across Components
Efficient networks depend on more than just connectivity; they require careful optimization. Switches can prioritize traffic to ensure that critical applications receive the necessary bandwidth. Routers can select optimal paths to reduce latency and avoid congestion. Firewalls can be tuned to minimize delays while maintaining strong security.
Balancing performance and security is a key challenge in network design. Too much filtering can slow down communication, while too little can expose vulnerabilities. Achieving the right balance requires a deep understanding of how each component operates and how they influence one another.
The Foundation for Advanced Networking Concepts
The interaction between switches, routers, and firewalls forms the foundation for more advanced networking concepts. Technologies such as virtual networks, cloud computing, and secure remote access all build on these core principles.
For example, network segmentation relies on switches to divide a network into smaller sections. Routing protocols depend on routers to exchange information about network paths. Security frameworks use firewalls to enforce policies and protect sensitive data.
By mastering these three components, it becomes much easier to understand and implement more complex systems.
Real-World Applications and Everyday Impact
Although these components operate behind the scenes, their impact is visible in everyday digital experiences. Smooth video calls, fast website loading, secure online transactions, and reliable cloud services all depend on the seamless interaction of switches, routers, and firewalls.
In professional environments, these components support critical operations such as data storage, communication systems, and business applications. Their reliability and efficiency directly influence productivity and user satisfaction.
From small home networks to global enterprise systems, the same principles apply. The scale may differ, but the core components remain unchanged.
Bringing It All Together
Switches, routers, and firewalls are more than just technical terms—they are the backbone of modern networking. Each component has a distinct role, yet their true value lies in how they work together to create a system that is fast, reliable, and secure.
Switches ensure that devices within a network can communicate efficiently. Routers connect those networks to the broader world, enabling global communication. Firewalls protect the entire system by controlling and inspecting traffic.
Together, they form a complete framework that supports everything from simple home setups to complex enterprise infrastructures. Understanding how these components interact provides a solid foundation for anyone looking to work with networks, troubleshoot issues, or design robust systems.
This integrated perspective transforms networking from a collection of isolated concepts into a cohesive and practical discipline, making it easier to navigate the complexities of modern digital communication.
Final Thoughts
Switches, routers, and firewalls are not just individual devices performing isolated tasks—they form a tightly integrated system that powers every modern network. From the simplest home setup to large-scale enterprise infrastructures, these three components define how devices communicate, how data travels, and how networks stay protected.
Switches provide the foundation by enabling smooth and efficient communication within a local network. They ensure that devices can exchange data quickly without unnecessary congestion. Routers extend that communication beyond local boundaries, connecting networks together and enabling access to the global internet. Firewalls complete the system by enforcing security, carefully inspecting traffic and preventing unauthorized access or malicious activity.
When combined, these components create a balanced environment where performance and security coexist. Data flows seamlessly from one point to another while being continuously monitored and controlled. This layered approach not only improves efficiency but also makes networks easier to manage, troubleshoot, and scale as demands grow.
Understanding how these components work—both individually and together—provides a strong foundation for anyone exploring networking. Whether the goal is to manage a small network, prepare for certifications from organizations like Cisco Systems, or build advanced infrastructures, this knowledge is essential.
As technology continues to evolve, the principles behind switches, routers, and firewalls remain constant. They are the core building blocks that support everything from everyday internet use to complex digital systems, making them one of the most important concepts in the world of networking.