802.1Q port tagging is a networking mechanism used to carry Virtual Local Area Network (VLAN) information across Ethernet networks. It allows a single physical network infrastructure to support multiple logical networks by marking, or “tagging,” Ethernet frames with VLAN identifiers. This tagging ensures that network switches and other devices can correctly identify which VLAN a frame belongs to and handle it according to predefined rules. In modern networking environments such as enterprise systems, data centers, and service provider networks, 802.1Q plays a central role in maintaining structured, secure, and efficient communication between devices.
At its core, 802.1Q enables the separation of traffic without requiring separate physical cabling or switches for each network segment. Instead, it uses intelligent frame modification, embedding VLAN information directly into Ethernet frames as they travel across trunk links between switches. This makes network design significantly more flexible and scalable, especially in environments where multiple departments, services, or customer networks must coexist securely on the same infrastructure.
Understanding the Concept of VLAN-Based Network Segmentation
To fully understand 802.1Q port tagging, it is important to first grasp the concept of VLAN-based segmentation. A Virtual Local Area Network is a logical grouping of devices that behave as if they are on the same physical network, even if they are not physically connected to the same switch or location. VLANs are created to improve network efficiency, reduce broadcast traffic, and increase security by isolating different groups of devices from one another.
Without VLANs, a network operates as a single broadcast domain, meaning every broadcast packet is sent to all devices. This can quickly lead to congestion and performance issues in larger environments. VLANs solve this problem by dividing the network into smaller broadcast domains. Each VLAN operates independently, and communication between VLANs requires routing through a Layer 3 device such as a router or a Layer 3 switch.
802.1Q port tagging is the mechanism that makes this segmentation possible across interconnected switches. When a frame moves from one switch to another through a trunk port, the VLAN identity must be preserved. This is where tagging becomes essential.
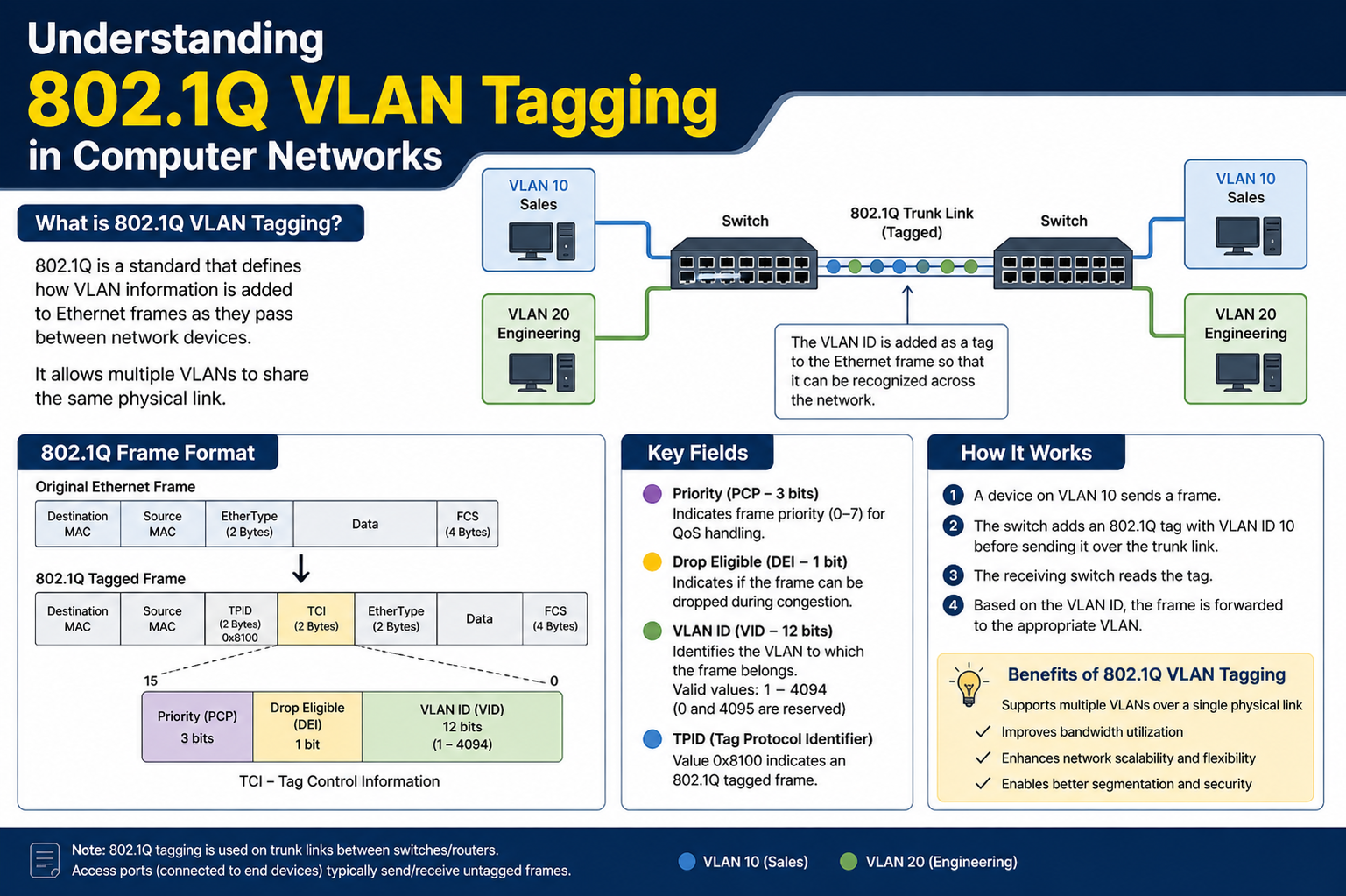
How Ethernet Frames Are Modified Through Tagging
In standard Ethernet communication, frames carry information such as source and destination MAC addresses, but they do not include VLAN identifiers. The 802.1Q standard modifies this structure by inserting an additional field into the Ethernet frame header. This inserted field carries VLAN identification data, allowing network devices to recognize which VLAN the frame belongs to as it traverses the network.
When a device sends traffic on an access port, the frame is typically untagged because the device itself is not aware of VLANs. The switch receiving this traffic assigns it to a specific VLAN based on the port configuration. However, when that frame needs to be sent to another switch over a trunk link, the switch adds a VLAN tag to the frame. This tag ensures that the receiving switch knows exactly which VLAN the frame belongs to and can forward it appropriately.
Once the frame reaches its destination switch, the VLAN tag is either retained or removed depending on whether it is being forwarded to another trunk or delivered to an end device. This dynamic tagging and untagging process ensures seamless communication across complex network infrastructures.
Structure and Function of the 802.1Q Tag
The 802.1Q tag is a small but critical part of the Ethernet frame structure. It is inserted between the source MAC address and the EtherType field of the frame. This tag contains several important fields that control how the frame is handled across the network.
One of the key components is the VLAN Identifier, which specifies the exact VLAN to which the frame belongs. This identifier allows switches to maintain proper separation of traffic even when multiple VLANs share the same physical link. The VLAN ID system supports thousands of unique VLANs, making it suitable for both small and extremely large networks.
Another important component is the priority field, which helps determine the quality of service level for the frame. This allows network administrators to prioritize certain types of traffic, such as voice or video communication, over less critical data. This prioritization is especially useful in environments where latency-sensitive applications must operate smoothly even during heavy network load.
The 802.1Q tag also includes a field that ensures compatibility with devices that do not support VLAN tagging. This ensures that untagged traffic can still be handled correctly through a designated default VLAN, often referred to as the native VLAN.
Role of Access Ports and Trunk Ports in Tagging
In a VLAN-enabled network, ports on switches are generally configured in two main ways: access mode and trunk mode. Access ports are used to connect end devices such as computers, printers, or IP phones. These ports typically belong to a single VLAN, and any traffic entering or leaving the port is untagged. The switch assigns incoming traffic to the configured VLAN without requiring the device itself to understand VLAN tagging.
Trunk ports, on the other hand, are designed to carry traffic for multiple VLANs simultaneously. These ports are commonly used between switches or between switches and routers. Because multiple VLANs share the same physical link, tagging becomes essential. 802.1Q tags are added to frames on trunk ports so that the receiving device can identify and separate traffic according to VLAN membership.
This distinction between access and trunk ports is fundamental to how VLAN networks operate. Without tagging on trunk ports, it would be impossible to maintain proper separation of VLAN traffic across interconnected devices.
Why Port Tagging Is Essential in Modern Networks
Modern networks are required to support a wide variety of applications, users, and devices, often with different security and performance requirements. Port tagging provides the flexibility needed to manage this complexity without requiring separate physical infrastructure for each network segment.
One of the most important benefits of port tagging is improved network organization. By dividing traffic into VLANs, administrators can logically separate departments such as finance, human resources, and IT, even if all devices share the same physical switches. This separation helps reduce unnecessary traffic and improves overall efficiency.
Another key advantage is enhanced security. Because VLANs are isolated from one another, unauthorized access between different network segments is significantly more difficult. Even if a device is compromised within one VLAN, it cannot easily access data from another VLAN without proper routing and access control policies.
Port tagging also contributes to better performance. By limiting broadcast traffic within individual VLANs, network congestion is reduced, and bandwidth is used more efficiently. This is particularly important in environments with high data transfer requirements, such as video streaming, cloud computing, or large-scale enterprise systems.
Challenges and Considerations in VLAN Tagging Environments
Although 802.1Q port tagging offers many advantages, it also introduces certain challenges that must be carefully managed. One of the most common issues is misconfiguration. If VLAN assignments are inconsistent across switches, traffic may not reach its intended destination, leading to communication failures between devices.
Another potential issue is compatibility between devices. Not all networking hardware handles VLAN tagging in the same way, and older devices may not fully support the 802.1Q standard. This can create integration challenges in mixed environments where legacy systems are still in use.
Network complexity can also increase significantly as more VLANs are introduced. Without proper planning and documentation, managing a large number of VLANs can become difficult, leading to configuration errors and troubleshooting delays. For this reason, careful network design is essential before implementing VLAN tagging at scale.
Despite these challenges, most issues can be avoided through structured planning, consistent configuration practices, and regular network monitoring.
The Importance of Proper VLAN Planning Before Implementation
Effective VLAN design is a critical step before implementing 802.1Q tagging in any network. Planning involves determining how many VLANs are required, what purpose each VLAN will serve, and how devices will be assigned to them.
A well-designed VLAN structure takes into account factors such as department separation, security requirements, traffic flow, and future scalability. Without this planning stage, networks can become disorganized, making it difficult to manage traffic or implement security policies effectively.
Mapping out VLANs before configuration also helps ensure that trunk links are properly defined between switches. This prevents issues where certain VLANs are unintentionally blocked or unable to communicate across the network.
Careful planning also makes troubleshooting easier, as administrators can quickly identify which VLAN a device belongs to and trace its traffic path through the network infrastructure.
Basic Understanding of Configuration Workflow in Tagged Networks
Setting up 802.1Q port tagging typically begins with enabling VLAN support on network switches. Once VLANs are created, ports are assigned to either access mode or trunk mode depending on their role in the network.
Access ports are configured to belong to a single VLAN, ensuring that connected devices are automatically placed into the correct network segment. Trunk ports are configured to carry multiple VLANs, with tagging enabled so that traffic can be properly identified across switches.
After configuration, testing is essential to ensure that devices within the same VLAN can communicate correctly and that inter-VLAN routing functions as expected. Network tools are often used to verify connectivity and identify any tagging issues that may be present.
Proper implementation ensures that VLANs operate smoothly, with consistent tagging behavior across all network devices.
Early Understanding of Security Concerns in Tagged Networks
Security plays a significant role in VLAN and port tagging environments. Although VLANs provide logical isolation, they are not completely immune to security threats. Misconfigurations or vulnerabilities in network devices can potentially allow unauthorized access between VLANs.
Common security risks include VLAN hopping attacks, where attackers attempt to gain access to restricted VLANs, and misconfigured trunk ports, which may unintentionally expose multiple VLANs to unauthorized devices. These risks highlight the importance of secure configuration practices and ongoing network monitoring.
Even at a basic level, understanding these security considerations helps ensure that VLAN implementations remain safe and reliable in real-world environments.
Deep Dive into How 802.1Q Encapsulation Works in Ethernet Frames
802.1Q port tagging operates by modifying the structure of standard Ethernet frames so that VLAN information can be carried across a shared network infrastructure. In a traditional Ethernet frame, there is no built-in mechanism to identify VLAN membership. The 802.1Q standard resolves this by inserting an additional 4-byte tag into the frame header. This tag is placed between the source MAC address and the EtherType field, effectively extending the frame without breaking compatibility with existing Ethernet systems.
This inserted tag contains critical information that allows network switches to understand how to treat the frame as it moves through the network. The most important part of this tag is the VLAN Identifier, which determines the exact VLAN to which the frame belongs. Without this identifier, switches would have no way to distinguish between traffic belonging to different logical networks when transmitted over the same physical link.
The insertion of this tag is performed by network switches operating in trunk mode. When a frame leaves an access port, it is untagged because the connected device is unaware of VLANs. However, once the frame reaches a trunk port, the switch adds the VLAN tag before forwarding it to another switch. This ensures that VLAN identity is preserved across the network.
Structure and Meaning of the 802.1Q Tag Fields
The 802.1Q tag is composed of multiple fields, each serving a specific purpose in VLAN identification and traffic handling. One of the most important components is the Tag Protocol Identifier, which signals that the frame contains VLAN information. This allows receiving devices to recognize that the frame has been modified according to the 802.1Q standard.
Another key component is the Priority Code Point field, which is used to assign quality of service levels to different types of network traffic. This field enables prioritization of critical applications such as voice communication, video conferencing, or real-time data systems. By assigning priority values, network administrators can ensure that time-sensitive traffic is processed before less important data.
The Drop Eligible Indicator is also included in the tag structure. This field provides a mechanism for marking frames that can be discarded during network congestion. It helps optimize bandwidth usage by allowing non-critical traffic to be dropped when necessary, ensuring that high-priority traffic maintains performance.
Finally, the VLAN Identifier field defines the exact VLAN to which the frame belongs. This 12-bit value allows for thousands of unique VLANs within a single network environment. The VLAN ID is the core element that enables logical segmentation across physical infrastructure.
Behavior of Switches When Processing Tagged and Untagged Frames
Network switches play a central role in interpreting and forwarding tagged Ethernet frames. When a frame enters a switch through an access port, the switch assigns it to a VLAN based on the port configuration. Since end devices typically do not support VLAN tagging, these frames are initially untagged.
Once the frame is classified into a VLAN, the switch determines how to forward it based on the destination MAC address and VLAN membership. If the destination device is located within the same VLAN and connected to another access port, the switch removes any VLAN tag before forwarding the frame. This ensures that the receiving device does not need to interpret VLAN information.
If the frame must travel between switches, it is forwarded through a trunk port. In this case, the switch adds the appropriate 802.1Q tag before transmission. The receiving switch reads this tag, identifies the VLAN, and continues forwarding the frame within the correct broadcast domain. This process ensures consistent VLAN separation across multiple interconnected devices.
Trunk Links and Their Role in VLAN Communication
Trunk links are essential in environments where multiple VLANs must communicate across different switches. Unlike access links, which carry traffic for a single VLAN, trunk links are designed to carry traffic for multiple VLANs simultaneously. This is achieved through VLAN tagging, which allows each frame to be identified as belonging to a specific VLAN.
When a trunk link is established between two switches, both devices agree to use 802.1Q tagging to maintain VLAN separation. Each frame transmitted over the trunk includes a VLAN tag that identifies its origin VLAN. This allows the receiving switch to forward the frame correctly without mixing traffic between different VLANs.
Trunk links are commonly used in enterprise environments, where large numbers of VLANs must be supported across multiple network devices. Without trunking, administrators would need to create separate physical connections for each VLAN, which would be inefficient and impractical.
Native VLAN Behavior and Untagged Frame Handling
Within 802.1Q networks, there is a concept known as the native VLAN. This VLAN is used to handle untagged traffic that passes through trunk links. When a switch receives an untagged frame on a trunk port, it assigns that frame to the native VLAN by default.
The native VLAN is typically set to a specific VLAN ID, often VLAN 1 in default configurations. However, in secure environments, administrators frequently change this value to avoid potential security risks. The native VLAN plays an important role in maintaining compatibility with devices or systems that do not support VLAN tagging.
If both ends of a trunk link are not configured with the same native VLAN, communication issues can occur. This condition, known as a native VLAN mismatch, may result in traffic being incorrectly assigned or dropped. Proper configuration is essential to ensure consistent behavior across all network devices.
MAC Address Tables and VLAN Isolation Mechanisms
Switches maintain MAC address tables to track which devices are connected to which ports. In a VLAN-enabled network, these tables are segmented based on VLAN membership. This means that the same MAC address can exist in different VLAN contexts without conflict.
When a switch learns a MAC address, it associates that address with both the physical port and the VLAN identifier. This allows the switch to make precise forwarding decisions based on both physical location and logical segmentation.
This separation ensures that traffic from one VLAN is never accidentally forwarded into another VLAN unless explicitly routed. It reinforces the isolation provided by VLAN architecture and prevents unintended data leakage between network segments.
Interaction Between 802.1Q and Inter-VLAN Routing
While VLANs provide logical separation, communication between different VLANs requires routing. This is where inter-VLAN routing comes into play. A Layer 3 device such as a router or a Layer 3 switch is used to forward traffic between VLANs based on IP addressing.
In an 802.1Q environment, trunk links are often used to connect switches to routers. The router receives tagged frames from multiple VLANs through a single physical interface. It then processes these frames and routes them to the appropriate destination VLAN.
Each VLAN is typically assigned a subinterface on the router, which allows it to handle multiple VLANs over a single physical connection. This design simplifies network architecture while maintaining logical separation between different network segments.
Inter-VLAN routing is essential for enabling communication between departments or services that reside on separate VLANs, such as finance systems, application servers, and user workstations.
Role of Spanning Tree Protocol in Tagged Networks
In networks with multiple switches and redundant links, loop prevention is critical. The Spanning Tree Protocol helps prevent broadcast storms by disabling redundant paths while maintaining network redundancy.
In a VLAN-aware environment, Spanning Tree operates on a per-VLAN basis or using a single instance depending on configuration. This ensures that loops are prevented independently for each VLAN, allowing more granular control over network topology.
802.1Q tagging works alongside Spanning Tree by ensuring that VLAN information is preserved even when certain paths are blocked. This allows the network to remain stable while still providing redundancy in case of link failures.
Proper coordination between VLAN tagging and Spanning Tree is essential for maintaining a stable and efficient network infrastructure.
Impact of VLAN Tagging on Broadcast and Multicast Traffic
Broadcast and multicast traffic behave differently in VLAN-based networks compared to flat networks. In a VLAN environment, broadcast traffic is confined to the VLAN in which it originates. This significantly reduces unnecessary traffic on the network.
802.1Q tagging ensures that broadcast frames are correctly associated with their VLAN, preventing them from being forwarded to unrelated segments. This isolation reduces congestion and improves overall network performance.
Multicast traffic is also controlled within VLAN boundaries. Network devices can optimize multicast distribution by limiting traffic to only those VLANs that require it. This helps conserve bandwidth and ensures that only relevant devices receive specific data streams.
Forwarding Decisions Based on VLAN Membership
When a switch receives a tagged frame, it uses the VLAN identifier to determine how the frame should be processed. The switch first checks its MAC address table within the context of that VLAN. It then forwards the frame only to ports that belong to the same VLAN.
This VLAN-based forwarding ensures strict separation between different logical networks. Even if multiple devices share the same physical switch, they will only receive traffic intended for their VLAN.
This mechanism is fundamental to how 802.1Q maintains both security and efficiency in complex network environments.
Early Considerations in Multi-VLAN Traffic Flow Design
Designing traffic flow in a multi-VLAN environment requires careful attention to how data moves between devices and switches. Administrators must consider which VLANs need to communicate, how trunk links are configured, and how routing will be handled between segments.
Without proper planning, traffic bottlenecks or communication failures can occur. Ensuring that VLANs are logically structured and that trunk links are properly defined helps maintain smooth data flow across the entire network infrastructure.
Advanced VLAN Segmentation in Large Network Environments
802.1Q port tagging becomes significantly more important when networks grow beyond small or simple setups. In large enterprise environments, there are often hundreds or even thousands of devices spread across multiple departments, floors, or geographic locations. Without VLAN segmentation, such networks would quickly become unmanageable due to excessive broadcast traffic and lack of security boundaries. 802.1Q provides the foundation for creating structured and scalable network architectures by allowing multiple logical networks to exist on the same physical infrastructure.
In these environments, VLAN design is not just a technical configuration task but a strategic planning exercise. Each VLAN typically represents a business function such as finance, human resources, engineering, guest access, or server management. By tagging traffic with 802.1Q, switches can carry multiple VLANs over a single trunk link while maintaining strict separation between them. This allows organizations to scale without continuously adding physical hardware for every new department or service.
As networks expand, administrators often introduce hierarchical switching designs, where access switches connect to distribution switches, and distribution switches connect to core switches. 802.1Q tagging ensures that VLAN information is preserved at every layer, enabling consistent communication across the entire network topology.
Importance of VLAN Trunking in Scalable Network Design
VLAN trunking is the backbone of 802.1Q-based communication between network devices. A trunk link is capable of carrying traffic from multiple VLANs simultaneously, and tagging ensures that each frame is correctly identified as it moves across the network. Without trunking, each VLAN would require a separate physical connection between switches, which would not be practical in modern network environments.
In a typical trunk configuration, a single physical interface can carry traffic for dozens or even hundreds of VLANs. This dramatically reduces hardware requirements while increasing flexibility. Trunk links are commonly configured between switches, between switches and routers, and sometimes between switches and firewalls in advanced security architectures.
The efficiency of trunking is one of the main reasons 802.1Q has become the industry standard for VLAN tagging. It allows networks to remain logically segmented while still maintaining physical simplicity. However, proper configuration is critical because even small mistakes in trunk setup can lead to VLAN leakage, communication failures, or security vulnerabilities.
VLAN Tagging and Its Role in Data Center Architecture
In data center environments, 802.1Q port tagging plays an even more critical role due to the extremely high density of servers, virtual machines, and storage systems. Data centers rely heavily on VLANs to isolate customer environments, separate production and testing systems, and manage internal service communication.
Virtualization has further increased the importance of VLAN tagging. A single physical server may host dozens of virtual machines, each belonging to different VLANs. Instead of dedicating separate physical network interfaces for each virtual machine, 802.1Q allows virtual switches to tag traffic internally before sending it through a shared physical network interface.
This capability significantly increases resource efficiency and allows data centers to maximize hardware utilization. It also supports cloud computing models where multiple tenants share the same physical infrastructure while remaining logically isolated from one another.
Without 802.1Q tagging, modern virtualization and cloud systems would be far less efficient and significantly more expensive to operate.
Role of Native VLAN in Legacy and Mixed Environments
In real-world networks, not all devices support VLAN tagging. Some older devices or simple network appliances still transmit untagged Ethernet frames. To accommodate these devices, 802.1Q introduces the concept of a native VLAN, which acts as a default VLAN for untagged traffic passing through trunk links.
When a switch receives an untagged frame on a trunk port, it assigns that frame to the native VLAN. This ensures that even devices without VLAN awareness can still communicate within a structured network environment. However, this convenience introduces potential risks if not properly managed.
Security best practices often recommend changing the default native VLAN from VLAN 1 to a custom VLAN. This helps reduce the risk of VLAN hopping attacks, where malicious actors attempt to exploit native VLAN behavior to access restricted network segments.
In mixed environments where legacy and modern devices coexist, careful planning of native VLAN assignments is essential to avoid traffic misrouting and unintended exposure between network segments.
Load Distribution and Traffic Optimization Through VLAN Separation
One of the lesser-discussed benefits of 802.1Q port tagging is its role in optimizing network performance under heavy load conditions. By dividing a network into multiple VLANs, broadcast and multicast traffic is confined to smaller domains. This reduces unnecessary traffic propagation and helps prevent congestion on shared network links.
In high-performance environments such as financial systems, video streaming platforms, or large enterprise applications, this optimization is critical. VLAN separation ensures that heavy traffic in one segment does not negatively impact performance in another segment.
Additionally, Quality of Service mechanisms can be applied in combination with 802.1Q tagging. Since VLAN tags can carry priority information, network devices can prioritize latency-sensitive traffic such as voice calls or real-time data over less critical operations like file transfers or background updates.
This combination of segmentation and prioritization allows networks to maintain consistent performance even under high utilization.
VLAN Tag Propagation Across Multi-Switch Networks
As traffic moves across multiple switches in a network, 802.1Q tags ensure that VLAN identity is preserved at every hop. Each switch in the path reads the VLAN tag, determines the appropriate forwarding action, and ensures that the frame remains within its assigned VLAN.
In multi-switch environments, trunk links form a chain that carries VLAN traffic across the entire network infrastructure. Without tagging, switches would lose VLAN context as frames move between devices, leading to traffic mixing and breakdown of logical separation.
This consistent propagation of VLAN identity is what allows large organizations to build geographically distributed networks while maintaining centralized control over VLAN architecture.
In some cases, VLANs may even extend across wide area networks using encapsulation technologies that preserve 802.1Q tagging beyond local infrastructure, allowing organizations to connect multiple sites under a unified VLAN structure.
Impact of VLAN Design on Network Scalability and Maintenance
Proper VLAN design has a direct impact on how easily a network can be scaled and maintained over time. A well-structured VLAN architecture allows administrators to add new devices, departments, or services without redesigning the entire network.
802.1Q tagging supports this scalability by allowing new VLANs to be added dynamically without requiring changes to the physical infrastructure. Only configuration updates are needed on switches and routers to define new VLANs and assign ports or trunks accordingly.
Maintenance becomes more manageable as well because network issues can be isolated to specific VLANs. Instead of troubleshooting an entire network, administrators can focus on individual segments, reducing downtime and improving efficiency in problem resolution.
However, poor VLAN design can have the opposite effect, leading to complex dependencies, overlapping configurations, and difficult troubleshooting scenarios. This is why structured planning remains essential in any VLAN-based architecture.
Security Layering in 802.1Q-Based Networks
Security in VLAN environments does not rely solely on segmentation. Instead, it is built in layers. While 802.1Q provides logical separation, additional security mechanisms are required to protect against attacks that target VLAN infrastructure.
One important aspect is controlling trunk access. Only authorized switches should be allowed to form trunk links, as unauthorized trunk connections can expose multiple VLANs to potential attackers. Port security features can also be used to restrict which devices are allowed to connect to specific switch ports.
Access control lists are commonly applied at routing points between VLANs to control which types of traffic are permitted between segments. This ensures that even if VLAN boundaries are bypassed, communication remains restricted by policy rules.
By combining VLAN tagging with these additional security layers, organizations create a robust defense system that protects both data and infrastructure.
Early Understanding of Inter-VLAN Communication Dependencies
As networks become more segmented, communication between VLANs becomes a critical design consideration. While 802.1Q handles tagging and transport of VLAN traffic, actual communication between VLANs depends on routing mechanisms.
Each VLAN operates as an independent broadcast domain, meaning devices in different VLANs cannot communicate directly without a routing device. This separation is intentional and provides security and control benefits. However, it also means that network designers must carefully plan how inter-VLAN communication will occur.
This planning includes deciding which VLANs need to communicate, what type of traffic should be allowed, and where routing should take place. Poor planning in this area can result in communication bottlenecks or unnecessary complexity in network architecture.
Properly designed inter-VLAN communication ensures that 802.1Q tagging works seamlessly as part of a larger, structured network ecosystem.
Security Challenges in 802.1Q VLAN Environments
While 802.1Q port tagging significantly improves network organization and isolation, it does not automatically guarantee complete security. VLANs create logical boundaries, but those boundaries can still be compromised if the network is misconfigured or poorly managed. As a result, understanding potential security risks is a critical part of working with VLAN-based networks.
One of the most well-known threats in VLAN environments is VLAN hopping. This type of attack occurs when an attacker attempts to gain unauthorized access to traffic in other VLANs. It usually exploits weaknesses in trunk configuration or native VLAN handling. If a switch is improperly configured, an attacker may be able to send specially crafted traffic that is incorrectly forwarded into another VLAN.
Another serious risk is double tagging, where malicious frames are crafted with multiple VLAN tags. In certain misconfigured environments, the first switch removes one tag and forwards the frame into a different VLAN than intended. This can allow attackers to bypass segmentation controls and reach restricted network segments.
Unauthorized access to switch configuration is another concern. If attackers gain access to network devices, they can modify VLAN settings, alter trunk configurations, or redirect traffic between VLANs. This kind of compromise can disrupt entire network infrastructures and expose sensitive data.
These risks highlight an important reality: VLAN tagging improves structure and control, but it must always be paired with strong security practices to be effective.
Strengthening VLAN Security Through Proper Configuration
Securing an 802.1Q-based network begins with correct and consistent configuration. One of the most important practices is disabling unused switch ports. Any inactive port should be either shut down or assigned to a dedicated unused VLAN to prevent unauthorized access.
Another essential measure is ensuring that trunk ports are explicitly defined rather than left in automatic negotiation modes. Allowing automatic trunk formation can create opportunities for attackers to exploit misconfigurations and gain access to multiple VLANs.
Changing the default native VLAN is also a widely recommended security practice. Many attacks rely on default VLAN behavior, so assigning a non-default VLAN reduces the risk of exploitation.
Additionally, limiting which VLANs are allowed on trunk links can significantly reduce exposure. Instead of allowing all VLANs across every trunk, administrators can restrict trunk links to only the VLANs that are necessary for communication. This minimizes the attack surface and improves network control.
These configuration practices form the foundation of a secure VLAN implementation and help ensure that 802.1Q tagging functions as intended without introducing unnecessary vulnerabilities.
Access Control and Layered Security in VLAN Networks
In modern networks, VLAN segmentation is only one layer of a broader security strategy. Access control mechanisms are used alongside 802.1Q tagging to enforce strict communication rules between devices and network segments.
Access Control Lists are commonly applied at Layer 3 devices such as routers or Layer 3 switches. These rules define which types of traffic are allowed between VLANs. For example, a finance VLAN may only be allowed to communicate with specific database servers, while being restricted from accessing other internal systems.
Port security is another important layer. It allows administrators to limit the number of MAC addresses that can connect to a specific switch port. This helps prevent unauthorized devices from being physically connected to the network.
Dynamic security features such as DHCP snooping and dynamic ARP inspection also help protect VLAN environments from spoofing and interception attacks. These tools work by validating network traffic and ensuring that only legitimate devices can communicate within a VLAN.
By combining VLAN tagging with these layered controls, organizations create a defense-in-depth strategy that significantly reduces the likelihood of successful attacks.
Monitoring and Troubleshooting VLAN Tagging Issues
Even in well-designed networks, issues can arise in 802.1Q configurations. Troubleshooting VLAN-related problems requires a structured approach and an understanding of how tagged traffic flows through the network.
One of the most common problems is VLAN mismatch, where trunk ports on different switches are not configured with the same allowed VLANs. This can result in traffic being dropped or incorrectly routed, leading to communication failures between devices.
Another frequent issue is incorrect native VLAN configuration. If the native VLAN does not match on both ends of a trunk link, untagged traffic may be misinterpreted, causing connectivity problems or unexpected behavior in the network.
Misconfigured access ports can also lead to devices being placed in the wrong VLAN. This often results in users being unable to access required resources or experiencing restricted network connectivity.
To diagnose these issues, network administrators rely on tools such as packet analyzers and switch diagnostic commands. These tools help identify whether VLAN tags are being correctly applied and whether traffic is flowing through the intended paths.
Careful observation of traffic behavior is essential, especially in large networks where multiple VLANs and trunk links interact simultaneously.
Role of VLAN Tagging in Virtualized and Cloud Systems
802.1Q port tagging plays a crucial role in modern virtualized environments. In systems where multiple virtual machines run on a single physical server, VLAN tagging allows each virtual machine to belong to a different network segment while sharing the same physical network interface.
Virtual switches inside hypervisors use 802.1Q tagging to separate traffic between virtual machines. When a virtual machine sends data, the virtual switch tags the frame before sending it through the physical network adapter. This ensures that the receiving network infrastructure can correctly identify the VLAN.
In cloud computing environments, VLAN tagging helps isolate customer workloads on shared infrastructure. Each tenant may be assigned one or more VLANs, ensuring that their data remains logically separated from other tenants.
This capability is essential for maintaining security and scalability in cloud platforms, where thousands of virtual systems may coexist on the same physical hardware.
Without 802.1Q tagging, virtualization and cloud networking would require significantly more physical resources and would be far less flexible.
Network Efficiency Improvements Through VLAN Segmentation
One of the most important advantages of 802.1Q tagging is improved network efficiency. By dividing a network into multiple VLANs, broadcast traffic is significantly reduced. Instead of flooding all devices in a large network, broadcasts are confined to smaller logical segments.
This reduction in broadcast traffic leads to better performance, especially in environments with high device density. It also reduces unnecessary processing load on switches and routers, allowing them to handle traffic more efficiently.
Multicast traffic can also be optimized through VLAN segmentation. Devices only receive multicast streams relevant to their VLAN, which helps conserve bandwidth and improves overall network responsiveness.
In environments such as corporate offices, universities, and data centers, these efficiency improvements can have a significant impact on user experience and system performance.
Importance of Documentation and Network Planning
Proper documentation is a critical but often overlooked part of VLAN and 802.1Q implementation. Without clear records of VLAN assignments, trunk configurations, and port mappings, troubleshooting becomes extremely difficult.
Good documentation includes VLAN naming conventions, IP address mappings, port assignments, and device roles. It also includes diagrams that show how switches are interconnected and how VLANs flow through the network.
Network planning should always be done before implementing VLANs. This includes identifying which departments or services require isolation, determining communication requirements between VLANs, and designing trunk link structures.
Without proper planning, VLAN environments can quickly become complex and difficult to manage, leading to configuration errors and security gaps.
Final Conclusion
802.1Q port tagging is a foundational technology in modern networking that enables scalable, secure, and efficient communication across complex infrastructures. It allows multiple VLANs to coexist on the same physical network while maintaining strict logical separation.
Through VLAN tagging, trunking, and structured segmentation, organizations can design networks that are both flexible and manageable. However, successful implementation depends on careful configuration, strong security practices, and continuous monitoring.
When properly designed and maintained, 802.1Q-based networks provide a powerful framework for supporting modern computing environments, including enterprise systems, data centers, and cloud platforms.