Address Resolution Protocol (ARP) is a fundamental communication mechanism used in computer networks to connect logical addressing with physical addressing. In simple terms, it acts as a translator between IP addresses, which are used for logical identification of devices, and MAC addresses, which are permanent hardware identifiers assigned to network interfaces. Without ARP, devices on a local network would struggle to locate each other physically even if they already know each other’s IP addresses. This makes ARP an essential part of local network communication, especially in Ethernet-based environments where data delivery depends on hardware-level addressing.
Role of ARP in Network Communication
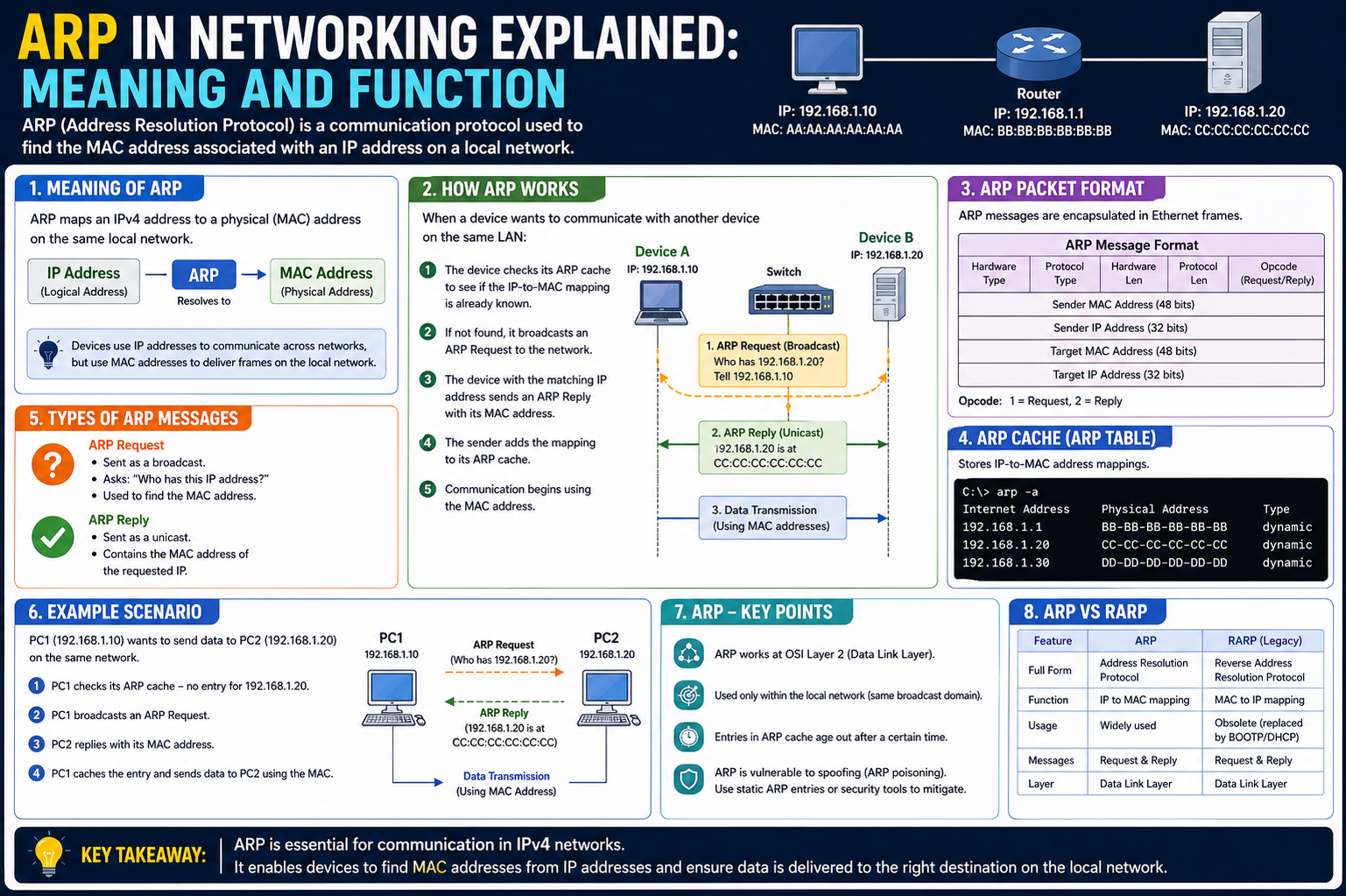
In a network, devices communicate using IP addresses at a logical level, but actual data transfer over a local network segment happens using MAC addresses. ARP serves as the bridge between these two addressing systems. When one device wants to send data to another device within the same network, it must know the recipient’s MAC address. If that information is not already known, ARP steps in to discover it. This ensures that packets are correctly delivered to the intended device without confusion or misrouting at the local level.
Relationship Between IP and MAC Addresses
Every device connected to a network has at least two important identifiers. The IP address can change over time depending on network configuration, while the MAC address is permanently embedded into the network interface hardware. IP addresses help with logical routing across networks, while MAC addresses handle delivery within the same local network segment. ARP connects these two layers by resolving which MAC address belongs to a given IP address. This relationship is critical because without mapping between the two, data packets would not reach the correct physical device even if the logical destination is known.
Need for ARP in Local Networks
ARP is mainly used in local area networks where devices are directly reachable without needing external routing. When a device wants to communicate within the same subnet, it cannot rely on IP routing alone. Instead, it needs the MAC address of the destination device to send data frames properly. ARP enables this by allowing devices to discover and store MAC addresses associated with IP addresses. Without ARP, every communication attempt would require manual configuration of MAC addresses, making networking impractical and inefficient.
How ARP Begins Communication
When a device wants to send data, it first checks whether it already knows the MAC address associated with the target IP address. This check is performed using a local storage area known as the ARP cache. If the required information is not found there, the device initiates an ARP process to discover it. This process begins with a broadcast request sent across the local network. The request essentially asks all connected devices which one owns the specified IP address. This broadcast mechanism ensures that the correct device can respond even if the sender does not know its physical location.
ARP Request Mechanism
The ARP request is a network-wide query that is sent to all devices in the local segment. It is not directed at a specific device because the sender does not yet know the physical address of the destination. Instead, it announces the IP address it is trying to reach and asks which device owns it. All devices on the network receive this request, but only the one with the matching IP address responds. This process ensures that the sender can locate the correct device without prior knowledge of its hardware address.
ARP Reply Process
Once the device with the matching IP address receives the request, it responds with an ARP reply. This reply contains its MAC address, allowing the requesting device to establish a direct communication path. The reply is sent directly back to the requester rather than being broadcast again. After receiving this information, the requesting device stores it in its ARP cache for future use. This reduces the need for repeated requests and improves communication efficiency within the network.
Function of the ARP Cache
The ARP cache is a temporary storage area maintained by each device on a network. It stores recently resolved IP-to-MAC address mappings so that future communication can happen more quickly. Instead of broadcasting a new request every time data needs to be sent, the device first checks its cache. If the required mapping exists and has not expired, it is used directly. This significantly improves network performance by reducing unnecessary traffic and lowering latency during communication.
Expiration and Refresh of ARP Entries
Entries in the ARP cache are not permanent and are designed to expire after a certain period. This expiration ensures that outdated information does not remain in the system, especially in environments where devices frequently join or leave the network. The expiration time can vary depending on the operating system and network configuration. Once an entry expires, the device must perform the ARP request process again to obtain fresh information. This dynamic updating mechanism ensures that the network maintains accurate and current mappings.
Efficiency Benefits of ARP
ARP contributes significantly to network efficiency by reducing the overhead required to locate devices. Once a MAC address is resolved and stored in the cache, communication between devices becomes faster and more direct. This avoids repeated broadcasts and minimizes network congestion. In environments with many devices, this efficiency becomes even more important because it helps maintain smooth communication without overwhelming the network with unnecessary traffic.
Limitations in Basic ARP Design
Despite its importance, ARP has limitations due to its simple design. It does not include built-in authentication, meaning devices must trust the responses they receive. This lack of verification can lead to potential security risks if malicious activity is present on the network. Additionally, since ARP relies on broadcasting for discovery, it can generate unnecessary traffic in large networks. These limitations highlight that while ARP is essential, it must be managed carefully within secure network environments.
ARP Packet Structure and Internal Components
To understand how Address Resolution Protocol functions at a deeper level, it is important to examine the structure of an ARP message. An ARP packet contains specific fields that carry the necessary information for resolving an IP address into a MAC address. These fields include the hardware type, protocol type, hardware address length, protocol address length, operation type, sender hardware address, sender protocol address, target hardware address, and target protocol address. Each of these fields plays a precise role in ensuring that the request and reply process can occur smoothly across the network.
The hardware type identifies the network technology being used, such as Ethernet. The protocol type indicates the type of network layer protocol involved, most commonly IPv4. The address length fields define the size of MAC and IP addresses so that devices can correctly interpret the packet. The operation type specifies whether the packet is an ARP request or an ARP reply. The sender and target address fields carry the actual IP and MAC information that enables resolution. This structured format ensures that devices from different manufacturers and operating systems can interpret ARP messages consistently.
How ARP Operates Within a Local Broadcast Domain
ARP operates strictly within a local broadcast domain, which means its messages do not travel beyond routers. When a device sends an ARP request, it is broadcast to all devices within the same network segment. This behavior is essential because ARP relies on direct hardware-level communication, which is only possible within the same local environment. Routers intentionally do not forward ARP packets because they function at a higher layer of the networking model and handle IP routing instead of MAC resolution.
Within a broadcast domain, every device receives the ARP request, but only the device with the matching IP address responds. This ensures that ARP remains efficient and avoids unnecessary processing across unrelated networks. The limitation to a single broadcast domain also helps reduce global network congestion, as ARP traffic remains localized and does not scale beyond its intended scope.
Detailed Flow of ARP Resolution Process
When a device attempts to communicate with another device on the same network, it first checks whether the destination IP address already has an associated MAC address stored locally. If not, the ARP resolution process begins. The device constructs an ARP request packet containing the target IP address and broadcasts it across the network. All devices receive this packet and examine the target IP field.
The device whose IP address matches the request responds with an ARP reply. This reply contains its MAC address, which allows the requesting device to update its internal ARP cache. Once this mapping is stored, the device can begin sending data frames directly to the correct hardware address. This entire process happens quickly, often within milliseconds, ensuring minimal delay in communication between devices.
Role of ARP Cache in Network Optimization
The ARP cache plays a critical role in optimizing network communication by storing recently resolved address mappings. Without this cache, every communication attempt would require a new ARP request, significantly increasing network traffic. The cache acts as a temporary memory that holds IP-to-MAC mappings for a defined period of time.
When a device needs to send data, it first checks this cache. If a valid entry exists, it is used immediately, bypassing the ARP request process. This reduces broadcast traffic and improves overall efficiency. However, these entries are not permanent and are removed after a timeout period to ensure accuracy. This balance between caching and expiration ensures that the network remains both fast and reliable.
Gratuitous ARP and Its Network Function
Gratuitous ARP is a special type of ARP communication where a device sends an ARP request for its own IP address. At first glance, this may seem unnecessary, but it serves several important purposes in networking. One primary use is to detect IP address conflicts. If another device responds to a gratuitous ARP request, it indicates that the same IP address is already in use elsewhere on the network.
Another important function of gratuitous ARP is updating other devices’ ARP caches. When a device changes its MAC address or network interface, it can broadcast a gratuitous ARP to inform other devices of the new mapping. This ensures that communication continues without interruption and that outdated entries are quickly replaced. This mechanism is especially useful in systems that require high availability and frequent failover.
Proxy ARP and Its Role in Network Communication
Proxy ARP is an advanced networking technique where a device, typically a router, responds to ARP requests on behalf of another device. This allows communication between devices that are not on the same subnet without requiring them to understand routing complexities. When a device sends an ARP request for an IP address outside its local network, a router configured with proxy ARP can respond with its own MAC address, effectively acting as an intermediary.
This allows traffic to be forwarded across different network segments while maintaining the illusion that all devices are on the same local network. Proxy ARP can simplify network configuration in certain environments, but it can also introduce complexity and potential inefficiencies if not managed carefully.
Interaction Between ARP and Network Switches
Switches play an important role in how ARP traffic is handled within a local network. A switch operates at the data link layer and uses MAC addresses to forward frames between devices. When an ARP broadcast is sent, the switch forwards it to all ports except the one it originated from. This ensures that all devices in the network receive the request.
Switches also maintain MAC address tables that map connected devices to specific ports. While ARP helps devices discover MAC addresses, switches help direct traffic efficiently once those addresses are known. This combination of ARP resolution and switch forwarding creates a highly efficient local communication system.
Impact of Subnetting on ARP Behavior
Subnetting affects how ARP operates by defining the boundaries of broadcast domains. Devices within the same subnet can communicate directly using ARP, while devices in different subnets must rely on routers. When a device determines that the destination IP address is outside its subnet, it does not initiate an ARP request for that device. Instead, it sends the request to its default gateway, whose MAC address is resolved using ARP.
This means ARP is only used for local communication within a subnet, while routing handles communication across networks. Subnetting therefore plays a key role in limiting ARP scope and improving overall network structure.
Operating System Behavior in ARP Handling
Different operating systems manage ARP slightly differently, but the core principles remain consistent. Each system maintains its own ARP cache, which stores resolved addresses temporarily. The size of the cache, the expiration time of entries, and the behavior during updates can vary depending on system design.
Some systems aggressively cache ARP entries for performance, while others prioritize frequent updates for accuracy. Operating systems also handle ARP requests in the background, automatically resolving addresses when needed without user intervention. This automation ensures that applications and services can communicate seamlessly without needing to manually manage network details.
Importance of ARP in Everyday Network Communication
ARP is continuously working in the background during everyday network activities. Whether browsing websites, sharing files, or streaming content within a local network, ARP ensures that devices can locate each other at the hardware level. Although users rarely interact directly with ARP, it is fundamental to the functioning of all Ethernet-based networks.
Its simplicity and efficiency make it one of the most important protocols in local networking. However, its reliance on trust and broadcast communication also introduces vulnerabilities that require careful network design and security considerations.
ARP Table Maintenance and Dynamic Updates
The ARP table, also known as the ARP cache, is not a static structure. It is constantly updated based on network activity. Whenever a device communicates with another device on the same local network, the ARP table is either checked, updated, or refreshed depending on whether an entry already exists. This dynamic behavior ensures that the network always maintains relatively accurate mappings between IP addresses and MAC addresses.
When a device receives an ARP reply, it immediately stores the mapping in its ARP table. However, if the same IP address later appears with a different MAC address, the existing entry can be replaced or updated. This allows networks to adapt to changes such as device replacement, interface changes, or network reconfiguration. Without this dynamic updating mechanism, outdated mappings would persist and cause communication failures.
Timeout Mechanism and Entry Aging
ARP entries are not permanent and are subject to aging mechanisms. Each entry in the ARP table has a lifetime, after which it is automatically removed if it is not refreshed. This timeout mechanism prevents stale entries from accumulating and ensures that the system continues to operate with accurate data.
The aging process is important because network environments are constantly changing. Devices may disconnect, reconnect, or change their network configuration. If ARP entries were permanent, the system could attempt to send data to incorrect MAC addresses, resulting in packet loss or communication errors. By enforcing expiration, ARP ensures that outdated mappings are periodically verified or removed.
When an entry expires and the device needs to communicate again with the same IP address, a new ARP request is triggered. This cycle of expiration and re-resolution helps maintain accuracy while balancing network efficiency.
ARP in Multi-Device Network Environments
In networks with many devices, ARP plays an even more critical role. As the number of connected devices increases, the number of possible IP-to-MAC mappings also grows. ARP ensures that each device can still locate others without requiring centralized coordination. Every device independently manages its own ARP table, which reduces the need for a central directory.
In such environments, broadcast traffic from ARP requests can become more frequent. However, the use of caching significantly reduces the overall load. Once devices learn about each other, repeated broadcasts are minimized. This distributed approach allows ARP to scale effectively in medium-sized local networks, although very large networks may require additional optimization techniques.
Broadcast Nature of ARP Requests
One of the most important characteristics of ARP is its reliance on broadcast communication. When a device sends an ARP request, it is transmitted to every device within the local network segment. This ensures that even if the sender does not know where the target device is located, the request will still reach it.
Broadcasting is necessary because ARP operates before MAC address resolution has occurred. Without knowing the destination MAC address, the only option is to send the request to all devices. While this method is efficient in small to medium networks, it can create overhead in very large networks if ARP requests become too frequent.
Despite this limitation, broadcasting remains a simple and effective solution for local address resolution. It ensures reliability, as every device has the opportunity to respond if it matches the requested IP address.
Unicast Communication After ARP Resolution
Once ARP successfully resolves the MAC address, communication between devices switches from broadcast-based discovery to direct unicast communication. This means that data packets are sent directly from one device to another using the resolved MAC address.
This transition is important because unicast communication is much more efficient than broadcasting. Instead of sending packets to all devices, the sender now targets a single recipient. This reduces unnecessary network traffic and improves performance significantly. ARP essentially acts as the discovery phase, while unicast communication handles the actual data transfer.
Interaction Between ARP and Network Interfaces
Network interfaces are responsible for handling ARP messages at the hardware level. When an ARP request is received, the network interface checks whether the target IP address matches its own configuration. If it does, it generates an ARP reply and sends it back to the requester.
This process is handled automatically by the network interface card (NIC) and its associated driver. The operating system coordinates this behavior, ensuring that ARP requests are processed quickly and efficiently. Because this process happens at a low level, users are generally unaware of ARP activity occurring on their devices.
ARP in Virtualized and Cloud Environments
In modern computing environments such as virtualization and cloud networks, ARP still plays an important role but operates in more complex ways. Virtual machines often share physical network interfaces, meaning ARP must function across virtual switches and software-defined networks.
In these environments, ARP requests may be handled by virtual switches rather than physical hardware. This allows communication between virtual machines on the same host or across different hosts within a data center. Despite the added complexity, the core principle remains the same: mapping IP addresses to MAC addresses for local communication.
Virtualization also introduces additional layers where ARP responses may be controlled or filtered for security and performance reasons. This ensures that large-scale cloud environments can manage traffic efficiently without relying solely on traditional broadcast-based discovery.
Limitations of ARP in Large Networks
Although ARP is highly effective in local networks, it has limitations when used in large-scale environments. The reliance on broadcasting can lead to excessive network traffic if not properly managed. As the number of devices increases, the volume of ARP requests can also increase, potentially affecting performance.
Another limitation is the lack of authentication in ARP communication. Since ARP responses are accepted without verification, malicious devices can potentially send false information. This weakness becomes more significant in large or unsecured networks where many devices interact.
To address these limitations, network administrators often implement additional security measures and segmentation strategies to control ARP traffic and reduce exposure to risks.
ARP and Network Troubleshooting
ARP is often used as a diagnostic tool in network troubleshooting. By examining the ARP table, administrators can verify whether devices are correctly communicating within a network. If an expected entry is missing or incorrect, it may indicate a connectivity issue or misconfiguration.
Tools that display ARP tables help identify whether IP-to-MAC mappings are correct. If a device cannot communicate with another device, checking the ARP table is often one of the first steps in diagnosing the problem. This makes ARP not only a communication protocol but also a valuable diagnostic resource in network management.
Efficiency of ARP in Repeated Communication
Once ARP has resolved a MAC address, repeated communication between the same devices becomes highly efficient. The ARP cache allows devices to skip the resolution process and directly send data frames to known MAC addresses. This reduces delay and improves responsiveness in applications that require continuous communication.
In environments where devices frequently interact, such as file sharing or local services, ARP caching significantly improves performance. The reduction in broadcast traffic also helps maintain network stability and prevents unnecessary load on network infrastructure.
ARP Security Challenges in Modern Networks
Although Address Resolution Protocol is essential for local network communication, it has a major weakness: it was designed in an era when networks were considered relatively trusted environments. Because of this, ARP does not include built-in authentication or verification mechanisms. This means that devices accept ARP responses without confirming whether they are legitimate or not. This design limitation creates opportunities for attackers to manipulate network behavior.
In modern networks, where security threats are more common and more advanced, this lack of authentication becomes a serious concern. Attackers can exploit ARP behavior to intercept, redirect, or disrupt network traffic. Since ARP operates at a fundamental layer of local communication, successful manipulation can affect a wide range of systems and applications connected to the same network.
ARP Spoofing and Cache Poisoning Mechanism
One of the most well-known attacks related to ARP is ARP spoofing, also known as ARP cache poisoning. In this type of attack, a malicious device sends fake ARP responses across the network. These responses falsely associate the attacker’s MAC address with the IP address of another legitimate device, such as a gateway or server.
When other devices receive these forged responses, they update their ARP tables with incorrect mappings. As a result, traffic intended for a legitimate device is redirected to the attacker instead. Because ARP does not verify the authenticity of responses, this manipulation can occur without immediate detection. Once the ARP cache is poisoned, communication within the network can be silently intercepted or disrupted.
Man-in-the-Middle Exploitation Using ARP
ARP spoofing is often used as a foundation for man-in-the-middle attacks. In this scenario, the attacker positions themselves between two communicating devices without their knowledge. Once ARP tables are manipulated, network traffic intended for one device is redirected through the attacker’s system before reaching its final destination.
This allows the attacker to inspect, modify, or capture data packets in real time. Sensitive information such as login credentials, session tokens, or unencrypted data can be exposed during this process. Even if the attacker does not alter the traffic, simply observing it can lead to serious security breaches. This makes ARP spoofing a powerful and dangerous technique in unsecured networks.
Denial of Service Through ARP Manipulation
ARP can also be exploited to cause denial of service conditions. Instead of redirecting traffic to themselves, attackers can send incorrect or non-existent MAC addresses in ARP responses. When devices update their ARP tables with these invalid entries, they lose the ability to communicate properly.
As a result, network traffic is sent into a void where no device exists to receive it. This effectively disrupts communication between systems without physically damaging any hardware or software. Such disruptions can affect critical services and lead to downtime in both small and large networks.
Detection and Monitoring of ARP Activity
To address ARP-related threats, network monitoring tools are often used to observe ARP activity in real time. These tools analyze ARP traffic and look for unusual patterns such as frequent changes in IP-to-MAC mappings or unexpected ARP replies. When suspicious behavior is detected, alerts can be generated for network administrators.
Monitoring helps identify potential ARP spoofing attempts early before significant damage occurs. By continuously observing ARP tables and network traffic, administrators can maintain better control over network integrity and respond quickly to anomalies.
Static ARP Entries as a Security Measure
One way to reduce ARP-based attacks is through the use of static ARP entries. In this approach, specific IP-to-MAC mappings are manually configured and permanently stored in a device’s ARP table. These entries do not change automatically and are not overwritten by ARP responses.
This method is especially useful for critical devices such as gateways, servers, or routers. Since static entries do not accept dynamic updates, they are immune to ARP spoofing attempts targeting those specific mappings. However, this approach is not scalable for large networks because manually maintaining ARP entries for many devices becomes impractical.
Dynamic ARP Inspection and Switch-Level Protection
Modern network switches often include security features designed to protect against ARP attacks. One such feature is Dynamic ARP Inspection, which verifies ARP packets before allowing them to be processed by the network. It checks whether ARP responses match trusted IP-to-MAC bindings stored in a secure database.
If a packet does not match the expected information, it is dropped or rejected. This prevents malicious ARP messages from being accepted by devices in the network. Switch-level protection adds an important layer of defense because it filters harmful traffic before it reaches end devices.
Role of Network Segmentation in Reducing ARP Risks
Network segmentation is another important strategy for limiting ARP-related risks. By dividing a large network into smaller subnets, the scope of ARP broadcasts is reduced. Since ARP operates only within local broadcast domains, segmentation naturally limits how far ARP traffic can spread.
Smaller network segments also reduce the number of devices exposed to potential spoofing attempts. Even if an attacker successfully manipulates ARP within one segment, the impact is contained and does not easily spread across the entire network. This improves both performance and security simultaneously.
ARP in Secure Network Design
In secure network design, ARP is treated as a necessary but vulnerable protocol that must be supported with additional protections. Security strategies often combine multiple layers, including monitoring, filtering, static configuration, and segmentation.
Rather than replacing ARP, these strategies focus on controlling how ARP behaves within the network. This ensures that devices can still communicate efficiently while reducing exposure to potential threats. Secure design principles recognize that ARP is essential for operation but must be carefully managed in modern environments.
Performance Considerations in ARP Usage
While ARP is lightweight and efficient, its performance impact becomes more noticeable in large or busy networks. Frequent ARP broadcasts can contribute to background traffic, especially when many devices are joining or leaving the network. However, caching mechanisms significantly reduce this impact by reusing stored mappings.
Efficient ARP operation depends on a balance between caching and refreshing entries. Too much caching can lead to outdated information, while too little caching increases unnecessary network traffic. Proper tuning of ARP timeout values helps maintain optimal performance without compromising accuracy.
Importance of ARP in Real-World Networking
Despite its limitations, ARP remains one of the most important protocols in local networking. It enables seamless communication between devices without requiring manual configuration of hardware addresses. Every time a device connects to a local network, ARP plays a role in ensuring that data reaches the correct destination.
From simple home networks to complex enterprise systems, ARP continues to function as a foundational mechanism for local communication. Even with the introduction of modern networking technologies, its core role has not been replaced.
Final Conclusion
Address Resolution Protocol remains one of the most foundational mechanisms in computer networking because it enables direct communication between devices at the local level. Even though modern networks include complex routing systems, virtualization layers, and advanced security frameworks, ARP continues to perform a very basic but extremely important job: connecting logical IP addresses with physical MAC addresses so that data can actually move between devices on the same network. Without this mapping process, IP-based communication would not be able to reach the physical hardware that ultimately sends and receives data frames.
What makes ARP particularly important is its simplicity and universality. It does not require heavy configuration or centralized control. Instead, each device independently performs address resolution when needed and stores results temporarily in its ARP cache. This decentralized behavior allows networks to function efficiently without constant administrative intervention. The use of broadcasting for discovery and caching for optimization creates a balance between accuracy and performance, ensuring that devices can communicate quickly while still adapting to changes in the network environment.
At the same time, ARP is not without weaknesses. Its original design assumed a trusted local environment, which is no longer realistic in many modern network scenarios. Because ARP does not include authentication, it can be exploited through techniques such as spoofing and cache poisoning. These vulnerabilities can lead to serious consequences, including traffic interception, data theft, service disruption, and complete communication breakdown within a network segment. This is why ARP security has become an important topic in modern network administration.
Despite these limitations, ARP continues to be widely used because it is deeply integrated into the structure of Ethernet-based communication. Replacing it would require significant changes to how local networks operate, which is not practical given its efficiency and compatibility. Instead of replacing ARP, modern networking focuses on securing it through additional mechanisms such as static entries, monitoring systems, switch-level protections, and network segmentation. These protective layers help reduce risk while still allowing ARP to perform its essential role.
Another important aspect of ARP is its role in supporting scalability within local networks. Through caching, ARP reduces repetitive broadcast traffic and improves communication speed. Devices do not need to repeatedly discover MAC addresses for frequently used IPs, which significantly reduces overhead. This caching system is simple but highly effective in maintaining smooth network performance, especially in environments where devices communicate continuously.
ARP also plays an important role in troubleshooting and diagnostics. By examining ARP tables, network administrators can quickly determine whether devices are correctly communicating and whether IP-to-MAC mappings are accurate. This makes ARP not only a communication protocol but also a valuable diagnostic tool that helps identify connectivity issues, misconfigurations, or potential security threats.
In modern environments such as virtualization and cloud computing, ARP has adapted rather than disappeared. Virtual networks still rely on ARP for local communication, although its behavior may be influenced by virtual switches and software-defined networking systems. This shows that even as networking technology evolves, ARP remains relevant and continues to operate at the core of local communication systems.
Overall, ARP should be understood as a silent but essential foundation of networking. It operates behind the scenes every time a device sends data to another device on the same network. While users rarely interact with it directly, nearly all local communication depends on its proper functioning. Its combination of simplicity, efficiency, and wide compatibility has ensured its long-term survival in networking systems.
In conclusion, ARP is not just a technical protocol but a critical building block of network communication. It enables devices to find each other, communicate efficiently, and maintain accurate addressing within local environments. At the same time, it requires careful management and security awareness due to its inherent vulnerabilities. Understanding ARP provides deeper insight into how networks function at a fundamental level, making it an essential concept for anyone studying or working in the field of networking.