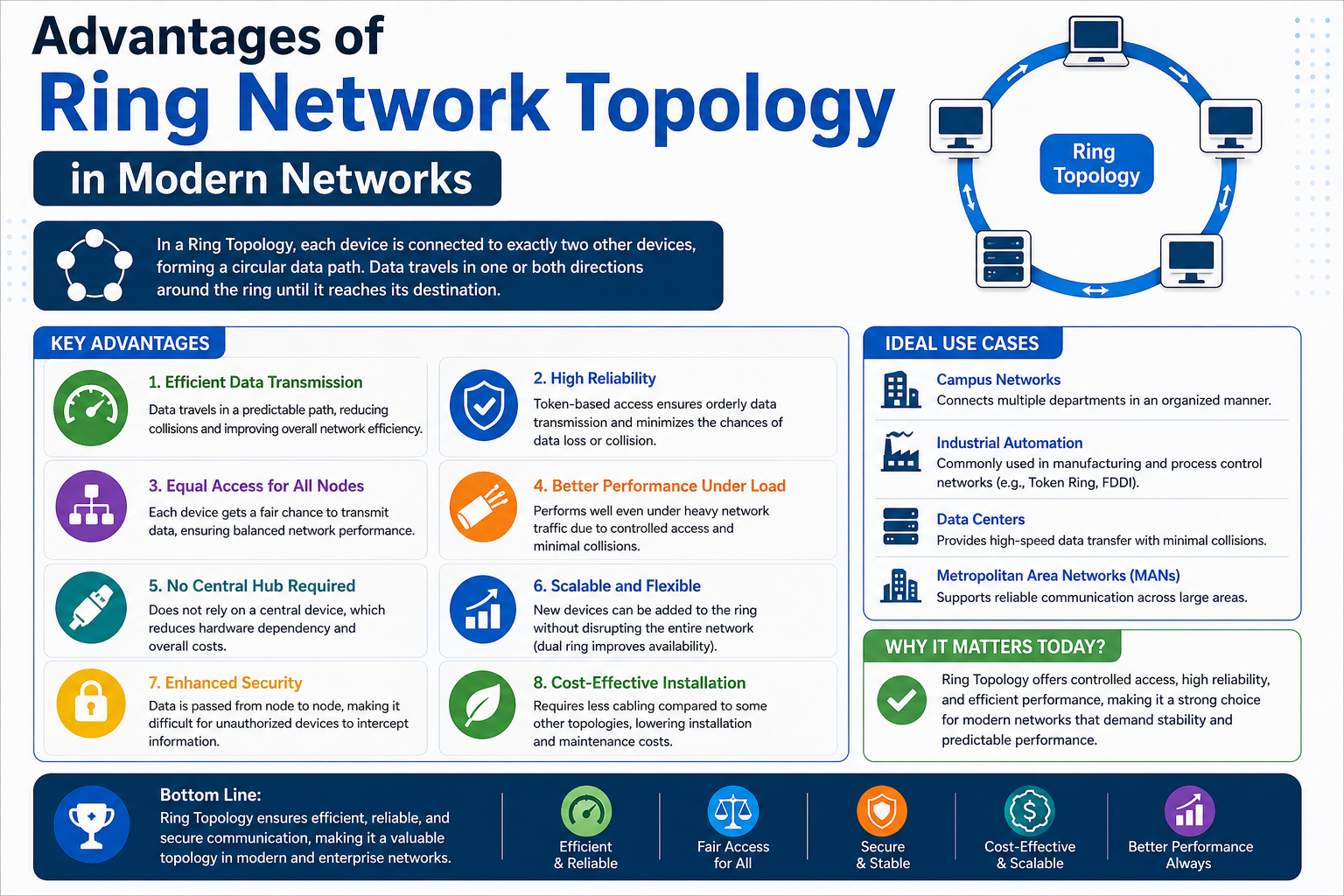
Ring network topology remains an important reference point in networking education because it represents one of the earliest structured methods for organizing communication between devices. Even though modern networks rarely use it in practical deployments, its design principles continue to appear in certification syllabi and theoretical discussions. The reason for this continued relevance is simple: ring topology solved several critical networking problems in its time, particularly those related to data collisions and fair access to transmission resources.
At its core, ring topology arranges devices in a circular formation where each device connects to exactly two neighboring devices. This structure creates a continuous loop for data flow, ensuring that every node is part of a unified communication path. Unlike more modern star-based systems where a central hub manages traffic, ring topology distributes responsibility evenly across all devices in the network. This equal participation model made it highly appealing during the early development of local area networks.
Fundamental Structure of a Ring Network System
The structure of a ring network is defined by its closed-loop configuration. Each device, often referred to as a node, is directly linked to two other nodes. This creates a circular pathway for data transmission, allowing information to circulate through the network in a predictable direction. In most traditional implementations, data flows in a single direction, although some variations allow dual-direction movement for improved redundancy.
This arrangement eliminates the need for a central controlling device, which was a significant advantage during early networking eras. However, it also meant that each node played an active role in maintaining the continuity of communication. If any single node or connection failed, the entire loop could potentially be disrupted, which highlights both the simplicity and vulnerability of the design.
Despite its limitations, the ring structure introduced a level of order and predictability that was not present in earlier bus-based systems. Every device had a defined place within the communication chain, which helped regulate how and when data was transmitted.
How Data Moves Through a Ring Network
Data transmission in a ring topology follows a sequential path. When a device wants to send information, the data is passed from one node to the next until it reaches its intended destination. Each intermediate node receives the data, examines the address, and decides whether to forward it or process it.
This step-by-step movement ensures that data travels in an orderly fashion, reducing the likelihood of simultaneous transmissions that could disrupt the network. Because each node handles data in sequence, the system avoids the chaotic overlap of signals that was common in earlier networking models.
The predictable flow of data also makes performance more consistent. Since there is a defined route for every transmission, network behavior becomes easier to anticipate. However, this also means that the speed of communication depends heavily on the number of nodes in the loop, as each additional device introduces a slight delay in the transmission chain.
The Role of Controlled Access in Ring Networks
One of the most important innovations associated with ring topology is the concept of controlled access. Instead of allowing all devices to transmit data freely at any time, ring networks use a structured method to determine which device has permission to send information. This approach prevents multiple devices from transmitting simultaneously, which significantly reduces the risk of data collisions.
Controlled access ensures that communication remains orderly and efficient, especially in environments where multiple devices need to share the same communication medium. By regulating transmission rights, the network maintains stability even under heavy usage.
This system was particularly valuable in early local area networks where hardware limitations made collision handling expensive and inefficient. By controlling access to the communication channel, ring topology minimized wasted bandwidth and improved overall reliability.
Understanding the Concept of Token-Based Communication
A defining feature of many ring network implementations is token-based communication. In this system, a special data packet known as a token circulates continuously around the ring. The token acts as a permission slip, granting the holder the right to transmit data.
When a device receives the token, it checks whether it has data to send. If it does, it attaches the data to the token and sends it along the network. If not, it simply passes the token to the next device. This ensures that only one device transmits at a time, eliminating the possibility of collisions.
The token system introduces fairness into the network. Every device eventually receives the opportunity to transmit, preventing any single node from dominating communication resources. This structured approach was highly effective in maintaining balance across early shared networks.
Advantages of Equal Access in Network Communication
One of the key strengths of ring topology is its ability to provide equal access to all connected devices. Since each node receives the token in a predictable sequence, every device gets a fair chance to communicate. This eliminates the issue of resource monopolization, where one device could otherwise consume most of the available bandwidth.
Equal access also contributes to improved network stability. Because transmission opportunities are evenly distributed, the system avoids congestion caused by simultaneous data requests. This makes ring topology particularly effective in environments where fairness and order are more important than raw speed.
Additionally, equal access helps maintain predictable performance. Network administrators can estimate how long it will take for a device to receive transmission rights, which simplifies planning and management.
Collision Prevention as a Core Strength
Collision prevention is one of the most significant technical achievements of ring topology. In earlier network designs, especially those that allowed free transmission, data collisions were common. These collisions occurred when multiple devices attempted to send information at the same time, resulting in data loss and retransmission delays.
Ring topology avoids this problem by ensuring that only one device can transmit at any given moment. The token mechanism enforces this rule strictly, making collisions virtually impossible under normal operation.
This improvement leads to more efficient use of network resources. Instead of spending time and bandwidth resolving transmission errors, the network can focus on delivering data smoothly and consistently. This was a major reason why ring topology was once considered superior to bus-based systems in certain environments.
Predictability and Stability in Data Flow
Another important benefit of ring topology is the predictability of data flow. Since each node has a fixed position in the transmission loop, network behavior becomes highly structured. Data always follows the same path, making it easier to analyze performance and diagnose issues.
This predictability also contributes to stability. In a well-functioning ring network, data moves at a consistent pace, and transmission delays remain relatively uniform. Unlike more dynamic systems where traffic can fluctuate unpredictably, ring topology offers a steady and controlled communication environment.
However, this predictability comes at the cost of flexibility. The rigid structure of the network makes it less adaptable to changes, especially when new devices need to be added or removed.
Performance Characteristics in Small and Medium Networks
Ring topology performs best in small to medium-sized networks where the number of nodes is limited. In such environments, the delay introduced by passing data from one node to another remains minimal, allowing the network to operate efficiently.
As the network grows, however, performance begins to degrade. Each additional node increases the time required for data or tokens to complete a full cycle around the ring. This can introduce noticeable latency, especially in systems with high communication demands.
Despite this limitation, ring topology was once considered a strong performer due to its ability to maintain consistent data flow without collisions. Its structured nature made it particularly suitable for controlled environments where network size remained stable.
Foundational Importance in Networking History
Ring topology holds a significant place in the evolution of computer networking. It represented a shift from unregulated communication models to more structured and controlled systems. By introducing mechanisms like token passing and sequential data flow, it laid the groundwork for more advanced networking technologies.
Even though modern networks have largely moved away from ring structures in favor of more scalable and flexible designs, the concepts developed within ring topology continue to influence networking principles today. Understanding its operation provides valuable insight into how network efficiency, fairness, and collision management evolved over time.
The study of ring topology also helps explain why certain design choices were made in later technologies, particularly those focused on improving scalability and fault tolerance.
Evolution of Ring Network Implementations in Real Systems
Ring topology did not remain a purely theoretical concept; it was implemented in real networking environments, most notably in early enterprise and institutional systems. One of the most recognized implementations was IBM’s Token Ring architecture, which brought structured ring communication into practical use. This system demonstrated how controlled access and token passing could be applied in real-world environments to manage shared network resources efficiently.
In these early deployments, ring networks were often chosen for their predictability and fairness in communication. Organizations that required stable and orderly data transmission found value in a system where every device had a guaranteed opportunity to communicate. This was especially important in environments where multiple users needed consistent access without interference from high-traffic devices.
However, even during its adoption phase, ring topology was considered specialized rather than universal. It required careful design and strict adherence to network rules, making it less flexible compared to emerging alternatives.
IBM Token Ring and Its Practical Significance
IBM Token Ring played a major role in bringing ring topology into mainstream networking discussions. It introduced a structured token-passing mechanism that controlled how devices accessed the network. The token acted as a regulating element, ensuring that only one device could transmit data at a time, thereby preventing collisions.
This system was particularly effective in corporate environments where network stability was more important than raw speed. Token Ring networks were known for their reliability and consistency under controlled conditions. The deterministic nature of token circulation allowed administrators to predict network behavior more accurately than in contention-based systems.
Despite these strengths, the complexity of installation and maintenance limited widespread adoption. Token Ring required specialized hardware and careful configuration, which increased costs and made it less attractive as Ethernet technologies began to evolve.
Dual Ring Architecture for Improved Reliability
To address one of the most critical weaknesses of basic ring topology—its vulnerability to a single point of failure—dual ring architecture was introduced. In this configuration, two separate rings operate in opposite directions, providing redundancy in communication paths.
If one ring experiences a failure or break, the second ring can continue to carry traffic, maintaining network functionality. This significantly improves fault tolerance and reduces the risk of complete network failure due to a single damaged connection or node.
Dual ring systems were widely used in fiber-based implementations such as FDDI networks. These systems were designed for high-speed backbone communication and were often deployed in environments where uptime was critical. However, the added redundancy also increased complexity and cost, making it suitable primarily for specialized use cases rather than general networking.
Failure Sensitivity and Network Vulnerability
One of the most significant disadvantages of ring topology is its sensitivity to failures. Because each device is part of a continuous loop, a break in any part of the network can disrupt communication across the entire system. This structural vulnerability made ring networks less resilient compared to topologies that allowed multiple alternative paths.
When a single node or connection fails, data cannot continue flowing through the ring unless redundancy mechanisms are in place. In basic ring systems without dual architecture, this results in a complete network interruption.
This dependency on every single node being functional created operational risks. Even minor hardware issues, such as a malfunctioning network interface card, could lead to widespread communication failure. As a result, organizations had to invest heavily in monitoring and maintenance to ensure network stability.
Troubleshooting Complexity in Ring Networks
Diagnosing issues in ring topology networks is often more difficult than in other architectures. Since data flows in a continuous loop, identifying the exact point of failure requires systematic inspection of each node and connection.
When a failure occurs, the entire network may stop functioning, making it challenging to determine which device is responsible. Technicians often need to physically or logically test each segment of the ring to locate the fault. This process can be time-consuming, especially in larger networks.
Unlike star topology, where a central hub simplifies troubleshooting, ring topology distributes responsibility across all nodes. While this improves fairness, it also increases diagnostic complexity. Maintenance teams must be highly methodical when resolving issues, which adds operational overhead.
Impact of Node Addition and Network Expansion Challenges
Expanding a ring network is not a straightforward process. Adding a new device requires temporarily breaking the existing loop, inserting the new node, and then restoring the connection. During this process, network communication may be interrupted.
This limitation makes scalability one of the weakest aspects of ring topology. In environments where growth is expected, constant restructuring of the network becomes impractical. Each addition increases complexity and risk, particularly if the network is already operating in a production environment.
Furthermore, as more devices are added, the time required for a token or data packet to complete a full cycle increases. This introduces additional latency, reducing overall performance efficiency. Over time, this scalability constraint became one of the primary reasons for the decline of ring topology in mainstream networking.
Latency Behavior in Expanding Ring Structures
Latency in ring networks is directly influenced by the number of nodes in the loop. Since data must pass through each device sequentially, every additional node contributes to transmission delay. While this delay may be negligible in small networks, it becomes more noticeable as the system grows.
The token-passing mechanism also introduces waiting time. Each device must wait for the token to reach it before it can transmit data. As the number of nodes increases, the interval between transmission opportunities becomes longer for each device.
This predictable but cumulative delay makes ring topology unsuitable for high-performance environments where low latency is critical. Modern networks prioritize direct and parallel communication paths to minimize such delays.
Comparison with Bus and Star Topologies in Practice
Ring topology was developed partly as an improvement over bus topology, which suffered from frequent collisions and performance degradation under heavy traffic. In contrast, ring networks eliminated collisions through structured token passing, offering a more stable communication model.
However, star topology eventually surpassed both systems in popularity due to its simplicity and scalability. In a star configuration, each device connects to a central hub, making it easier to manage, expand, and troubleshoot. This centralization reduces the complexity associated with ring structures.
While ring topology offered fairness and collision-free communication, it lacked the flexibility and resilience of star-based systems. Over time, the advantages of easier maintenance and scalability made star topology the dominant choice in modern networking.
Signal Flow Characteristics and Deterministic Behavior
One of the defining characteristics of ring topology is its deterministic data flow. Unlike networks where data can take multiple paths, ring topology enforces a fixed route. This ensures that data movement is predictable and follows a strict sequence.
This deterministic behavior simplifies network analysis and performance forecasting. Administrators can estimate transmission times and understand network load more easily. However, it also limits adaptability, as the system cannot dynamically reroute traffic in response to congestion or failures without additional mechanisms.
The rigidity of this structure is both a strength and a weakness. It enhances predictability but reduces flexibility, which is a critical factor in modern dynamic network environments.
Hardware Dependency and Infrastructure Requirements
Ring networks rely heavily on consistent and reliable hardware. Each node must be capable of forwarding data accurately and maintaining continuous communication with its neighbors. A failure in any single device can affect the entire system.
The cabling requirements also contribute to complexity. Since each device must connect to two others in a precise sequence, physical layout planning becomes essential. In some environments, this leads to inefficient space utilization or additional installation costs.
Fiber-based implementations, such as those used in high-speed backbones, further increase infrastructure costs. While they offer improved performance and distance capabilities, they also require specialized equipment and maintenance expertise.
Operational Control and Network Discipline Requirements
Ring topology requires strict operational discipline to function correctly. Devices must adhere to the rules of token passing and ensure that data is transmitted only when permitted. Any deviation from this protocol can disrupt the entire network.
This requirement for strict adherence makes ring networks more sensitive to configuration errors. Unlike more forgiving topologies, where misconfigurations may affect only a single device, ring networks can experience widespread disruption due to a single fault.
As a result, administrators must maintain careful control over network behavior. This includes monitoring token circulation, ensuring node health, and managing timing synchronization across devices.
Transition Away from Ring-Based Systems in Modern Networking
As networking technology evolved, the limitations of ring topology became more apparent. The rise of Ethernet and star-based systems offered greater scalability, simpler management, and improved fault tolerance. These advantages gradually led to the decline of ring-based architectures in general-purpose networking.
However, the principles developed in ring topology did not disappear. Concepts such as controlled access, orderly transmission, and fairness in resource allocation continue to influence modern network protocols and designs.
Even though ring topology is no longer widely used in everyday networking, it remains an important educational tool. It helps illustrate fundamental networking concepts and provides historical context for the evolution of communication systems.
Fault Tolerance Mechanisms in Ring Network Topology
Ring topology was originally designed with simplicity in mind, but over time engineers recognized that its biggest weakness was its sensitivity to failure. Because every device is part of a continuous loop, even a small disruption could interrupt communication for the entire network. To address this, several fault tolerance mechanisms were introduced to improve reliability without abandoning the core ring structure.
One of the earliest improvements was the introduction of bypass mechanisms. These allowed a failed node to be automatically skipped so that data could continue flowing through the network. In more advanced systems, intelligent hardware would detect a malfunctioning device and temporarily reroute traffic around it. While this added complexity, it significantly improved uptime in environments where continuous communication was essential.
Another important development was the use of dual ring structures, which provided redundancy by creating a secondary communication path. This ensured that even if one loop was broken, the network could continue operating through the backup path. These enhancements extended the lifespan of ring-based systems in enterprise and industrial environments.
Role of Redundancy in Improving Network Stability
Redundancy became a key design principle in improving ring network reliability. In its basic form, ring topology has no alternative routes for data transmission, which means every node and connection is critical. Redundancy introduced additional pathways that allowed the network to recover from failures more gracefully.
In dual-ring configurations, redundancy works by maintaining two opposite data flows. If one direction becomes disrupted, the other can continue to support communication. This significantly reduces downtime and helps maintain consistent performance even under fault conditions.
However, redundancy also introduces trade-offs. It increases the amount of hardware required and makes network configuration more complex. Despite these challenges, redundancy was essential for making ring topology viable in environments where reliability was a priority.
Data Transmission Efficiency Under Controlled Access Systems
Efficiency in ring networks is closely tied to their controlled access mechanism. Since only one device can transmit at a time, the network avoids the inefficiencies caused by data collisions. This makes the system highly efficient in environments with moderate traffic levels.
The controlled access model ensures that bandwidth is used in an organized manner. Each device receives a fair opportunity to transmit data, preventing any single node from overwhelming the network. This structured approach improves predictability and reduces wasted transmission cycles.
However, efficiency decreases as network size increases. The time required for the token or data packet to circulate grows with each additional node, leading to increased waiting times. This highlights the balance between fairness and speed that defines ring-based communication systems.
Timing and Synchronization in Ring Networks
Timing plays a crucial role in maintaining proper operation within a ring topology. Because data moves sequentially from one node to another, synchronization ensures that each device knows when to send and receive information.
In token-based systems, timing determines how long a device can hold the token before passing it along. This prevents any single node from monopolizing the network and helps maintain consistent flow. Proper synchronization also ensures that data packets are not lost or delayed due to timing conflicts.
Maintaining accurate timing across all nodes requires careful configuration. Any inconsistency in synchronization can lead to delays or disruptions in communication flow. This makes timing management a critical aspect of ring network design.
Bandwidth Utilization in Sequential Data Flow Systems
Bandwidth utilization in ring topology is influenced by its sequential nature. Since data travels through each node in a fixed order, the available bandwidth is shared across all devices in the loop. This ensures fair usage but can limit overall throughput.
In small networks, this shared approach works efficiently because the number of nodes is limited. However, as the network grows, bandwidth becomes increasingly divided among devices, reducing individual performance.
Despite this limitation, ring topology is effective in maintaining consistent bandwidth distribution. Unlike contention-based systems where traffic spikes can lead to congestion, ring networks provide a more stable and predictable bandwidth allocation model.
Token Lifecycle and Its Impact on Network Behavior
The lifecycle of a token is central to the operation of many ring networks. The token continuously circulates through the network, granting transmission rights to each node in turn. Its movement determines the rhythm of communication within the system.
When a device receives the token, it evaluates whether it has data to send. If it does, it attaches the data and transmits it along the ring. If not, the token is immediately passed along to the next device. This ensures that network resources are not wasted.
The efficiency of this system depends on how quickly the token completes a full cycle. A shorter cycle means faster communication opportunities for each device, while a longer cycle increases waiting time. This makes token management a critical factor in network performance.
Network Load Distribution Across Nodes
One of the advantages of ring topology is its even distribution of network load. Since each device participates equally in data transmission, no single node becomes overloaded with traffic responsibilities. This balanced structure helps maintain system stability.
Load distribution is inherently sequential, meaning each device handles a portion of the communication process in turn. This prevents bottlenecks that often occur in centralized systems where a single hub manages all traffic.
However, this uniform distribution also means that slower devices can affect overall performance. If one node processes data more slowly, it can delay the entire transmission cycle, impacting the efficiency of the whole network.
Hardware Role in Maintaining Continuous Communication
Hardware reliability is essential for maintaining continuous communication in ring networks. Each device must not only send and receive data but also forward it to the next node without interruption. This creates a dependency chain where every component plays a critical role.
Network interface cards, cabling, and connectors all contribute to the stability of the system. A failure in any of these components can disrupt the flow of data. As a result, ring networks require high-quality hardware to function effectively.
This dependency on hardware consistency made ring topology more expensive to maintain over time, especially in large-scale environments where even small hardware issues could have significant network-wide consequences.
Impact of Network Traffic Patterns on Ring Performance
Traffic patterns play a significant role in determining the efficiency of ring networks. In environments with steady and predictable traffic, ring topology performs well because its structured nature aligns with consistent communication demands.
However, in environments with bursty or unpredictable traffic, performance can degrade. Since devices must wait for their turn to transmit, sudden spikes in demand can lead to delays and increased latency.
The token system helps regulate traffic flow, but it cannot eliminate delays caused by high demand. This makes ring topology more suitable for controlled environments rather than dynamic or high-traffic systems.
Scalability Constraints and Structural Limitations
Scalability is one of the most significant limitations of ring topology. Adding new devices requires modifying the existing loop, which can temporarily disrupt network operations. This makes expansion more complex compared to other topologies.
As the network grows, the time required for data to circulate increases, reducing overall efficiency. Each additional node introduces latency and increases the workload on the token system.
These structural limitations make ring topology less suitable for modern networks that require frequent scaling and dynamic reconfiguration. Its rigid structure, while orderly, does not align well with the demands of large-scale or rapidly changing environments.
Maintenance Requirements in Ring-Based Systems
Maintaining a ring network requires continuous monitoring and careful management. Since every node is critical to the system, maintenance activities must be planned to avoid disrupting communication.
Even routine tasks such as replacing hardware or updating configurations can require temporarily breaking the ring. This adds operational complexity and increases the risk of downtime during maintenance windows.
As networks grow larger, maintenance becomes more resource-intensive. The need for precision and coordination makes ring topology less practical for environments that require high availability and minimal disruption.
Evolution of Ring Concepts into Modern Networking Ideas
Although ring topology is rarely used in its original form today, its concepts continue to influence modern networking systems. Ideas such as controlled access, orderly communication, and fair resource distribution are still relevant in various protocols and technologies.
Modern networks often incorporate hybrid approaches that borrow elements from ring structures while eliminating their limitations. For example, token-based logic can still be found in certain specialized systems where controlled access is required.
This evolution shows that while the physical structure of ring topology has largely been replaced, its conceptual contributions remain valuable in understanding how networks manage communication and resources.
Ring Topology in Industrial and Specialized Environments
Although ring topology is no longer common in everyday office or home networks, it still finds relevance in certain industrial and specialized environments. These settings often prioritize predictability, controlled communication, and deterministic behavior over flexibility or scalability. In such cases, the structured nature of ring-based communication can still offer practical advantages.
Industrial control systems, for example, sometimes rely on ring-like designs to ensure consistent data flow between machines. These environments typically operate with fixed numbers of devices and well-defined communication patterns, which aligns well with the rigid structure of a ring network. Because the network does not frequently change, the limitations related to scalability become less of a concern.
Another area where ring principles remain relevant is in certain backbone or transport-level network designs. Even when not implemented as a pure ring, the concept of circular redundancy and dual-path routing can still be found in modern fiber-based infrastructure.
Deterministic Networking and Predictable Communication Flow
One of the most valuable characteristics of ring topology is its deterministic behavior. In networking terms, deterministic communication means that data transmission occurs in a predictable and pre-planned manner rather than being influenced by random access or competition between devices.
This predictability allows administrators to estimate transmission delays and network performance with a high degree of accuracy. Since each device gets a defined opportunity to send data, the system avoids uncertainty in communication timing.
Deterministic flow is especially important in environments where timing consistency is more important than speed. Applications such as synchronized machine operations or controlled data acquisition benefit from this structured communication model. Even though modern networks often prioritize flexibility, deterministic behavior remains an important design goal in specific use cases.
Security Implications of Ring-Based Communication
Ring topology also presents unique security characteristics due to its structured flow of data. Since all communication passes through a defined sequence of nodes, monitoring and controlling data movement can be more straightforward in controlled environments.
The predictable path of data makes it easier to implement surveillance and traffic analysis within the network. Unauthorized behavior can be detected more easily when every transmission follows a known route.
However, this same predictability can also introduce risks. If a malicious actor gains control of a node within the ring, they may be able to intercept or manipulate data as it passes through. Because every device is part of the communication chain, a single compromised node can potentially impact the entire network.
Energy and Resource Efficiency Considerations
Ring topology can offer certain efficiencies in terms of resource usage, particularly in controlled environments. Because data transmission is regulated and collisions are eliminated, unnecessary retransmissions are minimized. This reduces wasted bandwidth and improves overall communication efficiency.
From an energy perspective, devices in a ring network may operate in a more predictable pattern, reducing the need for constant high-intensity processing. Each node only transmits when it receives permission, which can lead to more balanced resource consumption.
However, these benefits are offset by the need for continuous participation from all nodes. Since every device plays a role in forwarding data, all nodes must remain active and responsive, which can limit potential energy savings in large deployments.
Legacy Value of Ring Topology in Networking Education
Even though ring topology is rarely used in modern network design, it continues to hold significant educational value. Understanding ring structures helps learners grasp fundamental networking concepts such as data flow control, collision avoidance, and token-based access.
By studying ring topology, students can better understand why modern systems evolved toward more flexible and scalable architectures. It serves as a historical reference point that illustrates the trade-offs between fairness, performance, and complexity.
Many networking certification programs still include ring topology as part of their curriculum because it provides insight into the evolution of network design principles. It also helps explain why certain modern protocols prioritize decentralization and fault tolerance.
Transition from Ring-Based Systems to Ethernet Dominance
The decline of ring topology is closely tied to the rise of Ethernet-based networking. Ethernet introduced a more flexible approach to communication, allowing devices to transmit data more freely while still managing collisions through improved protocols.
Unlike ring networks, Ethernet systems do not require a fixed circular structure. This makes them easier to install, expand, and maintain. As Ethernet technology advanced, it began to offer higher speeds, better scalability, and lower cost, which gradually replaced the need for ring-based systems in most environments.
This transition marked a major shift in networking philosophy, moving from rigid, deterministic structures to more adaptive and scalable designs.
Hybrid Networking Models Inspired by Ring Principles
Even though pure ring topology is largely obsolete, some of its principles continue to influence hybrid network models. These systems combine elements of different topologies to achieve better performance and reliability.
For example, some modern networks incorporate circular redundancy paths inspired by dual-ring structures. These designs allow traffic to reroute automatically in case of failure, improving fault tolerance without fully relying on a traditional ring layout.
Hybrid systems often aim to balance the predictability of ring communication with the flexibility of star or mesh topologies. This blending of concepts demonstrates how older network ideas continue to evolve rather than disappear completely.
Limitations That Led to the Decline of Ring Networks
Several inherent limitations contributed to the decline of ring topology in mainstream networking. Its most significant weakness is the dependency on every node within the loop. A single failure can disrupt the entire system unless additional redundancy is implemented.
Another limitation is scalability. Expanding a ring network requires interrupting the existing structure, which is impractical in dynamic environments where devices are frequently added or removed.
Latency also becomes a growing concern as the network expands. Because data must pass through each node sequentially, performance degrades as the number of devices increases. These combined limitations made ring topology less suitable for modern high-demand networks.
Conceptual Influence on Modern Network Protocols
Despite its physical decline, ring topology has left a lasting conceptual influence on modern networking protocols. The idea of controlled access, where devices take turns transmitting data, is still used in various forms of network coordination systems.
Similarly, the concept of orderly data flow continues to inspire scheduling and traffic management techniques in more advanced networks. Even systems that appear completely different from ring structures may still incorporate similar principles under the surface.
This shows that ring topology’s importance lies not only in its physical implementation but also in the foundational ideas it introduced to the field of networking.
Long-Term Relevance in Understanding Network Evolution
Studying ring topology provides valuable insight into how networking systems evolve over time. It represents a stage in technological development where simplicity and order were prioritized over scalability and flexibility.
By examining its strengths and weaknesses, it becomes easier to understand why modern networks are designed the way they are. Concepts such as redundancy, decentralization, and dynamic routing can be better appreciated when compared to earlier rigid systems like ring topology.
In this sense, ring topology remains relevant not as a practical solution, but as a historical and educational framework that helps explain the evolution of network engineering.
Final Conclusion
Ring topology played a crucial role in the early development of computer networks by introducing structured communication, collision-free data transmission, and fair access through token-based systems. Its predictable behavior and orderly design made it an effective solution for small and controlled environments.
However, its limitations in scalability, fault tolerance, and flexibility led to its replacement by more advanced topologies such as star and mesh networks. Despite this, its influence continues to shape modern networking concepts, particularly in areas involving controlled access and redundancy.
Understanding ring topology remains important because it provides a foundation for appreciating how far networking technology has evolved and why modern systems are designed the way they are today.