Network automation has rapidly become a core part of how modern infrastructure is designed, managed, and scaled. Instead of manually logging into each device and applying configurations one by one, engineers now rely on automation to handle repetitive tasks, enforce consistency, and reduce human error. This shift is not just about convenience; it is about building networks that are faster to deploy, easier to maintain, and more reliable under pressure.
As organizations grow, so does the complexity of their networks. Multiple vendors, mixed operating systems, and large distributed environments make manual management inefficient and risky. This is where Python has become a preferred language for network engineers. Its simplicity, readability, and vast ecosystem of libraries allow professionals to automate everything from configuration changes to full-scale network validation.
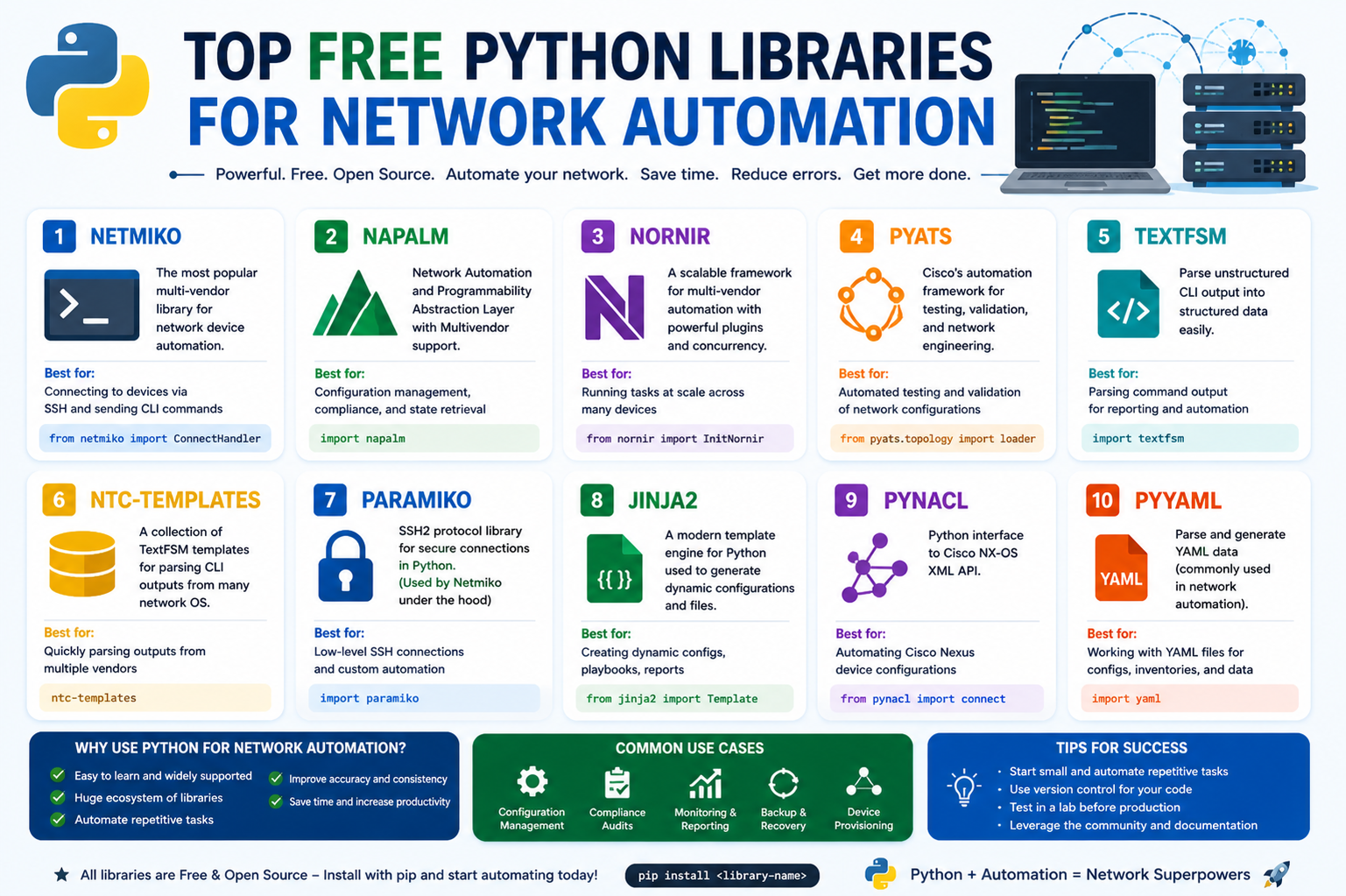
The challenge today is not a lack of tools but the overwhelming number of them. Engineers often struggle to decide which libraries are worth learning and which ones provide real-world stability. Among many available options, a small group of Python libraries has proven itself through consistent use in production environments. These tools are widely adopted, well-supported, and designed specifically for network automation tasks.
One of the most important advantages of these libraries is abstraction. Instead of dealing with low-level protocol details, engineers can interact with devices using simplified commands and structured data. This significantly reduces development time and allows teams to focus more on network logic rather than communication complexity.
In the following sections, we begin exploring some of the most trusted and widely used Python libraries that form the backbone of modern network automation workflows. Each tool has its own strengths, but together they provide a powerful foundation for building scalable and efficient automation systems.
Netmiko for Simplified SSH-Based Network Device Automation
Netmiko is one of the most widely used Python libraries in network automation because it simplifies how engineers interact with network devices over SSH. At its core, it is built on top of a lower-level SSH library, but it adds a powerful abstraction layer specifically designed for networking equipment. This means engineers do not have to deal with raw SSH sessions or manually handle device-specific quirks.
One of the biggest advantages of Netmiko is its awareness of different network operating systems. Devices from different vendors often behave differently when executing commands, especially when entering configuration modes or applying changes. Netmiko understands these differences and automatically adjusts its behavior depending on the device type. This reduces the need for writing custom logic for each vendor, which is one of the biggest challenges in multi-vendor environments.
For example, when interacting with a device that requires entering a privileged configuration mode before applying changes, Netmiko automatically handles this transition. Instead of manually sending multiple commands and tracking session states, the engineer can simply issue high-level instructions, and Netmiko takes care of the rest in the background. This makes automation scripts shorter, cleaner, and significantly easier to maintain.
Another important strength of Netmiko is its ability to work with command output in a more structured way when combined with parsing tools. In traditional network operations, command outputs are often unstructured text, which can be difficult to analyze programmatically. Netmiko integrates smoothly with parsing solutions that convert this output into structured data formats, making it easier to extract meaningful information from devices.
This becomes extremely useful in large environments where engineers need to gather information from hundreds or thousands of devices. Instead of manually reading through raw command outputs, automation scripts can extract specific fields such as interface status, routing information, or system health metrics.
Netmiko also supports a wide range of network devices, making it a flexible choice for environments that include multiple vendors. Whether working with routers, switches, or firewalls, engineers can use the same library interface to perform consistent operations across the entire infrastructure.
In addition to configuration tasks, Netmiko is commonly used for operational commands such as retrieving device status, checking logs, or validating network behavior. Because it simplifies SSH interactions, it is often one of the first libraries introduced to engineers who are new to network automation.
Over time, Netmiko has become a foundational tool in many automation workflows. Its simplicity, reliability, and strong community support make it a dependable choice for both small projects and large-scale enterprise automation systems. It does not attempt to solve every problem but instead focuses on doing one thing very well: making SSH-based network automation easier and more consistent.
Why Netmiko Reduces Complexity in Real Network Environments
One of the key reasons Netmiko is so valuable in real-world environments is its ability to reduce hidden complexity. Network devices often require precise sequences of commands, and even small variations between vendors can cause automation scripts to fail. Netmiko eliminates much of this uncertainty by standardizing how connections and commands are handled.
This is especially important in environments where multiple engineers are working on automation scripts. Without a consistent tool, each engineer might implement their own SSH handling logic, leading to fragmented and difficult-to-maintain codebases. Netmiko provides a unified approach that improves collaboration and code reuse across teams.
Another major benefit is error handling. Network connections are not always stable, and automation scripts must be able to handle unexpected disconnections or timeouts. Netmiko includes built-in mechanisms to manage these situations more gracefully, reducing the likelihood of complete script failure during execution.
It also improves efficiency by managing session persistence. Instead of opening and closing SSH sessions repeatedly, Netmiko can maintain sessions for multiple operations, reducing overhead and improving performance when working with large numbers of devices.
Because of these capabilities, Netmiko is often used as the first building block in more advanced automation systems. Engineers frequently combine it with other libraries to create full automation pipelines that handle configuration, validation, and reporting in a single workflow.
As network environments continue to grow in complexity, tools like Netmiko play a crucial role in simplifying operational tasks and enabling engineers to scale their automation efforts without increasing manual workload.
Early Foundation of Network Automation with Python
Before advanced orchestration systems became common, network automation was largely built around simple scripts that executed commands over SSH. Python quickly became the preferred language for this task due to its readability and strong support for network-related libraries.
Netmiko emerged as one of the earliest tools that made this process practical for real-world use. It bridged the gap between basic scripting and professional-grade automation by providing a reliable interface for interacting with network devices.
This foundational role is one of the reasons Netmiko remains relevant today. Even as newer tools and protocols have been introduced, many modern automation systems still rely on Netmiko at some level because of its stability and simplicity.
Its design philosophy focuses on reducing barriers for engineers who may not have extensive programming backgrounds. By abstracting complex SSH operations into simple function calls, it allows network professionals to focus on infrastructure logic rather than programming details.
This approach has made it a stepping stone for many engineers entering the field of network automation. Once they become comfortable with Netmiko, they often move on to more advanced libraries and frameworks, building on the concepts they learned.
Netmiko continues to serve as a reliable entry point into the world of automated network management, making it one of the most important tools in the Python networking ecosystem.
Transition Toward More Advanced Automation Concepts
As network automation evolves, tools like Netmiko often serve as the starting point for more advanced workflows. Engineers who begin with simple SSH automation eventually expand into areas such as API-based management, configuration validation, and automated testing.
Netmiko plays an important role in this transition by helping engineers understand how automated communication with devices works in practice. Once the fundamentals are clear, it becomes easier to adopt more complex tools and frameworks that build on similar concepts.
This gradual learning path is one of the reasons Python has become so dominant in network automation. It allows engineers to start simple and progressively adopt more powerful techniques without changing languages or ecosystems.
Netmiko remains a key part of this journey, providing a stable foundation for understanding how automation interacts with real network infrastructure.
NAPALM for Multi-Vendor Network Abstraction and Unified Management
NAPALM is a powerful Python library designed to simplify how engineers interact with network devices across different vendors. In real-world networks, one of the biggest challenges is dealing with inconsistency. Every vendor tends to implement its own command structure, output format, and configuration logic. This makes automation difficult because scripts often need to be rewritten or heavily modified depending on the device type.
NAPALM addresses this problem by introducing a unified API layer. Instead of writing vendor-specific logic for each device, engineers can use a single set of standardized functions. These functions are then translated internally into the appropriate commands for each platform. This abstraction significantly reduces complexity and improves scalability in heterogeneous network environments.
One of the most important concepts in NAPALM is the idea of “getters.” Getters are pre-defined methods that retrieve specific types of operational data from network devices. For example, instead of manually writing different commands for different vendors to retrieve routing information, an engineer can simply use a single getter function. NAPALM then handles the translation behind the scenes.
This becomes especially powerful in multi-vendor environments. Consider a network where some devices are from one vendor, others from another, and additional equipment comes from a third source. Without abstraction, each device type would require unique scripts. With NAPALM, a single function call can retrieve consistent data from all devices regardless of manufacturer.
Another major advantage of NAPALM is its ability to return structured data. Traditional network device outputs are usually unstructured text, which is difficult to process programmatically. NAPALM converts this output into structured formats such as JSON-like objects, making it much easier to analyze, compare, and store.
This structured approach is extremely useful in automation workflows that involve monitoring or reporting. Instead of manually parsing command output, engineers can directly access specific fields such as interface status, routing neighbors, or system uptime. This reduces both development time and the likelihood of errors in scripts.
NAPALM also supports configuration management features. Engineers can retrieve the current configuration, compare it with a desired state, and apply updates in a controlled manner. This is particularly important in environments that follow infrastructure-as-code principles, where configuration consistency is critical.
One of the strengths of NAPALM is its flexibility in handling different operating systems. Whether working with traditional enterprise devices or modern network platforms, NAPALM provides a consistent interface. This allows engineers to build automation systems that are not tied to a single vendor ecosystem.
Because of this flexibility, NAPALM is often used in larger automation frameworks where consistency across devices is essential. It reduces the need for maintaining multiple scripts and allows teams to focus on logic rather than compatibility issues.
In many production environments, NAPALM is used alongside other libraries to build comprehensive automation pipelines. It handles data retrieval and configuration abstraction, while other tools manage communication, testing, or orchestration layers. This modular approach improves maintainability and scalability.
NAPALM’s design also encourages best practices in automation. By enforcing structured interactions with devices, it reduces the risk of inconsistent configurations and human error. This makes it a reliable choice for organizations aiming to standardize their network operations.
Overall, NAPALM plays a critical role in simplifying multi-vendor network management by providing a consistent and predictable interface for interacting with diverse infrastructure components.
Understanding the Getter Model in NAPALM
The getter model in NAPALM is one of its most important features because it defines how data is retrieved from network devices. Instead of writing device-specific commands, engineers use predefined functions that represent common operational queries.
Each getter is designed to retrieve a specific type of information, such as interface details, routing tables, or device facts. When a getter is called, NAPALM automatically determines the correct commands required for the underlying platform and executes them on the device.
This abstraction eliminates the need for engineers to memorize or manage different command syntaxes across vendors. It also reduces the risk of errors caused by slight differences in command structures.
The results returned by getters are standardized, meaning the output format remains consistent regardless of the device being queried. This consistency is extremely valuable when building automation systems that need to process data from multiple sources.
For example, when retrieving routing information, different devices may present data in completely different formats. One device might use tabular text output, while another uses hierarchical formatting. NAPALM converts all of this into a unified structure that can be easily processed.
This standardization also simplifies integration with other systems such as monitoring tools or dashboards. Since the data format remains consistent, it can be easily consumed by external applications without additional parsing logic.
The getter model also improves maintainability. When network infrastructure changes or new devices are added, automation scripts do not need major modifications. As long as the device is supported by NAPALM, the same getter functions continue to work.
This makes it easier for engineering teams to scale their automation efforts without constantly rewriting code. It also ensures that automation systems remain stable even as the underlying network evolves.
In practice, getters are often used in combination with scheduling systems or monitoring frameworks. This allows organizations to continuously collect network data and detect anomalies or configuration changes in real time.
The simplicity and consistency of the getter model are key reasons why NAPALM is widely adopted in enterprise environments where reliability and scalability are critical.
Genie for Network State Learning and Intelligent Validation
Genie is a Python-based framework designed to provide deep visibility into network state and enable automated validation and testing. Unlike traditional automation tools that focus mainly on configuration, Genie focuses on understanding and comparing the actual state of the network.
One of the most powerful concepts in Genie is state learning. This allows engineers to capture a complete snapshot of a network’s operational state at a given moment. This snapshot includes detailed information about protocols, interfaces, routing behavior, and other critical components.
Once this baseline is captured, it can be used for comparison at a later time. If something changes in the network, Genie can identify exactly what has changed and highlight the differences in a structured format.
This approach is extremely useful for troubleshooting. Instead of manually checking multiple devices and comparing outputs, engineers can rely on Genie to automatically detect deviations from the expected state.
Genie is often used in environments where stability and predictability are essential. By continuously capturing and comparing network states, it becomes easier to detect misconfigurations or unexpected behavior before they cause larger issues.
The framework integrates closely with automation testing systems, making it a valuable tool for validation in continuous integration pipelines. This ensures that changes to the network do not introduce unintended side effects.
Another important aspect of Genie is its ability to interpret complex network protocols. It supports a wide range of technologies, allowing engineers to gain detailed insights into how different parts of the network are functioning.
This makes it particularly useful in large-scale environments where multiple protocols and technologies are in use simultaneously. Instead of manually analyzing each component, Genie provides a unified view of the entire network state.
Genie also simplifies documentation of network behavior. By capturing structured snapshots, it becomes easier to understand how the network is operating at any given time. This can be useful for audits, troubleshooting, or capacity planning.
Because it is built on a flexible architecture, Genie can be integrated into broader automation systems. It works well alongside other libraries, providing validation and state analysis capabilities within larger workflows.
In many cases, Genie is used not only for troubleshooting but also for proactive monitoring. By regularly capturing network state snapshots, engineers can detect gradual changes that may indicate potential issues.
This proactive approach helps improve network reliability and reduces downtime by identifying problems before they escalate.
Overall, Genie provides a powerful set of tools for understanding, validating, and comparing network behavior in a structured and automated way, making it an essential component of modern network automation strategies.
NCClient for NETCONF-Based Network Automation and API Control
NCClient is a specialized Python library designed to simplify automation over the NETCONF protocol, which is widely used for programmatic network device management. Unlike traditional command-line based interactions, NETCONF allows engineers to communicate with devices using structured data, enabling more precise and controlled configuration changes.
One of the main challenges with NETCONF is that it relies on XML-based communication, which can feel complex and verbose when handled manually. NCClient solves this problem by providing a clean Python interface that abstracts much of the underlying XML handling. Instead of constructing raw XML payloads, engineers can use simple method calls to perform configuration and operational tasks.
This abstraction is extremely valuable in modern network environments where consistency and accuracy are critical. Manual configuration through CLI commands can introduce errors due to formatting or syntax differences, but NETCONF interactions through NCClient are structured and predictable.
NCClient introduces the concept of a “Manager” object, which acts as the primary interface between Python scripts and network devices. Through this manager, engineers can execute remote procedure calls, retrieve device data, and apply configuration changes in a controlled manner.
One of the key advantages of using NCClient is its support for both configuration and operational data retrieval. Engineers can query device state, retrieve configuration details, and even make precise updates to specific parts of a device configuration without affecting unrelated settings.
This level of granularity is especially important in large networks where small changes can have wide-reaching effects. Instead of replacing entire configurations, NCClient allows targeted modifications, reducing the risk of unintended disruptions.
Another important feature is the ability to lock device configurations during changes. This ensures that no other process modifies the configuration while an update is in progress. This locking mechanism is crucial in environments where multiple automation systems or engineers may be interacting with the same device simultaneously.
NCClient also supports filtering mechanisms such as subtree and XPath filtering. These tools allow engineers to request only specific portions of configuration or operational data, reducing unnecessary data transfer and improving efficiency.
For example, instead of retrieving an entire device configuration, an engineer can query only interface-related settings or routing information. This makes automation workflows faster and more efficient, especially when working with large-scale infrastructures.
Because NCClient operates directly with NETCONF-enabled devices, it is often used in environments that prioritize API-based automation over traditional CLI methods. This aligns with modern infrastructure practices where systems are designed to be programmable and consistent.
In many automation architectures, NCClient is used as a backend communication layer. Higher-level tools or frameworks may define the logic of automation workflows, while NCClient handles the actual communication with devices.
This separation of concerns improves modularity and makes automation systems easier to maintain. Engineers can update or replace components without affecting the entire system, as long as the interface between layers remains consistent.
NCClient is particularly useful in environments that require strict configuration control and auditing. Because all changes are structured and traceable, it becomes easier to track modifications and ensure compliance with network policies.
It also integrates well with other Python-based automation tools, allowing it to be part of larger orchestration systems. Whether used for configuration deployment, compliance checks, or operational monitoring, NCClient provides a reliable interface for NETCONF-based interactions.
Overall, NCClient plays an important role in enabling structured, API-driven network automation, especially in environments that require precision, control, and consistency across devices.
The Role of NETCONF in Modern Network Automation
NETCONF is a network management protocol designed to provide a structured and programmatic way of interacting with network devices. Unlike traditional CLI-based management, NETCONF uses structured data formats that are easier to process and automate.
One of the key advantages of NETCONF is its ability to separate configuration and operational data. This separation allows engineers to clearly distinguish between what a device is configured to do and what it is currently doing.
This clarity is essential in automation systems where accuracy and predictability are important. By working with structured data, engineers can build reliable automation workflows that reduce ambiguity and improve consistency.
NETCONF also supports transactional operations, meaning configuration changes can be applied in a controlled manner. If something goes wrong during an update, changes can be rolled back, preventing partial or inconsistent configurations.
This transactional capability is particularly useful in large-scale networks where even small configuration errors can lead to service disruptions. It adds an extra layer of safety to automation processes.
Another important feature of NETCONF is its ability to lock configuration datastores during updates. This prevents conflicts when multiple processes attempt to modify the same device simultaneously.
This locking mechanism ensures that configuration changes are applied in a controlled and predictable manner, reducing the risk of conflicts or corruption.
NETCONF is also designed to be extensible, allowing vendors to define custom capabilities while still adhering to a standard framework. This makes it suitable for multi-vendor environments where flexibility is required.
In modern network automation, NETCONF is often used alongside APIs such as RESTCONF, which provide similar functionality using HTTP-based communication. Together, these protocols form the foundation of API-driven network management.
NCClient acts as a bridge between Python automation scripts and NETCONF-enabled devices, making it easier for engineers to take advantage of these capabilities without dealing with low-level protocol details.
This combination of structured communication and Python-based automation provides a powerful foundation for building scalable and reliable network systems.
Requests Library for REST-Based Network Automation and API Interaction
The Requests library is one of the most widely used Python libraries for handling HTTP communication, and it plays an important role in modern network automation through REST-based APIs such as RESTCONF.
Unlike NETCONF, which uses XML and structured protocol operations, REST-based systems rely on standard HTTP methods such as GET, POST, PUT, and DELETE. These methods make it easier for engineers to interact with network devices using familiar web-based concepts.
Requests simplifies this process by providing a clean and intuitive interface for sending HTTP requests. Instead of manually handling connections, headers, or payload formatting, engineers can use simple function calls to interact with APIs.
One of the most important features of the Requests library is its ability to handle responses in a structured way. Each request returns a response object that contains useful information such as status codes, response data, and headers.
This makes it easy to determine whether a request was successful or if an error occurred. Engineers can also implement exception handling to manage failed requests gracefully, improving the reliability of automation scripts.
In network automation, Requests is often used to interact with RESTCONF APIs provided by modern network devices. These APIs expose configuration and operational data in a structured format, usually JSON, which is easy to process in Python.
By using Requests, engineers can retrieve device information, apply configuration changes, or monitor network status without relying on traditional command-line interfaces.
This approach aligns with the broader shift toward API-driven infrastructure, where systems are designed to be programmatically accessible rather than manually configured.
Requests also supports authentication mechanisms, which are essential when working with secure network devices. Engineers can easily include credentials or tokens in their requests to ensure secure communication.
Because of its simplicity and flexibility, Requests is often used as a foundational tool in network automation scripts. It can be combined with other libraries to build more complex workflows that involve data collection, analysis, and configuration management.
In many cases, Requests serves as the communication layer for REST-based automation systems, while other tools handle logic and processing.
Its widespread adoption and ease of use make it an essential component of modern Python-based network automation, especially in environments that rely on REST APIs for device management.
Expanding Automation with Requests in Real Network Environments
The Requests library becomes especially powerful in real-world network automation when it is used as the bridge between Python scripts and REST-based network APIs. Modern network devices increasingly expose RESTful interfaces that allow engineers to interact with configurations and operational data using standard HTTP methods. This shift has made network automation more accessible and aligned with general web development practices.
One of the key strengths of Requests is its simplicity. Even complex interactions with network devices can be reduced to a few lines of Python code. Instead of dealing with low-level socket programming or manually handling HTTP connections, engineers can focus entirely on what data they want to retrieve or modify.
This simplicity becomes very important when building scalable automation systems. In large infrastructures, scripts often need to communicate with hundreds or thousands of devices. A lightweight and reliable library like Requests ensures that these operations remain manageable and easy to maintain.
Another important aspect is how Requests handles response objects. Every interaction with a network API returns a structured response that includes status information, headers, and content. This allows engineers to quickly determine whether a request was successful or if something went wrong during execution.
Error handling is also a major benefit. Instead of silently failing or producing unclear results, Requests allows scripts to explicitly check response codes and raise exceptions when needed. This makes automation workflows more predictable and safer to run in production environments.
In REST-based network automation, data is usually returned in JSON format. Requests integrates naturally with this structure, allowing engineers to easily convert responses into Python dictionaries. This makes it simple to extract specific fields such as interface statistics, routing information, or system status.
Because of this tight integration, Requests is often used as the foundation for more advanced automation frameworks. It handles the communication layer while other components focus on decision-making, data analysis, or orchestration logic.
In modern networks, REST APIs are becoming more common because they are lightweight and easy to scale. As a result, Requests has become an essential tool for interacting with next-generation network devices and controllers.
Its flexibility also allows it to be used in hybrid environments where both legacy CLI-based systems and modern API-driven systems coexist. Engineers can combine Requests with other libraries to create unified automation workflows across different types of infrastructure.
Over time, Requests has become more than just an HTTP library. In the context of network automation, it acts as a key enabler for API-first infrastructure management, supporting the shift away from manual configuration methods toward fully programmable networks.
Role of Ansible in Network Automation Ecosystems
Ansible is a widely adopted automation tool that plays a significant role in network management, even though it is not strictly a Python library. It is built using Python internally and integrates deeply with Python-based automation workflows, making it highly relevant in this ecosystem.
One of the main advantages of Ansible is its agentless architecture. This means that it does not require any additional software to be installed on network devices. Instead, it communicates over standard protocols such as SSH or APIs, which makes deployment simple and scalable.
Ansible uses a declarative approach to automation. Instead of writing step-by-step instructions, engineers define the desired state of the network, and Ansible ensures that the system reaches that state. This is a major shift from traditional scripting methods, where every action must be explicitly defined.
This approach is particularly useful in network environments where consistency is important. By defining the end state rather than individual steps, Ansible reduces complexity and minimizes the risk of configuration drift.
Another important feature of Ansible is its use of playbooks. These are structured files written in a simple format that describe automation tasks. Playbooks allow engineers to organize complex workflows in a clear and readable way.
Because playbooks are easy to understand, Ansible is often used not only by developers but also by network engineers who may not have strong programming backgrounds. This accessibility has contributed to its widespread adoption in enterprise environments.
Ansible also provides a large collection of modules specifically designed for network automation. These modules allow engineers to interact with different types of network devices, apply configurations, and retrieve operational data without writing custom code for each task.
In more advanced use cases, Ansible can be extended using Python. Engineers can create custom modules or inventory scripts to handle specialized automation requirements. This flexibility makes it suitable for both simple tasks and highly complex workflows.
Another strength of Ansible is its ability to manage orchestration across multiple systems. It can coordinate changes across servers, network devices, and applications in a single workflow. This makes it a powerful tool for full-stack infrastructure automation.
In network automation scenarios, Ansible is often used for configuration management, compliance enforcement, and deployment automation. It ensures that network devices remain consistent with defined policies and reduces manual intervention.
Its scalability is another key advantage. Whether managing a small lab environment or a large enterprise network, Ansible can handle automation tasks efficiently without significant changes to the underlying logic.
Because of these capabilities, Ansible has become a central component in many automation strategies. It complements Python libraries like Netmiko, NAPALM, and Requests by providing higher-level orchestration and workflow management.
Building a Complete Network Automation Stack
When combined, tools like Netmiko, NAPALM, Genie, NCClient, Requests, and Ansible form a complete ecosystem for network automation. Each tool serves a specific purpose, but together they cover the entire lifecycle of network management.
Netmiko handles SSH-based device communication, making it easy to execute commands and retrieve outputs. NAPALM provides abstraction across different vendors, ensuring consistency in multi-vendor environments. Genie focuses on network state learning and validation, helping engineers detect and analyze changes.
NCClient enables structured communication through NETCONF, allowing precise configuration control. Requests supports REST-based interactions with modern APIs, making it essential for API-driven environments. Ansible provides orchestration and workflow automation, tying everything together into a unified system.
This layered approach is what makes modern network automation so powerful. Instead of relying on a single tool, engineers can combine multiple libraries to build flexible and scalable systems tailored to their specific needs.
Each tool reduces complexity in a different area. Some simplify communication, others standardize data, and some manage workflows. Together, they eliminate much of the manual effort traditionally required in network operations.
As networks continue to evolve, this ecosystem approach becomes even more important. No single tool can solve every problem, but a well-designed combination of tools can handle nearly all aspects of network automation effectively.
Final Thoughts
The landscape of network automation continues to expand as infrastructure becomes more complex and demand for efficiency increases. Python has established itself as a dominant language in this field due to its simplicity and powerful ecosystem.
Libraries such as Netmiko, NAPALM, Genie, NCClient, and Requests each address specific challenges in network automation. Together with tools like Ansible, they form a complete toolkit for building modern, scalable, and reliable network systems.
What makes these tools valuable is not only their technical capabilities but also their maturity and community support. They have been tested in real production environments and continue to evolve alongside industry needs.
For engineers entering the field, learning these libraries provides a strong foundation for understanding how modern networks are managed. They offer practical experience in automation, API interaction, configuration management, and network validation.
As organizations continue moving toward fully automated and programmable infrastructure, these Python-based tools will remain central to how networks are designed, operated, and maintained.