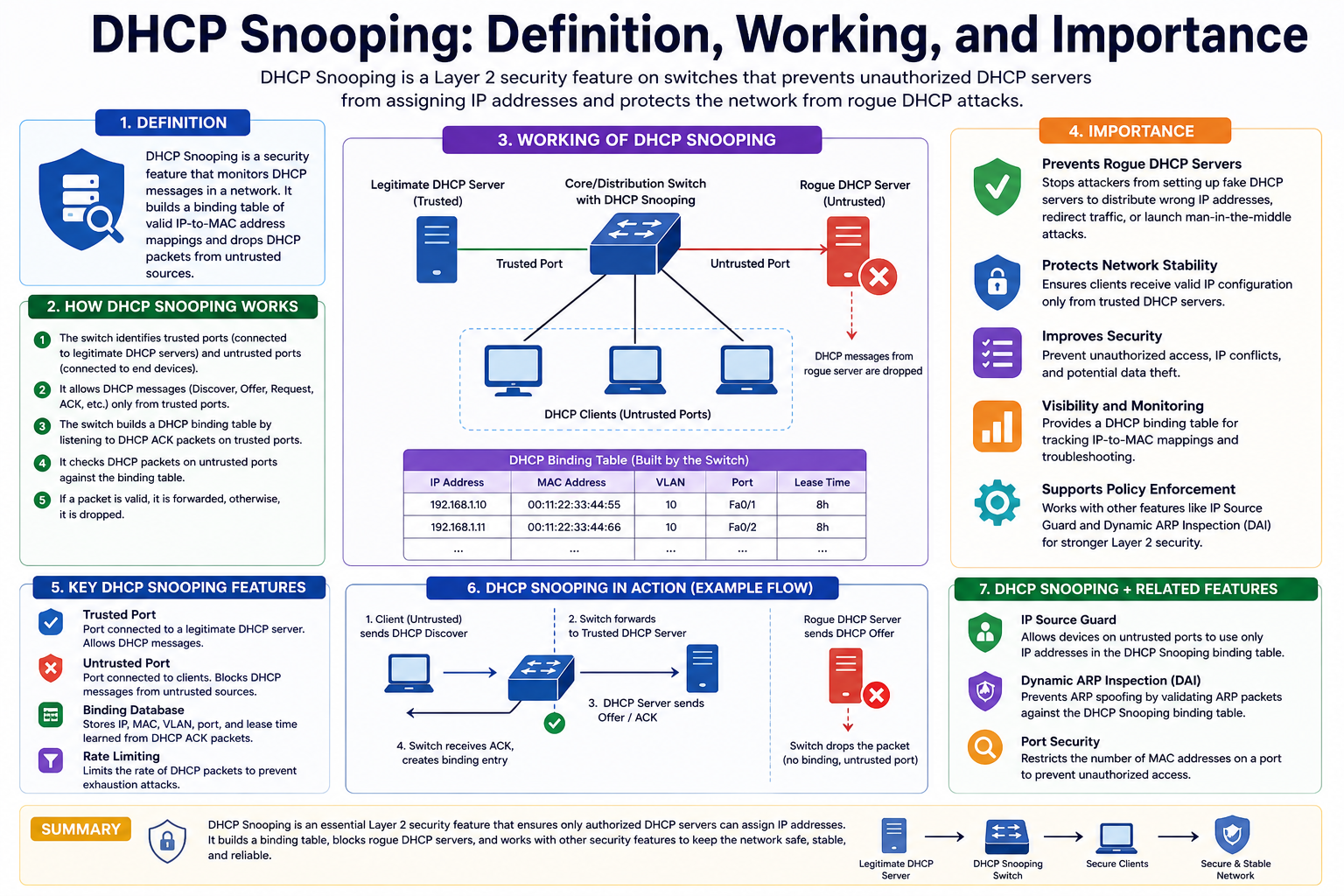
DHCP snooping is a network security control designed to protect devices and users from malicious or unauthorized DHCP activity inside a local network. It works by monitoring DHCP traffic at the switch level and making decisions about which devices are allowed to behave as trusted DHCP sources. In simple terms, it ensures that only legitimate DHCP servers are allowed to assign IP addresses, while blocking any suspicious or rogue devices that try to interfere with the process. This feature is especially important in environments where multiple devices share the same network infrastructure, such as offices, campuses, public WiFi systems, and enterprise networks.
At its core, DHCP snooping acts like a gatekeeper. It sits between devices requesting network configuration and the devices providing that configuration, carefully inspecting messages as they pass through network switches. If a device attempts to send DHCP responses without proper authorization, DHCP snooping identifies it as untrusted and blocks its traffic. This prevents attackers from hijacking the IP assignment process and redirecting users to malicious systems.
The importance of DHCP snooping becomes clearer when considering how essential DHCP is to modern networking. Without DHCP, every device would require manual configuration of IP addresses, subnet masks, gateways, and DNS settings. DHCP automates this process, making it easy for devices to join networks seamlessly. However, this convenience also introduces security risks because DHCP does not include built-in authentication, meaning any device can technically attempt to act as a DHCP server unless additional protections are implemented.
How DHCP Works Before Snooping Comes Into Play
To fully understand DHCP snooping, it is important to understand how DHCP itself operates in a normal network environment. When a device connects to a network for the first time, it does not yet have an IP address. To obtain one, it goes through a structured communication process with a DHCP server. This process involves several messages exchanged between the client device and the server, allowing automatic network configuration.
The first step begins when a device sends a DHCP Discover message. This message is essentially a broadcast across the network announcing that the device is looking for a DHCP server. Since the device does not yet know the network structure, it sends this message to all available nodes. Any DHCP server listening on the network receives this request.
Next, a DHCP server responds with a DHCP Offer message. This message contains an available IP address along with other configuration details such as lease duration, subnet mask, and gateway information. The server also includes the MAC address of the requesting device to ensure the offer reaches the correct recipient.
Once the device receives one or more offers, it selects one and responds with a DHCP Request message. This step is important because it informs all DHCP servers on the network which offer has been accepted. It also acts as a confirmation that the device intends to use the selected IP address.
Finally, the DHCP server sends a DHCPACK message, confirming that the IP address has been officially assigned to the device. At this point, the device is fully configured and can communicate on the network using the assigned IP address. This entire process is fast, automatic, and usually happens within seconds when a device joins a network.
However, the critical issue is that none of these messages are authenticated by default. This means any device connected to the network can potentially send DHCP Offer or DHCPACK messages, which opens the door to exploitation if proper safeguards are not in place.
Security Weaknesses in the DHCP Process
The lack of authentication in DHCP communication is one of its biggest vulnerabilities. Since DHCP was designed for simplicity and ease of use rather than security, it does not verify whether a DHCP server is legitimate or malicious. This creates an opportunity for attackers to introduce rogue DHCP servers into a network.
A rogue DHCP server is a device that falsely claims to provide valid IP configuration information. When such a device is introduced into the network, it can respond to DHCP Discover messages faster than the legitimate server. As a result, client devices may unknowingly accept incorrect network settings provided by the attacker.
Once a device receives malicious configuration, the attacker can redirect traffic through their own system. This allows them to intercept sensitive information such as login credentials, emails, browsing activity, and internal communications. In many cases, users do not even realize that their traffic is being monitored or manipulated.
Another major risk is DHCP starvation. In this type of attack, a malicious user floods the DHCP server with a large number of fake DHCP requests using different MAC addresses. The goal is to exhaust the pool of available IP addresses. Once the server runs out of IPs, legitimate devices cannot join the network. At this point, the attacker may introduce their own DHCP server to take control of the assignment process.
These vulnerabilities highlight why additional security mechanisms are necessary in environments where network integrity is critical. DHCP snooping is specifically designed to address these weaknesses by introducing control and verification at the switch level.
The Role of DHCP Snooping in Blocking Rogue DHCP Activity
DHCP snooping operates by dividing network ports into two categories: trusted and untrusted. Trusted ports are those that are allowed to send DHCP server responses, such as Offer and ACK messages. These typically connect to legitimate DHCP servers or upstream network infrastructure. Untrusted ports, on the other hand, are all other ports where end-user devices are connected.
By default, all ports are considered untrusted. This default state is intentional because it ensures maximum security until an administrator explicitly defines trusted points in the network. When DHCP snooping is enabled, the switch begins inspecting DHCP traffic passing through all ports. If it detects DHCP server responses coming from an untrusted port, it immediately blocks that traffic.
This mechanism effectively prevents any unauthorized device from acting as a DHCP server. Even if a malicious user attempts to inject fake DHCP offers into the network, those messages will not reach client devices because the switch filters them out.
DHCP snooping also maintains a binding table that tracks legitimate IP assignments. This table records information such as MAC addresses, IP addresses, VLAN IDs, and associated ports. This database helps the switch validate future traffic and detect inconsistencies in network behavior.
Through these mechanisms, DHCP snooping ensures that only verified devices can participate in IP allocation, significantly reducing the risk of spoofing attacks and unauthorized network manipulation.
Understanding Trusted and Untrusted Ports in Practice
The concept of trusted and untrusted ports is central to how DHCP snooping functions. Trusted ports are manually configured by network administrators based on network topology. These ports usually connect to DHCP servers, routers, or other infrastructure components that are authorized to distribute IP addresses.
Untrusted ports, in contrast, are typically edge ports where end-user devices connect. These include employee computers, laptops, printers, and other client devices. Since these devices should never act as DHCP servers, their ports remain untrusted by default.
When a DHCP Offer or DHCPACK message is detected on an untrusted port, the switch immediately drops the packet. This ensures that only messages originating from trusted infrastructure are allowed to influence IP assignment decisions.
This separation is crucial because it establishes a clear boundary of trust within the network. Without this distinction, any device could potentially interfere with DHCP operations. With DHCP snooping, the network becomes structured in a way that enforces strict control over where DHCP responses can originate.
This mechanism is particularly effective in large-scale environments where many users share the same network infrastructure. It ensures that even if one device is compromised, it cannot disrupt the entire DHCP system.
Rate Limiting and Protection Against DHCP Exhaustion Attacks
In addition to blocking unauthorized DHCP servers, DHCP snooping also provides protection against DHCP starvation attacks through rate limiting. Rate limiting controls the number of DHCP requests that can be sent through a port within a specific time frame.
Without rate limiting, an attacker could generate thousands of DHCP requests in a short period, overwhelming the DHCP server’s address pool. This would prevent legitimate users from obtaining IP addresses, effectively causing a denial of service condition.
By setting a limit on how many DHCP packets a port can send per second, the switch ensures that no single device can flood the network with excessive requests. If a device exceeds this threshold, the switch automatically blocks or drops additional DHCP traffic from that port.
This mechanism is simple but highly effective. It does not require complex detection algorithms or external systems. Instead, it enforces a basic constraint that prevents abnormal behavior from affecting network stability.
Rate limiting works alongside trusted port configuration to create a layered defense system. While trusted ports ensure only authorized DHCP servers can respond, rate limiting ensures that untrusted devices cannot overwhelm the system with excessive requests.
Together, these protections significantly reduce the attack surface associated with DHCP-based vulnerabilities and strengthen the overall reliability of network operations.
Understanding DHCP Snooping in Enterprise Network Protection
DHCP snooping plays a crucial role in strengthening enterprise network security by acting as a control mechanism at the switch level. It is not just a simple filtering feature but a structured security framework that continuously evaluates DHCP traffic flowing through a network. In large-scale environments, where hundreds or even thousands of devices connect daily, maintaining trust in IP address allocation becomes essential. DHCP snooping ensures that only verified and legitimate DHCP servers can distribute network configuration details, while all other sources are treated with caution and restricted accordingly.
In enterprise networks, DHCP snooping is often deployed alongside other security technologies to create a layered defense strategy. While firewalls protect external traffic and intrusion detection systems monitor suspicious behavior, DHCP snooping focuses specifically on internal network integrity. It ensures that even if an attacker gains access to the internal network, they cannot easily manipulate IP assignment processes or introduce rogue infrastructure.
One of the key strengths of DHCP snooping in enterprise environments is its ability to maintain visibility over DHCP transactions. By tracking every DHCP message, switches can build a clear map of which device received which IP address, from which port, and under what conditions. This level of visibility is essential for troubleshooting, auditing, and forensic analysis in case of a security incident.
How DHCP Snooping Builds a Secure Trust Model
At the heart of DHCP snooping lies a trust-based model that divides the network into controlled zones. This model is built around the idea that not all network devices should have equal authority when it comes to assigning IP addresses. Instead, only specific, pre-approved devices are allowed to send DHCP server responses, while all others are restricted.
This trust model is enforced through switch configuration. Network administrators explicitly define trusted interfaces based on network topology and infrastructure design. These trusted interfaces typically connect to legitimate DHCP servers or core network devices. Once configured, the switch automatically treats all other interfaces as untrusted, applying strict filtering rules to DHCP traffic passing through them.
The trust model is dynamic in the sense that it can adapt to changes in network design. For example, if a new DHCP server is added to the network, its connected switch port must be manually marked as trusted. Without this configuration, the server will be unable to distribute IP addresses, as its responses will be blocked by the DHCP snooping mechanism.
This approach significantly reduces the risk of unauthorized DHCP activity. Even if an attacker connects a rogue device to the network, the switch will not recognize it as trusted and will immediately block any DHCP server responses originating from it.
DHCP Snooping Binding Database and Its Importance
One of the most powerful components of DHCP snooping is the binding database, also known as the DHCP snooping table. This database stores detailed information about DHCP transactions observed by the switch. It includes mappings between MAC addresses, IP addresses, VLAN identifiers, lease times, and the switch ports through which devices are connected.
This binding information serves multiple security and operational purposes. From a security perspective, it helps verify that devices are using legitimate IP addresses assigned through trusted DHCP servers. If a device attempts to use an IP address that does not match the recorded binding information, the switch can detect and block the traffic, preventing spoofing or unauthorized access.
From an operational standpoint, the binding database is extremely useful for troubleshooting network issues. Network administrators can quickly identify which device is connected to which port and what IP address it has been assigned. This reduces the time required to diagnose connectivity problems and improves overall network efficiency.
The binding database is continuously updated as devices join and leave the network. When a DHCP lease expires or a device disconnects, the corresponding entry is removed or updated accordingly. This ensures that the database remains accurate and reflects the current state of the network at all times.
DHCP Snooping and Its Role in Preventing IP Address Manipulation
One of the major security concerns in unmanaged or poorly secured networks is IP address manipulation. Attackers often attempt to assign themselves valid IP addresses by bypassing normal DHCP procedures or by introducing unauthorized DHCP servers. DHCP snooping directly addresses this issue by enforcing strict validation of all DHCP-related activities.
When DHCP snooping is enabled, the switch verifies every DHCP message before allowing it to influence network configuration. If a device attempts to send a DHCP Offer message from an untrusted port, the switch immediately discards it. This prevents attackers from injecting false IP configuration data into the network.
Additionally, DHCP snooping ensures that devices cannot impersonate legitimate DHCP servers. Even if an attacker mimics the behavior of a DHCP server, their messages will be blocked unless they originate from a trusted interface. This prevents a wide range of attacks, including man-in-the-middle attacks that rely on redirecting network traffic through malicious systems.
By controlling IP assignment at the switch level, DHCP snooping ensures that the foundation of network communication remains secure. Since IP addresses are the basis of all network communication, protecting this layer is essential for maintaining overall network integrity.
Interaction Between DHCP Snooping and Network Switches
DHCP snooping operates directly on network switches, making it a layer 2 security feature. This positioning is important because it allows the switch to inspect DHCP traffic before it reaches higher layers of the network stack. By intercepting and analyzing packets at this early stage, DHCP snooping can prevent malicious activity before it affects the broader network.
Switches configured with DHCP snooping inspect all incoming DHCP packets and classify them based on their source port. If a packet originates from a trusted port, it is allowed to pass through without restriction. If it originates from an untrusted port, the switch applies filtering rules to determine whether the packet should be allowed or dropped.
This interaction between DHCP snooping and switching hardware enables high-speed processing of DHCP traffic without introducing significant performance overhead. Since switches are designed to handle large volumes of network traffic efficiently, DHCP snooping can operate at scale without degrading network performance.
In addition to filtering traffic, switches also use DHCP snooping data to enforce other security policies. For example, they can integrate with features like dynamic ARP inspection and IP source guard, which rely on DHCP snooping binding information to validate network behavior.
Integration of DHCP Snooping with Other Security Features
DHCP snooping is rarely used in isolation. In modern network security architectures, it is often integrated with multiple complementary features to provide comprehensive protection. One of the most common integrations is with Dynamic ARP Inspection (DAI). DAI uses DHCP snooping binding tables to verify ARP packets and prevent ARP spoofing attacks.
Another important integration is with IP Source Guard, which restricts IP traffic based on DHCP snooping bindings. This ensures that only devices with valid DHCP-assigned IP addresses can communicate on the network. If a device attempts to use a static or unauthorized IP address, its traffic is blocked.
These integrations create a multi-layered defense system that protects different aspects of network communication. While DHCP snooping focuses on IP assignment, DAI and IP Source Guard extend protection to address resolution and traffic validation. Together, they significantly reduce the risk of internal network attacks.
This layered approach is particularly important in environments where sensitive data is transmitted regularly. By combining multiple security mechanisms, organizations can ensure that even if one layer is bypassed, others will continue to provide protection.
Common Misconfigurations and Their Impact on Network Behavior
Despite its effectiveness, DHCP snooping can cause network issues if not configured correctly. One of the most common misconfigurations occurs when network administrators fail to designate trusted ports properly. Since all ports are untrusted by default, forgetting to mark the DHCP server’s port as trusted can result in complete DHCP failure.
In such cases, devices may connect to the network but fail to obtain IP addresses, leading to connectivity issues across the entire network segment. This highlights the importance of careful planning and documentation when deploying DHCP snooping in production environments.
Another common issue arises from incorrect VLAN configuration. If DHCP snooping is enabled on the wrong VLAN or not enabled on the correct one, DHCP traffic may be blocked unintentionally. This can create confusion and lead to troubleshooting delays.
Rate limiting misconfigurations can also impact network performance. If the rate limit is set too low, legitimate devices may be incorrectly flagged as suspicious, resulting in dropped DHCP requests. On the other hand, if the limit is too high, it may fail to prevent DHCP starvation attacks effectively.
These challenges emphasize the need for careful configuration and ongoing monitoring when implementing DHCP snooping. While the feature is powerful, its effectiveness depends heavily on proper setup and maintenance.
DHCP Snooping in Layered Network Defense Architecture
DHCP snooping is an essential part of layered network defense, where multiple security mechanisms work together to protect different aspects of communication. Instead of relying on a single security control, modern networks use a combination of features that address specific vulnerabilities at different layers of the OSI model. DHCP snooping primarily operates at the data link layer, focusing on controlling and validating DHCP traffic before it influences IP-level communication.
In a layered architecture, DHCP snooping works alongside perimeter security tools, internal access controls, and monitoring systems. While firewalls control traffic entering and leaving the network, DHCP snooping ensures that internal devices cannot manipulate IP assignment processes. This separation of responsibilities improves overall resilience because even if one layer is bypassed, others continue to provide protection.
The importance of DHCP snooping in layered security becomes more evident in environments with high device mobility. In such networks, devices frequently connect and disconnect, making dynamic IP allocation essential. Without DHCP snooping, this dynamic environment becomes vulnerable to internal manipulation, where attackers can exploit the automatic nature of DHCP to introduce malicious configurations.
By enforcing strict rules on DHCP message flow, DHCP snooping ensures that the foundational process of network communication remains trustworthy. Since all higher-level communication depends on correct IP assignment, securing this early stage strengthens the entire network stack.
Advanced Packet Inspection and DHCP Message Filtering
DHCP snooping does more than simply block or allow traffic based on port trust levels. It performs deep inspection of DHCP packets to ensure that they comply with expected behavior patterns. Each DHCP message is analyzed for its type, source, and direction before the switch decides how to handle it.
For example, DHCP Offer and DHCPACK messages are only permitted from trusted interfaces. If these messages are detected on untrusted ports, they are immediately dropped. This prevents unauthorized devices from participating in the DHCP response process. At the same time, DHCP Discover and DHCP Request messages from clients are allowed to pass through, as they are part of normal network behavior.
The switch also checks consistency in DHCP communication. If a device attempts to send conflicting messages or behave in a way that does not match standard DHCP flow, the switch can flag or block the traffic. This level of inspection helps prevent subtle attack techniques that rely on manipulating DHCP state transitions.
This filtering process is lightweight and efficient because it is handled at the switch hardware level. Unlike software-based security systems that may introduce latency, DHCP snooping operates in real time, allowing networks to maintain high performance while still enforcing security policies.
Role of DHCP Snooping in Preventing Internal Network Threats
Internal network threats are often more dangerous than external attacks because they originate from devices that already have physical or logical access to the network. DHCP snooping is specifically designed to address these internal risks by controlling how devices interact with DHCP infrastructure.
One of the most common internal threats is the introduction of unauthorized DHCP servers. A compromised or malicious device connected to the network can attempt to distribute fake IP configurations to other devices. Without DHCP snooping, these fake configurations may be accepted, allowing attackers to redirect traffic or intercept sensitive information.
DHCP snooping prevents this by ensuring that only trusted ports can send DHCP server responses. Even if an attacker has physical access to a network port, their device will not be able to act as a DHCP server unless that port has been explicitly configured as trusted.
Another internal threat is ARP-based spoofing that builds on DHCP manipulation. Attackers may first use rogue DHCP services to assign themselves network positions that allow them to intercept traffic. By blocking unauthorized DHCP activity, snooping reduces the effectiveness of these combined attack strategies.
This internal protection is particularly important in environments such as corporate offices, universities, and data centers, where many users share the same physical network infrastructure.
DHCP Snooping and Network Visibility Enhancement
Beyond security enforcement, DHCP snooping significantly improves network visibility. By tracking DHCP transactions, it creates a detailed record of device activity across the network. This visibility is crucial for both operational management and security monitoring.
Every time a device requests an IP address, the switch records relevant information such as the device’s MAC address, assigned IP, VLAN membership, and connection port. This information is stored in the DHCP snooping binding table, which acts as a real-time map of network device distribution.
This visibility allows administrators to quickly identify which device is connected to which part of the network. In large environments where hundreds of devices may be active simultaneously, this mapping becomes extremely valuable for troubleshooting and auditing purposes.
It also supports forensic investigations. If suspicious activity is detected on the network, administrators can refer to DHCP snooping logs to trace the origin of the activity. This helps in identifying compromised devices and understanding the scope of an attack.
In addition, this visibility improves compliance with security policies. Organizations often need to demonstrate control over network access, and DHCP snooping provides a verifiable record of IP assignment activity that supports these requirements.
Behavior of DHCP Snooping in High Traffic Environments
In high traffic environments, DHCP snooping must process a large volume of DHCP messages without introducing delays or bottlenecks. Network switches are designed to handle this efficiently by integrating DHCP snooping directly into hardware-based forwarding logic.
When traffic volume increases, the switch continues to apply the same inspection rules but does so at line speed. This ensures that DHCP operations remain unaffected even during peak usage periods. Devices can still obtain IP addresses quickly, and network performance remains stable.
However, high traffic environments also increase the importance of rate limiting. Without proper limits, a large number of devices attempting to join the network simultaneously could overwhelm DHCP servers or create congestion. DHCP snooping helps mitigate this by controlling how many DHCP requests each port can generate within a given time period.
This balance between performance and security is critical in environments such as large campuses, public WiFi networks, and enterprise data centers. In these settings, both scalability and protection must be maintained simultaneously.
DHCP Snooping in Wireless and Hybrid Networks
Modern networks often combine wired and wireless infrastructure, creating hybrid environments where devices move freely between different connection types. DHCP snooping is equally important in both scenarios, although its implementation is primarily focused on switch-based wired networks.
In wireless networks, access points connect back to wired switches where DHCP snooping is enforced. This means that even though users connect wirelessly, their DHCP traffic is still controlled at the switch level. Any attempt to introduce rogue DHCP behavior through wireless devices is still subject to filtering once it reaches the wired infrastructure.
In hybrid environments, DHCP snooping ensures consistency across different network segments. Whether a device connects through Ethernet or WiFi, its DHCP interactions are still validated through the same trust model. This uniformity simplifies network security design and reduces the likelihood of configuration inconsistencies.
It also helps prevent attacks that attempt to exploit differences between wired and wireless security policies. Since DHCP snooping is applied at a central switching layer, it provides a consistent enforcement point across the entire network infrastructure.
Impact of DHCP Snooping on Network Reliability and Stability
In addition to improving security, DHCP snooping contributes to overall network stability. By ensuring that only valid DHCP responses are accepted, it reduces the chances of misconfiguration and IP conflicts. This leads to more predictable network behavior and fewer connectivity issues.
IP conflicts often occur when multiple devices attempt to use the same address or when incorrect DHCP responses are received. DHCP snooping minimizes this risk by strictly controlling which devices can assign IP addresses and by maintaining accurate binding records.
This stability is particularly important in environments where uptime is critical. For example, in business networks, even short periods of connectivity issues can disrupt operations. DHCP snooping helps prevent these disruptions by ensuring that IP assignment remains consistent and reliable.
It also reduces troubleshooting complexity. When DHCP-related issues occur, administrators can refer to snooping logs to quickly identify whether the problem is caused by misconfiguration, unauthorized activity, or network congestion.
By improving both security and operational stability, DHCP snooping becomes a foundational component of modern network design, supporting both day-to-day functionality and long-term reliability.
DHCP Snooping in Large Scale Network Environments
In large scale network environments, DHCP snooping becomes even more critical because of the sheer number of devices and the complexity of traffic flow. Enterprise networks, service providers, universities, and data centers often manage thousands of connected devices simultaneously, all relying on automatic IP assignment. Without a control mechanism like DHCP snooping, maintaining trust in such an environment would be extremely difficult.
One of the main challenges in large networks is maintaining consistent security policies across multiple switches and segments. DHCP snooping helps solve this by enforcing a standardized rule set at every switch where it is enabled. Regardless of where a device connects, its DHCP activity is checked against the same trust model. This ensures uniform security enforcement across the entire infrastructure.
Scalability is another important factor. As networks grow, administrators may add new switches, VLANs, or DHCP servers. DHCP snooping can scale with these changes as long as proper configuration is maintained. Each new segment can be integrated into the existing trust framework by defining trusted interfaces and enabling snooping on relevant VLANs.
Large environments also benefit from the centralized visibility provided by DHCP snooping. With thousands of devices generating DHCP traffic, tracking IP assignments manually would be impractical. The binding database automatically maintains this information, allowing administrators to quickly locate devices, identify usage patterns, and detect anomalies across the entire network.
DHCP Snooping in Multi VLAN and Segmented Networks
Modern networks are rarely flat. Instead, they are divided into multiple VLANs to improve performance, security, and management. DHCP snooping works effectively in these segmented environments by applying policies on a per VLAN basis.
Each VLAN can have DHCP snooping enabled independently, allowing administrators to control how DHCP traffic is handled within specific network segments. This is important because different VLANs may serve different purposes, such as user access, guest access, or server communication. Each of these environments may require different levels of DHCP control.
In a multi VLAN setup, DHCP snooping ensures that DHCP traffic does not leak between segments in unintended ways. For example, a rogue device in a guest VLAN cannot interfere with DHCP operations in a secure internal VLAN. This isolation helps maintain security boundaries within the network.
Additionally, VLAN based DHCP snooping helps reduce broadcast noise. Since DHCP requests are limited to their respective VLANs, unnecessary traffic does not propagate across the entire network. This improves efficiency and reduces load on network devices.
Proper VLAN configuration is essential for DHCP snooping to function correctly. If VLAN mappings are incorrect or inconsistent, DHCP traffic may be blocked unintentionally, leading to connectivity issues. Therefore, careful planning is required when deploying DHCP snooping in segmented networks.
Monitoring and Logging Behavior in DHCP Snooping Systems
Monitoring and logging are essential components of DHCP snooping, providing administrators with insight into network behavior and security events. Every time DHCP traffic is processed, relevant events can be logged for analysis and review.
These logs typically include information about blocked DHCP messages, untrusted port activity, and binding table updates. When a device attempts to send unauthorized DHCP responses, the switch records the event and marks it as a violation. This allows administrators to identify potential security threats and investigate further if needed.
In addition to security monitoring, logs also help with operational troubleshooting. If a device fails to obtain an IP address, administrators can check DHCP snooping logs to determine whether the request was blocked due to misconfiguration or rate limiting.
In more advanced environments, DHCP snooping logs are integrated into centralized monitoring systems. These systems collect data from multiple switches and provide real time alerts when suspicious activity is detected. This enables faster response times and improves overall network security posture.
The combination of logging and monitoring also supports compliance requirements. Many organizations must maintain records of network activity for auditing purposes. DHCP snooping provides a reliable source of structured data that can be used to demonstrate network control and security enforcement.
Common Deployment Challenges and Configuration Issues
Although DHCP snooping is highly effective, deploying it in real world environments can present several challenges. One of the most common issues is misconfiguration of trusted ports. Since all ports are untrusted by default, failing to properly identify DHCP server connections can result in widespread connectivity problems.
Another frequent challenge is incomplete VLAN coverage. If DHCP snooping is enabled on some VLANs but not others, inconsistencies can occur in IP assignment behavior. Devices in non configured VLANs may fail to receive IP addresses or may bypass intended security controls.
Rate limiting can also introduce challenges if not properly tuned. Setting limits too low may prevent legitimate devices from obtaining IP addresses, especially in environments where many devices connect simultaneously. On the other hand, setting limits too high may reduce the effectiveness of protection against DHCP starvation attacks.
Another issue involves legacy devices or unusual network configurations. Some older devices may not fully comply with modern DHCP behavior, leading to unexpected interactions with DHCP snooping rules. In such cases, administrators may need to adjust configurations carefully to maintain compatibility while preserving security.
These challenges highlight the importance of thorough planning, testing, and documentation before deploying DHCP snooping in production environments. A well designed configuration reduces the risk of disruptions and ensures smooth operation.
Interaction Between DHCP Snooping and Network Performance
DHCP snooping is designed to operate with minimal impact on network performance. Since it is implemented at the switch level, it processes DHCP traffic efficiently without introducing significant latency. This allows networks to maintain high throughput while still enforcing security policies.
However, in very large networks with high DHCP traffic volumes, careful resource management is required. Switches must maintain binding tables and process continuous DHCP updates, which can consume memory and processing resources. Modern enterprise switches are optimized to handle this load, but capacity planning is still important.
Performance considerations also include the frequency of DHCP lease renewals. In environments where leases are short, DHCP traffic increases, which may result in more frequent updates to the snooping database. While this is manageable, it should be considered when designing network policies.
Despite these considerations, DHCP snooping is generally lightweight compared to other security mechanisms. Its integration into hardware forwarding paths ensures that it does not become a bottleneck, even in high traffic environments.
Security Strength of DHCP Snooping in Real World Scenarios
In real world scenarios, DHCP snooping significantly reduces the risk of several common network attacks. Rogue DHCP server attacks are effectively neutralized because only trusted ports can send DHCP responses. This prevents attackers from redirecting traffic or altering network configurations.
DHCP starvation attacks are also mitigated through rate limiting and binding validation. Even if an attacker floods the network with DHCP requests, the switch can detect abnormal behavior and restrict traffic accordingly.
In combination with other security features, DHCP snooping forms a strong defense against internal threats. When paired with ARP inspection and IP validation mechanisms, it creates a multi layer protection system that is difficult to bypass.
Organizations that deploy DHCP snooping as part of their security architecture benefit from improved network integrity, reduced attack surface, and better visibility into device behavior. This makes it a foundational technology in modern enterprise networking environments.
Conclusion
DHCP snooping is a critical network security feature that strengthens the integrity of IP address allocation by controlling how DHCP messages are handled within a switched network. By separating trusted and untrusted ports, it ensures that only legitimate DHCP servers can assign IP addresses while blocking unauthorized or malicious devices from interfering with the process. This simple but powerful trust model directly protects against threats such as rogue DHCP servers, DHCP spoofing, and DHCP starvation attacks.
Its ability to maintain a binding database adds another layer of control by tracking which device has been assigned which IP address and through which port. This not only improves security but also enhances network visibility, making troubleshooting and auditing far more efficient. Combined with features like rate limiting, DHCP snooping also helps maintain network stability even under high traffic conditions or attack attempts.
In modern enterprise and large-scale networks, DHCP snooping plays an important role in layered defense strategies. It works alongside other security technologies to protect internal traffic, enforce policy consistency, and reduce vulnerabilities at the data link layer. While it requires careful configuration—especially in defining trusted ports and VLAN coverage—its benefits far outweigh its complexity.
Overall, DHCP snooping is an essential safeguard for any network that relies on dynamic IP addressing, ensuring that the foundation of communication remains secure, stable, and trustworthy.