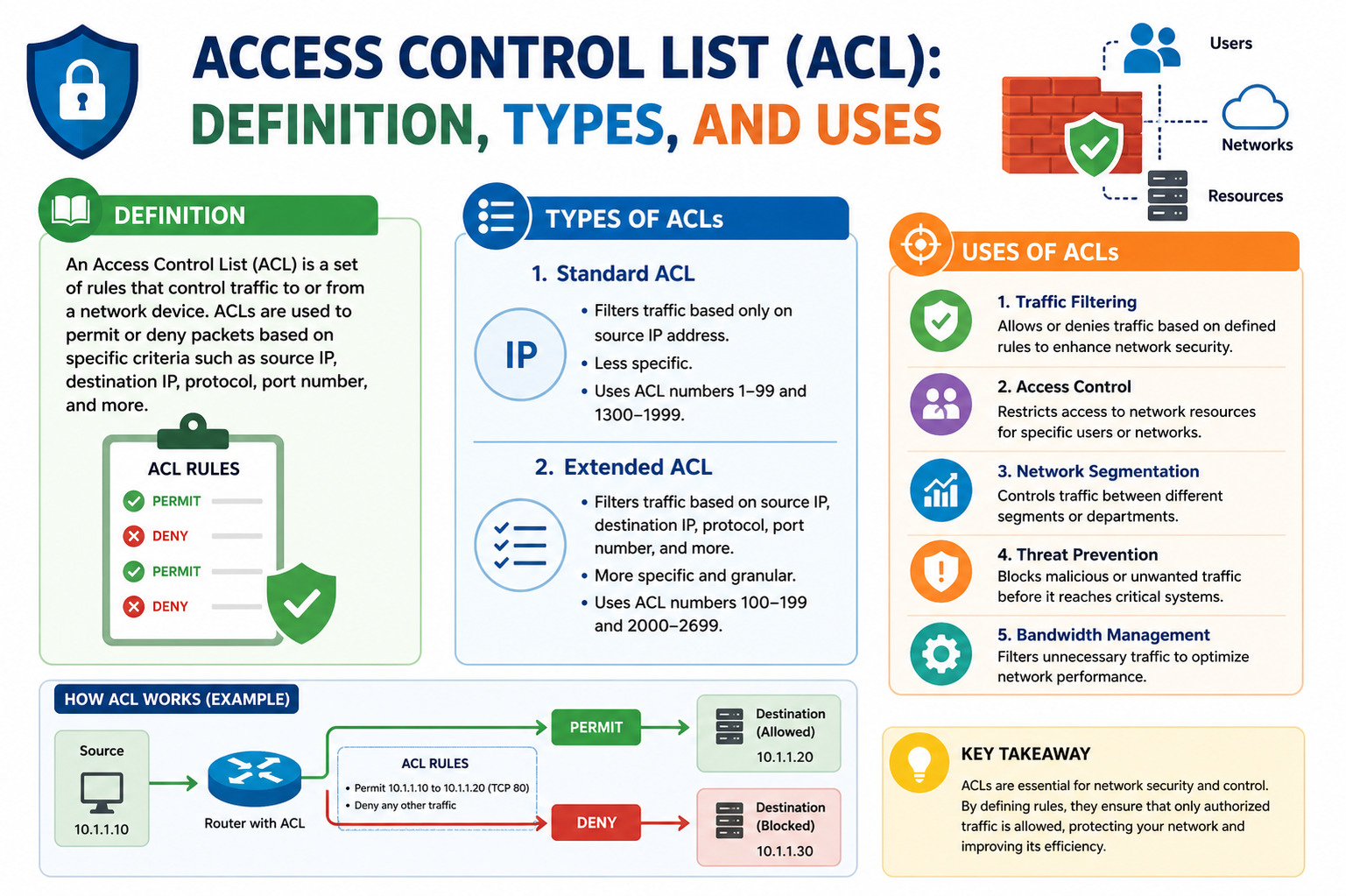
An Access Control List (ACL) is a structured set of rules used in networking environments to control how data packets are handled as they move through devices such as routers, switches, and firewalls. These rules determine whether specific network traffic is permitted or blocked based on defined conditions like source IP address, destination IP address, protocol type, and port number. In simple terms, an ACL acts like a security filter that evaluates every incoming and outgoing data packet and decides whether it should be allowed to pass through the network or be stopped.
At its core, an ACL is a foundational mechanism used to enforce network security policies. It allows network administrators to regulate communication between devices, users, and external networks in a controlled and predictable way. Without ACLs, network traffic would flow freely without restrictions, increasing the risk of unauthorized access, data breaches, and malicious activity. By implementing ACL rules, organizations gain precise control over who can access their systems and how that access is granted.
ACLs are widely used in both small and large-scale networks, including enterprise systems, data centers, and cloud-based infrastructures. They play a vital role in maintaining confidentiality, integrity, and availability of network resources. Whether it is preventing external threats from entering a private network or restricting internal users from accessing sensitive services, ACLs provide an essential layer of security enforcement.
Importance of Access Control Lists in Network Security
Access Control Lists are essential because they serve as a primary defense mechanism in network security architecture. Every organization that relies on digital communication must ensure that only legitimate traffic is allowed into its network. ACLs help achieve this by defining clear boundaries for traffic flow. They reduce the attack surface by blocking unwanted or suspicious connections before they can reach critical systems.
One of the most important roles of ACLs is preventing unauthorized access. Cyber threats such as malware, ransomware, and intrusion attempts often rely on open or poorly secured network paths. ACLs help minimize these risks by filtering traffic at the entry point of a network device. This proactive filtering ensures that harmful traffic is stopped early, rather than being allowed deeper into the system where it could cause significant damage.
Another key benefit of ACLs is traffic management. Networks often carry a wide variety of data, including web traffic, file transfers, voice communication, and application requests. ACLs help prioritize or restrict certain types of traffic to maintain performance and efficiency. For example, essential business applications can be prioritized over less critical traffic to ensure smooth operation even during peak usage times.
ACLs also support compliance and policy enforcement. Many organizations are required to follow strict security standards and regulations. ACLs help enforce these rules by ensuring that only approved communication paths are allowed. This makes it easier for administrators to align network behavior with organizational security policies.
Core Concept of How ACL Filtering Works
The fundamental idea behind an Access Control List is packet filtering. Every piece of data that travels across a network is broken into small units called packets. Each packet contains information such as its origin, destination, and type of service. ACLs inspect these details to determine whether the packet matches any predefined rule.
When a packet arrives at a network device where an ACL is configured, it is immediately compared against the list of rules. These rules are written in a specific order and evaluated sequentially. The device checks each rule one by one until it finds a match. Once a matching rule is found, the action specified by that rule is applied. This action is typically either to permit the packet or deny it.
This process happens extremely quickly, often in milliseconds, allowing networks to maintain high performance while still enforcing strict security controls. The efficiency of ACLs makes them suitable for environments where large volumes of traffic must be processed without delays.
ACLs can be applied in two main directions: inbound and outbound. Inbound ACLs filter traffic entering a network interface, while outbound ACLs filter traffic leaving it. This flexibility allows administrators to control traffic flow at multiple points within the network infrastructure.
Rule Creation and Logical Ordering in ACLs
The effectiveness of an ACL depends heavily on how its rules are created and organized. Each rule within an ACL is defined using specific criteria such as IP addresses, protocols, or port numbers. These criteria determine what type of traffic the rule applies to.
For example, a rule may specify that traffic coming from a particular IP address should be blocked, or that traffic using a specific protocol should be allowed. Each rule is written in a structured format so that network devices can interpret and apply it consistently.
One of the most critical aspects of ACL design is rule ordering. ACLs are processed from top to bottom, meaning the first matching rule is the one that gets applied. This makes order extremely important because a poorly placed rule can unintentionally override more specific rules below it.
To ensure proper functioning, more specific rules are typically placed at the top of the ACL, while broader or general rules are placed lower down. This approach ensures that detailed conditions are evaluated first before applying general policies. If this order is not followed correctly, it can lead to unexpected network behavior, such as legitimate traffic being blocked or unauthorized traffic being allowed.
ACL rule creation requires careful planning and a clear understanding of network requirements. Administrators must consider which services need access, which users should be restricted, and how different types of traffic interact within the system.
Packet Evaluation Process in Access Control Lists
When a data packet enters a network device configured with an ACL, it undergoes a structured evaluation process. This process ensures that every packet is checked against security rules before being allowed to proceed further into the network.
The evaluation begins with the inspection of the packet’s header information. This includes details such as the source address, destination address, protocol type, and port numbers. The ACL compares this information against its list of rules in sequential order.
As the packet moves through the ACL, each rule is checked to see if it matches the packet’s characteristics. If a match is found, the corresponding action is immediately applied. This means the packet will either be permitted to continue its journey or denied and dropped from the network flow.
If the packet does not match any explicit rule in the ACL, it does not automatically get approved. Instead, it is handled according to a predefined default behavior. This ensures that no packet bypasses security controls unintentionally.
This evaluation process is similar to a checkpoint system where every packet must be verified before being allowed entry. It ensures that network traffic remains controlled, predictable, and secure at all times.
Default Behavior and Implicit Deny Principle
A critical concept in Access Control Lists is the idea of default behavior, often referred to as the implicit deny principle. This means that if a packet does not match any rule in the ACL, it is automatically denied by default.
This default deny behavior is a key security feature because it ensures that only explicitly allowed traffic is permitted. Instead of relying on the absence of rules, ACLs operate on a positive permission model where access must be clearly granted.
In some configurations, administrators may explicitly define a final rule to deny all remaining traffic. However, even if this rule is not manually added, the system still applies an implicit deny at the end of the ACL.
This approach strengthens network security by minimizing the risk of unintended access. It ensures that unknown or unexpected traffic does not pass through the network unchecked. It also encourages administrators to carefully define every allowed communication path rather than relying on broad permissions.
The implicit deny principle plays a major role in enforcing strict access control policies, especially in environments where security is a top priority. It acts as a safety net that catches any traffic that does not meet defined conditions.
Early Understanding of ACL Structure and Types Overview
Access Control Lists can vary in complexity depending on how they are configured. At a basic level, they are designed to filter traffic based on simple criteria, but they can also support more advanced filtering based on multiple parameters.
Some ACLs are designed for broad filtering decisions, while others allow highly detailed control over network traffic. This flexibility makes ACLs suitable for a wide range of use cases, from simple network segmentation to complex enterprise-level security enforcement.
The structure of an ACL is typically linear, meaning rules are processed in sequence. Each rule adds a layer of decision-making that contributes to the overall behavior of the network device. Understanding this structure is essential for designing effective access control strategies.
As networks grow in complexity, ACLs become even more important for maintaining order and security. They provide a structured way to manage communication between different parts of a network while ensuring that only authorized traffic is allowed to pass through controlled points.
This foundational understanding of ACL behavior sets the stage for deeper exploration of how different types of ACLs function and how they can be applied in various networking scenarios.
Standard Access Control Lists (ACLs) Explained in Depth
Standard Access Control Lists are the simplest form of ACLs used in networking environments. These ACLs focus primarily on filtering traffic based only on the source IP address. They do not inspect destination addresses, ports, or protocols in detail, which makes them lightweight and fast in processing. Because of this simplicity, standard ACLs are often used in scenarios where broad-level traffic control is sufficient without requiring deep inspection of packet contents.
Standard ACLs are typically used to permit or deny traffic from entire networks or individual hosts. For example, a network administrator might configure a standard ACL to block all traffic originating from a specific IP range that is known to be untrusted. This type of filtering is effective when the goal is to restrict access based on origin rather than application type or service.
Due to their limited scope, standard ACLs are generally placed closer to the destination network in a routing path. This placement ensures that only the final traffic reaching a destination is filtered, preventing unnecessary restrictions on intermediate routing paths. Since they lack detailed filtering capabilities, improper placement can lead to overblocking or unintended access restrictions.
Standard ACLs are often preferred in smaller networks or in situations where performance is a priority over granular control. They consume fewer processing resources compared to more advanced ACL types, making them suitable for devices with limited computational capacity. However, this simplicity also means they cannot distinguish between different types of traffic originating from the same source.
Extended Access Control Lists and Their Advanced Capabilities
Extended Access Control Lists provide a much more detailed level of control compared to standard ACLs. These ACLs can filter traffic based on multiple parameters, including source IP address, destination IP address, protocol type, and port numbers. This makes them highly flexible and suitable for complex networking environments where precise traffic control is required.
With extended ACLs, administrators can define rules that target specific applications or services. For example, they can allow web traffic on HTTP or HTTPS ports while blocking file-sharing protocols or other unwanted services. This level of granularity allows organizations to enforce strict security policies while still maintaining necessary business communication.
Extended ACLs are typically placed closer to the source of the traffic. This placement allows unwanted traffic to be filtered early in the network path, reducing unnecessary load on downstream devices. By stopping unwanted packets at the entry point, extended ACLs help improve overall network efficiency and security.
These ACLs are particularly useful in enterprise environments where different departments or user groups require different levels of access. For example, a finance department may be granted access to specific internal servers, while other departments are restricted from accessing those resources. Extended ACLs make it possible to enforce such policies with precision.
Despite their flexibility, extended ACLs require careful planning and configuration. Because they include multiple criteria in each rule, they are more complex to design and maintain. Incorrect configuration can lead to unintended access issues or service disruptions, making proper understanding essential for network administrators.
Importance of Rule Ordering in ACL Configuration
Rule ordering is one of the most critical aspects of Access Control List configuration. Since ACLs are processed sequentially from top to bottom, the position of each rule directly affects how traffic is handled. The first rule that matches a packet determines its fate, whether it is allowed or denied.
This sequential evaluation means that more specific rules should always be placed before general rules. If a general rule is placed at the top, it may override more specific rules placed below it, leading to incorrect filtering behavior. For example, a rule that denies all traffic from a network should not be placed above a rule that allows specific trusted communication from that same network.
Proper rule ordering ensures that exceptions are handled correctly before broader policies are applied. This structure allows administrators to build layered security policies where specific permissions are granted first, followed by general restrictions. Without correct ordering, ACLs can become ineffective or even harmful to network operations.
In large networks, ACLs can grow to include many rules, making ordering even more important. Administrators must regularly review and optimize rule placement to ensure efficiency and accuracy. Poorly organized ACLs can lead to increased processing time and difficulty in troubleshooting network issues.
Understanding rule precedence is essential for maintaining predictable network behavior. Each rule should be carefully evaluated not only for its function but also for its position within the overall ACL structure.
Inbound and Outbound ACL Placement Strategies
Access Control Lists can be applied in two primary directions: inbound and outbound. Inbound ACLs filter traffic as it enters a network interface, while outbound ACLs filter traffic as it exits an interface. The choice between inbound and outbound placement depends on the specific security requirements and network design.
Inbound ACLs are often used to prevent unwanted traffic from entering a network. By filtering packets at the entry point, they help reduce the processing load on internal devices and improve overall security. This approach is commonly used to block malicious traffic before it reaches critical systems.
Outbound ACLs, on the other hand, control traffic leaving a network. These ACLs are useful for enforcing policies on data transmission, such as restricting access to external websites or preventing sensitive data from being sent outside the organization. Outbound filtering is also used to ensure compliance with organizational policies.
Choosing the correct direction for ACL placement is important for achieving optimal performance and security. In many cases, extended ACLs are placed inbound to stop unwanted traffic early, while standard ACLs may be placed outbound near the destination.
Both inbound and outbound ACLs can work together to create a layered security model. This dual approach ensures that traffic is filtered both when entering and leaving the network, reducing the risk of unauthorized communication.
Traffic Filtering Criteria Used in ACL Rules
ACL rules are built using specific filtering criteria that determine how packets are evaluated. These criteria include source IP address, destination IP address, protocol type, and port numbers. Each criterion plays a role in identifying whether a packet should be allowed or denied.
Source IP address filtering allows administrators to control which devices or networks are permitted to initiate communication. Destination IP filtering controls where traffic is allowed to go. Protocol-based filtering enables control over different types of network communication such as TCP, UDP, or ICMP.
Port-based filtering is especially important for controlling application-level traffic. Different services use specific port numbers, and ACLs can be configured to allow or block traffic based on these ports. This enables administrators to control access to web services, email servers, file transfer systems, and other applications.
By combining multiple criteria, extended ACLs can create highly specific rules that target exact types of traffic. This level of control is essential for maintaining secure and efficient network operations in complex environments.
Each rule must be carefully designed to avoid conflicts with other rules. Overlapping conditions can lead to unpredictable behavior if not properly structured.
Wildcard Masks and Their Role in ACL Matching
Wildcard masks are used in some ACL implementations to define ranges of IP addresses. They function as inverse subnet masks, allowing administrators to specify which bits in an IP address should be matched and which should be ignored.
This mechanism provides flexibility in defining groups of IP addresses without having to list each one individually. For example, a wildcard mask can be used to represent an entire subnet or a specific range of addresses.
Wildcard masks are particularly useful in large networks where managing individual IP addresses would be inefficient. They simplify ACL configuration while still allowing precise control over traffic filtering.
When a packet is evaluated against an ACL rule using a wildcard mask, the network device compares the relevant bits of the IP address to determine whether it matches the rule criteria. This process enables efficient grouping and filtering of network traffic.
Understanding wildcard masks is essential for configuring ACLs accurately, especially in environments that require scalable and flexible access control policies.
Scenario-Based Use of Standard and Extended ACLs
Different networking scenarios require different types of ACLs depending on the level of control needed. Standard ACLs are often used in situations where basic filtering is sufficient, such as blocking traffic from a specific network or allowing access from trusted sources.
Extended ACLs are used in more complex scenarios where detailed filtering is necessary. For example, organizations may use extended ACLs to allow web browsing while blocking file-sharing applications or restricting access to sensitive internal systems.
In enterprise networks, both types of ACLs are often used together. Standard ACLs may handle broad-level restrictions, while extended ACLs manage detailed application-level controls. This combination provides a balanced approach to security and performance.
The choice of ACL type depends on factors such as network size, security requirements, and performance considerations. Larger and more complex networks typically rely more heavily on extended ACLs due to their flexibility and precision.
By understanding different use cases, administrators can design ACL strategies that align with organizational needs while maintaining efficient network operation.
Practical Role of ACLs in Real Network Environments
Access Control Lists are not only theoretical constructs used in textbooks or certifications; they are actively deployed in real-world networks to enforce security boundaries and control traffic behavior. In enterprise environments, ACLs serve as an essential control mechanism between internal systems, external networks, and segmented departments. They ensure that communication flows only in ways that align with organizational policies and security requirements.
In modern infrastructures, ACLs are commonly implemented in routers, switches, and firewalls to regulate traffic between different network zones. For example, an internal corporate network may be divided into multiple segments such as finance, human resources, and IT operations. Each segment may require different access levels, and ACLs are used to enforce these restrictions without requiring physical separation of networks.
Cloud-based systems also rely heavily on ACL concepts, even if they are implemented under different naming conventions. Virtual networks in cloud environments use similar rule-based filtering systems to control access between virtual machines, subnets, and external services. This demonstrates that ACL principles remain relevant across traditional and modern networking models.
Step-by-Step Logic Behind ACL Configuration Planning
Before configuring an Access Control List, network administrators must carefully plan the logic behind the rules. This planning stage is critical because ACLs operate in a strict sequential order, and even a small mistake in rule design can disrupt network communication. The first step involves identifying the purpose of the ACL, whether it is meant to block malicious traffic, restrict internal access, or prioritize specific services.
After defining the purpose, administrators analyze the network structure to understand how data flows between devices and services. This includes identifying key IP ranges, critical servers, and frequently used protocols. Without this understanding, ACL rules may be incomplete or overly restrictive, leading to performance issues or service outages.
Once the traffic flow is understood, rules are designed based on specific requirements. These rules must be written in a logical order, starting with the most specific conditions and gradually moving toward more general conditions. This ensures that exceptions are handled properly before broader policies take effect.
Proper planning also involves anticipating future changes in the network. Since ACLs can become complex over time, administrators must design them in a way that allows easy modification without breaking existing rules. This foresight helps maintain long-term stability and reduces maintenance overhead.
Cisco-Based ACL Configuration Process in Detail
In many networking environments, Cisco devices are widely used for implementing Access Control Lists. The configuration process begins by entering privileged execution mode, which allows administrative control over the device. From there, global configuration mode is accessed to begin defining ACL rules.
Standard ACLs are typically created by specifying a numeric identifier followed by permit or deny statements. These statements define which source IP addresses are allowed or blocked. The simplicity of standard ACL configuration makes them easy to deploy but limited in functionality.
Extended ACLs require more detailed configuration because they include multiple parameters. Each rule must specify the protocol type, source address, destination address, and optionally port numbers. This allows for highly specific filtering, such as permitting web traffic while blocking other services between the same endpoints.
After defining ACL rules, they must be applied to specific interfaces on the device. This step determines whether the ACL will filter incoming or outgoing traffic. The direction of application plays a critical role in how traffic is processed and must align with the intended security policy.
Once applied, the configuration is saved to ensure persistence across device reboots. Administrators must also verify the configuration using built-in diagnostic commands that display active ACL rules and their order of execution.
Understanding ACL Traffic Flow Evaluation Process
When a packet enters a network interface where an ACL is active, it undergoes a structured evaluation process. This process begins with reading the packet header information, which contains essential details such as source IP address, destination IP address, and protocol type.
The ACL compares this information against its list of rules in sequential order. Each rule is evaluated one by one until a match is found. If a match occurs, the defined action is executed immediately, and no further rules are checked for that packet.
This sequential evaluation ensures efficiency but also highlights the importance of rule placement. A misconfigured rule placed too early in the list can unintentionally block legitimate traffic before it reaches more specific permitting rules.
If no rules match the packet, the implicit deny rule automatically applies. This means the packet is dropped without needing an explicit deny statement. This behavior reinforces the security-first design of ACL systems.
The entire evaluation process happens at high speed, allowing networks to handle large volumes of traffic without noticeable delays. This efficiency is one of the reasons ACLs are widely used in high-performance environments.
Common Misconfigurations and Their Impact on Networks
One of the most frequent issues in ACL deployment is misconfiguration. Since ACLs rely heavily on rule order and accuracy, even small mistakes can lead to significant network disruptions. A common error is placing a broad deny rule above a specific permit rule, which results in legitimate traffic being blocked unintentionally.
Another common issue involves incorrect IP addressing or subnet definitions. If the wrong range is specified in a rule, the ACL may either allow unwanted traffic or block valid communication. These errors can be difficult to diagnose without proper logging and monitoring tools.
Port misconfiguration is another frequent problem in extended ACLs. Since many applications rely on specific port numbers, incorrectly defining these ports can prevent applications from functioning properly. This often leads to service outages that are difficult to trace back to ACL rules.
Overly complex ACLs can also create maintenance challenges. As the number of rules increases, it becomes harder to track dependencies and interactions between them. This can lead to accidental rule conflicts and degraded network performance.
Proper documentation and regular review are essential to avoid these issues. Without structured management, ACLs can become outdated and ineffective over time.
Testing ACL Behavior in Controlled Environments
Before deploying ACLs in live production networks, it is essential to test them in controlled environments. This helps ensure that the rules behave as expected and do not interfere with critical services. Testing environments replicate real network conditions without risking actual business operations.
During testing, simulated traffic is generated to represent different types of network activity. This includes both permitted and denied traffic scenarios to verify that ACL rules are functioning correctly. Observing how packets are handled in these tests provides valuable insight into rule accuracy.
Packet analysis tools are often used during testing to inspect how traffic flows through the network. These tools allow administrators to see whether packets are being dropped or forwarded based on ACL rules. This level of visibility is crucial for identifying misconfigurations.
Testing also helps validate rule order and priority. Since ACLs operate sequentially, testing ensures that rules are evaluated in the correct sequence and produce the expected outcomes. Any inconsistencies can be corrected before deployment.
By thoroughly testing ACLs before implementation, organizations reduce the risk of downtime and improve overall network reliability.
Troubleshooting ACL-Related Network Issues
When network problems occur, ACLs are often one of the first areas to investigate. Troubleshooting begins by reviewing the ACL configuration to identify any incorrect or missing rules. Administrators check whether the expected traffic is being permitted or denied correctly.
One common troubleshooting step involves reviewing logs generated by ACLs. These logs provide information about which packets were blocked or allowed, helping identify patterns of unexpected behavior. Logging is particularly useful for detecting unauthorized access attempts or misconfigured rules.
Another important step is verifying rule order. Since ACLs are processed sequentially, a misplaced rule can significantly alter traffic behavior. Adjusting rule placement often resolves issues related to blocked or misrouted traffic.
Testing connectivity between devices is also a key part of troubleshooting. If communication fails, administrators determine whether ACLs are responsible by temporarily modifying or disabling specific rules in a controlled manner.
Troubleshooting ACLs requires a systematic approach because multiple rules may interact with each other. Understanding the logic behind each rule is essential for identifying the root cause of network issues.
Performance Considerations and Optimization of ACLs
Although ACLs are designed to be efficient, poorly structured rules can impact network performance. Large ACLs with many entries may increase processing time as each packet must be evaluated against multiple rules. This can introduce delays in high-traffic environments.
To optimize performance, administrators ensure that frequently matched rules are placed at the top of the ACL. This reduces the number of comparisons required for common traffic types and improves processing efficiency.
Unnecessary or outdated rules should also be removed regularly. Over time, networks evolve, and some ACL rules may no longer serve a purpose. Removing these rules simplifies the ACL structure and reduces processing overhead.
Another optimization strategy involves grouping similar rules together. This reduces redundancy and improves readability, making it easier to manage large ACL configurations.
Efficient ACL design balances security requirements with performance considerations, ensuring that network protection does not come at the cost of usability or speed.
Logging, Monitoring, and Continuous ACL Management
Ongoing monitoring is essential for maintaining effective Access Control Lists. Logging allows administrators to track how ACL rules are being applied in real time. This includes information about permitted and denied traffic, which helps identify potential security threats or misconfigurations.
Regular monitoring also helps detect unusual traffic patterns that may indicate attempted attacks or unauthorized access. By analyzing these patterns, administrators can adjust ACL rules to strengthen network security.
Continuous management involves periodically reviewing ACL configurations to ensure they remain aligned with organizational needs. As business requirements change, ACL rules must be updated accordingly to reflect new services, users, or security policies.
Without continuous management, ACLs can become outdated and less effective over time. Regular audits help maintain accuracy and ensure that only necessary rules are active within the system.
This ongoing process of monitoring and adjustment ensures that ACLs remain a reliable and effective component of network security architecture.
Advanced Use Cases of Access Control Lists in Modern Networks
Access Control Lists are widely used beyond basic traffic filtering, especially in modern enterprise and hybrid network environments. In advanced implementations, ACLs are integrated with other security systems such as intrusion detection systems, intrusion prevention systems, and identity-based access control frameworks. This integration allows organizations to build layered security architectures where ACLs act as an initial filtering mechanism before deeper inspection systems analyze traffic behavior.
In large-scale enterprise networks, ACLs are often used to enforce segmentation between different operational zones. For example, development environments, production systems, and testing environments are separated using strict ACL rules to ensure that changes or experiments in one environment do not affect critical production systems. This segmentation reduces risk and improves operational stability.
ACLs are also used in multi-tenant environments where multiple organizations share the same physical infrastructure. In such cases, ACLs ensure that traffic belonging to one tenant remains isolated from others. This is especially important in cloud computing environments where virtualization and shared resources are common.
Another advanced use case involves securing administrative access to network devices. ACLs can restrict management interfaces so that only authorized IP addresses or networks can access configuration panels or remote management services. This significantly reduces the risk of unauthorized configuration changes or administrative compromise.
Role of ACLs in Network Segmentation and Isolation
Network segmentation is one of the most effective strategies for improving security and performance, and ACLs play a central role in achieving it. Segmentation involves dividing a large network into smaller, controlled sections, each with its own access rules and communication boundaries.
ACLs enforce segmentation by controlling which segments can communicate with each other. For example, a finance network segment may be completely isolated from a guest user segment, ensuring that sensitive financial data is not accessible from less secure areas of the network. This reduces the risk of lateral movement by attackers who may gain access to one part of the network.
In internal enterprise environments, segmentation also helps improve performance. By limiting unnecessary traffic between departments or systems, ACLs reduce congestion and ensure that critical applications receive sufficient bandwidth and resources.
Isolation through ACLs also supports compliance with regulatory requirements. Many industries require strict separation of sensitive data, and ACLs provide a technical mechanism to enforce these rules consistently across the network infrastructure.
This structured separation of network zones creates a controlled environment where access is tightly managed and security risks are minimized.
Integration of ACLs with Firewalls and Security Policies
ACLs are often implemented as part of a larger firewall system, where they act as rule-based filters that define how traffic should be handled. Firewalls use ACL-like logic to inspect packets and enforce security policies at network boundaries.
In many systems, ACLs form the foundation of firewall rule sets. They define basic allow and deny conditions, while advanced firewall features add deeper inspection capabilities such as application awareness, content filtering, and behavioral analysis.
Security policies within an organization are translated into ACL rules to ensure consistent enforcement across all network devices. These policies define who can access specific resources, what types of traffic are allowed, and under what conditions communication can occur.
By aligning ACLs with security policies, organizations ensure that technical configurations directly reflect business requirements. This reduces gaps between policy design and actual enforcement, improving overall security posture.
ACLs also complement other firewall features by handling early-stage filtering. This reduces the workload on more advanced inspection systems, allowing them to focus on more complex threats rather than basic traffic validation.
ACL Optimization for Large-Scale Enterprise Networks
In large networks with thousands of devices and users, ACL management becomes increasingly complex. Without proper optimization, ACLs can become inefficient and difficult to maintain. Optimization strategies are therefore essential to ensure scalability and performance.
One important optimization technique involves rule consolidation. Instead of creating multiple similar rules, administrators combine them into broader, well-structured rules that achieve the same outcome with fewer entries. This reduces processing overhead and simplifies management.
Another optimization approach is hierarchical ACL design. In this model, ACLs are structured in layers, where general rules are applied at higher network levels and more specific rules are applied closer to critical resources. This reduces redundancy and improves efficiency.
Periodic cleanup of unused rules is also essential. Over time, networks evolve, and certain ACL entries may become obsolete. Removing these unnecessary rules reduces complexity and improves processing speed.
Performance tuning also includes ensuring that frequently matched rules are placed higher in the ACL sequence. This reduces evaluation time for common traffic patterns and improves overall network responsiveness.
These optimization techniques help maintain high performance even in complex and rapidly changing network environments.
Security Benefits of Proper ACL Implementation
When properly configured, ACLs significantly enhance network security by enforcing strict access control policies. One of the primary benefits is the reduction of unauthorized access attempts. By explicitly defining allowed communication paths, ACLs ensure that any undefined traffic is automatically blocked.
ACLs also help prevent internal misuse of network resources. Not all security threats come from external sources; sometimes, internal users may attempt to access restricted systems or services. ACLs provide a mechanism to enforce internal boundaries and prevent unauthorized lateral movement.
Another important benefit is the reduction of attack surface. By limiting which services and ports are accessible, ACLs minimize the number of entry points available to potential attackers. This makes it more difficult for malicious actors to exploit vulnerabilities.
ACLs also support incident containment. In the event of a security breach, ACLs can be quickly adjusted to isolate affected systems and prevent further spread of the attack. This containment capability is critical in minimizing damage during security incidents.
Overall, ACLs act as a foundational layer of defense that strengthens the entire network security architecture.
Common Challenges in Managing Access Control Lists
Despite their benefits, ACLs present several challenges when not managed properly. One of the most common challenges is complexity. As networks grow, ACLs can become large and difficult to interpret, especially when multiple rules interact with each other.
Another challenge is maintaining consistency across devices. In distributed environments, ACLs must often be replicated across multiple routers and firewalls. Ensuring that all devices have consistent configurations can be difficult and requires careful coordination.
Human error is also a significant issue in ACL management. Incorrect rule entries, misplaced priorities, or misconfigured IP ranges can lead to network outages or security gaps. These errors are often subtle and difficult to detect without thorough testing.
Scalability is another concern. As the number of ACL rules increases, the time required to process each packet may also increase if the rules are not optimized. This can lead to performance degradation in high-traffic environments.
Addressing these challenges requires strong documentation practices, regular audits, and automated management tools where possible.
Best Practices for Effective ACL Design and Maintenance
Effective ACL management requires following structured best practices. One of the most important practices is simplicity. ACLs should be kept as simple as possible while still achieving security objectives. Overly complex rule sets increase the likelihood of errors and make troubleshooting more difficult.
Another best practice is documentation. Every ACL rule should be clearly documented with its purpose and intended behavior. This helps administrators understand why a rule exists and how it fits into the overall security strategy.
Regular audits are also essential. Periodic reviews ensure that ACL rules remain relevant and aligned with current network requirements. Outdated rules should be removed or updated to reflect changes in infrastructure or policy.
Testing changes before deployment is another critical practice. Any modifications to ACLs should first be tested in a controlled environment to ensure they do not disrupt network operations.
Finally, continuous monitoring should be implemented to track ACL performance and detect anomalies. This proactive approach helps maintain security and ensures that ACLs continue to function as intended over time.
Final Conclusion
Access Control Lists remain one of the most fundamental tools in network security and traffic management. They provide a structured and efficient way to control how data flows through a network, ensuring that only authorized communication is permitted.
From basic filtering to advanced enterprise-level segmentation, ACLs offer flexibility and precision in managing network behavior. Their role in protecting systems from unauthorized access, reducing attack surfaces, and enforcing security policies makes them an essential component of modern networking.
When properly designed, configured, and maintained, ACLs significantly enhance both security and performance. They form the foundation of controlled communication in digital environments, ensuring that networks remain secure, efficient, and reliable in an increasingly connected world.