In today’s digital environments, securing access to networks is one of the most critical responsibilities for IT professionals. Organizations are no longer dealing with simple, isolated systems; instead, they operate in highly connected infrastructures where users, devices, and services constantly interact over local and remote networks. With this level of connectivity comes a major challenge: ensuring that only authorized individuals and devices are allowed to access internal resources.
Even with strong perimeter defenses such as firewalls and intrusion prevention systems, security can still be compromised if physical or wireless access points are not properly controlled. A person with unauthorized physical access to a network port or someone who obtains a shared Wi-Fi password can easily bypass many traditional protections. This is where centralized authentication systems become essential, and among the most widely used solutions for this purpose is RADIUS.
RADIUS plays a vital role in enforcing secure access control by verifying users before granting them permission to connect to a network. It acts as a centralized authority that validates identity, applies security policies, and records access activity, ensuring that every connection is monitored and controlled.
Meaning and Definition of RADIUS in Networking
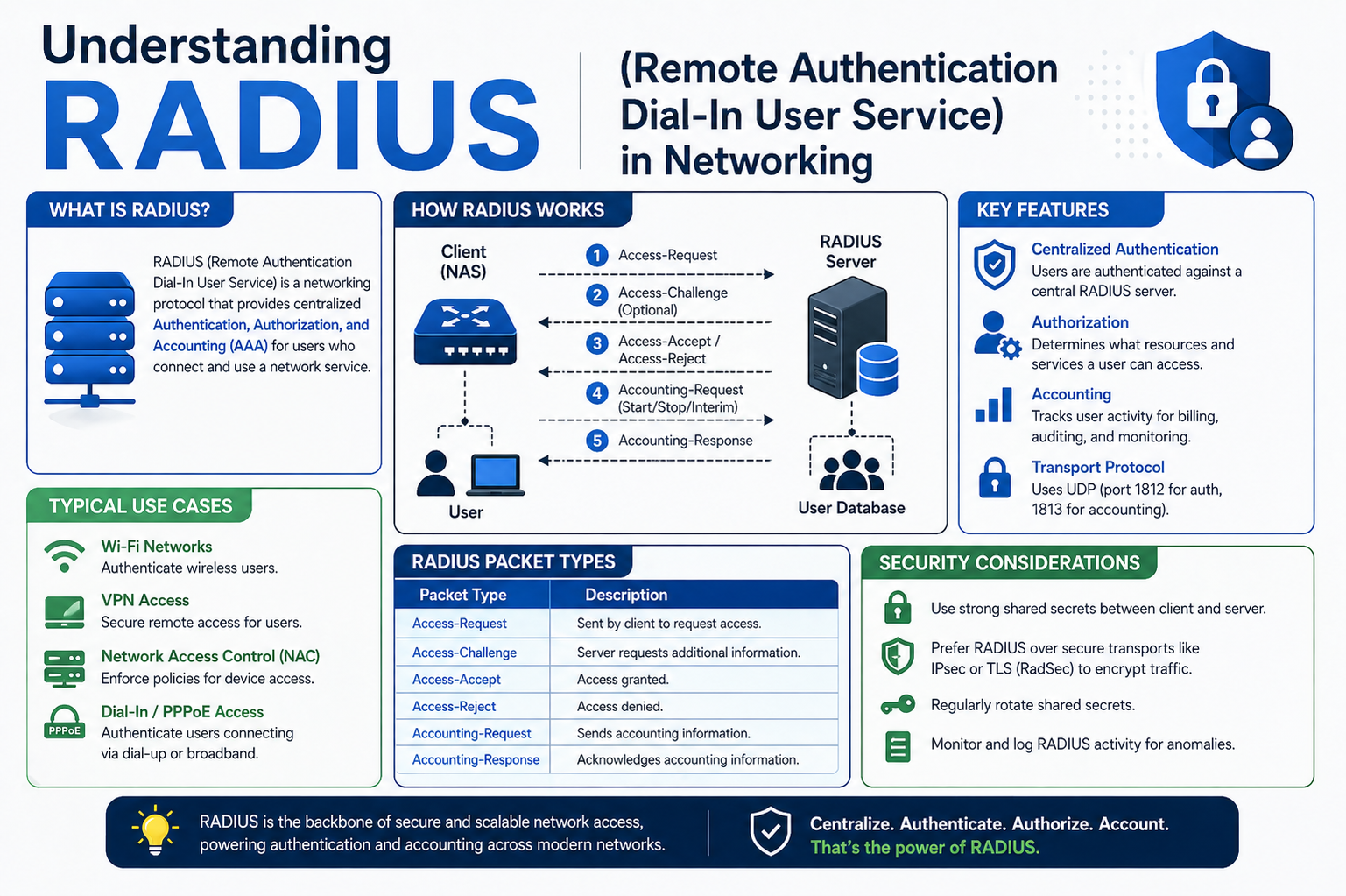
RADIUS stands for Remote Authentication Dial-In User Service. It is a networking protocol designed to provide centralized management for authentication, authorization, and accounting. These three functions are commonly referred to as AAA in networking security frameworks.
Authentication refers to verifying the identity of a user or device attempting to access a network. Authorization determines what resources or services that authenticated user is allowed to use. Accounting tracks and logs user activity, such as login times, session duration, and accessed resources.
RADIUS integrates all three of these functions into a single system, allowing organizations to manage network access in a structured and secure way. Instead of managing user credentials separately on every network device, RADIUS centralizes this process, making administration more efficient and consistent.
At its core, RADIUS ensures that every user requesting access to a network must first prove their identity through valid credentials or digital certificates. Only after successful verification are they granted access according to predefined security policies.
Understanding the Role of AAA Framework in RADIUS
The AAA framework is the foundation on which RADIUS operates. Each component plays a distinct role in controlling network access and maintaining security.
Authentication is the first step in the process. It confirms whether a user or device is genuinely who they claim to be. This is typically done using a username and password combination, digital certificates, or sometimes multi-factor authentication methods.
Authorization comes after authentication. Once a user’s identity has been confirmed, the system determines what level of access should be granted. For example, a user might be allowed access to email services but restricted from accessing sensitive administrative systems.
Accounting is the final component. It involves tracking user activity within the network. This includes recording login and logout times, monitoring bandwidth usage, and maintaining logs of accessed resources. This data is useful for auditing, troubleshooting, and security analysis.
RADIUS brings these three functions together into a unified system, allowing network administrators to enforce consistent policies across all connected devices.
Core Structure and Components of RADIUS System
A RADIUS setup typically consists of two primary components: the RADIUS client and the RADIUS server. Each plays a specific role in the authentication process.
The RADIUS client is usually a network device such as a wireless access point, switch, or VPN gateway. This device acts as a gatekeeper that controls access to the network. It is responsible for collecting user credentials and forwarding them to the authentication server for verification.
The RADIUS server is the central authority that processes authentication requests. It runs on a dedicated system, often using specialized software, and is responsible for validating user credentials against a database or directory service. This directory might contain user accounts stored in systems such as centralized identity management platforms.
When a user attempts to connect to a network through a RADIUS-enabled device, the client does not make the decision independently. Instead, it sends the authentication request to the RADIUS server, which evaluates the credentials and returns a response indicating whether access should be granted or denied.
This separation of roles ensures that access control decisions are centralized, consistent, and easier to manage across large and complex networks.
Step-by-Step Process of How RADIUS Works in a Network
The working process of RADIUS follows a structured flow that ensures secure verification before granting network access.
When a user connects to a network port or wireless access point, the RADIUS client first requests authentication credentials. This could include a username and password or other identity verification methods depending on the network configuration.
Once the credentials are provided, the RADIUS client forwards this information to the RADIUS server. The server then checks the credentials against its configured identity database. If the credentials match a valid user record, the authentication process continues.
After successful authentication, the RADIUS server sends a response back to the client indicating that the user is authorized to access the network. At this stage, the user is granted connectivity based on predefined policies.
If authentication fails, the server sends a rejection response, and access is denied. This ensures that only verified users can interact with the network.
Throughout the session, the system may also log user activity, including connection time and usage details, which are stored for auditing and monitoring purposes.
Real-World Application of RADIUS Authentication Flow
To better understand how RADIUS functions in practice, consider an office environment where employees connect their laptops to a wired or wireless network.
When an employee plugs into a network port, the switch connected to that port does not immediately allow access. Instead, it requests credentials from the device. The employee enters a username and password, which the switch forwards to the authentication server.
The RADIUS server checks these credentials against a centralized user directory. If the information is correct, the server approves the request and sends a response back to the switch. The switch then allows the employee’s device to access the network.
This same process applies to wireless networks as well. When a user tries to connect to Wi-Fi, the access point acts as the RADIUS client, forwarding authentication requests to the server before granting access.
This method ensures that every connection is verified individually, eliminating the risks associated with shared passwords or unmanaged access points.
Importance of Centralized Authentication in RADIUS
One of the most significant advantages of RADIUS is centralized authentication. Instead of managing user credentials separately on each network device, all authentication is handled through a single system.
This centralized approach reduces administrative overhead and improves consistency in security policies. It also minimizes the risk of configuration errors across multiple devices, which can often lead to security vulnerabilities.
In environments without centralized authentication, administrators often rely on shared passwords for wireless access or manually configured credentials on each device. This creates security challenges, especially when employees leave the organization or when passwords are shared beyond intended users.
RADIUS eliminates these problems by ensuring that access is individually verified and centrally managed. This makes it significantly easier to maintain control over who is accessing the network at any given time.
Scalability and Adaptability of RADIUS in Large Networks
RADIUS is designed to handle large-scale environments efficiently. Because authentication requests are processed centrally and not stored on individual devices, the system can support a large number of users without significant performance issues.
In large organizations, multiple RADIUS servers can be deployed to distribute load and ensure continuous availability. This makes the system highly scalable and suitable for enterprise-level networks, educational institutions, and service providers.
Additionally, RADIUS can integrate with various identity management systems, allowing it to adapt to different organizational infrastructures. Whether a company uses traditional directory services or modern cloud-based identity platforms, RADIUS can be configured to work seamlessly within those environments.
Introduction to Authentication Flexibility in RADIUS
Another important aspect of RADIUS is its flexibility in supporting different authentication methods. While username and password combinations are commonly used, RADIUS is not limited to this approach.
It can also support digital certificates, hardware tokens, and multi-factor authentication systems. This flexibility allows organizations to implement stronger security measures based on their specific requirements.
Multi-factor authentication adds an extra layer of protection by requiring users to verify their identity using more than one method. For example, a user may need to enter a password and confirm a code sent to their mobile device.
This adaptability makes RADIUS suitable for environments with varying security needs, from small businesses to large enterprises with strict compliance requirements.
Foundational Importance of RADIUS in Network Access Control
RADIUS serves as a foundational technology in modern network security by ensuring that access is controlled, verified, and monitored. It provides a structured approach to managing authentication while maintaining flexibility and scalability.
By centralizing access control and integrating with existing identity systems, RADIUS helps organizations maintain stronger security postures without increasing administrative complexity.
Deeper Understanding of RADIUS Architecture in Real Environments
RADIUS operates as a distributed authentication system designed to separate decision-making from network access points. This separation is what makes it highly effective in complex infrastructures where multiple devices and users require controlled access simultaneously. Instead of each network device independently verifying users, all authentication logic is centralized in a dedicated system.
In practical environments, this architecture is especially useful in organizations with multiple departments, branches, or remote users. Each access point, switch, or gateway simply forwards authentication requests, while the RADIUS server performs the heavy lifting of verification and policy enforcement. This design significantly reduces inconsistencies in access control, since all decisions come from a single authoritative source.
Another important aspect of this architecture is its ability to integrate with identity repositories. These repositories may contain user credentials, group memberships, and access rules. When a request arrives, the RADIUS server consults these repositories to determine whether access should be granted and under what conditions.
Detailed Flow of Authentication Communication in RADIUS
The communication process in RADIUS follows a structured exchange of messages between the client and the server. When a user attempts to access a network, the first step is the creation of an authentication request by the network access device. This request contains user credentials and session details, which are then encapsulated and securely forwarded to the RADIUS server.
Once the server receives the request, it processes the credentials by comparing them against stored records in the identity system. If the credentials match an existing user profile, the server evaluates additional conditions such as group membership, access policies, or time-based restrictions.
After evaluation, the server responds with one of three possible outcomes. It may accept the request, allowing full or limited access to the network. It may reject the request, denying access entirely. Or it may challenge the user for additional authentication factors if multi-step verification is enabled.
This structured communication ensures that no user gains access without proper validation, and every decision is centrally controlled for consistency and security enforcement.
Role of Network Access Server in RADIUS Ecosystem
The network access server plays a crucial intermediary role in the RADIUS ecosystem. It is responsible for enforcing access control at the point where users connect physically or wirelessly to the network.
This device does not independently decide whether a user should be granted access. Instead, it acts as a relay between the user and the authentication server. It collects credentials, forwards them securely, and then enforces the response received from the RADIUS server.
In environments such as corporate offices or educational campuses, these network access servers are typically switches, wireless controllers, or VPN gateways. Each of these devices ensures that unauthorized users cannot bypass authentication checks, even if they have direct physical access to network ports or wireless signals.
This design is essential for maintaining strong perimeter security within internal networks, where physical access alone should not guarantee connectivity.
Integration of RADIUS with Directory Services
One of the most powerful features of RADIUS is its ability to integrate with existing directory services. These services act as centralized databases that store user identities, credentials, and access permissions.
When a RADIUS server receives an authentication request, it does not store user credentials locally in most cases. Instead, it queries an external directory system to validate the information. This approach ensures that user management remains centralized and consistent across the entire organization.
Directory integration also allows organizations to apply group-based policies. For example, users belonging to a specific department can be assigned different access levels compared to general staff or administrators. These policies are automatically enforced during authentication without requiring manual configuration on individual network devices.
This integration reduces administrative complexity while improving scalability, as changes in user roles or permissions only need to be updated in one central location.
Security Mechanisms Used Within RADIUS Communication
Security is a fundamental aspect of RADIUS design, and several mechanisms are used to protect authentication data during transmission and processing.
RADIUS uses shared secret keys between clients and servers to secure communication. These keys ensure that only trusted devices can exchange authentication data. If a device does not have the correct shared secret, it cannot participate in the authentication process.
Although early implementations of RADIUS used limited encryption methods, modern deployments often incorporate additional security layers such as Transport Layer Security. This helps protect sensitive information like passwords from interception during transmission.
Another important security feature is request authentication integrity. This ensures that authentication messages cannot be altered or forged while traveling between the client and server. If any modification is detected, the request is automatically rejected.
These security mechanisms work together to maintain the confidentiality and integrity of authentication processes across the network.
Understanding Authorization Policies in RADIUS Systems
After authentication, the next critical step in RADIUS is authorization. This stage determines what a user is allowed to do once access has been granted.
Authorization policies are defined centrally and can include a wide range of restrictions. These may control which network segments a user can access, what applications they can use, or how much bandwidth they are allowed to consume.
For example, an employee in the finance department might have access to internal financial systems but restricted access to development environments. Similarly, guest users may only be allowed internet access without any connection to internal resources.
These policies are enforced automatically by the RADIUS server and applied dynamically based on user identity and role. This ensures that access control is not only secure but also flexible and adaptable to organizational needs.
Accounting Functions and Their Importance in RADIUS
Accounting is the final component of the AAA framework and plays a crucial role in monitoring network activity. It involves recording detailed information about user sessions, including login times, logout times, and resource usage.
This data is stored for auditing purposes and can be used to analyze network behavior, detect anomalies, or investigate security incidents. For example, if unauthorized activity is suspected, administrators can review accounting logs to identify which user account was active at a specific time.
Accounting also supports operational analysis by providing insights into network usage patterns. Organizations can use this information to optimize performance, allocate resources more efficiently, and plan infrastructure upgrades.
In many environments, accounting data is also required for compliance with regulatory standards, making it an essential part of network governance.
Interaction Between RADIUS and Wireless Networks
RADIUS plays a particularly important role in securing wireless networks, where physical boundaries are not present. In such environments, anyone within signal range could potentially attempt to connect to the network.
To address this risk, wireless access points are configured as RADIUS clients. When a user attempts to connect to a Wi-Fi network, the access point forwards authentication requests to the RADIUS server instead of relying on a shared password.
This ensures that each user must provide valid credentials before gaining access. It also allows organizations to enforce individual authentication rather than relying on a single password shared among all users.
This approach significantly improves wireless security and reduces the risks associated with password leakage or unauthorized sharing.
Use of RADIUS in Virtual Private Network Environments
RADIUS is also commonly used in virtual private network systems to control remote access. When users connect from external locations, their authentication requests are processed through the RADIUS server before granting access to internal resources.
This ensures that remote users are subject to the same security policies as internal users. It also allows organizations to monitor and control remote access in a centralized manner.
In VPN environments, RADIUS can enforce additional security conditions such as device compliance checks, multi-factor authentication, or time-based access restrictions. This helps maintain consistent security across both internal and external connections.
Importance of Policy Enforcement in RADIUS Systems
Policy enforcement is one of the most critical functions of RADIUS. It ensures that access decisions are not only based on identity but also on predefined organizational rules.
These policies can be highly granular, allowing administrators to define specific access conditions for different user groups. For example, certain users may only be allowed access during business hours, while others may have continuous access based on their role.
Policy enforcement also ensures that security rules are applied consistently across all network devices. Since decisions are centralized, there is no risk of inconsistent configurations across different access points.
This centralized policy management makes RADIUS a powerful tool for maintaining structured and secure network environments.
Growing Importance of RADIUS in Modern Infrastructure
As networks continue to expand and become more complex, the need for centralized authentication systems like RADIUS becomes even more important. Organizations are increasingly adopting hybrid environments that combine on-premises infrastructure with cloud-based services, making consistent access control a major challenge.
RADIUS provides a unified solution that can integrate with both traditional and modern systems, ensuring that security policies remain consistent regardless of where users are connecting from.
Its ability to scale, integrate, and enforce centralized control makes it a foundational component in enterprise network security strategies.
Advanced Authentication Processing Inside RADIUS Systems
RADIUS is designed to handle authentication requests in a structured and highly controlled manner, ensuring that every access attempt is evaluated carefully before any permission is granted. When a request reaches the RADIUS server, it does not simply perform a basic check and respond immediately. Instead, it follows a multi-layer evaluation process that may involve credential verification, policy matching, and conditional rule application.
The first layer of processing involves identity validation, where the system confirms whether the provided credentials exist within the authorized directory. Once a match is found, the system moves to the next layer, which evaluates the user’s role, group membership, and assigned permissions. This ensures that authentication alone is not enough; authorization rules must also be satisfied.
In more advanced configurations, RADIUS may also apply contextual checks. These checks can include the device type being used, the location of the login attempt, or even the time of access. This additional intelligence allows organizations to enforce adaptive security policies that respond dynamically to different conditions.
Multi-Factor Authentication Support in RADIUS Environments
Modern RADIUS deployments often extend beyond simple username and password verification by integrating multi-factor authentication mechanisms. This approach significantly improves security by requiring users to provide multiple forms of identity verification before gaining access.
In such systems, after entering primary credentials, users may be required to verify their identity through an additional factor. This could include a one-time passcode sent to a mobile device, a hardware authentication token, or biometric verification depending on the system’s configuration.
The RADIUS server coordinates these authentication steps by interacting with external authentication services or secondary verification systems. Only after all required factors are successfully validated does the system approve access.
This layered authentication approach helps protect against credential theft, as stolen passwords alone are no longer sufficient to gain network entry. It is particularly useful in environments where sensitive data or critical infrastructure is involved.
Role of RADIUS in Policy-Based Network Access Control
One of the most powerful aspects of RADIUS is its ability to enforce policy-based access control. Instead of granting or denying access solely based on identity, RADIUS evaluates predefined rules that determine what level of access a user should receive.
These policies can be highly detailed and customized according to organizational needs. For instance, different departments within an organization may have varying access requirements. A finance team might require access to accounting systems, while a technical team may need access to server infrastructure.
RADIUS evaluates these policies during the authentication process and dynamically assigns access privileges accordingly. This ensures that users only receive the permissions necessary for their roles, reducing the risk of unauthorized access to sensitive resources.
Policy-based control also supports time restrictions, bandwidth limitations, and device-specific rules. These capabilities allow organizations to create highly controlled and secure network environments.
Dynamic Authorization and Session Control in RADIUS
RADIUS not only determines access at the initial login stage but can also manage user sessions dynamically after authentication. This means that access permissions can be adjusted even while a user is actively connected to the network.
For example, if a user’s role changes or if suspicious activity is detected, the RADIUS server can modify or terminate the session in real time. This dynamic control adds an additional layer of security by ensuring that access is continuously evaluated rather than granted once and ignored.
Session control also includes tracking active connections and applying usage limits. If a user exceeds defined thresholds, such as bandwidth consumption or session duration, the system can automatically restrict or disconnect the session.
This capability is especially useful in environments where resource management and security monitoring must operate simultaneously.
Interaction Between RADIUS and Network Infrastructure Devices
RADIUS relies heavily on network infrastructure devices to enforce authentication decisions at the edge of the network. These devices include switches, wireless access points, and VPN concentrators, all of which act as intermediaries between users and the authentication server.
When a device receives a connection request, it does not make an independent decision. Instead, it forwards the request to the RADIUS server and waits for a response. Based on this response, the device either allows or blocks access.
This interaction ensures that authentication is consistently enforced across all entry points into the network. It also prevents unauthorized bypass attempts, as every connection must pass through the same centralized verification process.
By integrating RADIUS with network hardware, organizations create a unified security layer that protects both wired and wireless access points equally.
Role of RADIUS in Enterprise-Level Identity Management
In large organizations, identity management becomes a critical challenge due to the number of users, devices, and services involved. RADIUS plays an important role in simplifying this complexity by acting as a centralized authentication gateway.
Instead of managing credentials separately across multiple systems, RADIUS integrates with enterprise identity platforms to provide a single source of truth. This ensures that user information remains consistent across all connected services.
When changes occur, such as employee onboarding, role modification, or account deactivation, these updates are reflected automatically across the entire network through the identity system. RADIUS simply references this centralized data during authentication.
This approach reduces administrative overhead and minimizes the risk of outdated or inconsistent access permissions across different systems.
Security Logging and Monitoring Capabilities of RADIUS
RADIUS provides extensive logging and monitoring capabilities through its accounting functions. Every authentication attempt, whether successful or failed, can be recorded for analysis and auditing purposes.
These logs typically include details such as user identity, access time, session duration, and the device used for connection. This information is valuable for both security monitoring and operational analysis.
From a security perspective, these logs help identify suspicious behavior, such as repeated failed login attempts or unauthorized access patterns. Administrators can use this information to detect potential threats and respond proactively.
From an operational standpoint, usage logs provide insights into network performance and user behavior. This data can be used to optimize resource allocation and improve system efficiency.
Redundancy and High Availability in RADIUS Deployments
Since RADIUS plays a central role in network authentication, its availability is critical for maintaining uninterrupted access. If a RADIUS server becomes unavailable, users may be unable to connect to the network, even if all other systems are functioning properly.
To address this issue, organizations often deploy multiple RADIUS servers in a redundant configuration. In such setups, if one server fails, another can automatically take over authentication responsibilities without disrupting service.
This high availability design ensures continuous network access and prevents single points of failure. Load balancing can also be implemented to distribute authentication requests across multiple servers, improving performance and reliability.
Redundant configurations are considered essential in enterprise environments where downtime can have significant operational impacts.
Challenges in Configuring and Managing RADIUS Systems
Although RADIUS provides powerful security benefits, it can also introduce complexity during setup and management. Proper configuration requires careful alignment between the RADIUS server, network devices, and identity systems.
One of the main challenges lies in ensuring compatibility between different components. Each device may have its own configuration requirements, and misalignment can lead to authentication failures or access issues.
Another challenge is managing shared secrets and encryption settings securely across multiple devices. If these credentials are not properly managed, they can become a potential security risk.
Additionally, troubleshooting authentication issues in RADIUS environments can be complex, as failures may originate from multiple sources such as network configuration, directory services, or policy mismatches.
Importance of Testing and Controlled Deployment of RADIUS
Due to its critical role in network access control, RADIUS should always be deployed in a controlled and tested environment before being implemented in production systems. Testing allows administrators to identify configuration issues, verify policy behavior, and ensure compatibility across all connected devices.
A controlled deployment typically involves setting up a test network that mirrors the production environment. This allows administrators to simulate real-world conditions without risking disruption to live systems.
Through testing, organizations can validate authentication flows, verify failover mechanisms, and ensure that security policies are correctly enforced. This reduces the risk of unexpected issues when the system goes live.
Proper testing is a key step in ensuring a stable and secure RADIUS implementation.
Expanding Role of RADIUS in Modern Digital Networks
As digital networks continue to evolve, the role of RADIUS is expanding beyond traditional authentication systems. It is increasingly being integrated into hybrid infrastructures that combine on-premises systems with cloud-based services.
This expansion allows organizations to maintain consistent identity and access control across diverse environments. Whether users are connecting from internal networks, remote locations, or cloud platforms, RADIUS provides a unified authentication framework.
Its adaptability and strong security foundation make it a critical component in modern identity and access management strategies, ensuring secure connectivity across increasingly complex network ecosystems.
RADIUS in Cloud-Based and Hybrid Network Environments
Modern IT infrastructures are no longer limited to traditional on-premises systems. Many organizations now operate in hybrid environments where cloud services and local networks coexist. In such setups, maintaining consistent authentication and access control becomes more challenging, and RADIUS plays an important role in bridging this gap.
RADIUS can integrate with cloud-based identity providers while still supporting internal directory systems. This allows users to authenticate regardless of whether they are accessing resources hosted locally or in the cloud. The authentication request still follows the same structured process, but the identity validation may occur across distributed systems.
In hybrid environments, RADIUS acts as a central authentication gateway that connects multiple identity sources. This ensures that security policies remain uniform across different platforms. Whether a user logs in from an office network, a remote location, or a cloud-hosted application, the authentication rules are consistently applied.
This unified approach reduces complexity for administrators and strengthens overall security by ensuring that identity verification is not fragmented across different systems.
Performance Optimization and Load Handling in RADIUS Systems
As networks grow, the number of authentication requests increases significantly. RADIUS is designed to handle this load efficiently, but proper optimization is essential to maintain performance.
One important optimization technique involves distributing authentication requests across multiple servers. This prevents any single server from becoming overloaded and ensures smooth processing even during peak usage times.
Caching mechanisms can also be used to temporarily store authentication results, reducing repeated queries for frequently accessed users. This improves response time and reduces unnecessary load on backend identity systems.
Network administrators may also fine-tune timeout settings and retry intervals to ensure that authentication requests are processed efficiently without unnecessary delays. These optimizations help maintain a balance between security and performance.
Security Risks and Threat Mitigation in RADIUS Deployments
Although RADIUS is a secure authentication system, it is not completely immune to risks if not properly configured. One potential risk is misconfiguration of shared secrets between clients and servers. If these secrets are weak or exposed, unauthorized devices could potentially send fraudulent authentication requests.
Another risk involves unsecured communication channels. If encryption is not properly implemented, sensitive authentication data could be intercepted during transmission. To mitigate this, modern deployments often rely on secure transport protocols to protect data integrity.
Brute-force attacks are also a concern in authentication systems. RADIUS environments must implement rate limiting and account lockout policies to prevent repeated unauthorized login attempts.
Proper monitoring and logging play a crucial role in identifying suspicious behavior early. By analyzing authentication patterns, administrators can detect anomalies and respond to potential threats before they escalate.
Role of RADIUS in Wireless Enterprise Security
Wireless networks present unique security challenges because access is not physically restricted. Anyone within range of a wireless signal could attempt to connect, making strong authentication essential.
RADIUS enhances wireless security by replacing shared passwords with individual authentication. Instead of using a single password for all users, each connection request is verified individually through the authentication server.
This approach allows organizations to assign unique credentials to each user, ensuring accountability and traceability. If a security incident occurs, administrators can identify exactly which user account was involved.
RADIUS also supports dynamic access control for wireless networks. For example, users can be assigned different levels of access based on their role, device type, or security status. This ensures that sensitive internal resources remain protected even within wireless environments.
Use of RADIUS in Remote Work and VPN Connectivity
With the rise of remote work, secure access to internal networks from external locations has become essential. RADIUS is widely used in virtual private network systems to authenticate remote users before granting access.
When a remote user attempts to connect, their credentials are sent through the VPN gateway, which acts as a RADIUS client. The request is then forwarded to the RADIUS server for verification.
Once authenticated, the user is granted secure access to internal systems as if they were physically present in the office network. This ensures that remote connections are subject to the same security policies as internal users.
RADIUS also allows organizations to enforce additional controls for remote access. These may include device compliance checks, geographic restrictions, or time-based access rules. This ensures that remote connectivity remains secure and controlled.
Administrative Efficiency and Centralized Policy Management
One of the key advantages of RADIUS is the simplification of administrative tasks through centralized policy management. Instead of configuring access rules on each individual network device, administrators define policies in a single location.
These policies are then automatically enforced across all connected devices through the RADIUS server. This reduces configuration errors and ensures consistency across the entire network.
Centralized management also simplifies user administration. When an employee joins, changes roles, or leaves an organization, their access rights can be updated in one place. These changes are immediately reflected across all systems that rely on RADIUS for authentication.
This efficiency reduces administrative workload and improves overall security governance within the organization.
Troubleshooting Authentication Issues in RADIUS Networks
Despite its structured design, RADIUS environments can sometimes experience authentication issues. These problems may arise due to network misconfigurations, incorrect credentials, or communication failures between components.
One common issue is mismatched shared secrets between the RADIUS client and server. If these values do not match exactly, authentication requests will fail. Another issue may involve incorrect directory synchronization, where user accounts are not properly updated in the identity system.
Network connectivity problems can also disrupt authentication flow. If the RADIUS server is unreachable, users may be unable to access the network unless backup systems are in place.
To resolve these issues, administrators typically rely on detailed log analysis provided by the RADIUS system. These logs help identify where the authentication process failed and guide corrective actions.
Evolution of RADIUS in Modern Authentication Technologies
Over time, RADIUS has evolved to support more advanced authentication requirements. While its core purpose remains the same, it has adapted to work with modern identity systems and security frameworks.
Earlier implementations focused primarily on simple username and password authentication. Modern systems now support multi-factor authentication, certificate-based authentication, and integration with cloud identity platforms.
This evolution has allowed RADIUS to remain relevant in increasingly complex network environments. It continues to serve as a foundational authentication protocol while adapting to new security demands.
Its flexibility ensures that it can coexist with newer technologies without losing its core functionality.
Importance of Regular Maintenance and Monitoring in RADIUS Systems
Maintaining a RADIUS system requires continuous monitoring and regular updates. Security policies must be reviewed periodically to ensure they align with organizational requirements.
System updates are also important to address vulnerabilities and improve performance. Outdated configurations can expose networks to unnecessary risks, making maintenance a critical responsibility.
Monitoring authentication logs helps identify unusual patterns or potential security threats. By analyzing this data, administrators can take proactive measures to strengthen network security.
Regular testing of failover systems is also necessary to ensure high availability. This ensures that backup servers can take over smoothly in case of primary system failure.
Future Role of RADIUS in Network Security Infrastructure
As networks continue to expand and become more complex, the role of RADIUS is expected to remain significant. Its ability to provide centralized authentication and policy enforcement makes it a reliable foundation for secure network access.
Future implementations are likely to focus on deeper integration with cloud-native identity systems, improved automation, and enhanced security analytics. These advancements will help organizations manage access control more efficiently in increasingly dynamic environments.
Despite the emergence of newer authentication technologies, RADIUS continues to serve as a trusted backbone for enterprise network security. Its structured approach, scalability, and adaptability ensure that it remains a key component in modern access control systems.
Conclusion
RADIUS remains a fundamental protocol in network security because it provides a structured and centralized way to control who can access a network and under what conditions. By combining authentication, authorization, and accounting into a single system, it ensures that every access request is verified, controlled, and recorded in a consistent manner. This reduces reliance on decentralized device-based authentication, which is often harder to manage and more vulnerable to security gaps.
Its greatest strength lies in centralization. Instead of configuring security settings on every switch, access point, or VPN gateway individually, administrators manage all access rules from a single server. This not only improves security consistency but also significantly reduces administrative effort and the risk of misconfiguration across large infrastructures.
RADIUS also supports scalability, making it suitable for small organizations as well as large enterprise environments with thousands of users and devices. Through integration with directory services and modern identity platforms, it adapts well to evolving IT ecosystems, including cloud-based and hybrid networks.
At the same time, it is important to recognize its operational challenges. Proper configuration, secure deployment, and redundancy planning are essential to avoid downtime and security weaknesses. A poorly configured RADIUS system can become a point of failure, which is why testing, monitoring, and failover planning are critical parts of its implementation.
Overall, RADIUS continues to play a vital role in securing network access in both traditional and modern infrastructures. Its ability to enforce centralized control, support flexible authentication methods, and maintain detailed access logs makes it one of the most reliable and widely used authentication frameworks in enterprise networking today.