Lightweight Directory Access Protocol, commonly known as LDAP, is a foundational protocol used to access and manage directory information across a network. It acts as a standardized method for organizing and retrieving structured data, especially in environments where user identities, devices, and services must be centrally managed. Rather than being a standalone application, LDAP functions as a communication language that enables systems to interact with directory services efficiently. This distinction is important because it highlights LDAP’s role as a bridge between clients and directory databases, ensuring that information can be queried and modified in a consistent and predictable manner across diverse systems.
The Growing Need for Structured Directory Services
As organizations expand, the complexity of managing users, devices, and permissions increases significantly. In a small environment, tracking a handful of users may be straightforward, but as the number grows into hundreds or thousands across multiple locations, manual management becomes impractical. LDAP addresses this challenge by providing a centralized and hierarchical structure for storing directory data. This structure allows administrators to organize information logically, such as grouping users by department or location, making it easier to manage access and maintain consistency across the network. The ability to scale efficiently is one of LDAP’s most valuable strengths.
LDAP as a Logical Framework Rather Than Software
It is essential to understand that LDAP is not software in itself but a protocol that defines how data should be structured and accessed. Directory services implement LDAP to provide actual functionality. This means that different platforms can use LDAP while still maintaining interoperability. For example, directory solutions like Microsoft Active Directory and Open LDAP both rely on LDAP to organize and retrieve data, even though their internal implementations differ. This flexibility allows organizations to choose solutions that best fit their needs while maintaining compatibility with other systems.
Hierarchical Data Organization in LDAP
One of LDAP’s defining characteristics is its hierarchical data structure, often visualized as a tree. This structure is known as the Directory Information Tree, where each node represents an entry such as a user, group, or device. Entries are organized in a parent-child relationship, which reflects real-world organizational structures. For example, a company might have a top-level domain, followed by organizational units for departments, and individual user entries beneath them. This hierarchical model ensures that data is both organized and easily searchable, enabling efficient queries and streamlined management.
Distinguished Names and Unique Identification
Within the LDAP structure, each entry is uniquely identified by a Distinguished Name, often abbreviated as DN. This identifier specifies the exact location of an entry within the directory tree, ensuring there is no ambiguity when accessing data. A Distinguished Name is composed of multiple components that represent different levels of the hierarchy, such as common names and organizational units. This approach allows systems to pinpoint specific entries quickly, which is crucial for tasks like authentication and data retrieval. Without a reliable identification mechanism like DN, managing large directories would become significantly more complex.
Core Functions of LDAP in Network Environments
LDAP plays a central role in several critical network operations, particularly those related to identity and access management. One of its primary functions is authentication, where it verifies user credentials against stored directory data. When a user attempts to log in, their credentials are sent to the directory service, which checks for a match before granting access. LDAP is also used for authorization, determining what resources a user is allowed to access based on their role or group membership. These functions are essential for maintaining security and ensuring that users can only access appropriate resources.
User and Resource Management Capabilities
Beyond authentication, LDAP is widely used for managing user accounts and other directory objects. Administrators can create, modify, and delete entries within the directory, allowing them to keep information up to date. This includes tasks such as updating user details, assigning roles, and managing group memberships. Because LDAP centralizes this information, changes made in one place are reflected across all connected systems. This eliminates inconsistencies and reduces administrative overhead, making it easier to maintain an accurate and reliable directory.
Integration Across Applications and Services
Another key advantage of LDAP is its ability to integrate seamlessly with various applications and services. Many enterprise tools rely on LDAP to access directory information, enabling features like centralized login and address book lookups. For instance, email clients and collaboration platforms often use LDAP to retrieve user details, allowing employees to search for colleagues بسهولة within the organization. This level of integration enhances productivity by providing a unified source of information that can be accessed from multiple applications without duplication.
How LDAP Communication Works
LDAP operates on a client-server model, where a client application sends requests to a directory server. These requests follow a standardized format, ensuring compatibility across different implementations. When a client needs information, it sends a query specifying the criteria for the search. The server processes this request by traversing the directory structure and returning the relevant results. This process is optimized for efficiency, allowing even large directories to be searched بسرعة without significant delays.
Common LDAP Operations and Their Purpose
Several core operations define how LDAP interacts with directory data. The bind operation is used to authenticate a client to the server, establishing a session for further communication. The search operation allows clients to query the directory for specific entries based on defined criteria. The add operation enables the creation of new entries, while the modify operation updates existing ones. Finally, the delete operation removes entries that are no longer needed. Together, these operations provide a complete set of tools for managing directory information effectively.
The Role of TCP/IP in LDAP Communication
LDAP relies on the TCP/IP protocol suite for network communication, ensuring reliable data transfer between clients and servers. TCP provides a connection-oriented approach, which guarantees that data packets are delivered accurately and in the correct order. This reliability is essential for directory operations, where even minor errors could lead to incorrect data retrieval or failed authentication attempts. By building on TCP/IP, LDAP benefits from a widely adopted and robust networking foundation.
Introduction to LDAP Ports and Their Significance
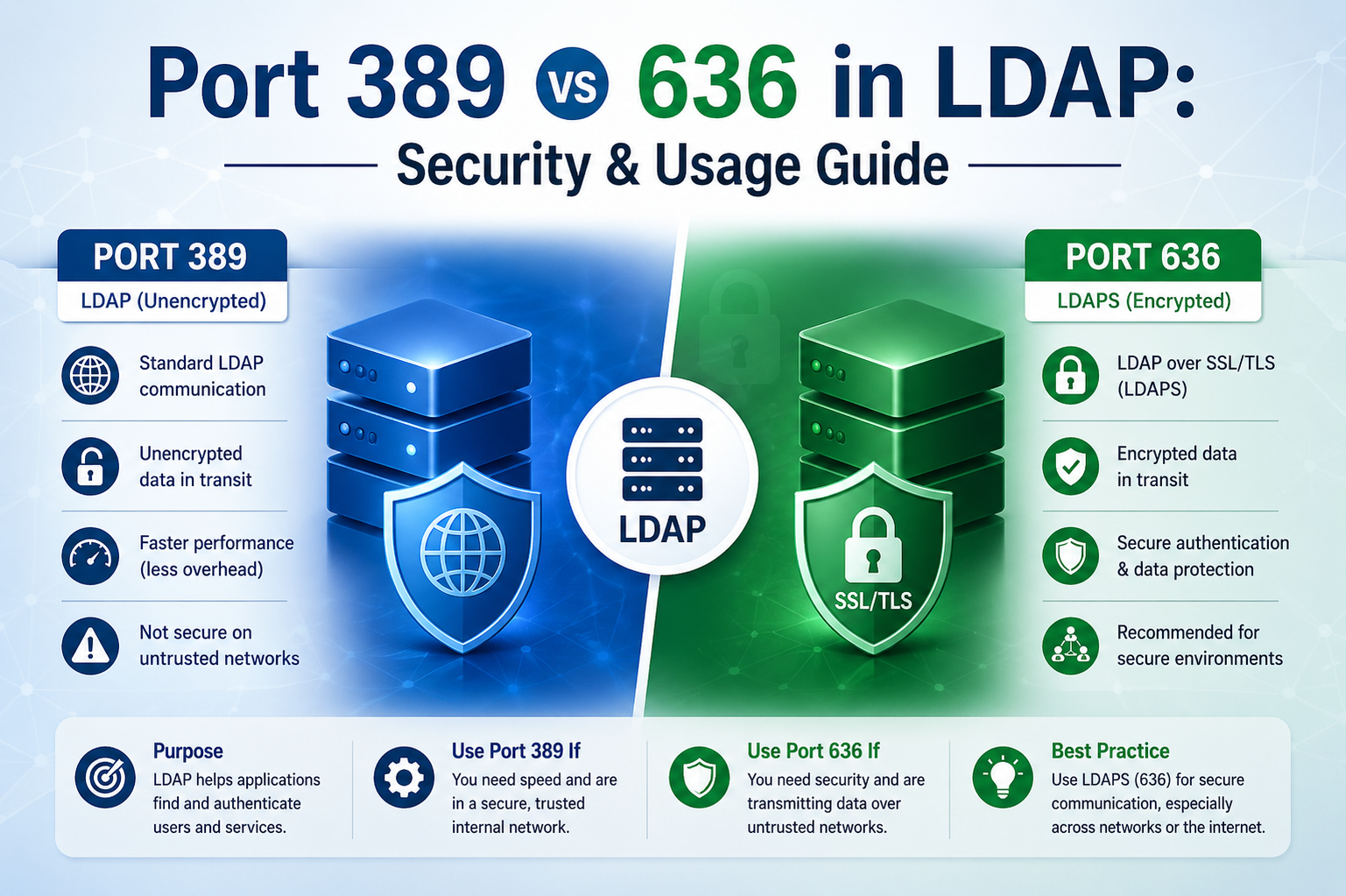
In networking, ports serve as communication endpoints that allow different services to operate simultaneously on the same device. LDAP uses specific ports to handle its traffic, ensuring that requests are directed to the correct service. The two primary ports associated with LDAP are 389 and 636. These ports differentiate between unencrypted and encrypted communication, respectively. Understanding the distinction between them is crucial for configuring secure and efficient directory services.
Default Port 389 and Its Characteristics
Port 389 is the default port used for standard LDAP communication. It is commonly referred to as the clear text port because data transmitted through it is not encrypted. This means that information sent between the client and server can potentially be intercepted and read by unauthorized parties. While this may be acceptable in low-risk internal environments, it poses significant security concerns in most modern networks. Despite these risks, port 389 remains widely used due to its simplicity and lower computational overhead.
Clear Text Communication and Its Implications
The term clear text refers to data that is transmitted in an unencrypted form, making it easily readable if intercepted. In the context of LDAP, this means that sensitive information such as usernames and passwords could be exposed during transmission. This vulnerability highlights the importance of carefully considering when and where to use port 389. While it may offer performance advantages, the lack of encryption makes it unsuitable for scenarios involving confidential data or external network access.
Security Considerations for Unencrypted LDAP
Using unencrypted LDAP requires a thorough assessment of potential risks. In environments where network access is tightly controlled and isolated, the risk of interception may be minimal. However, as soon as data travels beyond a secure internal network, the likelihood of exposure increases significantly. Attackers can use packet sniffing tools to capture and analyze network traffic, potentially gaining access to sensitive information. This risk underscores the need for stronger security measures in most real-world applications.
Balancing Performance and Security Needs
One reason some organizations continue to use port 389 is the reduced computational overhead compared to encrypted communication. Encryption requires additional processing power to encode and decode data, which can impact performance in high-traffic environments. In cases where security risks are low, organizations may prioritize efficiency over encryption. However, this decision must be made carefully, taking into account the sensitivity of the data and the potential consequences of a security breach.
Transitioning from Unencrypted to Encrypted LDAP Communication
As network environments evolve and security threats become more sophisticated, the shift from unencrypted to encrypted communication has become increasingly important. LDAP implementations that once relied heavily on port 389 are now often complemented or replaced by secure alternatives to protect sensitive directory data. This transition is not merely a technical upgrade but a fundamental change in how organizations approach data protection. Encryption ensures that even if data is intercepted during transmission, it remains unreadable to unauthorized parties, significantly reducing the risk of breaches.
Introduction to LDAP Port 636 and Secure Communication
LDAP port 636 is designated for secure communication using encryption protocols. Unlike port 389, which transmits data in plain text, port 636 ensures that all information exchanged between the client and server is protected. This port is commonly associated with LDAP over SSL or TLS, providing a secure channel for directory operations. By using encryption, organizations can safeguard credentials, personal information, and other sensitive data from interception and misuse. This makes port 636 the preferred choice in most modern network environments.
Understanding Encryption in LDAP Context
Encryption in LDAP involves converting readable data into a coded format that can only be deciphered with the appropriate key. This process ensures confidentiality and integrity during data transmission. When a client connects to an LDAP server over port 636, an encrypted session is established before any data is exchanged. This secure session prevents unauthorized access and protects against common network attacks such as eavesdropping and man-in-the-middle attacks. Encryption thus forms a critical layer of defense in directory service communication.
Role of TLS in Securing LDAP Traffic
Transport Layer Security, often referred to as TLS, plays a central role in securing LDAP communication over port 636. TLS operates beneath the application layer, providing encryption and authentication services to ensure secure data exchange. When a connection is initiated, TLS performs a handshake process that verifies the identities of both the client and the server. This process establishes trust and negotiates encryption parameters, ensuring that subsequent data transmission is secure. TLS has largely replaced older encryption protocols due to its enhanced security features and widespread adoption.
The TLS Handshake Process Explained
The TLS handshake is a multi-step process that establishes a secure connection between two parties. Initially, the client sends a request to the server, indicating its supported encryption methods. The server responds by selecting the most suitable option and presenting its digital certificate. The client then verifies the certificate to ensure the server’s authenticity. Once verification is complete, both parties generate session keys used to encrypt and decrypt data. This process ensures that communication remains confidential and tamper-proof throughout the session.
Encryption Algorithms and Key Exchange Mechanisms
During the TLS handshake, encryption algorithms and key exchange methods are selected to secure the connection. Symmetric encryption is typically used for data transmission due to its efficiency, while asymmetric encryption is employed during the handshake to exchange keys securely. This combination provides a balance between performance and security. The strength of encryption depends on factors such as key length and algorithm choice, making it important to use modern, well-supported standards to maintain robust protection.
Certificates and Their Importance in LDAP Security
Digital certificates are a cornerstone of secure LDAP communication. These certificates verify the identity of the server and, in some cases, the client as well. Issued by trusted certificate authorities or generated internally, certificates contain information about the entity they represent and a public key used for encryption. Proper certificate management is essential to maintaining secure connections. Expired or misconfigured certificates can disrupt communication or create vulnerabilities, emphasizing the need for regular monitoring and updates.
Steps to Enable Secure LDAP Communication
Enabling LDAP over port 636 involves several key steps. First, a digital certificate must be generated or obtained from a trusted source. This certificate is then installed on the LDAP server, allowing it to establish secure connections. Client devices must also trust the certificate to ensure successful communication. Once the certificate is in place, secure LDAP is enabled within the directory service configuration. Finally, the server is restarted to apply the changes, and firewall settings are updated to allow traffic on port 636. Each of these steps contributes to establishing a secure and reliable LDAP environment.
Firewall Configuration and Port Accessibility
Firewalls play a crucial role in controlling access to network services, including LDAP. Proper configuration ensures that only authorized traffic can reach the LDAP server. When enabling secure LDAP, administrators must verify that port 636 is open and accessible while restricting unnecessary access to port 389 if it is not required. This approach minimizes potential attack vectors and enhances overall network security. Careful firewall management is essential to maintaining both accessibility and protection.
Comparing Port 389 and Port 636 in Practical Use
The primary difference between port 389 and port 636 lies in the presence of encryption. Port 389 facilitates straightforward communication without additional processing overhead, making it suitable for low-risk environments. In contrast, port 636 prioritizes security by encrypting all transmitted data. While this introduces some computational overhead, the benefits of protecting sensitive information far outweigh the costs in most scenarios. Organizations must evaluate their specific needs to determine which port is appropriate, though secure communication is generally recommended.
Performance Considerations in Encrypted LDAP
Encryption introduces additional processing requirements, which can impact performance in high-demand environments. However, modern hardware and optimized encryption algorithms have significantly reduced this impact. In most cases, the performance difference between encrypted and unencrypted LDAP is negligible compared to the security benefits gained. Organizations should consider factors such as server capacity and network load when implementing secure LDAP, ensuring that performance remains acceptable while maintaining strong protection.
Use Cases for Unencrypted LDAP Communication
Despite its limitations, unencrypted LDAP communication still has valid use cases in certain परिस्थितियों. Internal networks with strict access controls and minimal exposure to external threats may use port 389 for efficiency. Additionally, some legacy systems may not support encrypted communication, requiring the continued use of unencrypted LDAP. In such cases, additional security measures, such as network segmentation and monitoring, should be implemented to mitigate risks.
Advantages of Using Secure LDAP in Modern Networks
Secure LDAP offers numerous advantages that make it the preferred choice for most organizations. By encrypting data in transit, it protects sensitive information from interception and unauthorized access. This is particularly important for authentication प्रक्रियाएँ, where credentials must remain confidential. Secure LDAP also helps organizations comply with regulatory requirements المتعلقة بحماية البيانات, ensuring that they meet industry standards for data security. These benefits make port 636 an essential component of modern network infrastructure.
Potential Challenges in Implementing Secure LDAP
While secure LDAP provides significant benefits, its implementation can present challenges. Configuring certificates, ensuring compatibility with existing systems, and managing encryption settings require careful planning and expertise. Misconfigurations can lead to connectivity issues or कमजोर सुरक्षा, highlighting the importance of thorough testing and validation. Organizations must allocate sufficient resources and training to ensure a successful deployment of secure LDAP.
Maintaining and Updating Encryption Standards
Encryption standards evolve over time as new vulnerabilities are discovered and addressed. Maintaining secure LDAP requires नियमित updates to encryption protocols and algorithms to ensure continued protection. Outdated encryption methods can become ineffective, leaving systems vulnerable to attack. Regular audits and updates are essential to keeping LDAP communication secure and aligned with current best practices. This ongoing maintenance is a critical aspect of effective directory service management.
Understanding the Broader Impact of LDAP Security
The security of LDAP communication extends beyond the directory service itself, influencing the overall امنیت posture of an organization. Because LDAP is often used for authentication and authorization, any compromise يمكن أن يؤثر على multiple systems and applications. Ensuring secure communication helps protect not only directory data but also the العديد من الخدمات التي تعتمد عليها. This interconnected nature underscores the importance of implementing strong security measures at every level of LDAP communication.
Security Risks Associated with Unencrypted LDAP Communication
Unencrypted LDAP communication over port 389 introduces a range of security risks that can significantly impact an organization’s network integrity. Because data is transmitted in clear text, it can be intercepted by anyone with access to the network traffic. Attackers often use packet sniffing tools to capture and analyze this data, allowing them to extract sensitive information such as usernames, passwords, and directory details. This type of vulnerability is especially dangerous in environments where authentication requests are frequent, as it increases the likelihood of exposing critical credentials. Once compromised, these credentials can be used to gain unauthorized access to systems and resources, potentially leading to broader security breaches.
Exposure of Sensitive Directory Information
Directory services often store highly sensitive information, including employee details, organizational structures, and access permissions. When this data is transmitted without encryption, it becomes vulnerable to interception. Attackers can use this information to map out the network, identify key افراد, and target specific systems or users. This level of insight can significantly enhance the effectiveness of subsequent attacks, such as phishing or social engineering campaigns. Protecting directory data during transmission is therefore essential to maintaining confidentiality and preventing unauthorized disclosure.
Man-in-the-Middle Attacks and Their Impact
One of the most significant threats to unencrypted LDAP communication is the risk of man-in-the-middle attacks. In such scenarios, an attacker intercepts the communication between the client and the server, potentially altering or capturing the data being exchanged. Without encryption, there is no mechanism to verify the integrity or authenticity of the data, making it easier for attackers to manipulate requests or responses. This can lead to unauthorized changes in directory data or the redirection of authentication requests to malicious systems. The consequences of such attacks can be severe, affecting both security and operational stability.
Credential Theft and Unauthorized Access
When credentials are transmitted in clear text, they become an easy target for attackers. Once obtained, these credentials can be used to access systems, escalate privileges, and move laterally within the network. This type of unauthorized access can go undetected for extended periods, allowing attackers to gather information, install malware, or disrupt العمليات. The risk of credential theft highlights the importance of encrypting authentication data to prevent interception and misuse.
Risks in Public and Shared Network Environments
Public and shared networks present additional challenges for unencrypted LDAP communication. In such environments, multiple users and devices share the same network infrastructure, increasing the likelihood of interception. Attackers can exploit weak security controls to capture data packets and analyze them for valuable information. This makes the use of port 389 particularly risky outside controlled internal networks. Encrypting LDAP traffic ensures that even if data is intercepted, it remains unreadable and protected from unauthorized access.
Advantages of Encrypted LDAP Communication
Using encrypted LDAP communication over port 636 provides a strong دفاع against many of the risks associated with unencrypted data transfer. Encryption ensures that data remains confidential and cannot be easily intercepted or understood by unauthorized parties. It also provides integrity, ensuring that data is not altered during transmission. Additionally, encryption supports authentication mechanisms that verify the identities of both the client and the server, establishing trust and preventing impersonation. These benefits make encrypted LDAP an essential component of secure network operations.
Common Vulnerabilities in Secure LDAP Implementations
While encrypted LDAP significantly improves security, it is not without potential vulnerabilities. Many of these issues arise from misconfigurations or ضعف in implementation rather than flaws in the protocol itself. For example, using outdated encryption algorithms or weak key lengths can reduce the effectiveness of encryption. Similarly, failing to properly configure certificates can lead to trust issues or expose the system to attacks. Regular audits and adherence to best practices are necessary to ensure that secure LDAP remains effective.
Certificate Expiration and Management Challenges
Digital certificates used in secure LDAP have a محدد lifespan and must be renewed before they expire. If a certificate expires, secure connections may fail, disrupting network operations. In some cases, expired certificates can also create security vulnerabilities if they are not properly replaced. Managing certificates involves tracking expiration dates, renewing certificates on time, and ensuring that all مرتبط systems trust the updated certificates. Effective certificate management is therefore critical to maintaining secure LDAP communication.
Encryption Key Protection and Risks
Encryption relies on the use of keys to encode and decode data. If these keys are compromised, the security of the entire system is at risk. Attackers who gain access to encryption keys can decrypt intercepted data, rendering encryption ineffective. Protecting keys involves storing them securely, limiting access, and regularly rotating them to reduce the risk of compromise. Key management is a fundamental aspect of maintaining the integrity of encrypted LDAP communication.
Potential Port Conflicts in LDAP Deployments
In complex network environments, multiple applications may attempt to use the same ports for communication, leading to conflicts. For LDAP, ports 389 and 636 must be carefully managed to ensure that services operate without interference. Port conflicts can result in failed connections, सेवा disruptions, and difficulty troubleshooting issues. Proper planning and configuration help prevent these conflicts, ensuring that LDAP services remain accessible and reliable.
Dynamic Ports and Their Role in Communication
While the destination ports for LDAP are typically fixed, client systems often use dynamic ports for initiating connections. These ports are assigned temporarily and can vary with each session. This approach allows multiple connections to occur simultaneously without conflict. Understanding the role of dynamic ports is important for configuring firewalls and network policies, as it ensures that legitimate traffic is allowed while unauthorized access is restricted.
Mitigating Conflicts Through Network Design
Effective network design plays a crucial role in جلوگیری of port conflicts and ensuring smooth LDAP operation. This includes segregating applications, documenting port usage, and implementing clear policies for network communication. By organizing network resources بشكل منظم, administrators can minimize the risk of conflicts and improve overall performance. Regular monitoring and testing also help identify potential issues before they impact operations.
Importance of Regular Security Audits
Regular security audits are essential for identifying vulnerabilities and ensuring that LDAP implementations remain secure. These audits involve reviewing configurations, testing for weaknesses, and verifying compliance with security standards. By conducting audits on a consistent basis, organizations can detect and address issues قبل they are exploited by attackers. This proactive approach helps maintain a strong security posture and reduces the likelihood of breaches.
Best Practices for Secure LDAP Deployment
Implementing secure LDAP effectively requires adherence to a set of best practices. These include using strong encryption algorithms, regularly updating software, and ensuring proper certificate management. Access controls should be محدود to authorized users, and monitoring systems should be in place to detect suspicious activity. Additionally, organizations should provide training to administrators to ensure they understand the complexities of LDAP security. اتباع these practices helps create a robust and reliable directory service environment.
Balancing Usability and Security in LDAP Systems
While security is a top priority, it must be balanced with usability to ensure that systems remain efficient and accessible. Overly complex security measures can lead to configuration errors or hinder productivity. Organizations باید strive to implement solutions that provide strong protection without compromising الأداء. This balance can be achieved through careful planning, user-friendly tools, and ongoing evaluation of system performance.
LDAP in Enterprise Identity and Access Management
LDAP plays a central role in modern identity and access management strategies by acting as a unified source of truth for user identities and permissions. Organizations rely on directory services built on LDAP to control who can access systems, applications, and data. This centralized approach simplifies administration by allowing policies to be applied consistently across the entire network. Instead of managing separate user databases for each application, LDAP enables a single directory to serve multiple systems, reducing duplication and minimizing the risk of inconsistencies. This integration improves both efficiency and security, as administrators can enforce uniform access controls and quickly respond to changes in user status.
How Directory Services Support Authentication Workflows
Authentication workflows depend heavily on LDAP to validate user credentials and establish trust between systems. When a user attempts to log in, their credentials are sent to a directory service, which verifies them against stored records. If the credentials match, access is granted; otherwise, the request is denied. This process occurs rapidly and is often invisible to the user, yet it is critical for maintaining secure access to resources. Directory services such as Microsoft Active Directory use LDAP as the underlying protocol to handle these authentication requests efficiently, ensuring that users can access the resources they need without unnecessary delays.
Authorization and Role-Based Access Control
Beyond authentication, LDAP also supports authorization by determining what actions a user is allowed to perform. This is often implemented through role-based access control, where permissions are assigned based on group membership or organizational roles. For example, employees in a finance department may have access to financial systems, while others do not. LDAP facilitates this by organizing users into groups and associating those groups with specific permissions. This structured approach simplifies الإدارة and ensures that access rights are aligned with organizational policies.
Single Sign-On and User Convenience
One of the most significant advantages of LDAP integration is its ability to support single sign-on solutions. With single sign-on, users can authenticate once and gain access to multiple applications without needing to log in repeatedly. This improves user experience and reduces the likelihood of password fatigue, which can lead to weak security practices. LDAP enables this functionality by acting as a central authentication authority, allowing مختلف applications to اعتماد on a single set of credentials. This not only enhances convenience but also strengthens security by reducing the number of credentials that must be managed.
LDAP Integration with Diverse Technologies
LDAP is widely used across a variety of technologies, making it a versatile component of network infrastructure. It integrates with applications such as email systems, collaboration tools, databases, and virtual private networks. These systems تعتمد on LDAP to retrieve user information and validate access requests. Open-source solutions like OpenLDAP provide flexibility for organizations that prefer customizable and cost-effective options, while enterprise platforms offer advanced features for large-scale deployments. This broad compatibility ensures that LDAP remains relevant across different environments and use cases.
Directory Services Beyond Traditional Environments
While LDAP is often associated with on-premises networks, it also plays a role in modern cloud and hybrid environments. Many cloud-based services integrate with LDAP directories to provide seamless authentication and user management. This allows organizations to extend their existing directory infrastructure into the cloud without significant تغييرات. By maintaining a consistent identity framework across environments, LDAP helps organizations manage access securely regardless of where resources are located.
Operational Considerations for LDAP Deployment
Deploying LDAP effectively requires careful planning and ongoing management. Administrators must design the directory structure to reflect organizational needs while ensuring scalability for future growth. This includes defining organizational units, naming conventions, and access policies. Proper planning helps prevent issues such as inefficient searches or overly complex hierarchies. Additionally, administrators must monitor performance and adjust configurations as needed to maintain optimal operation.
Monitoring and Troubleshooting LDAP Systems
Monitoring LDAP systems is essential for ensuring reliability and identifying potential issues. Սա includes tracking performance metrics, analyzing logs, and detecting unusual activity. Troubleshooting LDAP problems often involves بررسی connection issues, authentication failures, and configuration errors. By maintaining visibility into system performance, administrators can quickly resolve issues and minimize disruptions to users. Effective monitoring alsoساهم in identifying security threats, allowing organizations to respond proactively.
Impact of LDAP on Organizational Security Posture
LDAP has a direct impact on an organization’s overall security posture because it is deeply integrated with authentication and access control processes. A well-configured LDAP system enhances security by enforcing strong authentication mechanisms and protecting sensitive data. Conversely, misconfigurations or ضعف in LDAP implementation can create vulnerabilities that attackers may exploit. Ensuring that LDAP communication is encrypted, access controls are properly defined, and systems are regularly updated is essential for maintaining a मजबूत security environment.
Future Trends in LDAP and Directory Services
As technology continues to evolve, LDAP remains a relevant and adaptable protocol. Emerging trends such as zero-trust security models and increased reliance on cloud सेवाएँ are influencing how directory services are used. LDAP is being integrated with modern authentication methods, including multi-factor authentication, to provide stronger protection against unauthorized access. These developments demonstrate LDAP’s ability to adapt to changing security requirements while maintaining its core functionality as a directory access protocol.
Best Practices for Long-Term LDAP Management
Maintaining an effective LDAP environment requires adherence to best practices over the long term. This includes नियमित updates to software and encryption standards, consistent monitoring of system performance, and thorough documentation of configurations. Administrators should also implement backup and recovery strategies to protect against data loss. Training and awareness are equally important, ensuring that those responsible for managing LDAP understand its complexities and potential risks. By following these practices, organizations can ensure that their directory services remain reliable and secure.
Strategic Importance of Choosing the Right LDAP Configuration
Selecting the appropriate LDAP configuration, including the choice between ports 389 and 636, is a strategic decision that affects both performance and security. While unencrypted communication may offer simplicity and reduced overhead, it is generally unsuitable for environments where sensitive data is involved. Encrypted communication, though slightly more resource-intensive, provides the protection اللازمة for modern networks. Organizations must evaluate their specific requirements and जोखिम tolerance when making this decision, ensuring that their LDAP implementation aligns with their overall security strategy.
Conclusion
LDAP serves as a critical component in modern networking by providing a structured and efficient way to manage directory information. Understanding the differences between port 389 and port 636 is essential for making informed decisions about security and performance. Port 389 enables straightforward communication but lacks encryption, making it suitable only for low-risk scenarios. In contrast, port 636 provides secure, encrypted communication that protects sensitive data and supports modern security requirements. By implementing best practices, maintaining strong encryption, and carefully managing directory services, organizations can leverage LDAP effectively while minimizing risks.