The internet relies on a structured communication system that allows devices to exchange information efficiently across vast distances. At the core of this system are ports, which function as logical gateways enabling data to flow between clients and servers. Among the many available ports, port 80 and port 443 are the most widely used because they handle the majority of web traffic that users interact with every day. While both ports serve the same general purpose of enabling access to websites, they differ significantly in how they process and protect data during transmission.
Port 80 is associated with HTTP, a protocol that delivers content in plain text without any built-in encryption. This means that the data traveling through this port is exposed and can potentially be intercepted by malicious actors. In contrast, port 443 is linked with HTTPS, which enhances HTTP by adding encryption, making data far more secure as it moves across networks. This distinction has become increasingly important as cybersecurity threats continue to grow and as users demand safer online experiences.
Every time a user opens a website, submits a form, or interacts with an online service, these ports are at work behind the scenes. Even though most users are unaware of them, their role is critical in determining whether that interaction is secure or vulnerable. Understanding how these ports function provides valuable insight into the mechanics of the internet and highlights why secure communication has become the standard in modern networking.
What is Port 80 and How It Works in Web Browsing
Port 80 has historically been the default port for web communication. It is primarily used by HTTP to facilitate the transfer of web pages from servers to users’ browsers. When a user types a web address into a browser without specifying a port, the system automatically connects through port 80 unless directed otherwise.
The communication process begins with a request sent from the browser to the server. This request typically asks for a specific webpage or resource. Once the server receives the request, it responds by sending back the required data, which includes HTML for structure, CSS for styling, and JavaScript for functionality. The browser then interprets this data and displays the webpage to the user.
Port 80 operates at the application layer of networking, which means it directly interacts with user-facing applications. However, it relies on underlying protocols to ensure that data is transmitted correctly and efficiently. This layered structure allows for smooth communication across networks, enabling millions of users to access web content simultaneously without noticeable delays.
Despite its importance in the early days of the internet, port 80 has become less dominant due to its lack of security. As online threats have increased, the need for encrypted communication has led to the widespread adoption of more secure alternatives. Even so, port 80 remains relevant in certain scenarios, particularly in development environments and internal systems.
The Importance of Port 80 in the Evolution of the Internet
Port 80 played a foundational role in shaping the modern internet. In its early stages, the internet was primarily focused on sharing information quickly and efficiently rather than securing it. HTTP over port 80 made it possible for users to access websites easily, contributing to the rapid growth of online content and services.
As more websites emerged, port 80 became the standard entry point for web traffic. It enabled seamless communication between browsers and servers, making it easier for developers to create and deploy web applications. This simplicity was a key factor in the widespread adoption of the internet, as it lowered the barrier to entry for both users and content creators.
However, as the internet evolved, so did the nature of the data being transmitted. What began as simple text and images expanded to include sensitive information such as login credentials, financial data, and personal details. This shift exposed the limitations of port 80, as its lack of encryption made it unsuitable for handling such data securely.
The growing awareness of these risks led to the development of more secure protocols, eventually resulting in the rise of HTTPS and port 443. While port 80 remains an important part of internet history, its role has shifted as security has become a top priority in web communication.
TCP and the Reliability of Port 80 Communication
Port 80 relies on the Transmission Control Protocol to ensure reliable data transfer between clients and servers. TCP is designed to provide a stable and consistent communication channel, ensuring that data is delivered accurately and in the correct order. This reliability is essential for web browsing, where incomplete or corrupted data can lead to broken pages or poor user experiences.
The process begins with the establishment of a connection through a three-step handshake. First, the client sends a request to initiate communication. The server responds by acknowledging the request and signaling that it is ready to proceed. Finally, the client confirms this acknowledgment, completing the handshake and allowing data transfer to begin.
Once the connection is established, TCP manages the flow of data, ensuring that each packet reaches its destination. If any packet is lost or arrives out of order, TCP detects the issue and retransmits the necessary data. This mechanism guarantees that the information received by the user is complete and accurate.
While TCP provides a strong foundation for reliable communication, it does not address the issue of security. Data transmitted through port 80 using HTTP remains unencrypted, meaning that it can be intercepted and read by unauthorized parties. This limitation highlights the need for additional security measures in modern web communication.
Why Port 80 is Not Encrypted and What It Means
One of the defining characteristics of port 80 is its lack of encryption. This means that any data sent through this port is transmitted in plain text, making it accessible to anyone who intercepts the communication. This vulnerability is a major concern, especially when dealing with sensitive information.
It is important to understand that ports themselves do not provide security. Instead, security is implemented through the protocols that operate over these ports. In the case of port 80, the default protocol does not include encryption, leaving data exposed during transit.
This lack of protection opens the door to various types of cyberattacks. For example, attackers can monitor network traffic to capture sensitive information such as usernames and passwords. They can also modify the data being transmitted, injecting malicious content or altering the information before it reaches its destination.
Because of these risks, the use of port 80 for public-facing websites has become increasingly discouraged. Modern best practices emphasize the importance of using secure protocols to protect data and maintain user trust. As a result, many organizations have transitioned to more secure alternatives for handling web traffic.
Common Uses of Port 80 in Modern Environments
Despite its security limitations, port 80 continues to be used in certain contexts where encryption is not a primary concern. One of the most common uses is in development and testing environments, where developers need a simple and efficient way to build and debug web applications. By using HTTP, they can focus on functionality without dealing with the complexities of encryption.
Another important use of port 80 is in load balancing. In this scenario, incoming traffic is received on port 80 and then distributed across multiple servers. This helps ensure that no single server becomes overwhelmed, improving performance and reliability for users.
Port 80 is also frequently used for redirecting traffic to secure connections. When a user attempts to access a website using an unsecured connection, the server can automatically redirect the request to a secure version on port 443. This ensures that users ultimately interact with the site through an encrypted channel, even if their initial request was not secure.
While these use cases highlight the continued relevance of port 80, it is important to recognize that it is no longer suitable as the primary means of serving web content. The emphasis on security in modern networking has shifted the focus toward encrypted communication.
The Shift from Port 80 to More Secure Alternatives
As the internet has matured, the need for secure communication has become increasingly important. This has led to a gradual shift away from port 80 toward more secure options such as port 443. This transition reflects a broader change in priorities, with security now being a fundamental requirement rather than an optional feature.
Users today expect their data to be protected when they browse the web, and organizations are under increasing pressure to meet these expectations. This has resulted in widespread adoption of secure protocols, with many websites enforcing encrypted connections by default.
In many cases, port 80 is still used as an entry point, but only to redirect users to a secure connection. This approach maintains compatibility while ensuring that sensitive data is transmitted safely. It also helps organizations comply with modern security standards and best practices.
Understanding this shift provides valuable insight into the evolution of the internet. It highlights the importance of adapting to changing threats and underscores the role of secure communication in maintaining trust and reliability in the digital world.
Introduction to Port 443 and Secure Web Communication
Port 443 represents a major advancement in how data is transmitted across the internet, primarily because it introduces security into a system that was originally built for openness rather than protection. While port 80 enabled the rapid expansion of the web, it did so without considering the risks associated with unencrypted communication. Port 443 addresses these concerns by supporting HTTPS, which ensures that information exchanged between users and servers is protected from unauthorized access.
This port has become the standard for secure web browsing, and most modern websites rely on it to safeguard user data. Whether someone is logging into an account, making an online purchase, or simply browsing content, port 443 ensures that the communication remains private. This is achieved through encryption, which transforms readable data into an unreadable format that can only be decoded by the intended recipient.
The adoption of port 443 has been driven by the increasing need for privacy and security in a digital world where data breaches and cyberattacks are common. It is now considered a best practice for websites to use secure connections, and many browsers actively warn users when they attempt to access unsecured sites. As a result, port 443 has become an essential component of modern web infrastructure.
What HTTPS Means and How It Works Over Port 443
HTTPS stands for HyperText Transfer Protocol Secure, and it is essentially an enhanced version of HTTP that incorporates encryption. While HTTP focuses on transferring data between a client and a server, HTTPS adds a layer of protection that ensures the data cannot be easily intercepted or altered during transit.
When a user connects to a website using HTTPS, the browser and server establish a secure connection before any data is exchanged. This process involves verifying the server’s identity and agreeing on encryption methods that will be used throughout the session. Once the connection is established, all data transmitted between the two parties is encrypted, making it unreadable to anyone who might intercept it.
This secure communication is made possible by cryptographic protocols that operate alongside HTTPS. These protocols handle tasks such as key exchange, data encryption, and integrity verification, ensuring that the information remains confidential and unchanged. The result is a browsing experience that is not only functional but also secure, providing users with confidence that their data is protected.
Understanding Encryption in HTTPS Communication
Encryption is the cornerstone of HTTPS and the primary reason why port 443 is considered secure. At its core, encryption involves converting readable data into a coded format that can only be decoded with the correct key. This ensures that even if the data is intercepted, it cannot be understood without the appropriate decryption mechanism.
When a secure session is initiated, the client and server exchange cryptographic keys that are used to encrypt and decrypt data. This process typically involves a combination of asymmetric and symmetric encryption techniques. Asymmetric encryption uses a pair of keys—a public key and a private key—to establish a secure connection. Once the connection is established, symmetric encryption is used to handle the actual data transfer, as it is faster and more efficient.
This layered approach provides both security and performance. The initial key exchange ensures that only the intended parties can access the data, while the use of symmetric encryption allows for rapid communication without compromising protection. As a result, HTTPS is able to deliver both security and speed, making it suitable for a wide range of online activities.
The Role of Public and Private Keys in Security
A key aspect of HTTPS encryption is the use of public and private keys. These keys work together to create a secure communication channel between the client and the server. The public key is shared openly and is used to encrypt data, while the private key is kept secret and is used to decrypt that data.
When a user connects to a secure website, the server provides its public key as part of its digital certificate. The browser uses this key to encrypt information that is sent to the server. Because only the server has the corresponding private key, it is the only entity capable of decrypting the data.
This system ensures that even if the encrypted data is intercepted, it cannot be read without access to the private key. It also allows the browser to verify the authenticity of the server, ensuring that the user is communicating with the intended website and not an imposter. This combination of confidentiality and authentication is what makes HTTPS a reliable choice for secure communication.
What is an HTTPS Certificate and Why It Matters
An HTTPS certificate, often referred to as a digital certificate, plays a crucial role in establishing trust between a user and a website. This certificate is issued by a trusted authority and contains information about the website, including its public key. It serves as proof that the website is legitimate and that it can be trusted to handle data securely.
When a user visits a secure website, the browser checks the certificate to ensure that it is valid and has been issued by a recognized authority. If the certificate is valid, the browser proceeds with establishing a secure connection. If not, the user may receive a warning indicating that the site may not be safe.
Certificates have a limited lifespan and must be renewed periodically to remain valid. Failure to renew a certificate can result in security warnings, which can deter users from accessing the site. This makes proper certificate management an essential part of maintaining a secure web presence.
In addition to verifying identity, certificates also facilitate the encryption process by providing the public key needed for secure communication. Without a valid certificate, it would be difficult to establish a trusted and encrypted connection between the client and the server.
TLS and Its Role in Securing Port 443 Communication
Transport Layer Security, commonly known as TLS, is the protocol responsible for securing data transmitted over port 443. It is the successor to older security protocols and is designed to provide confidentiality, integrity, and authenticity in digital communication.
TLS operates by establishing a secure session between the client and the server. During this process, both parties agree on encryption methods and generate session keys that will be used to protect the data. These session keys are unique to each connection, ensuring that even if one session is compromised, others remain secure.
One of the key features of TLS is its ability to verify the integrity of data. This means that it can detect if any data has been altered during transmission. If a discrepancy is found, the connection can be terminated to prevent further communication. This ensures that users receive accurate and unmodified information.
TLS also supports authentication, allowing the client to verify the identity of the server. This helps prevent attacks where malicious actors attempt to impersonate legitimate websites. By combining encryption, integrity checks, and authentication, TLS provides a comprehensive security framework for web communication.
Why Port 443 is the Standard for Secure Web Traffic
Port 443 has become the default choice for secure web communication due to its association with HTTPS and its widespread support across browsers and network devices. This standardization makes it easier for developers, administrators, and users to implement and recognize secure connections.
Firewalls and network security systems are typically configured to allow traffic through port 443, as it is widely recognized as the port for secure communication. This ensures that encrypted traffic can pass through networks without unnecessary restrictions, enabling seamless access to secure websites.
Using a standard port also simplifies the configuration of web servers and applications. Instead of specifying custom ports for secure communication, developers can rely on port 443, knowing that it will be supported by default. This consistency has contributed to the widespread adoption of HTTPS and has made secure browsing the norm rather than the exception.
In addition, search engines and browsers often prioritize secure websites, further reinforcing the importance of port 443. Websites that use secure connections are more likely to gain user trust and achieve better visibility, making port 443 an essential component of modern web strategy.
Flexibility of HTTPS Beyond Port 443
While port 443 is the standard for HTTPS, it is not the only port that can be used for secure communication. In theory, HTTPS can operate on any port, as long as both the client and server are configured to use it. However, using non-standard ports can lead to compatibility issues and may result in blocked connections due to firewall restrictions.
Most network systems are designed with the expectation that HTTPS traffic will use port 443. If a different port is used, it may not be recognized as secure traffic, leading to potential disruptions. This is why port 443 remains the preferred choice for implementing HTTPS, as it ensures compatibility and reliability across different environments.
Despite this flexibility, there are certain scenarios where alternative ports may be used, such as in testing environments or specialized applications. In these cases, additional configuration is required to ensure that the connection remains secure and accessible.
Understanding the relationship between HTTPS and port 443 helps clarify why this port has become the standard for secure communication. It highlights the importance of consistency and compatibility in maintaining a reliable and secure internet experience.
Direct Comparison Between Port 80 and Port 443
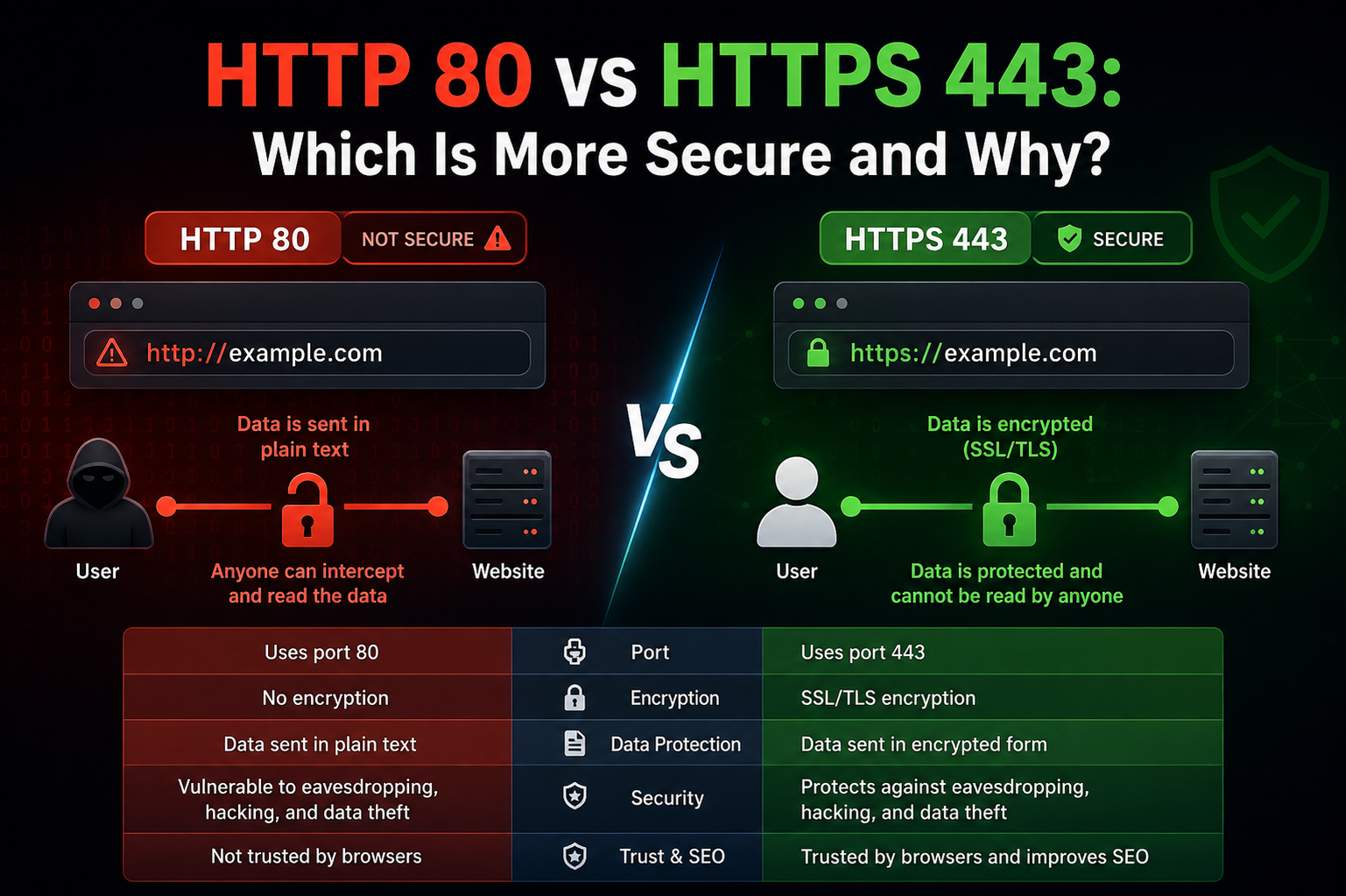
Port 80 and port 443 are often discussed together because they serve the same fundamental purpose of enabling communication between a client and a web server. However, the way they handle that communication sets them apart in a significant way. Both ports allow users to access websites, retrieve content, and interact with online services, but the level of security involved in each process is entirely different.
Port 80 operates using HTTP, which sends data in plain text without any form of encryption. This means that while the communication is functional and reliable, it is not protected. Port 443, on the other hand, uses HTTPS, which encrypts data before it is transmitted. This ensures that even if the data is intercepted, it cannot be easily understood or altered.
Another key difference lies in user trust and perception. Modern browsers often label HTTP connections as not secure, which can discourage users from interacting with such websites. HTTPS connections, associated with port 443, are typically marked with visual indicators that signal safety, encouraging users to proceed with confidence. This difference has had a major impact on how websites are designed and maintained today.
Key Functional Differences in Data Transmission
Although both ports enable the transfer of web content, the methods they use differ in important ways. Port 80 focuses on simplicity and speed, allowing data to be transmitted quickly without additional processing. This makes it efficient for basic communication but leaves it vulnerable to interception.
Port 443 introduces additional steps in the communication process to ensure security. Before any data is exchanged, a secure connection must be established through encryption protocols. This process may add a slight overhead in terms of time and resources, but it significantly enhances the safety of the data being transmitted.
The structure of the data itself also differs. In HTTP communication, the data is readable as it travels across the network. In HTTPS communication, the data is transformed into an encrypted format that cannot be interpreted without the correct decryption keys. This transformation is what provides the added layer of protection.
These functional differences highlight the trade-off between simplicity and security. While port 80 offers a straightforward approach to communication, port 443 provides a more robust solution that addresses the risks associated with modern internet usage.
Protocols Used by Port 80 and Port 443
The protocols associated with each port play a major role in defining their behavior. Port 80 relies on HTTP, which is built on top of a reliable transport mechanism. This protocol is designed for efficiency and ease of use, making it suitable for delivering web content quickly.
Port 443 uses HTTPS, which incorporates additional security protocols to protect data. These protocols handle tasks such as encryption, authentication, and data integrity verification. By combining these features, HTTPS ensures that communication remains private and secure.
Another important distinction is how these protocols interact with underlying systems. HTTP operates directly over a reliable transport layer, focusing primarily on delivering content. HTTPS, however, introduces an additional layer that manages encryption and security before the data is transmitted.
This layered approach makes HTTPS more complex but also far more secure. It allows for advanced features such as certificate validation and secure key exchange, which are essential for protecting sensitive information in today’s digital environment.
Are Port 80 and Port 443 Essentially the Same
At a fundamental level, port 80 and port 443 are similar in that they both enable web communication. They act as channels through which data flows between a client and a server, allowing users to access websites and interact with online services. In this sense, they serve the same core function.
However, the similarities largely end there. The way each port handles data is what truly differentiates them. Port 80 focuses on accessibility and simplicity, while port 443 emphasizes security and protection. This difference has become increasingly important as the internet has evolved.
A useful way to think about this comparison is to consider both ports as pathways. While both lead to the same destination, one is open and exposed, and the other is protected and monitored. The choice between them depends on the level of security required for the data being transmitted.
In modern web usage, the preference is clearly toward secure communication. While port 80 may still be used in certain scenarios, port 443 has become the standard for most online interactions, reflecting the growing importance of data protection.
Security Vulnerabilities Associated with Port 80
Port 80 is inherently vulnerable due to its lack of encryption. Because data is transmitted in plain text, it can be easily intercepted by anyone with access to the network. This makes it a target for various types of cyberattacks, especially in environments where sensitive information is being exchanged.
One common vulnerability is data interception, where attackers capture network traffic and extract valuable information such as login credentials or personal details. Another risk is data manipulation, where attackers alter the content being transmitted, potentially injecting malicious code or misleading information.
Port 80 is also susceptible to attacks that exploit its openness, such as content injection. In this scenario, attackers insert unauthorized content into a webpage, which can then be displayed to the user without their knowledge. This can lead to further security issues, including the spread of malware.
These vulnerabilities highlight the limitations of using port 80 in modern web environments. While it may still be suitable for certain non-sensitive applications, it is not recommended for handling any form of confidential data.
Security Considerations and Risks in Port 443 Usage
While port 443 provides a much higher level of security compared to port 80, it is not completely immune to risks. The effectiveness of HTTPS depends on proper implementation and maintenance. If these aspects are neglected, vulnerabilities can still arise.
One potential issue is the use of expired or invalid certificates. When a certificate is no longer valid, it can undermine the trust between the user and the website, making it easier for attackers to intercept data. Regular renewal and management of certificates are essential to maintaining a secure connection.
Another risk involves attempts to downgrade a secure connection to an insecure one. In such cases, attackers try to force communication to revert to HTTP, where it can be more easily intercepted. Proper configuration and enforcement of secure connections can help mitigate this risk.
There are also scenarios where attackers position themselves between the client and the server to intercept communication. While HTTPS makes this significantly more difficult, it is still possible if security measures are not properly implemented. This emphasizes the importance of vigilance and proper configuration when using secure protocols.
Comparing Performance and Efficiency Between the Two Ports
Performance is another area where port 80 and port 443 differ. Port 80, with its lack of encryption, generally requires fewer resources to process data. This can result in slightly faster communication, especially in environments where speed is prioritized over security.
Port 443, by contrast, involves additional processing to handle encryption and decryption. This can introduce a small amount of latency, particularly during the initial connection setup. However, advancements in technology have significantly reduced this impact, making the performance difference negligible in most cases.
Modern systems are designed to handle encrypted communication efficiently, and the benefits of security far outweigh the minor performance costs. In fact, many optimization techniques have been developed specifically for secure communication, allowing HTTPS to perform at a level comparable to HTTP.
As a result, performance is no longer a major barrier to adopting secure communication. The focus has shifted toward ensuring that data is protected without compromising the user experience, making port 443 the preferred choice in most scenarios.
Why Modern Web Standards Favor Port 443 Over Port 80
The shift toward port 443 is driven by the need to protect user data and maintain trust in online interactions. As cyber threats have become more sophisticated, the limitations of unencrypted communication have become increasingly apparent. This has led to a widespread adoption of secure protocols across the web.
Browsers now actively encourage the use of HTTPS by displaying warnings for unsecured sites and highlighting secure connections. Search engines also prioritize secure websites, making them more visible to users. These factors have created strong incentives for website owners to adopt port 443.
In addition, regulatory requirements and industry standards often mandate the use of secure communication for handling sensitive data. This includes information such as personal details, financial transactions, and authentication credentials. Using port 443 helps organizations meet these requirements and protect their users.
The preference for secure communication reflects a broader trend toward prioritizing privacy and security in the digital world. As a result, port 443 has become the default choice for modern web development, while port 80 is increasingly limited to specific use cases.
Understanding Security Vulnerabilities in Modern Web Communication
In the current digital environment, security is no longer optional but a necessity. Both port 80 and port 443 play a role in web communication, yet their exposure to vulnerabilities differs significantly. Understanding these vulnerabilities is essential for anyone working with networks, developing web applications, or managing online platforms. While port 80 is inherently insecure due to its lack of encryption, port 443 is designed to provide protection but still requires proper configuration and maintenance to remain effective.
Security vulnerabilities can arise from multiple sources, including outdated systems, improper configurations, and human error. Even the most secure protocols can become weak if not implemented correctly. This is why a deep understanding of how these ports operate—and where their weaknesses lie—is crucial for maintaining a secure digital environment. As cyber threats continue to evolve, awareness of these risks becomes a key factor in preventing data breaches and ensuring safe communication.
Common HTTPS Vulnerabilities and Misconfigurations
Although HTTPS operating on port 443 provides strong encryption, it is not completely immune to vulnerabilities. One of the most common issues arises from expired or invalid certificates. When a certificate expires, browsers can no longer verify the authenticity of the server, which may result in warnings or blocked access. This not only affects user trust but also creates an opportunity for attackers to exploit the weakened validation process.
Another potential vulnerability is improper certificate configuration. If certificates are not correctly installed or if weak encryption standards are used, the security provided by HTTPS can be compromised. This highlights the importance of using up-to-date cryptographic practices and ensuring that all configurations follow modern security guidelines.
There are also risks associated with improper implementation of secure connections. For example, if a website allows both secure and insecure versions without enforcing strict rules, attackers may attempt to exploit this flexibility. Proper configuration ensures that all traffic is directed through secure channels, minimizing the risk of exposure.
These vulnerabilities demonstrate that while HTTPS is a powerful tool for securing communication, it requires ongoing attention and management to remain effective.
The Risk of Downgrade Attacks and SSL Stripping
One of the more sophisticated threats targeting secure communication is the downgrade attack, often referred to as SSL stripping. In this type of attack, a malicious actor intercepts the connection between the client and the server and attempts to force it from a secure HTTPS connection to an insecure HTTP connection.
When this happens, the user may unknowingly continue browsing under the assumption that the connection is secure, while in reality, their data is being transmitted in plain text. This allows the attacker to capture sensitive information such as login credentials or personal details without detection.
Preventing such attacks requires strict enforcement of secure connections. Techniques such as forcing HTTPS for all requests and implementing security policies at the browser level can help mitigate this risk. These measures ensure that even if an attacker attempts to downgrade the connection, the browser will refuse to proceed with an insecure version.
This type of vulnerability highlights the importance of not only using secure protocols but also ensuring that they are enforced consistently across all interactions.
Man-in-the-Middle Attacks and Data Interception
Another significant threat in web communication is the man-in-the-middle attack. In this scenario, an attacker positions themselves between the client and the server, intercepting and potentially altering the data being exchanged. While HTTPS greatly reduces the likelihood of such attacks, it does not eliminate them entirely.
If an attacker is able to compromise a certificate or trick a user into trusting a malicious source, they may be able to intercept encrypted communication. Although the data remains encrypted, the attacker can still attempt to manipulate the session or redirect the user to a fraudulent site.
Proper certificate validation and user awareness are key factors in preventing these attacks. Browsers play a critical role by warning users when a certificate cannot be verified. Users should pay attention to these warnings and avoid proceeding with connections that appear suspicious.
This type of attack underscores the importance of trust in digital communication. Even with strong encryption, the integrity of the connection depends on verifying that both parties are legitimate.
Insecure Redirects and Configuration Weaknesses
Redirecting traffic from port 80 to port 443 is a common practice used to ensure that users access websites through secure connections. However, if this process is not implemented correctly, it can introduce vulnerabilities. Insecure redirects occur when the transition from an unsecured connection to a secured one is not properly enforced.
For example, if a website allows initial communication over HTTP without immediately redirecting to HTTPS, there is a window of opportunity for attackers to intercept the data. Even a brief exposure can be enough to compromise sensitive information.
To address this issue, websites must implement strict redirect policies that ensure all traffic is automatically directed to secure connections. This includes configuring servers to reject insecure requests and using mechanisms that instruct browsers to always use HTTPS when connecting to a particular site.
These measures help eliminate the gaps that attackers can exploit, ensuring that all communication remains protected from the moment it begins.
HTTP Vulnerabilities and Their Impact on Data Security
Port 80, due to its reliance on HTTP, is inherently vulnerable to a wide range of security threats. One of the most significant risks is data interception. Because the data is transmitted in plain text, it can be easily captured and read by anyone monitoring the network.
Another major concern is data tampering. Attackers can modify the information being transmitted, altering its content before it reaches the intended recipient. This can lead to the injection of malicious code, which may compromise the user’s system or steal sensitive information.
HTTP is also susceptible to various forms of injection attacks, where attackers exploit vulnerabilities in web applications to execute unauthorized commands. Without encryption and proper validation, these attacks become much easier to carry out.
These vulnerabilities make HTTP unsuitable for handling any form of sensitive data. While it may still be used in controlled environments or for non-critical applications, it is not recommended for public-facing services where security is a priority.
Risks Associated with Public Networks and Unsecured Connections
Using port 80 over public networks significantly increases the risk of data exposure. Public networks, such as those found in cafes, airports, and other shared spaces, are often less secure and more susceptible to monitoring by malicious actors.
When users connect to these networks and access websites through HTTP, their data can be easily intercepted. This includes not only the content of the websites they visit but also any information they submit, such as login credentials or personal details.
Even with HTTPS, users must remain cautious when using public networks. While encryption provides a strong layer of protection, attackers may still attempt to exploit other vulnerabilities, such as weak network configurations or compromised devices.
Practicing safe browsing habits and avoiding the use of unsecured connections in public environments can significantly reduce these risks. This highlights the importance of combining secure protocols with user awareness to achieve comprehensive protection.
Is HTTPS Completely Secure in Real-World Scenarios
HTTPS is widely regarded as a secure method of communication, but it is important to understand that no system is completely immune to risk. While HTTPS provides strong encryption and authentication, its effectiveness depends on proper implementation and ongoing maintenance.
Human error is one of the most common factors that can compromise security. Misconfigured servers, outdated certificates, and weak encryption settings can all reduce the effectiveness of HTTPS. Regular updates and adherence to best practices are essential for maintaining a secure environment.
There is also the possibility of new vulnerabilities being discovered over time. As technology evolves, so do the methods used by attackers. This makes it important to stay informed about emerging threats and to update security measures accordingly.
Despite these challenges, HTTPS remains one of the most effective tools for protecting data in transit. When properly implemented, it provides a high level of security that is suitable for most online activities.
The Ongoing Importance of Secure Web Practices
The comparison between port 80 and port 443 ultimately highlights the importance of adopting secure practices in web communication. While port 80 played a significant role in the development of the internet, its limitations have made it less suitable for modern use. Port 443, with its support for encrypted communication, has become the standard for protecting data and ensuring user trust.
Maintaining security requires more than just choosing the right port. It involves proper configuration, regular updates, and continuous monitoring to identify and address potential vulnerabilities. Organizations must remain proactive in their approach to security, ensuring that their systems are prepared to להתמודד emerging threats.
For users, understanding the basics of secure communication can lead to safer browsing habits. Recognizing the importance of encrypted connections and being aware of potential risks can help reduce the likelihood of falling victim to cyberattacks.
As the digital landscape continues to evolve, the emphasis on security will only grow stronger. The role of ports and protocols in enabling safe communication will remain a critical aspect of how the internet functions, shaping the future of online interactions.
Final Thoughts
The comparison between port 80 and port 443 highlights how the internet has evolved from a system focused primarily on accessibility to one that prioritizes security and trust. Both ports serve the same fundamental purpose of enabling communication between users and web servers, but the way they handle data sets them apart in a meaningful way. Port 80, associated with HTTP, represents the earlier stage of the web where simplicity and speed were the main priorities. Port 443, linked with HTTPS, reflects the modern need for protecting data in an environment where cyber threats are increasingly common.
Over time, the limitations of unencrypted communication have become clear. As more sensitive information began to flow through the internet, the risks associated with plain text transmission could no longer be ignored. This led to the widespread adoption of encryption, making port 443 the preferred choice for most web interactions today. Secure communication is no longer considered an optional feature but a fundamental requirement for maintaining privacy and user confidence.
Another important takeaway is that security is not achieved solely by choosing the right port or protocol. Proper implementation, regular maintenance, and awareness of potential vulnerabilities all play a crucial role in ensuring that communication remains safe. Even the most advanced encryption methods can be undermined by misconfiguration or neglect, which makes ongoing attention to security practices essential.
The shift from port 80 to port 443 also reflects broader changes in user expectations and industry standards. Modern browsers, search engines, and regulatory frameworks all encourage or enforce the use of secure connections. This has created a digital environment where encryption is the norm, and unsecured communication is gradually being phased out.
Understanding the difference between these two ports provides valuable insight into how the internet works and why security matters. It helps developers build better applications, enables organizations to protect their users, and allows individuals to make safer choices when browsing online.