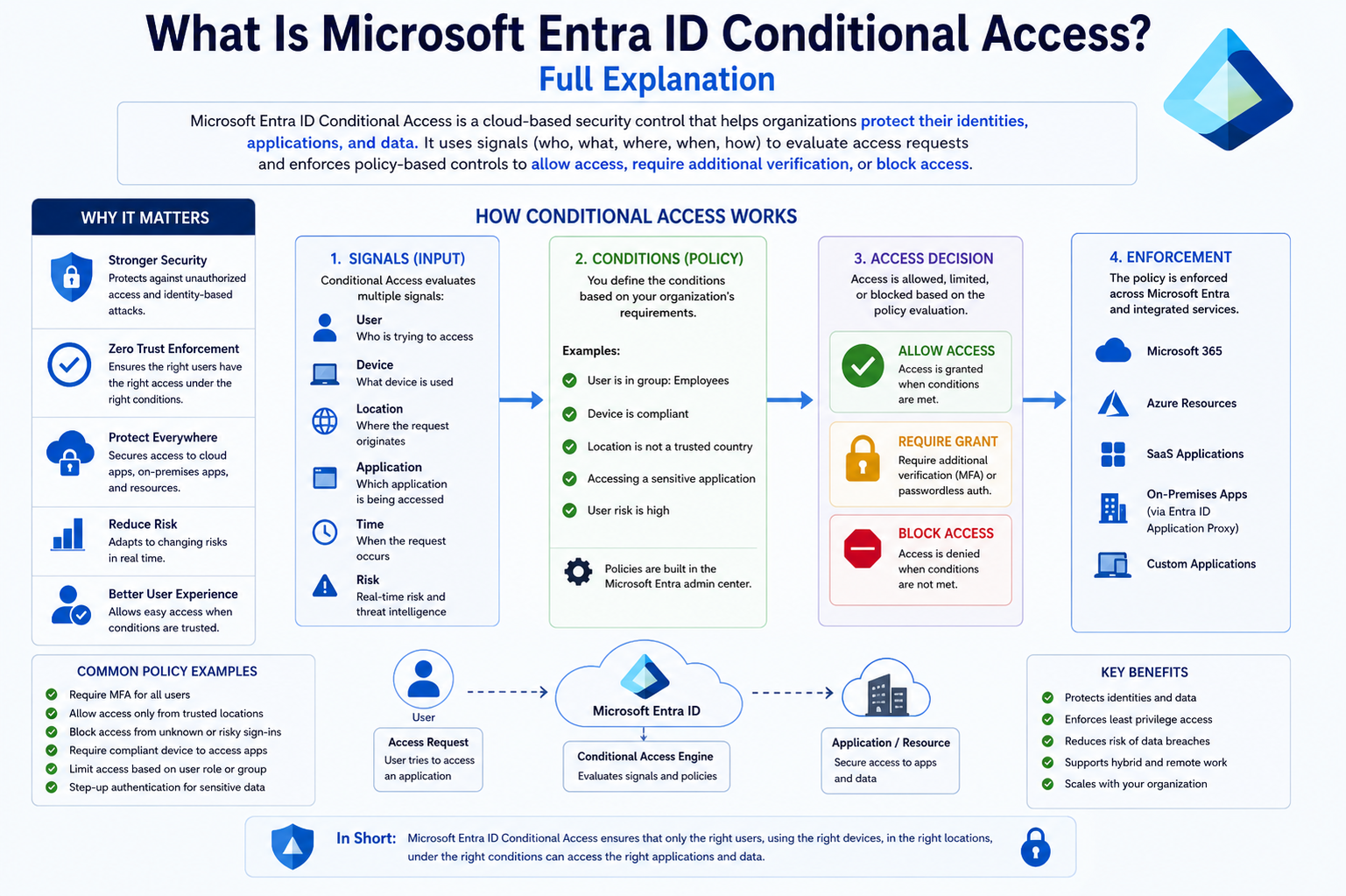
Microsoft Entra ID Conditional Access is a modern security capability designed to control how users access applications and data in a highly dynamic and intelligent way. In today’s digital environment, organizations no longer operate within clearly defined network boundaries. Employees work remotely, partners collaborate from different regions, and devices connect from a variety of networks. This shift has created a strong need for adaptive security mechanisms that go beyond traditional perimeter-based defenses. Conditional Access addresses this need by acting as a decision-making engine that evaluates access requests in real time and determines whether access should be granted, denied, or conditioned on additional requirements.
The concept behind Conditional Access revolves around ensuring that access decisions are not static but instead based on multiple contextual factors. Rather than relying solely on usernames and passwords, it evaluates signals such as user identity, device status, geographic location, and potential risk indicators. By doing so, it enables organizations to implement a more intelligent and flexible approach to security. This ensures that users can access resources seamlessly when conditions are safe, while additional safeguards are applied when risks are detected.
The Growing Need for Adaptive Access Control
Modern workplaces are no longer limited to office environments where users connect through secured internal networks. The widespread adoption of cloud services and mobile devices has significantly expanded the attack surface for organizations. Cyber threats have also evolved, becoming more sophisticated and targeted. Attackers often exploit weak authentication mechanisms, compromised credentials, or unmanaged devices to gain unauthorized access.
In such an environment, static security policies are insufficient. Organizations require systems that can continuously evaluate the context of access requests and respond accordingly. Conditional Access fulfills this requirement by introducing adaptive access control. It ensures that authentication and authorization processes are tailored to each specific scenario rather than applied uniformly across all users and situations.
For example, a user logging in from a trusted corporate device within a secure network may be granted access without interruption. However, the same user attempting to access sensitive data from an unfamiliar device or location may be required to complete additional verification steps. This dynamic approach enhances security without unnecessarily hindering productivity.
Understanding the Core Concept of Conditional Access
At its core, Conditional Access is a policy-driven framework that determines how access decisions are made. These policies define the conditions under which users are allowed to access resources and the actions that should be taken when those conditions are met or not met. The system evaluates every sign-in attempt against these policies, ensuring that access is granted only when predefined criteria are satisfied.
This approach transforms access control into a continuous process rather than a one-time verification. Each login attempt is treated as a unique event that must be assessed in its entirety. The system considers multiple factors simultaneously, creating a comprehensive view of the situation before making a decision. This ensures that access control is both precise and context-aware.
Conditional Access also aligns closely with modern security principles, particularly the idea that trust should not be assumed. Instead, trust must be verified continuously. This principle is essential in today’s threat landscape, where attackers often operate within compromised accounts and networks. By evaluating each access request independently, Conditional Access minimizes the risk of unauthorized access.
How Conditional Access Functions as a Decision Engine
When a user attempts to access an application or service, the Conditional Access system is triggered immediately. It begins by collecting relevant signals associated with the request. These signals include information about the user, the device being used, the location of the request, and any risk indicators identified by security systems.
Once the data is collected, it is analyzed against the organization’s defined policies. These policies act as rules that determine what conditions must be met for access to be granted. The evaluation process is completed in real time, ensuring that users experience minimal delay during authentication.
Based on the outcome of this evaluation, the system decides how to proceed. In some cases, access is granted without any additional steps. In other cases, the system may require the user to complete multifactor authentication or meet specific device compliance requirements. If the risk is deemed too high, access may be blocked entirely.
This decision-making process ensures that security measures are applied proportionally to the level of risk associated with each request. It eliminates the need for overly restrictive policies that could disrupt user productivity while still maintaining a strong security posture.
Key Elements That Influence Access Decisions
Conditional Access relies on several key elements to evaluate access requests effectively. These elements work together to provide a comprehensive understanding of each login attempt.
User identity is one of the most critical factors. The system verifies who the user is and whether they belong to specific groups or roles within the organization. This information helps determine what level of access should be granted.
Device information is another important element. The system assesses whether the device being used meets security requirements, such as having updated software, encryption enabled, and security tools installed. Devices that do not meet these standards may be restricted or denied access.
Location data is also considered. Access attempts originating from trusted locations may be treated differently from those coming from unfamiliar or high-risk regions. This helps organizations protect against unauthorized access from potentially dangerous locations.
Risk signals play a crucial role as well. These signals are generated by advanced security systems that analyze user behavior and detect anomalies. For example, an unusual login pattern or a sudden change in location may indicate a compromised account. In such cases, additional verification steps can be enforced to mitigate the risk.
Balancing Security and User Experience
One of the primary challenges in implementing security measures is finding the right balance between protection and usability. Overly strict security controls can frustrate users and hinder productivity, while weak controls can leave organizations vulnerable to attacks. Conditional Access addresses this challenge by providing a flexible and adaptive approach.
By applying security measures only when necessary, Conditional Access minimizes disruptions to the user experience. Users can access resources بسهولة when conditions are safe, without being repeatedly prompted for additional verification. At the same time, the system ensures that higher levels of security are enforced when risks are detected.
This balance is essential for maintaining user satisfaction while ensuring that organizational data remains protected. It allows employees to focus on their work without being burdened by unnecessary security hurdles, while still benefiting from robust protection behind the scenes.
The Role of Conditional Access in Modern Security Strategies
Conditional Access has become a fundamental component of modern security strategies. It supports the shift toward identity-based security models, where access decisions are centered around user identity rather than network location. This approach is particularly important in cloud environments, where traditional network boundaries are no longer relevant.
By integrating with other security solutions, Conditional Access enhances an organization’s overall security posture. It works in conjunction with identity protection systems, device management tools, and threat detection mechanisms to provide a comprehensive defense against cyber threats.
This integration enables organizations to respond to threats more effectively. For example, if a potential compromise is detected, Conditional Access can automatically enforce stricter authentication requirements or block access altogether. This proactive approach helps prevent security incidents before they escalate.
Why Traditional Authentication Methods Are No Longer Enough
Traditional authentication methods, such as passwords, are no longer sufficient to protect against modern threats. Passwords can be easily compromised through phishing attacks, brute-force attempts, or data breaches. Once an attacker gains access to valid credentials, they can often bypass basic security measures.
Conditional Access addresses this limitation by introducing additional layers of verification. Multifactor authentication is commonly used to ensure that users provide more than just a password. This may include a verification code, biometric data, or approval through a trusted device.
In addition to multifactor authentication, Conditional Access evaluates contextual factors to determine whether access should be granted. This ensures that even if credentials are compromised, unauthorized access can still be prevented. By combining multiple security measures, Conditional Access provides a more robust defense against attacks.
The Importance of Real-Time Policy Enforcement
One of the defining features of Conditional Access is its ability to enforce policies in real time. This means that access decisions are made instantly, based on the current context of the request. Real-time enforcement is critical in today’s fast-paced digital environment, where threats can emerge and evolve بسرعة.
By evaluating each access request as it occurs, Conditional Access ensures that security measures are always up to date. Policies can be adjusted بسرعة to respond to new threats or changing organizational requirements. This flexibility allows organizations to maintain a strong security posture without sacrificing agility.
Real-time enforcement also enhances the effectiveness of security measures. Instead of relying on periodic checks or static rules, Conditional Access continuously monitors access attempts and applies appropriate controls. This ensures that potential risks are addressed immediately, reducing the likelihood of security breaches.
Detailed Flow of Conditional Access Evaluation
Every interaction with a protected application begins with a sign-in attempt, and this is where the Conditional Access process becomes active. The system does not simply verify credentials and grant entry. Instead, it initiates a sequence of evaluations that consider the full context of the request. This process is designed to be both fast and comprehensive, ensuring that security decisions are made without introducing noticeable delays for users.
The first step involves identifying the user and gathering basic authentication details. This includes verifying credentials and determining whether the user exists within the organization’s directory. However, this is only the starting point. The system then expands its analysis to include additional contextual signals that provide a deeper understanding of the situation.
Once all relevant data is collected, the system compares it against predefined policies. These policies act as a framework for decision-making, specifying what conditions must be met and what actions should be taken. The outcome of this evaluation determines whether access is granted, denied, or conditioned on additional requirements. This layered approach ensures that access decisions are both accurate and adaptable to changing circumstances.
Understanding Policy Structure and Design
Conditional Access policies are the foundation of the entire system. They define how access decisions are made and what conditions must be satisfied. Designing these policies requires careful consideration, as they must balance security requirements with user convenience. Poorly designed policies can either create unnecessary friction or leave gaps in security.
A well-structured policy typically includes several components that work together to define its behavior. The first component specifies the users or groups to which the policy applies. This allows organizations to target specific individuals, departments, or roles, ensuring that policies are relevant and effective.
The second component focuses on the applications or services being accessed. Not all resources require the same level of protection. For example, accessing general information may require minimal restrictions, while accessing sensitive data may require stricter controls. By defining the scope of applications, organizations can apply appropriate levels of security where needed.
Conditions form another critical part of policy design. These conditions determine when a policy is triggered. They may include factors such as location, device type, or risk level. By combining multiple conditions, organizations can create highly specific scenarios that reflect real-world situations.
Finally, access controls define the actions that should be taken when conditions are met. These actions may include granting access, requiring additional authentication, or blocking access entirely. Together, these components create a flexible framework that can adapt to a wide range of scenarios.
The Role of Identity in Access Decisions
Identity is at the heart of Conditional Access. Every access decision begins with understanding who the user is and what permissions they should have. This involves more than just verifying a username and password. The system also considers the user’s role, group membership, and historical behavior.
Different users within an organization often have different levels of access. For example, an executive may have access to sensitive financial data, while a general employee may only access operational tools. Conditional Access policies can be tailored to reflect these differences, ensuring that each user receives the appropriate level of access.
In addition to role-based access, identity-based signals can also reveal potential risks. For instance, if a user suddenly attempts to access resources that are outside their normal scope, this may indicate suspicious activity. Conditional Access can respond by enforcing additional verification steps or restricting access until the risk is resolved.
By focusing on identity, organizations can implement a more precise and effective approach to access control. This reduces the likelihood of unauthorized access while ensuring that legitimate users can perform their tasks efficiently.
Device-Based Access Control and Compliance
Devices play a significant role in determining whether access should be granted. Not all devices are equally secure, and unmanaged or compromised devices can pose a serious risk to organizational data. Conditional Access addresses this challenge by incorporating device-based controls into its decision-making process.
When a user attempts to access a resource, the system evaluates the device being used. This includes checking whether the device meets security requirements, such as having up-to-date software, encryption enabled, and security tools installed. Devices that meet these requirements are considered compliant and may be granted access more easily.
On the other hand, devices that do not meet compliance standards may be restricted or denied access. In some cases, users may be required to bring their devices into compliance before they can proceed. This ensures that only secure devices are used to access sensitive information.
Device-based access control is particularly important in environments where employees use personal devices for work purposes. By enforcing compliance standards, organizations can maintain control over their data without restricting flexibility for users.
Location and Network Awareness in Conditional Access
Location is another critical factor that influences access decisions. Conditional Access can evaluate where a sign-in request is coming from and determine whether it aligns with expected patterns. This helps organizations identify and respond to potentially risky access attempts.
Trusted locations, such as corporate offices or known network ranges, are typically considered safe. Users accessing resources from these locations may experience fewer restrictions. However, access attempts from unfamiliar or high-risk locations may trigger additional security measures.
For example, a login attempt from a region where the organization does not operate may be flagged as suspicious. In such cases, Conditional Access can require additional authentication or block access entirely. This reduces the risk of unauthorized access from external threats.
Network conditions are also taken into account. Access from secure networks may be treated differently from access over public or unsecured networks. By considering both location and network context, Conditional Access provides a more comprehensive approach to security.
Risk-Based Access and Intelligent Decision Making
One of the most advanced aspects of Conditional Access is its ability to incorporate risk-based analysis into access decisions. This involves evaluating the likelihood that a sign-in attempt may be malicious or compromised. Risk signals are generated by analyzing user behavior, historical patterns, and known threat indicators.
For instance, if a user logs in from two different locations within a short period, this may indicate impossible travel, which is a common sign of compromised credentials. Similarly, repeated failed login attempts or unusual access patterns may raise suspicion.
When such risks are detected, Conditional Access can respond dynamically. It may require the user to complete additional verification steps, such as multifactor authentication, or even force a password reset. In high-risk scenarios, access may be blocked بالكامل to prevent potential damage.
This intelligent approach allows organizations to respond to threats in real time, without relying solely on static rules. By integrating risk analysis into the decision-making process, Conditional Access enhances both security and responsiveness.
Session Controls and Ongoing Access Management
Conditional Access does not stop at the point of login. It also plays a role in managing user sessions after access has been granted. Session controls allow organizations to define how users interact with applications and data במהלך their sessions.
For example, organizations can enforce sign-in frequency requirements, ensuring that users reauthenticate after a certain period. This reduces the risk of unauthorized access if a session is left unattended. Similarly, session controls can restrict certain actions, such as downloading sensitive data, especially when access is from an unmanaged device.
These controls provide an additional layer of security by monitoring user activity beyond the initial authentication مرحله. They ensure that access remains secure طوال the duration of the session, not just at the point of entry.
By extending security measures into the session itself, Conditional Access provides a more comprehensive approach to protecting organizational resources. This helps prevent data leaks and unauthorized actions, even after access has been granted.
Integration with Broader Security Ecosystem
Conditional Access is not a standalone feature. It is part of a broader security ecosystem that includes identity protection, device management, and threat detection systems. This integration allows organizations to create a unified and coordinated approach to security.
For example, device management solutions can provide information about device compliance, which is then used by Conditional Access to make access decisions. Similarly, identity protection systems can generate risk signals based on user behavior, which are incorporated into the evaluation process.
This interconnected approach ensures that all aspects of security work together seamlessly. Instead of operating in isolation, different systems share information and সহযোগিতা to enhance overall protection.
By leveraging this ecosystem, organizations can achieve a higher مستوى of security without increasing complexity for users. Conditional Access acts as the central نقطة where all these signals are combined and evaluated, enabling smarter and more effective access control decisions.
Common Real-World Scenarios for Conditional Access Implementation
Organizations adopt Conditional Access to address practical security challenges that arise in everyday operations. These scenarios highlight how flexible and context-aware access control can improve both protection and usability. Instead of enforcing rigid rules, Conditional Access adapts to the situation, ensuring that security measures align with actual risk levels.
One common scenario involves employees accessing corporate resources from different devices. In many cases, organizations allow users to work from personal laptops or mobile devices. While this increases flexibility, it also introduces potential risks. Conditional Access can evaluate whether the device meets security standards before allowing access. If the device is unfamiliar or does not meet compliance requirements, the system may require additional verification or restrict access altogether.
Another scenario involves remote work. Employees frequently connect from home networks, public Wi-Fi, or while traveling. Conditional Access can assess the security of these connections and apply appropriate controls. For example, access from a trusted home network may be allowed بسهولة, while access from an unsecured public network may require multifactor authentication.
These real-world applications demonstrate how Conditional Access provides a practical solution to modern security challenges, ensuring that access decisions are always aligned with the current context.
Handling Access from Unfamiliar or Risky Devices
Devices that are not recognized or managed by the organization present a significant security concern. These devices may lack essential protections such as updated software, antivirus tools, or encryption. Conditional Access addresses this issue by identifying whether a device is known and compliant before granting access.
When a user attempts to sign in from a new or unfamiliar device, the system treats the request with increased caution. It may prompt the user to verify their identity through additional authentication steps. This ensures that even if credentials are compromised, unauthorized users cannot بسهولة gain access from unknown devices.
In some cases, organizations may choose to block access entirely from unmanaged devices. Alternatively, they may allow limited access, such as restricting the ability to download sensitive data. This approach provides a balance between maintaining security and allowing flexibility for users who need to work from مختلف devices.
By carefully managing device-based access, organizations can reduce the risk of data breaches while still supporting modern work practices.
Managing Access Based on Geographic Location
Geographic location plays a critical role in identifying potential security threats. Access attempts from unexpected or high-risk regions can indicate malicious activity, especially if they deviate from a user’s normal behavior. Conditional Access uses location data to evaluate whether a sign-in request should be trusted.
Organizations can define trusted locations where access is considered safe. These may include office networks or regions where employees عادة operate. When users sign in from these locations, they may experience fewer restrictions, مما improves productivity.
Conversely, access attempts from unfamiliar or high-risk المناطق may trigger additional security measures. For example, a login attempt from a country where the organization has no presence may be flagged as suspicious. In such cases, Conditional Access can require multifactor authentication or block the request entirely.
This location-based approach helps organizations defend against external threats while ensuring that legitimate users can access resources without unnecessary barriers. It also provides an إضافي layer of intelligence that enhances overall security decision-making.
Ensuring Device Compliance Through Integrated Controls
Maintaining device compliance is essential for protecting organizational data. Devices that do not meet security standards can تصبح entry points for attackers. Conditional Access works alongside device management solutions to ensure that only compliant devices are allowed to access sensitive resources.
Compliance requirements may include having the latest operating system updates, enabling encryption, and installing security software. When a device meets these standards, it is considered safe for accessing corporate data. If it does not, Conditional Access can enforce restrictions until the device is brought into compliance.
This integration allows organizations to maintain a consistent level of security across all الأجهزة. Users are encouraged to keep their devices secure, knowing that non-compliant devices will limit their access. This not only protects data but also promotes better security practices among employees.
By enforcing compliance through Conditional Access, organizations يمكنهم ensure that their security policies are applied consistently, regardless of where or how users connect.
Securing Access for External Users and Guests
External users, such as partners, vendors, and contractors, often require access to organizational resources. However, these users typically do not operate within the same controlled environment as internal employees. This makes their access inherently more risky. Conditional Access provides the tools needed to manage this risk effectively.
Organizations can apply stricter policies to external users, ensuring that their access is carefully controlled. For example, multifactor authentication may be required for every login attempt, regardless of location or device. This ensures that external users are consistently verified before gaining access.
In addition to authentication requirements, organizations can محدود the scope of access for external users. They may only be allowed to access specific applications or data आवश्यक for their role. This principle of least privilege reduces the potential impact of a compromised account.
By applying targeted controls to guest access, Conditional Access helps organizations collaborate with external parties while maintaining strong security standards. This ensures that partnerships and التعاون can continue without exposing sensitive information to unnecessary risk.
Enhancing Security Through Granular Policy Control
One of the most powerful aspects of Conditional Access is its ability to provide granular control over security policies. Organizations are not limited to broad, one-size-fits-all rules. Instead, they can create highly specific policies that address different scenarios and user groups.
For example, a policy may require stronger authentication for users accessing financial البيانات, while allowing simpler access for less sensitive applications. Similarly, executives or administrators may be subject to stricter controls due to the حساس nature of their roles.
This level of customization allows organizations to align their security measures with their unique needs. It ensures that resources are protected appropriately without creating unnecessary complexity for users. By tailoring policies to specific situations, organizations can achieve a more effective and efficient security strategy.
Granular control also makes it easier to adapt to changing requirements. As new threats emerge or business needs evolve, policies can be adjusted بسرعة to reflect these changes. This flexibility is essential in maintaining a strong security posture over time.
Improving User Experience While Maintaining Security
Security measures are often seen as obstacles that slow down productivity. However, Conditional Access is designed to minimize this perception by providing a seamless user experience. It achieves this by applying security controls only when necessary, based on the level of risk associated with each access request.
When conditions are safe, users can access resources without interruption. This reduces frustration and allows them to focus on their work. At the same time, the system ensures that additional verification steps are enforced when risks are detected.
This approach eliminates the need for constant authentication prompts, which can be disruptive and time-consuming. Instead, users experience a smooth and efficient workflow, while security remains قوية in the background.
By balancing security and usability, Conditional Access helps organizations maintain عالية مستويات of productivity without compromising on protection. This is particularly important in fast-paced environments where efficiency is critical.
Automation and Real-Time Threat Response
Automation is a key عنصر of Conditional Access. The system is designed to make decisions automatically, without requiring constant intervention from IT teams. This not only improves efficiency but also ensures that security measures are applied consistently.
When a potential threat is detected, Conditional Access can respond immediately. For example, if a login attempt is identified as high risk, the system may automatically require multifactor authentication or block access. This rapid response helps prevent security incidents before they escalate.
Automation also reduces the burden on IT administrators. Instead of manually monitoring access requests and اتخاذ decisions, they can rely on predefined policies to handle most scenarios. This allows them to focus on more strategic tasks, such as improving overall security استراتيجية.
By leveraging automation, Conditional Access ensures that security is both proactive and responsive. It enables organizations to stay ahead of threats while maintaining a streamlined and efficient approach to access management.
Steps to Create and Configure Conditional Access Policies
Setting up Conditional Access policies requires a structured approach to ensure that security controls are both effective and practical. The process begins with accessing the administrative interface where identity and security configurations are managed. Administrators must use accounts with appropriate permissions to define and deploy policies that will impact user access across the organization.
Once inside the management environment, the next step is to locate the Conditional Access section under security settings. This is where all existing policies can be reviewed and new ones can be created. A clear understanding of organizational requirements is essential at this stage, as policies should reflect both security priorities and operational needs.
Creating a new policy involves assigning it a descriptive name that clearly indicates its purpose. This helps administrators manage multiple policies بسهولة and ensures that configurations remain organized over time. After naming the policy, administrators define the scope by selecting the users, groups, or roles to which the policy will apply. This step is critical لأن it determines who will be affected by the policy.
The next phase involves selecting the applications or services that require protection. Organizations often prioritize critical systems such as financial platforms, communication tools, or data storage services. By targeting specific applications, administrators can apply stronger controls where they are most needed while keeping access to less sensitive resources more flexible.
Defining Conditions for Policy Enforcement
Conditions are the backbone of any Conditional Access policy. They determine when a policy is triggered and what contextual factors must be evaluated. Administrators can define a wide range of conditions based on organizational requirements and threat scenarios.
Location-based conditions allow organizations to differentiate between trusted and untrusted environments. For example, access requests from corporate networks may be treated as منخفض risk, بينما requests from unknown locations may trigger additional verification. This ensures that security measures are aligned with the مستوى of risk associated with each access attempt.
Device-based conditions focus on the security posture of the الأجهزة being used. Administrators can require devices to meet specific compliance standards before granting access. This includes ensuring that devices are updated, encrypted, and protected by security software. Devices that fail to meet these criteria may be denied access or restricted until they become compliant.
Risk-based conditions add another layer of intelligence to policy enforcement. By analyzing user behavior and detecting anomalies, the system can identify potentially compromised accounts. Policies can then respond dynamically, requiring stronger authentication or blocking access altogether when risks are high.
By combining multiple conditions, administrators can create highly targeted policies that address specific scenarios. This flexibility allows organizations to implement nuanced security strategies that adapt to real-world situations.
Configuring Access Controls and Enforcement Actions
After defining conditions, administrators must specify how access should be controlled عندما those conditions are met. Access controls determine the actions that the system will take in response to an access request. These actions form the core of policy enforcement and directly impact the user experience.
One common control is requiring multifactor authentication. This adds an extra layer of security by ensuring that users provide additional verification beyond their passwords. It is particularly effective in preventing unauthorized access الناتج عن compromised credentials.
Another control involves enforcing device compliance. Users may be required to access resources only from devices that meet organizational security standards. This ensures that sensitive data is not exposed to insecure or unmanaged devices.
Blocking access is the most restrictive control and is typically used in high-risk scenarios. When the system detects a significant threat, it can prevent access entirely to protect organizational resources. This decisive action helps mitigate potential security incidents before they cause damage.
These controls can also be combined to create layered security measures. For example, a policy may require both multifactor authentication and device compliance for access to critical systems. This ensures that multiple conditions must be satisfied before access is granted.
Testing and Gradual Deployment of Policies
Implementing Conditional Access policies requires careful testing to avoid unintended disruptions. Before applying a policy across the entire organization, administrators should البداية with a controlled testing phase. This allows them to evaluate how the policy behaves in real-world scenarios and identify any potential issues.
One effective approach is to apply the policy to a small group of users, often referred to as a pilot group. These users can provide feedback on their experience, helping administrators فهم how the policy impacts اليومية operations. Adjustments can then be made to improve both security and usability.
Another important step is using a monitoring mode that allows administrators to observe how policies would affect access without actually enforcing them. This provides valuable insights into potential outcomes without risking disruptions. Once administrators are confident that the policy works as intended, it can be fully enabled.
Gradual deployment ensures that policies are introduced smoothly and that any issues are addressed before they affect the entire organization. This approach reduces the risk of user frustration and ensures a successful implementation.
Benefits of Conditional Access for Organizations
Conditional Access provides numerous benefits that make it an essential component of modern security strategies. One of the most significant advantages is enhanced security. By evaluating access requests in real time and applying appropriate controls, organizations can reduce the risk of unauthorized access and data breaches.
Another key benefit is improved user experience. Unlike traditional security measures that apply the same rules to all users, Conditional Access adapts to the context of each request. This means that users can access resources بسهولة when conditions are safe, while additional verification is only required when necessary.
The ability to create granular policies is also a major advantage. Organizations can tailor their security measures to different users, roles, and applications. This ensures that sensitive data receives the highest level of protection, while أقل critical resources remain easily accessible.
Automation further enhances the value of Conditional Access. By making decisions automatically based on predefined policies, the system reduces the need for manual intervention. This allows IT teams to focus on strategic initiatives rather than routine access management tasks.
Together, these benefits create a قوية security framework that supports both protection and productivity. Organizations can confidently manage access to their resources while maintaining a seamless user experience.
Supporting Modern Security Models with Conditional Access
Conditional Access plays a crucial role in supporting modern security models that prioritize identity and context over traditional network boundaries. One of the most widely adopted approaches is the concept of zero trust, which assumes that no access request should be trusted by default.
In a zero trust model, every access attempt must be verified based on multiple factors, including identity, device, and risk level. Conditional Access provides the mechanisms needed to implement this approach effectively. By continuously evaluating access requests, it ensures that trust is earned rather than assumed.
This model is particularly important in cloud environments, where users and devices connect from diverse locations. Conditional Access enables organizations to maintain control over access even عندما resources are hosted خارج traditional networks. It ensures that security policies are enforced consistently, regardless of where users are located.
By aligning with modern security principles, Conditional Access helps organizations stay ahead of evolving threats. It provides a flexible and scalable solution that can adapt to changing التكنولوجيا landscapes and business needs.
Final Thoughts
Conditional Access represents a significant shift in how organizations approach security. Instead of relying on static rules and assumptions, it introduces a dynamic and context-aware system that adapts to each access request. This تحول allows organizations to respond more effectively to modern threats while maintaining a smooth user experience.
The true strength of Conditional Access lies in its ability to combine multiple signals into a single decision-making process. By evaluating identity, device, location, and risk simultaneously, it provides a comprehensive view of each access attempt. This ensures that decisions are both accurate and informed.
As organizations continue to embrace digital transformation, the need for intelligent access control will only grow. Conditional Access provides the foundation for this capability, enabling organizations to protect their resources without limiting productivity. It ensures that the right individuals can access the right resources under the right conditions, creating a balanced and effective security strategy.