Access control is a fundamental concept in networking that determines how data flows between devices and networks. In any structured network environment, routers act as intelligent decision-makers that inspect incoming and outgoing traffic, allowing or denying packets based on predefined rules. One of the most powerful tools available to network administrators for enforcing these decisions is the Access Control List, commonly referred to as an ACL. These lists provide a mechanism to filter traffic and ensure that only authorized communication is permitted across network boundaries. By implementing ACLs, administrators can improve security, optimize performance, and maintain strict control over network behavior.
Access lists are not limited to a single protocol or environment; they are versatile and can be configured to manage traffic for various routed protocols, although they are most commonly associated with IP-based networks. Their primary function is to evaluate packets and determine whether they should be forwarded or dropped. This evaluation process is carried out by comparing packet characteristics such as source address, destination address, protocol type, and port numbers against a set of predefined rules. Once a match is found, the corresponding action—either permit or deny—is executed immediately.
Understanding how ACLs work is essential for anyone involved in network administration. They are not just about blocking unwanted traffic; they also play a crucial role in allowing legitimate communication to pass through without disruption. When used correctly, ACLs can create a secure and efficient network environment that aligns with organizational policies and requirements.
Understanding Extended Access Lists
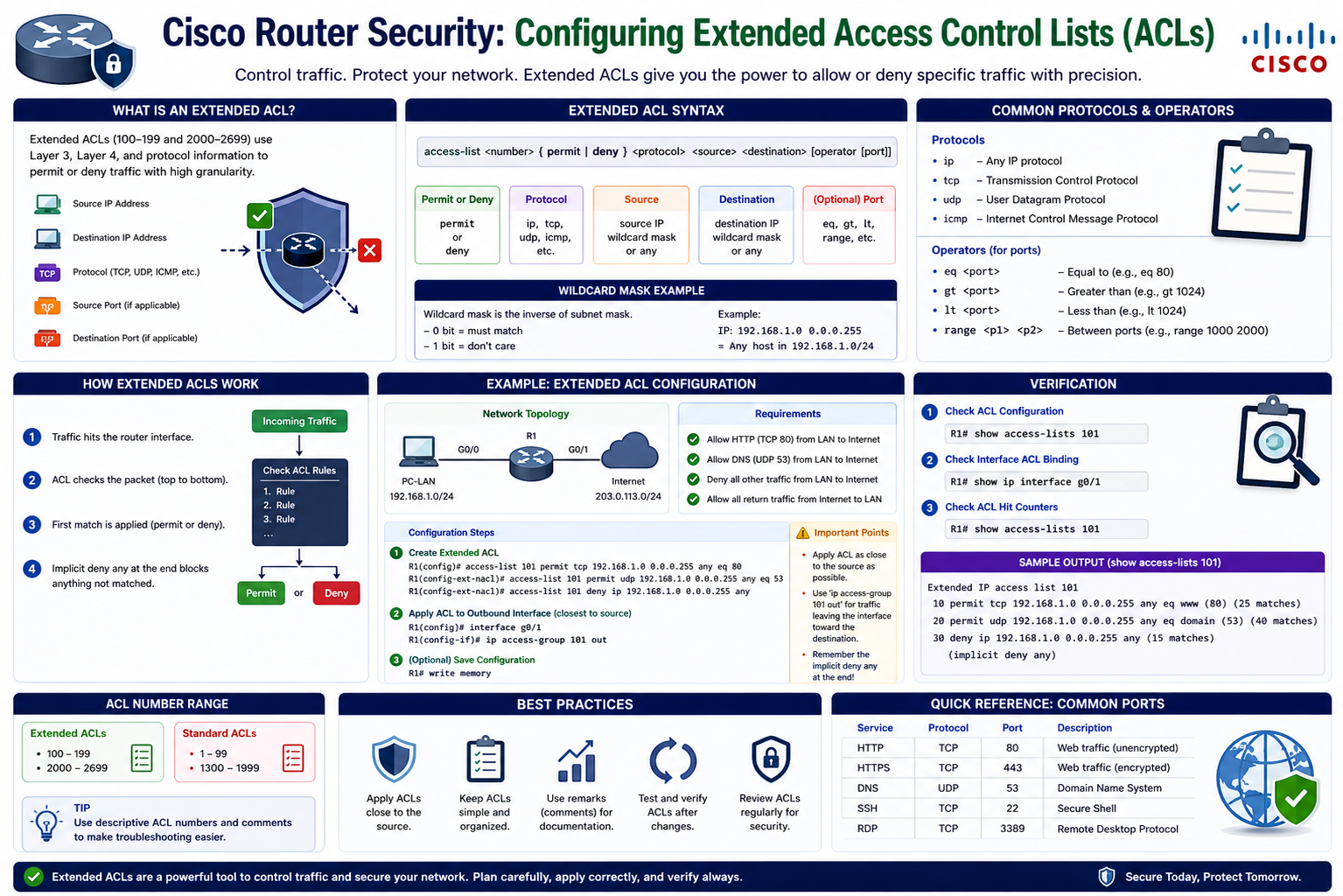
Extended Access Control Lists represent a more advanced and flexible form of traffic filtering compared to standard ACLs. While standard ACLs typically filter traffic based only on source IP addresses, extended ACLs provide much greater control by allowing administrators to define rules based on multiple criteria. These criteria include source and destination IP addresses, transport protocols such as TCP or UDP, specific port numbers, and even time-based conditions. This level of granularity makes extended ACLs an essential tool for implementing precise security policies.
The ability to filter traffic based on ports is particularly significant because many network services operate on well-known port numbers. For example, web traffic typically uses port 80 for HTTP and port 443 for HTTPS. By leveraging extended ACLs, administrators can selectively block or allow traffic for these services without affecting other types of communication. This ensures that network operations remain uninterrupted while still enforcing security restrictions where necessary.
Extended ACLs are often described as gatekeepers because they control access to network resources in a highly specific manner. Instead of applying broad restrictions that might disrupt legitimate traffic, they enable targeted filtering that addresses specific threats or requirements. This makes them especially useful in scenarios where certain devices or users need limited access to particular services while maintaining full access to others.
Another important aspect of extended ACLs is their placement within the network. Best practices recommend positioning them as close as possible to the source of the traffic being filtered. This approach minimizes unnecessary data transmission across the network and reduces the load on downstream devices. By stopping unwanted traffic early, extended ACLs contribute to both improved performance and enhanced security.
Scenario-Based Configuration Overview
To better understand how extended ACLs function in practice, consider a scenario where a specific device is attempting to access a server using web-based protocols. Suppose there is a host with the IP address 192.168.1.50 that is trying to connect to another host at 192.168.2.50 using HTTP and HTTPS. In this situation, the goal is to prevent this particular type of access without disrupting other forms of communication between the two devices.
A naive approach might involve blocking all traffic between these two IP addresses, but such a method would likely cause significant issues by preventing legitimate communication. Instead, a more refined solution is required—one that targets only the unwanted traffic while allowing everything else to function normally. This is where extended ACLs demonstrate their true value.
By focusing on specific ports associated with HTTP and HTTPS, it becomes possible to block only the undesired web traffic. This ensures that other services, such as file transfers or network management protocols, remain unaffected. The result is a balanced approach that maintains both security and usability within the network.
In this scenario, the first step is to clearly identify the source of the unwanted traffic. This involves specifying the IP address of the device that is initiating the connection attempts. Once the source is defined, the next step is to determine the destination, which is the server being targeted. With both endpoints identified, the ACL can be configured to evaluate traffic between them and apply the appropriate restrictions.
Defining Source and Destination Parameters
Accurate identification of source and destination addresses is a critical component of ACL configuration. The source address represents the origin of the traffic, while the destination address indicates where the traffic is headed. In extended ACLs, both of these parameters can be specified with a high degree of precision, allowing for detailed control over network communication.
When defining the source, administrators can choose to specify a single host or a range of addresses. In cases where only one device needs to be restricted, the “host” keyword can be used to indicate an exact match. This eliminates the need for a wildcard mask and simplifies the configuration process. On the other hand, if multiple devices within a subnet need to be included, a wildcard mask can be applied to define the range.
Wildcard masks play an important role in ACL configuration by determining which bits of an IP address should be considered during the matching process. Unlike subnet masks, which identify network and host portions of an address, wildcard masks specify which bits can vary. A value of 0 indicates that the corresponding bit must match exactly, while a value of 1 allows for variation. This flexibility enables administrators to create rules that apply to entire subnets or specific groups of devices.
Once the source is defined, attention shifts to the destination. Similar to the source, the destination can be specified as a single host or a range of addresses. In many cases, the destination will be a server or network resource that requires controlled access. By clearly defining both endpoints, the ACL can accurately evaluate traffic and enforce the desired policies.
Implementing Port-Specific Restrictions
One of the defining features of extended ACLs is their ability to filter traffic based on port numbers. This capability allows administrators to target specific services without affecting others, making it possible to implement highly selective security measures. Ports serve as communication endpoints for applications and services, and each port number corresponds to a particular type of traffic.
In the context of the scenario described earlier, the focus is on blocking HTTP and HTTPS traffic. These services operate on ports 80 and 443, respectively. By creating rules that deny traffic matching these port numbers, it becomes possible to prevent web-based access while leaving other types of communication untouched.
The configuration process involves specifying the protocol, which in this case is TCP, along with the source and destination addresses. The “equal to” condition is then used to match the desired port numbers. This ensures that only traffic destined for those specific ports is affected by the rule.
It is important to note that ACLs are processed sequentially, meaning that each rule is evaluated in the order it appears. As soon as a match is found, the corresponding action is taken, and no further rules are considered. This highlights the importance of carefully planning the order of entries to ensure that the desired behavior is achieved.
By implementing port-specific restrictions, administrators can address security concerns in a targeted manner. This approach minimizes disruption to legitimate network activity while effectively blocking unwanted access attempts. It also provides a scalable solution that can be adapted to a wide range of scenarios, making extended ACLs an indispensable tool in modern network management.
Reviewing Access List Entries and Rule Processing
Once extended access control list rules have been created, it becomes essential to verify that they are correctly defined and functioning as intended. Reviewing ACL entries is not just a routine step; it is a critical part of ensuring that the network behaves according to the desired security policies. When administrators configure multiple rules, even a small mistake in syntax, order, or addressing can lead to unexpected results. Therefore, inspecting the ACL after configuration helps confirm that each statement accurately reflects the intended filtering logic.
When an ACL is displayed, it shows each rule in a numbered sequence. These sequence numbers represent the order in which the router processes the entries. This order is extremely important because ACLs operate in a top-down manner. The router examines each packet and compares it against the first rule in the list. If the packet matches that rule, the specified action is applied immediately, and no further rules are evaluated. If it does not match, the router moves on to the next rule, continuing this process until a match is found or the list is exhausted.
This sequential processing means that the placement of rules directly affects how traffic is handled. For example, if a general permit statement is placed before a more specific deny statement, the deny rule may never be reached because the traffic will already have been permitted. As a result, administrators must carefully organize ACL entries to ensure that specific conditions are evaluated before broader ones. This principle is often summarized as placing more specific rules at the top and more general rules at the bottom.
By reviewing ACL entries and understanding how they are processed, administrators can ensure that their configurations are both accurate and effective. This step also provides an opportunity to identify and correct any logical errors before they impact network operations.
Understanding the Implicit Deny Rule
One of the most important concepts in access control list configuration is the presence of the implicit deny rule. This rule is automatically applied at the end of every ACL, regardless of whether it is explicitly defined in the configuration. Although it does not appear when viewing the ACL, it is always active and plays a crucial role in determining how unmatched traffic is handled.
The implicit deny rule essentially states that any traffic not explicitly permitted by the ACL will be denied. This behavior ensures that only traffic matching defined permit statements is allowed to pass through, while everything else is blocked by default. While this approach enhances security, it can also lead to unintended consequences if not properly managed.
In scenarios where only a few deny statements are configured without any corresponding permit statements, the implicit deny rule will block all other traffic. This can result in a complete disruption of network communication, effectively causing an outage. For example, if an administrator creates rules to block HTTP and HTTPS traffic between two hosts but does not include a permit statement for other traffic, the implicit deny rule will prevent all forms of communication between those hosts.
To avoid this issue, it is necessary to include at least one permit statement that allows legitimate traffic to pass through. This is often done by adding a general permit rule that applies to all IP traffic. By doing so, the administrator overrides the implicit deny for traffic that does not match the specific deny conditions. This approach ensures that only the intended restrictions are enforced while maintaining normal network functionality.
Balancing Security with Accessibility
Effective network security requires a careful balance between restricting unwanted access and allowing legitimate communication. Extended ACLs provide the tools needed to achieve this balance, but their effectiveness depends on how they are configured. Overly restrictive rules can disrupt normal operations, while overly permissive rules can leave the network vulnerable to threats.
In the scenario involving the restriction of HTTP and HTTPS traffic, the goal is to block only specific types of communication without affecting other services. This requires a precise configuration that targets the desired ports while permitting all other traffic. By combining deny statements for specific ports with a general permit statement, administrators can achieve this balance.
This approach ensures that web-based access between the specified hosts is blocked, while other types of communication, such as file sharing or remote management, remain unaffected. It also demonstrates the importance of understanding how different types of traffic interact within a network. Each service relies on specific protocols and ports, and ACLs must be configured with this knowledge in mind.
Another consideration is the potential impact on users and applications. Network changes should always be evaluated in terms of how they affect end users. A well-configured ACL should enhance security without introducing unnecessary disruptions. This requires careful planning, testing, and ongoing monitoring to ensure that the network continues to operate smoothly.
Adding Permit Statements to Maintain Connectivity
To ensure that legitimate traffic is not unintentionally blocked, administrators must include appropriate permit statements within their ACL configurations. These statements act as exceptions to the deny rules, allowing specific types of traffic to pass through the router. Without them, the implicit deny rule would block all traffic that does not match an explicit permit condition.
A common practice is to add a general permit statement that allows all IP traffic from any source to any destination. This type of rule effectively overrides the implicit deny for all traffic not explicitly denied by earlier entries. As a result, only the targeted restrictions remain in effect, while all other communication is permitted.
The placement of the permit statement is just as important as its content. Since ACLs are processed sequentially, the permit rule must appear after the specific deny statements. This ensures that the deny conditions are evaluated first, and only traffic that does not match those conditions is allowed by the permit rule. If the permit statement were placed at the top of the list, it would allow all traffic and render the deny rules ineffective.
By carefully adding and positioning permit statements, administrators can maintain network connectivity while enforcing specific security policies. This approach provides a flexible and reliable way to control traffic without causing unintended disruptions.
Verifying ACL Functionality and Behavior
After configuring and adjusting the ACL, it is essential to verify that it is functioning as expected. This involves checking the list of entries and ensuring that each rule is correctly defined and properly ordered. Verification also includes observing how the ACL interacts with actual network traffic.
One way to validate the configuration is by reviewing the ACL entries and confirming that they match the intended design. This includes checking source and destination addresses, protocols, and port numbers. Any discrepancies should be corrected immediately to prevent unexpected behavior.
In addition to reviewing the configuration, administrators can test the ACL by generating traffic that matches the defined conditions. For example, attempting to access a web service from the restricted host can help confirm whether the deny rules are working correctly. Similarly, testing other types of traffic can verify that the permit statement is allowing legitimate communication.
Monitoring tools and logs can also provide valuable insights into ACL performance. By analyzing traffic patterns and identifying blocked or permitted packets, administrators can gain a better understanding of how the ACL is affecting the network. This information can be used to refine the configuration and address any issues that arise.
Verification is not a one-time process but an ongoing practice. As network requirements change, ACLs may need to be updated to reflect new policies or address emerging threats. Regular reviews and testing ensure that the ACL continues to provide effective security while supporting the needs of the network.
Applying Access Lists to Network Interfaces
After creating and verifying an extended access control list, the next critical step is applying it to a router interface. Until an ACL is bound to an interface, it remains inactive and has no effect on traffic. This is a common oversight among beginners, where the configuration appears complete but does not actually influence packet flow. The application stage is what transforms a defined set of rules into an operational security mechanism within the network.
Routers operate by receiving and forwarding packets through their interfaces, and ACLs are applied directly to these interfaces to filter traffic at specific points. Each interface can have ACLs applied in one direction per protocol, meaning you can assign one ACL for inbound traffic and another for outbound traffic. Choosing the correct interface is essential because it determines where in the network the filtering will take place.
Best practices recommend applying extended ACLs as close to the source of the traffic as possible. This approach prevents unwanted packets from traveling further into the network, reducing unnecessary load and improving efficiency. In the example scenario, since the unauthorized traffic originates from a specific host, the ACL should be applied to the interface that first receives that traffic. This ensures that the unwanted packets are dropped early, before they consume network resources or reach sensitive destinations.
The configuration process involves entering the interface configuration mode and associating the ACL with that interface using the appropriate command. Once applied, the router begins evaluating packets against the ACL rules as they pass through the interface. This marks the transition from planning and configuration to active enforcement of network policies.
Understanding Traffic Direction in ACL Application
One of the most important decisions when applying an ACL is determining the direction of traffic flow. ACLs can be applied in either the inbound or outbound direction, and this choice directly affects how and when packets are evaluated. Misunderstanding direction can lead to incorrect filtering behavior, even if the ACL itself is perfectly configured.
Inbound traffic refers to packets entering the router through a specific interface. When an ACL is applied in the inbound direction, it examines packets as soon as they arrive at the interface, before any routing decisions are made. This is typically the preferred approach for extended ACLs because it allows the router to drop unwanted traffic immediately, conserving resources.
Outbound traffic, on the other hand, refers to packets leaving the router through an interface. When an ACL is applied in the outbound direction, it evaluates packets after the routing decision has been made but before they exit the interface. While this can be useful in certain scenarios, it is generally less efficient for filtering unwanted traffic originating from known sources.
A helpful way to understand direction is to think from the perspective of the router itself. Imagine standing inside the router and observing how packets move through its interfaces. If packets are coming into the router through an interface, that is inbound traffic. If they are leaving the router through an interface, that is outbound traffic. This mental model simplifies the process of choosing the correct direction for ACL application.
In the given scenario, the unwanted traffic is entering the router from the source network, so the ACL should be applied in the inbound direction on the relevant interface. This ensures that the traffic is filtered as soon as it arrives, preventing it from progressing further into the network.
Interface Selection and Strategic Placement
Selecting the appropriate interface for ACL application is just as important as choosing the correct direction. Routers often have multiple interfaces connected to different networks, and each interface represents a potential point for traffic filtering. Applying an ACL to the wrong interface can render it ineffective or cause unintended disruptions.
To determine the correct interface, administrators must analyze the network topology and identify where the targeted traffic enters or exits the router. In the example scenario, the source host resides on a specific network segment connected to one of the router’s interfaces. This interface becomes the logical point for applying the ACL because it is the first point of contact for the unwanted traffic.
Strategic placement of ACLs enhances both security and performance. By filtering traffic close to its source, the network avoids unnecessary transmission of unwanted packets across multiple segments. This reduces congestion and ensures that only relevant traffic reaches critical resources.
It is also important to consider how ACL placement interacts with other network configurations, such as routing protocols and network address translation. These elements can influence how traffic flows through the network and, consequently, how ACLs should be applied. A well-planned configuration takes all these factors into account to achieve optimal results.
Administrators should document their decisions regarding interface selection and ACL placement. Clear documentation helps maintain consistency, simplifies troubleshooting, and ensures that future modifications can be made with a full understanding of the existing setup.
Operational Impact of ACL Deployment
Once an ACL is applied to an interface, it immediately begins influencing traffic flow. This can have both positive and negative effects, depending on how well the configuration aligns with the network’s requirements. A properly configured ACL enhances security by blocking unauthorized access while allowing legitimate communication to continue uninterrupted.
However, if the ACL contains errors or is applied incorrectly, it can disrupt normal network operations. For example, an overly restrictive rule might block essential services, leading to connectivity issues for users and applications. This highlights the importance of thorough testing and validation before deploying ACLs in a production environment.
The impact of ACL deployment is not limited to security; it also affects network performance. By filtering out unwanted traffic early, ACLs reduce the amount of data that needs to be processed and forwarded by the router. This can lead to improved efficiency and faster response times for legitimate traffic.
At the same time, ACL processing itself consumes resources, particularly on high-traffic networks. Each packet must be evaluated against the ACL rules, and complex or poorly organized lists can increase processing overhead. To minimize this impact, administrators should keep ACLs as concise and efficient as possible, avoiding unnecessary entries and ensuring that rules are logically ordered.
Monitoring the network after ACL deployment is essential for assessing its impact. By observing traffic patterns and performance metrics, administrators can determine whether the ACL is achieving its intended goals. If issues are identified, adjustments can be made to refine the configuration and improve overall effectiveness.
Maintaining and Updating Access Control Policies
Network environments are dynamic, with changing requirements, new devices, and evolving security threats. As a result, ACLs must be regularly reviewed and updated to remain effective. A configuration that works well today may become outdated or insufficient as the network grows and changes.
Maintenance involves periodically reviewing ACL entries to ensure that they still align with current policies. This includes removing obsolete rules, updating address ranges, and adding new entries to address emerging needs. Regular audits help prevent the accumulation of unnecessary or conflicting rules, which can complicate management and increase the risk of errors.
Updating ACLs should be done carefully to avoid disrupting network operations. Changes should be tested in a controlled environment whenever possible, and administrators should have a rollback plan in case unexpected issues arise. Proper change management practices, including documentation and approval प्रक्रesses, contribute to a stable and secure network.
Another aspect of maintenance is staying informed about new security threats and best practices. As attackers develop new techniques, ACL configurations may need to be adjusted to address these challenges. This requires continuous learning and adaptation on the part of network administrators.
By maintaining and updating access control policies, organizations can ensure that their networks remain secure, efficient, and aligned with their operational goals. Extended ACLs, when properly managed, provide a powerful and flexible tool for achieving these objectives.
Advanced Considerations for Extended Access Lists
As network environments grow in complexity, extended access control lists must evolve beyond basic configurations to address more advanced requirements. While the earlier stages of ACL implementation focus on defining source, destination, protocol, and port-based rules, real-world deployments often require a deeper level of planning and refinement. Administrators must consider how ACLs interact with broader network policies, security frameworks, and operational goals. This involves thinking not only about what traffic should be blocked or allowed, but also about how these decisions impact scalability, performance, and long-term manageability.
One important consideration is the consistency of rule design. In large networks, multiple ACLs may be deployed across different routers and interfaces. If these lists are not structured in a consistent manner, it becomes difficult to manage and troubleshoot them. Establishing a standard naming convention, logical rule order, and clear documentation ensures that ACLs remain understandable even as they grow in size and complexity. Consistency also reduces the likelihood of configuration errors, which can lead to security vulnerabilities or service disruptions.
Another advanced aspect is the use of descriptive remarks within ACL configurations. Although remarks do not affect the operation of the ACL, they provide valuable context for administrators. By including explanations of what each rule is intended to accomplish, remarks make it easier to review and modify configurations in the future. This is particularly useful in environments where multiple administrators are responsible for managing the network. Clear documentation within the ACL itself can save time and prevent misunderstandings.
Optimizing ACL Performance and Efficiency
Performance optimization is a critical factor when working with extended ACLs, especially in high-traffic networks. Each packet that passes through a router must be evaluated against the ACL rules, and this process consumes processing resources. If the ACL is poorly designed or contains unnecessary entries, it can introduce delays and reduce overall network efficiency.
To optimize performance, administrators should focus on minimizing the number of rules and organizing them effectively. Placing the most frequently matched rules at the top of the list ensures that packets are processed quickly, reducing the need for further comparisons. This approach is particularly beneficial in environments where certain types of traffic are more common than others. By prioritizing these rules, the router can handle traffic more efficiently.
Another strategy is to eliminate redundant or overlapping entries. Over time, ACLs can accumulate rules that are no longer needed or that duplicate existing conditions. Regular reviews help identify and remove these entries, keeping the ACL concise and efficient. Simplifying the configuration not only improves performance but also makes it easier to manage and troubleshoot.
Administrators should also be mindful of how ACLs interact with hardware capabilities. Some modern networking devices support hardware-based ACL processing, which can significantly improve performance. Understanding the capabilities of the equipment being used allows administrators to design ACLs that take full advantage of available resources. This ensures that security measures do not come at the expense of network speed and reliability.
Troubleshooting Common ACL Issues
Even with careful planning, issues can arise when working with extended ACLs. Troubleshooting these problems requires a systematic approach and a clear understanding of how ACLs operate. One of the most common issues is unintended traffic blocking, which can occur when rules are too restrictive or incorrectly ordered. In such cases, reviewing the ACL entries and their sequence is the first step toward identifying the problem.
Another frequent issue involves incorrect address or port specifications. A simple mistake in an IP address or port number can cause a rule to match the wrong traffic or fail to match the intended traffic altogether. Verifying these details is essential when diagnosing ACL-related problems. Administrators should also consider whether the correct protocol has been specified, as this can affect how packets are evaluated.
Direction and interface placement are also common sources of errors. If an ACL is applied to the wrong interface or in the wrong direction, it may not produce the expected results. Revisiting the network topology and analyzing the flow of traffic can help determine whether the ACL has been applied correctly. This reinforces the importance of understanding how packets move through the network and how ACLs interact with that movement.
Testing plays a crucial role in troubleshooting. By generating specific types of traffic and observing how the ACL responds, administrators can pinpoint the exact cause of an issue. Logs and monitoring tools provide additional insights, allowing administrators to see which packets are being permitted or denied. This information is invaluable for refining the configuration and resolving problems بسرعة and effectively.
Security Best Practices and Policy Enforcement
Extended ACLs are a powerful tool for enforcing network security policies, but their effectiveness depends on how well they are integrated into a broader security strategy. ACLs should not be used in isolation; they are most effective when combined with other security measures such as firewalls, intrusion detection systems, and authentication mechanisms. Together, these tools create a layered defense that protects the network from a wide range of threats.
One best practice is to follow the principle of least privilege, which involves granting only the minimum level of access required for a given task. This approach reduces the risk of unauthorized activity and limits the potential impact of security breaches. Extended ACLs support this principle by allowing administrators to define highly specific rules that restrict access to only what is necessary.
Regular audits and reviews are also essential for maintaining security. As network requirements change, ACLs must be updated to reflect new policies and address emerging threats. This includes removing outdated rules, adding new restrictions, and ensuring that all entries align with current security objectives. Consistent review processes help maintain the integrity of the network and prevent vulnerabilities from developing over time.
Documentation is another key component of effective policy enforcement. Keeping detailed records of ACL configurations, changes, and their intended purposes ensures that administrators have a clear understanding of the network’s security posture. This documentation supports accountability and makes it easier to respond to incidents or implement future changes.
Final Thoughts
Mastering extended access control lists requires a combination of technical knowledge, practical experience, and careful attention to detail. From understanding the basic principles of traffic filtering to implementing advanced configurations and troubleshooting issues, each step plays a vital role in building a secure and efficient network. Extended ACLs provide the flexibility needed to address a wide range of scenarios, making them an essential skill for network administrators.
The journey begins with a solid understanding of how ACLs evaluate traffic and the importance of rule order, source and destination identification, and port-based filtering. As configurations become more complex, administrators must consider factors such as performance optimization, interface placement, and integration with broader security strategies. Continuous learning and adaptation are key to staying ahead of evolving network demands and security challenges.
Ultimately, the goal of using extended ACLs is to create a network environment that is both secure and functional. By carefully designing, applying, and maintaining these configurations, administrators can ensure that their networks operate smoothly while protecting critical resources from unauthorized access. The principles and practices discussed throughout this content provide a strong foundation for achieving that goal and for developing expertise in network access control.