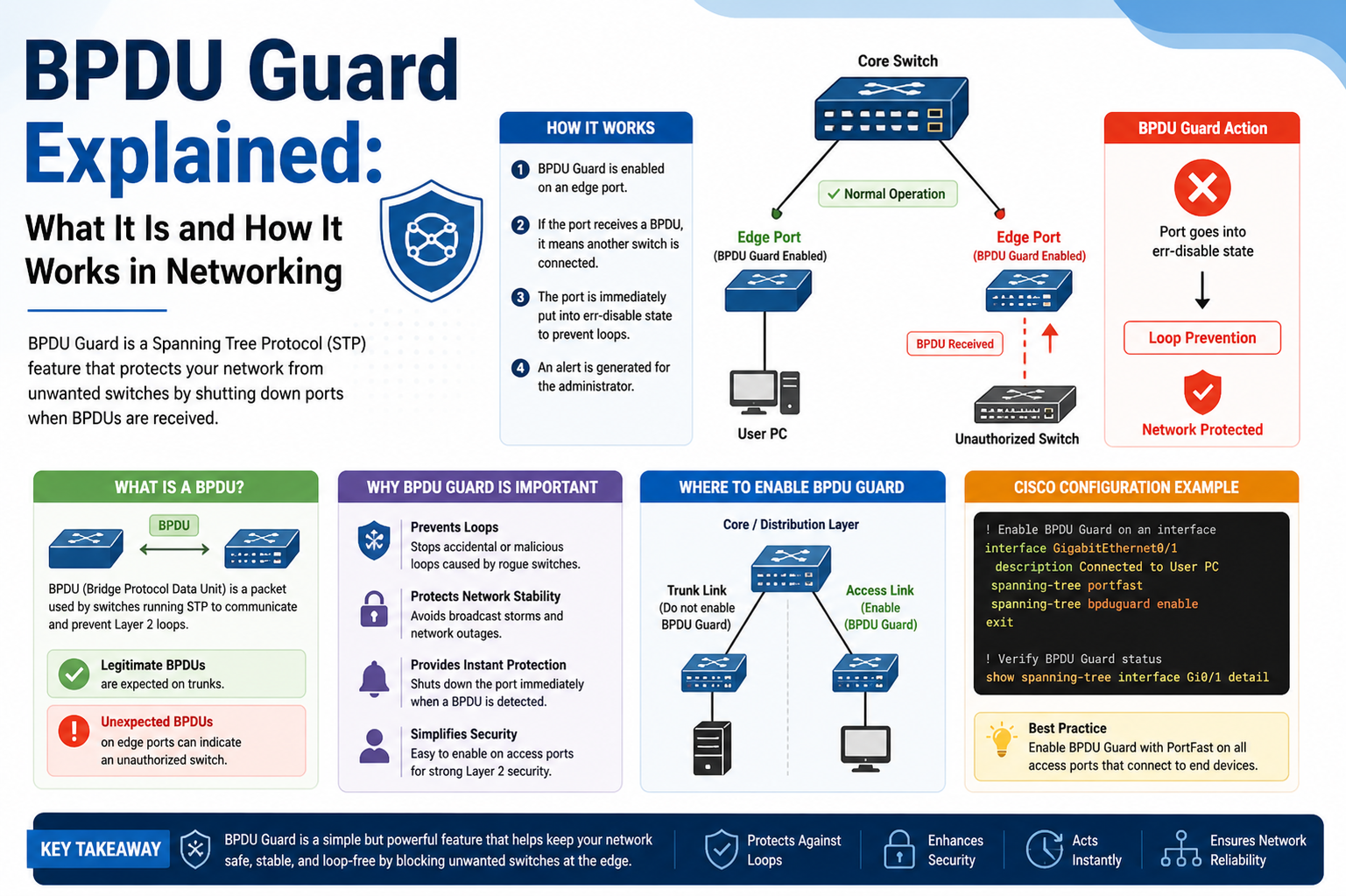
BPDU Guard is a protective mechanism used in modern network environments to safeguard switching infrastructure from unauthorized or potentially harmful devices. It is primarily associated with Cisco networking systems and is designed to enhance the stability and security of Layer 2 network operations. In simple terms, BPDU Guard helps ensure that only trusted and properly configured network devices participate in essential switching decisions, especially those related to loop prevention and topology management.
In a typical enterprise network, multiple switches are interconnected to provide redundancy and efficient data flow. While this design improves reliability, it also introduces the risk of network loops, which can severely degrade performance or even bring down an entire network. To prevent this, a protocol known as Spanning Tree Protocol is used. BPDU Guard is closely tied to this protocol and acts as a protective extension that prevents unexpected or malicious behavior from interfering with the spanning tree process.
Understanding the Role of Network Switching and Layer 2 Communication
To understand BPDU Guard properly, it is important to first understand how switches operate at Layer 2 of the network model. Switches are responsible for forwarding data based on MAC addresses rather than IP addresses. This allows communication within a local network to be fast and efficient. However, when multiple switches are connected together, there is a risk that data frames may circulate endlessly if proper safeguards are not in place.
This is where loop prevention becomes essential. Without a mechanism to control redundant paths, a network could experience broadcast storms, duplicated frames, and severe congestion. These issues not only reduce performance but can also make the network completely unusable. Therefore, specialized protocols are implemented to maintain order in switching environments, and BPDU Guard plays a supporting role in ensuring those protocols function correctly without interference.
Spanning Tree Protocol and Its Importance in Network Stability
Spanning Tree Protocol is one of the foundational technologies used in Ethernet networks to prevent switching loops. It works by creating a logical tree structure within a network, ensuring that there is only one active path between any two devices at a time, while redundant paths remain in standby mode. This structure allows networks to maintain redundancy while avoiding loops.
At the center of Spanning Tree Protocol is a concept known as the root bridge. The root bridge acts as the reference point for all path calculations within the network. Every switch in the network determines the best path to reach the root bridge, and all forwarding decisions are based on this structure. The selection of the root bridge is determined by a value known as the Bridge ID, which is derived from a combination of priority values and MAC address information.
Once the root bridge is established, it periodically sends special control messages to maintain the structure of the spanning tree. These messages ensure that all switches in the network remain synchronized and aware of the topology. Without this continuous exchange of information, the network would lose its structured hierarchy and become vulnerable to loops and instability.
Bridge Protocol Data Units and Their Function in Network Communication
Bridge Protocol Data Units are the messages exchanged between switches in a Spanning Tree Protocol environment. These units contain essential information about switch identity, priority, and topology structure. They are used by switches to determine how the network is organized and which paths should remain active or blocked.
Every switch sends and receives these units to maintain an updated view of the network. When a switch receives a BPDU, it uses the information to decide whether it should become part of the active forwarding topology or remain in a standby state. This continuous exchange of information ensures that the network remains loop-free and stable even when changes occur, such as adding or removing switches.
However, because BPDU messages play such an important role in determining network structure, they can also become a target for manipulation if an unauthorized device is introduced into the network. This is where security concerns arise, and protective features like BPDU Guard become necessary.
Risk of Unauthorized Devices and Network Manipulation Attempts
In a secure and properly managed network, only authorized switches should participate in Spanning Tree Protocol communication. However, if an unauthorized device is connected to the network, it may attempt to send its own BPDU messages. These messages could potentially confuse the existing topology and influence how the network selects its root bridge.
One of the most common attack scenarios involves a rogue device attempting to become the root bridge by advertising itself with a more favorable Bridge ID. If successful, this could cause traffic to be rerouted through an unintended path controlled by the malicious device. This opens the door to traffic interception, network disruption, and potential security breaches.
Even if the intent is not malicious, misconfigured devices such as consumer-grade switches or improperly set up equipment can unintentionally send BPDU messages that interfere with enterprise network operations. Because of this, network administrators must ensure that only trusted infrastructure devices are allowed to participate in spanning tree communication.
Introduction to BPDU Guard as a Protective Mechanism
BPDU Guard is designed to prevent exactly these types of issues by enforcing strict control over where BPDU messages are allowed. It is typically enabled on network ports that connect to end-user devices such as computers, printers, or access points. These devices do not need to participate in Spanning Tree Protocol, and therefore should never send or receive BPDU messages.
When BPDU Guard is enabled on a port, it monitors incoming traffic for any BPDU activity. If a BPDU is detected on a port where it should not exist, BPDU Guard immediately disables the port. This action places the port into an error-disabled state, effectively shutting down communication through that interface to protect the rest of the network.
This behavior is intentional and serves as a strong security measure. Instead of attempting to interpret or negotiate unexpected BPDU messages, BPDU Guard takes a defensive approach by isolating the port completely. This ensures that even if a malicious or misconfigured device is connected, it cannot influence the spanning tree topology.
Relationship Between BPDU Guard and Spanning Tree Stability
BPDU Guard is not a standalone protocol but rather a protective extension of Spanning Tree Protocol operations. While Spanning Tree ensures loop-free network design, BPDU Guard ensures that the integrity of that design is not compromised at the edge of the network. Together, they form a layered defense system that maintains both stability and security.
In environments where multiple access layers exist, BPDU Guard plays an especially important role. Access layer switches are typically connected directly to end-user devices, making them the most vulnerable points in the network. By enabling BPDU Guard at this level, administrators can ensure that no unauthorized device can influence core switching decisions.
This separation of responsibilities allows Spanning Tree Protocol to function without interference while maintaining strict control over network participation. It also reduces the risk of accidental misconfigurations causing widespread network disruptions.
Behavior of Network Ports When BPDU Guard Is Active
When BPDU Guard is enabled on a network port, the port remains fully functional under normal conditions as long as no BPDU messages are detected. The moment a BPDU is received, however, the port is immediately shut down to protect the network. This state is known as error-disabled mode.
In this state, the port stops forwarding traffic entirely, effectively isolating the connected device. The network administrator must manually investigate the cause and re-enable the port after resolving the issue. This ensures that no automated or unintended recovery occurs that could reintroduce the risk.
This strict response mechanism is what makes BPDU Guard highly effective in maintaining network security, especially in environments where physical access to network ports may not always be fully controlled.
Importance of Controlled Network Design in Relation to BPDU Guard
A properly designed network assumes that only specific ports will participate in Spanning Tree Protocol communication. BPDU Guard reinforces this design principle by enforcing boundaries between infrastructure devices and endpoint devices. This separation is essential for maintaining predictable network behavior.
Without such controls, even a single unauthorized connection could disrupt the entire spanning tree topology. By applying BPDU Guard strategically, network engineers ensure that the network remains resilient against both internal misconfigurations and external threats.
This foundational understanding of BPDU Guard, Spanning Tree Protocol, root bridge behavior, and BPDU communication forms the basis for more advanced network security practices.
BPDU Guard – Operational Behavior and Real Network Functionality
BPDU Guard plays a very specific role in maintaining the stability of a switching network by enforcing strict rules on edge ports. While its concept is simple, its real-world behavior is deeply tied to how modern Ethernet networks operate under Spanning Tree Protocol. Understanding how it behaves in active environments helps clarify why it is considered one of the most important protective features in Layer 2 network design.
In practical deployments, BPDU Guard is not something that actively participates in normal traffic forwarding. Instead, it silently monitors network ports where it is enabled. Its purpose is not to improve speed or routing efficiency but to act as a safeguard against unexpected control traffic. This makes it fundamentally different from other switching features that focus on performance optimization.
Edge Ports and the Need for Strict Control
Network switches typically have different types of ports based on their role in the topology. Some ports connect to other switches, while others connect directly to end-user devices such as computers, printers, or wireless access points. These user-facing ports are known as edge ports.
Edge ports are expected to carry only normal data traffic and not participate in Spanning Tree Protocol negotiations. Since end devices do not require knowledge of network topology, they should never send Bridge Protocol Data Units. However, if a device is misconfigured or malicious, it may still attempt to transmit such control messages.
This is where BPDU Guard becomes essential. By enabling it on edge ports, the network ensures that any attempt to send BPDU messages results in immediate action. The port is shut down to prevent further interaction, protecting the rest of the network from potential instability or manipulation.
Behavior of BPDU Guard During Normal Operation
When BPDU Guard is enabled on a switch port, it remains passive under normal conditions. If a standard device such as a laptop or printer is connected, the port behaves like any regular access port and allows communication without interruption. No performance degradation or additional processing occurs during this stage.
The monitoring process only becomes active when a BPDU is detected. The moment a BPDU enters the port, the switch interprets this as a violation of expected behavior. Since edge ports should never receive such control traffic, the system immediately triggers a protective response.
This response is not gradual or conditional. It is immediate and absolute. The port transitions into an error-disabled state, which completely stops all traffic flow. This ensures that no further spanning tree influence can occur from that connection point.
Error-Disabled State and Its Impact on Connectivity
The error-disabled state is one of the most important outcomes of BPDU Guard activation. When a port enters this state, it is effectively shut down at the software level by the switch. This means no frames are forwarded, no communication is allowed, and the connected device is isolated from the network.
From a user perspective, this may appear as a sudden network failure or disconnection. However, from a network security standpoint, this is an intentional protective action. It ensures that the potential risk introduced by unexpected BPDU traffic is immediately neutralized.
Once a port enters error-disabled state, it does not automatically recover. A network administrator must manually investigate the cause and re-enable the port. This manual intervention requirement is important because it prevents repeated or continuous violations from destabilizing the network repeatedly.
Difference Between BPDU Guard and Normal Port Blocking
It is important to understand that BPDU Guard is not the same as standard port blocking mechanisms used in Spanning Tree Protocol. Normal STP blocking occurs as part of loop prevention, where redundant paths are temporarily disabled to maintain a loop-free topology.
In contrast, BPDU Guard is triggered by a security violation rather than a topology decision. It does not consider alternative paths or network optimization. Instead, it reacts solely to the presence of unauthorized BPDU messages on a port where they are not expected.
This distinction makes BPDU Guard a security enforcement tool rather than a traffic management tool. Its primary goal is to protect the integrity of the network structure rather than optimize its flow.
Types of Devices That Trigger BPDU Guard
Not all devices connected to a network are capable of sending BPDU messages. Standard end-user devices such as laptops, desktops, and mobile phones do not generate these messages under normal conditions. However, certain devices can trigger BPDU Guard if they are misconfigured or intentionally designed to behave like network switches.
Small unmanaged switches, rogue network devices, or improperly configured access points are common examples. If such a device is connected to an edge port with BPDU Guard enabled, it may begin sending BPDU messages as part of its own internal switching logic.
Once these messages are detected, BPDU Guard treats them as a violation. The port is immediately shut down regardless of whether the intent was malicious or accidental. This strict enforcement ensures that only properly controlled infrastructure devices participate in spanning tree operations.
Interaction Between BPDU Guard and Network Topology Changes
Although BPDU Guard does not directly participate in topology calculations, its actions can indirectly influence network behavior. When a port is disabled due to BPDU detection, any devices connected through that port are effectively removed from the network topology.
This removal can cause temporary changes in traffic flow, especially in environments where redundancy depends on multiple access points. However, this impact is intentional and considered safer than allowing potentially harmful BPDU activity to continue.
In well-designed networks, such disruptions are minimal because BPDU Guard is only applied to edge ports. Core and distribution layer switches are typically not configured with BPDU Guard, as they require full participation in Spanning Tree Protocol communication.
Role of BPDU Guard in Preventing Root Bridge Manipulation
One of the most critical functions of BPDU Guard is preventing attempts to manipulate the root bridge election process. In Spanning Tree Protocol, the root bridge is the central reference point that determines network structure.
If a rogue device were allowed to send BPDU messages freely, it could attempt to advertise itself with a more favorable Bridge ID. This could potentially trick other switches into selecting it as the root bridge, which would significantly alter network traffic flow.
BPDU Guard prevents this scenario by ensuring that edge ports never allow BPDU communication in the first place. Since end devices are the most likely connection points for unauthorized devices, enforcing this restriction at the edge eliminates a major attack vector.
Administrative Responsibility and Network Control
While BPDU Guard automates the response to unauthorized BPDU traffic, it still requires administrative oversight for recovery and investigation. When a port is disabled, the network administrator must determine the source of the violation before reactivating the interface.
This process often involves checking connected devices, verifying configurations, and ensuring that no unauthorized switching devices are present. Once the issue is resolved, the port can be manually re-enabled to restore connectivity.
This controlled recovery process ensures that network stability is not compromised by automatic reactivation, which could otherwise allow repeated violations to occur without detection.
Importance of Proper Placement in Network Design
The effectiveness of BPDU Guard depends heavily on correct implementation. It is not meant to be enabled on every port indiscriminately. Instead, it should be carefully applied to access layer ports where end-user devices connect.
Applying BPDU Guard to incorrect interfaces, such as inter-switch links, can cause unintended network outages. Therefore, proper network design and planning are essential before deployment.
When used correctly, BPDU Guard becomes a powerful safeguard that strengthens network resilience without interfering with normal operations.
BPDU Guard – Configuration, Deployment Strategy, and Network Implementation
BPDU Guard is not just a theoretical security feature; it becomes highly effective only when it is properly configured and strategically deployed within a real network environment. In enterprise networks, configuration decisions determine whether BPDU Guard acts as a reliable safeguard or becomes a source of unexpected connectivity issues. Understanding how to apply it correctly is essential for maintaining both stability and security across switching infrastructure.
In most modern network designs, BPDU Guard is implemented at the access layer, where end-user devices connect to switches. These access layer ports are considered untrusted from a spanning tree perspective because they should never participate in topology decisions. Therefore, configuration is focused on ensuring that these ports remain isolated from any form of Spanning Tree Protocol negotiation.
Global Configuration Approach for Efficient Deployment
One of the most efficient ways to implement BPDU Guard is through global configuration on a switch. Instead of manually enabling the feature on each individual port, network administrators can apply it across all relevant ports simultaneously. This approach reduces configuration time and minimizes the risk of missing critical interfaces.
When configured globally, BPDU Guard is typically combined with PortFast functionality. PortFast allows edge ports to transition quickly into forwarding mode without going through the normal spanning tree listening and learning states. Since these ports are expected to connect to end devices, rapid convergence improves user experience while maintaining security enforcement through BPDU Guard.
In this setup, BPDU Guard remains active on all PortFast-enabled interfaces. If any BPDU is detected on these ports, the switch immediately places the port into an error-disabled state. This combination ensures both performance optimization and strict security enforcement at the network edge.
Interface-Level Configuration for Targeted Control
Although global configuration is widely used, there are situations where BPDU Guard is applied at the interface level. This method allows more granular control over specific ports that require additional protection or exceptions in design.
In interface-level configuration, the administrator manually selects a port and enables BPDU Guard only on that interface. This approach is useful in environments where not all edge ports follow the same trust model or where selective enforcement is required.
However, this method requires careful planning because manual configuration increases the risk of human error. Forgetting to enable BPDU Guard on a sensitive port can leave the network vulnerable, while enabling it on the wrong type of port can lead to unnecessary outages.
Deployment Strategy in Enterprise Network Architecture
In enterprise environments, BPDU Guard is deployed as part of a layered security strategy rather than as a standalone solution. Network architects design switching hierarchies where access, distribution, and core layers each have distinct roles.
At the access layer, BPDU Guard is heavily used because this is where end-user devices connect. These ports are the most exposed to unknown or untrusted devices, making them the primary point of enforcement. The goal at this layer is to ensure that no device connected by users can influence spanning tree behavior.
At higher layers, such as distribution and core switches, BPDU Guard is generally not enabled. These layers are responsible for inter-switch communication and require full participation in Spanning Tree Protocol. Applying BPDU Guard here would disrupt network operation and cause unnecessary failures.
Interaction with PortFast and Edge Design Principles
BPDU Guard is most commonly deployed alongside PortFast, and understanding their relationship is critical for correct configuration. PortFast is designed to accelerate the transition of edge ports into forwarding mode, bypassing the usual spanning tree listening and learning states.
However, this speed introduces a potential risk if a switch is mistakenly connected to a PortFast-enabled port. Without protection, such a device could begin participating in spanning tree operations and potentially disrupt the network topology.
BPDU Guard eliminates this risk by acting as a safety mechanism. If a switch is connected to a PortFast-enabled port, it will immediately send BPDU messages. BPDU Guard detects this behavior and disables the port instantly, preventing any further impact on the network.
This combination ensures that PortFast can safely improve performance without compromising network stability.
Designing a Secure Access Layer with BPDU Guard
A well-designed access layer assumes that all connected devices are untrusted from a switching perspective. This does not mean users are untrusted in terms of security access, but rather that their devices should not influence network topology decisions.
BPDU Guard enforces this principle by ensuring that access ports remain strictly non-participatory in Spanning Tree Protocol. This design philosophy simplifies network management because administrators can confidently assume that edge devices will never affect core switching behavior.
This separation of responsibilities between access and infrastructure devices is one of the key reasons why modern networks remain stable even in large-scale deployments. BPDU Guard acts as a reinforcing layer that ensures this separation is maintained at all times.
Common Configuration Mistakes and Their Impact
Despite its simplicity, BPDU Guard can be misconfigured, leading to unintended network disruptions. One common mistake is enabling BPDU Guard on inter-switch links. Since switches exchange BPDU messages as part of normal operation, enabling BPDU Guard on these links causes immediate port shutdowns and network outages.
Another frequent issue occurs when administrators forget to enable PortFast alongside BPDU Guard on access ports. While BPDU Guard will still function, the lack of PortFast may result in slower convergence times for end devices, reducing overall efficiency.
Misunderstanding the role of BPDU Guard can also lead to inconsistent deployment, where some access ports are protected while others are left unprotected. This inconsistency can create security gaps in the network edge.
Operational Impact During Network Events
In active networks, BPDU Guard plays a silent but important role in maintaining stability. During normal operation, it does not generate traffic or require continuous monitoring. However, during network changes or device additions, its behavior becomes highly visible.
If a user connects an unauthorized switch or misconfigured device to an access port, BPDU Guard immediately reacts by disabling the port. This prevents the device from influencing the spanning tree topology and isolates the issue at the edge rather than allowing it to propagate through the network.
This immediate containment is critical in large networks, where even a single misconfigured device could potentially affect multiple switches if left unchecked.
Administrative Control and Recovery Process
When BPDU Guard disables a port, the event is not automatically reversed. This intentional design requires network administrators to manually investigate and resolve the issue before restoring connectivity.
The recovery process typically involves identifying the connected device, verifying its configuration, and ensuring that it complies with network design standards. Once the issue is resolved, the administrator must manually re-enable the port.
This manual intervention ensures that the cause of the violation is addressed rather than simply bypassed. It also provides an opportunity to review network security posture and identify potential weaknesses in physical or logical design.
Scalability of BPDU Guard in Large Networks
In large-scale enterprise environments, BPDU Guard scales effectively because it operates locally on each switch port without requiring centralized coordination. This decentralized operation ensures that each switch independently enforces protection at its edge interfaces.
As networks grow, maintaining consistent configuration becomes more important. Automated configuration tools and standardized templates are often used to ensure that BPDU Guard is consistently applied across all access layer switches.
This scalability makes BPDU Guard suitable for environments ranging from small office networks to large data centers, as long as it is properly integrated into the overall design strategy.
Foundation of a Secure Switching Environment
BPDU Guard forms an essential part of a secure switching environment by reinforcing the boundaries between trusted infrastructure and untrusted endpoints. Its configuration and deployment must align with broader network design principles to ensure maximum effectiveness.
When implemented correctly, it provides a strong defensive layer that prevents unauthorized participation in spanning tree operations while maintaining smooth network performance for legitimate users.
BPDU Guard – Troubleshooting, Best Practices, and Real-World Network Reliability
BPDU Guard is designed to simplify network protection, but in real environments, administrators still need to understand how to troubleshoot its behavior and maintain consistent network reliability. Since BPDU Guard directly affects port states, its impact is often visible when issues occur. A well-prepared network engineer must be able to quickly identify when BPDU Guard is responsible for connectivity loss and respond appropriately without disrupting the overall network design.
In operational networks, BPDU Guard issues usually appear as sudden loss of connectivity on specific ports. Unlike general performance degradation, BPDU Guard does not gradually slow down traffic. Instead, it completely disables the affected interface when a violation is detected. This makes troubleshooting more straightforward because the problem is isolated rather than distributed across the network.
Identifying BPDU Guard-Induced Port Failures
When BPDU Guard is triggered, the affected port enters an error-disabled state. From a user perspective, this appears as an immediate network outage on that connection. Devices connected to that port lose all communication without prior warning.
To identify such issues, network administrators rely on switch-level diagnostic commands that display port status. These outputs clearly indicate which interfaces are in an error-disabled condition. Since BPDU Guard is one of the common reasons for this state, it becomes one of the first features to investigate during troubleshooting.
Once a problematic port is identified, the next step is determining the cause of the violation. In most cases, this involves checking whether an unauthorized switching device has been connected or whether a misconfigured endpoint is generating BPDU traffic unintentionally.
Understanding Root Causes of BPDU Guard Activation
BPDU Guard is not triggered randomly; it activates only when BPDU messages are detected on a port where they are not expected. This means every activation has a clear underlying cause that must be identified and corrected.
One common cause is the accidental connection of a small unmanaged switch. These devices often have built-in switching logic that sends BPDU messages as part of their normal operation. When connected to an access port with BPDU Guard enabled, they immediately violate the expected behavior.
Another cause is misconfigured network equipment. For example, a wireless access point or network extender may have switching capabilities enabled, causing it to transmit BPDU messages unintentionally. Even though the device is not malicious, its behavior is still considered a violation in a controlled network environment.
In rare cases, intentional attempts to influence network topology can also trigger BPDU Guard. However, most real-world incidents are caused by configuration errors rather than security attacks.
Recovery Process After BPDU Guard Shutdown
When a port is placed into an error-disabled state, it does not recover automatically. This behavior is intentional and ensures that the underlying issue is properly addressed before restoring connectivity.
The recovery process begins with physical and logical inspection of the connected device. Administrators verify whether the device is allowed on the network and whether it complies with access layer policies. If the device is unauthorized, it is removed or relocated to an appropriate network segment.
If the device is legitimate but misconfigured, its settings are corrected to ensure it does not send BPDU messages. Once the root cause is resolved, the administrator manually re-enables the port. This manual step ensures that the network does not automatically reintroduce a potentially harmful configuration.
This controlled recovery process is one of the reasons BPDU Guard is considered a strong security feature. It forces administrative validation before restoring connectivity, reducing the risk of repeated violations.
Best Practices for BPDU Guard Implementation
Proper use of BPDU Guard requires careful planning and adherence to best practices. One of the most important guidelines is ensuring that it is only enabled on access layer ports. These are the ports that connect directly to end-user devices and should never participate in Spanning Tree Protocol communication.
Another best practice is combining BPDU Guard with PortFast. This combination ensures that edge ports transition quickly into forwarding mode while still being protected against unauthorized BPDU traffic. Without this pairing, networks may either become slower or less secure depending on configuration.
Consistency is also critical. In large networks, BPDU Guard should be applied uniformly across all access switches. Inconsistent configuration can create weak points where unauthorized devices may bypass protection mechanisms.
Additionally, administrators should maintain clear documentation of which ports are expected to be protected. This helps during troubleshooting and reduces confusion when investigating error-disabled interfaces.
Avoiding Misconfiguration in Complex Network Environments
One of the most significant risks associated with BPDU Guard is misconfiguration. Applying it to the wrong type of port can cause unintended network outages. For example, enabling BPDU Guard on links between switches can immediately disrupt network connectivity because these links naturally exchange BPDU messages as part of normal operation.
To avoid such issues, network design must clearly define port roles before configuration is applied. Access ports, trunk links, and inter-switch connections must be properly categorized so that BPDU Guard is only applied where appropriate.
In complex environments, automation tools are often used to enforce configuration consistency. These tools reduce human error and ensure that BPDU Guard is applied only to designated edge interfaces.
BPDU Guard in High-Security Network Environments
In high-security environments such as enterprise data centers, financial institutions, or government networks, BPDU Guard becomes part of a broader defense strategy. It works alongside other security features to protect both data flow and network structure.
While other security mechanisms focus on authentication, encryption, and traffic filtering, BPDU Guard specifically protects the structural integrity of the network. This makes it a unique and essential component of Layer 2 security.
In such environments, even a single unauthorized switch connection can pose a significant risk. BPDU Guard ensures that these risks are contained immediately at the point of entry, preventing escalation into larger network issues.
Long-Term Network Stability and Operational Benefits
Over time, the use of BPDU Guard contributes significantly to network stability. By preventing unauthorized devices from participating in spanning tree operations, it reduces the likelihood of topology disruptions and broadcast storms.
This stability is especially important in networks with frequent device changes or large numbers of user connections. Since BPDU Guard automatically enforces rules at the edge, administrators do not need to manually monitor every connected device for compliance.
The feature also improves incident response time. Because BPDU Guard clearly identifies when a violation has occurred by disabling a port, troubleshooting becomes more focused and efficient. Instead of searching through complex network logs, administrators can quickly isolate the affected interface.
Integration with Broader Network Security Strategy
BPDU Guard is most effective when used as part of a layered security approach. While it protects against spanning tree manipulation, it does not address other network threats such as IP spoofing or unauthorized DHCP servers.
For this reason, it is commonly used alongside other features that protect different aspects of network operation. Each feature addresses a specific layer of risk, and together they form a comprehensive security model.
This layered approach ensures that even if one protection mechanism is bypassed or misconfigured, others remain active to maintain network integrity.
Final Conclusion
BPDU Guard remains one of the most practical and widely used security features in switching environments. Its strength lies in its simplicity and decisive action. By immediately disabling ports that receive unexpected BPDU traffic, it prevents potential disruptions before they can affect the broader network.
When properly configured and consistently applied, it enhances both security and operational stability. It ensures that only authorized infrastructure devices participate in Spanning Tree Protocol while keeping edge devices safely isolated.
Its role in modern networking continues to be essential, especially as networks grow in size, complexity, and exposure to diverse device types.