Network Address Translation (NAT) is a core networking technique that allows multiple devices inside a local network to communicate with the internet using a single public IP address. It acts as a bridge between private internal networks and the wider internet, ensuring efficient use of limited IP resources while maintaining organization and control over network traffic. There are three main NAT types—Open, Moderate, and Strict—each designed for different levels of accessibility, performance, and security depending on the situation.
Understanding NAT and Its Purpose
NAT plays a vital role in modern networking environments, whether in homes, offices, or large enterprise systems. At its core, NAT solves a major limitation of the internet: the shortage of public IP addresses. Since billions of devices need internet access but only a limited number of public IP addresses are available, NAT allows many devices to share a single public identity when communicating externally.
Inside a local network, each device is assigned a private IP address. These private addresses are not directly accessible from the internet and are used only within the local environment. When a device attempts to connect to an external server, NAT translates the private IP address into a public IP address before sending the request out. This process ensures that communication between internal devices and external servers remains seamless and properly routed.
NAT is not just about address translation; it also adds a layer of organization to network communication. By managing how traffic flows between internal and external networks, NAT ensures that data reaches the correct destination even when multiple devices are making requests simultaneously. Without NAT, the complexity of managing direct connections for each device would be overwhelming, and the available IP space would be quickly exhausted.
Public and Private IP Addressing Explained
To fully understand NAT, it is essential to grasp the difference between public and private IP addresses. A public IP address is assigned to a network by an internet service provider and is visible across the internet. This address acts as the identity of a network when it communicates with external servers and services.
On the other hand, private IP addresses are used within local networks and are not visible to the outside world. These addresses are assigned to devices such as computers, smartphones, printers, and smart home devices. Common private IP ranges are reserved specifically for internal use, allowing networks to reuse the same address ranges without conflict.
When a device inside a network sends a request to the internet, NAT translates its private IP into the public IP of the router. This translation allows the request to travel across the internet and reach its destination. When the response comes back, NAT reverses the process, ensuring the data is delivered to the correct device within the local network.
This system allows dozens or even hundreds of devices to share a single public IP address efficiently. It also simplifies network management and reduces the need for complex configurations on individual devices.
How NAT Works in Real-Time Communication
When a device initiates a connection to an external server, NAT performs several key operations to ensure proper communication. First, it records the source IP address of the device, which is typically a private IP. Then, it notes the source port, which is randomly assigned by the operating system for that specific connection.
Next, NAT identifies the destination IP address and port, which correspond to the server being accessed. For example, secure web traffic commonly uses port 443. NAT then replaces the private IP and port information with the public IP of the router and a mapped port number. This modified request is sent to the internet.
When the server responds, the data is sent back to the router’s public IP and the mapped port. NAT uses its internal tracking table to determine which device originally made the request. It then translates the response back to the device’s private IP and original port, ensuring the communication is completed successfully.
This process happens almost instantly and is repeated continuously for every active connection. NAT must keep track of numerous connections at once, especially in networks with many active devices. Its ability to manage these connections efficiently is what makes it such a critical component of modern networking.
The Importance of NAT in Network Efficiency
NAT significantly improves network efficiency by reducing the number of public IP addresses required. Instead of assigning a unique public IP to every device, a single address can represent an entire network. This approach conserves IP resources and allows more devices to connect to the internet without requiring additional infrastructure.
Another important benefit of NAT is its ability to streamline traffic management. By centralizing external communication through a router, NAT simplifies how data flows between devices and the internet. This centralization makes it easier to monitor, control, and troubleshoot network activity.
NAT also enables flexibility in network design. Organizations can structure their internal networks however they choose, using private IP ranges without worrying about conflicts with external networks. This flexibility is especially useful in large environments where multiple subnetworks may exist.
Security Advantages of NAT
Although NAT is not primarily a security feature, it does provide certain protective benefits. One of the most notable advantages is that it hides internal IP addresses from external networks. Since devices inside the network are not directly exposed to the internet, it becomes more difficult for unauthorized users to target them.
NAT also helps control incoming traffic. In most cases, only responses to outgoing requests are allowed back into the network. This means that unsolicited connection attempts from external sources are typically blocked unless specific configurations are in place.
This behavior acts as a basic barrier against certain types of attacks. However, it is important to note that NAT should not be relied upon as a replacement for dedicated security measures such as firewalls and intrusion detection systems. Instead, it should be viewed as an additional layer that complements other security strategies.
Challenges and Limitations of NAT
Despite its many benefits, NAT does come with some limitations. One of the primary challenges is that it can interfere with certain types of applications, especially those that require direct inbound connections. Examples include online gaming, video conferencing, and peer-to-peer file sharing.
These applications often need specific ports to remain open so that external servers can initiate connections back to the device. Without proper configuration, NAT may block these incoming connections, leading to performance issues or connectivity problems.
Another limitation is the added complexity in network troubleshooting. Since NAT modifies IP addresses and ports, it can sometimes make it more difficult to trace the path of network traffic. Network administrators must understand how NAT mappings work in order to diagnose and resolve issues effectively.
Additionally, NAT can introduce slight delays in communication due to the translation process. While these delays are usually negligible, they can become noticeable in scenarios that require real-time data exchange.
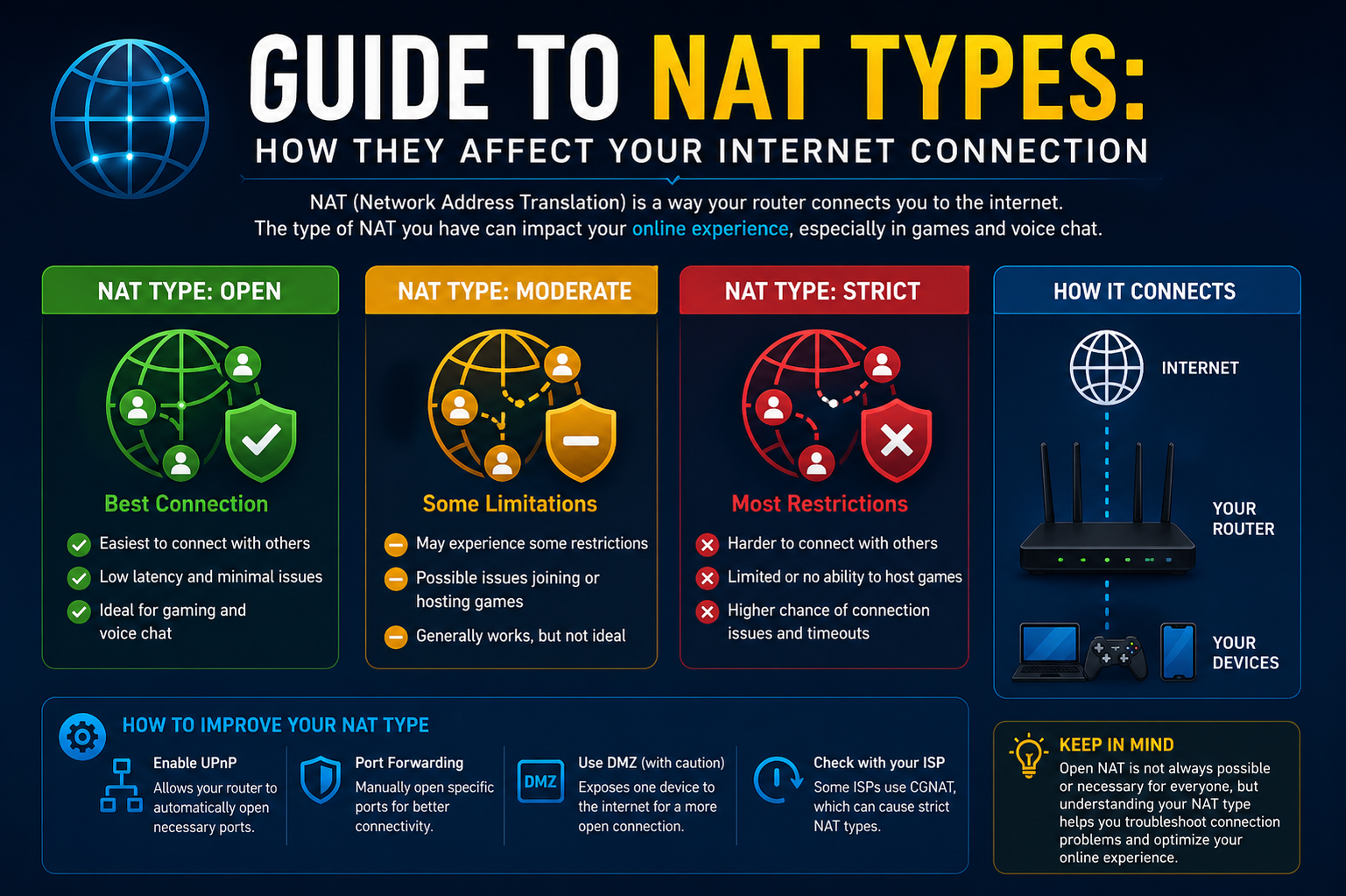
Introduction to NAT Types
NAT types define how open or restrictive a network is when handling communication between internal devices and external systems. These types determine how easily devices can establish connections, particularly when external servers attempt to initiate communication.
The three primary NAT types are Open NAT, Moderate NAT, and Strict NAT. Each type represents a different level of accessibility and security, making them suitable for different use cases. Understanding these types is essential for optimizing network performance and ensuring compatibility with various applications.
Different devices within the same network can sometimes operate under different NAT types, depending on how the router is configured. This flexibility allows users to tailor their network settings to meet specific requirements, such as improving gaming performance or enhancing security.
Why NAT Types Matter in Everyday Use
NAT types play a significant role in determining how well certain applications function. For example, online gaming often requires seamless communication between players and game servers. If the NAT type is too restrictive, it can prevent connections from being established, resulting in lag, disconnections, or limited multiplayer functionality.
Streaming services, voice calls, and remote access tools can also be affected by NAT behavior. In some cases, improper NAT configuration can lead to reduced quality or interrupted connections.
By understanding NAT types, users can make informed decisions about how to configure their networks. This knowledge allows them to strike a balance between performance and security, ensuring that their network operates efficiently while still protecting sensitive data.
Transition Toward NAT Type Differences
As networks continue to evolve, the importance of understanding NAT types becomes even more apparent. Each type offers unique characteristics that influence how data flows between devices and the internet. Some prioritize performance and accessibility, while others focus on security and control.
Understanding NAT Type Behavior in Networks
NAT types are essentially classifications that describe how a router handles incoming and outgoing traffic between a private network and the internet. While the basic function of NAT remains the same—translating private IP addresses into a public one—the way it manages connections can vary significantly. These variations directly impact how devices communicate, especially in situations where two-way communication is required.
In most cases, NAT is designed to allow internal devices to initiate connections outward while restricting unsolicited incoming traffic. However, depending on the NAT type, this restriction can be relaxed or tightened. This behavior becomes particularly important for applications that rely on real-time communication, such as online gaming, voice calls, and remote desktop access.
Understanding NAT types is not just about technical knowledge; it is about recognizing how different configurations affect user experience. A more open NAT type allows smoother and faster communication, while a stricter NAT type enhances security but may limit connectivity.
What is Open NAT
Open NAT is the least restrictive NAT type and provides the highest level of connectivity between a device and the internet. In this configuration, the device can send and receive data without significant interference from the router. It allows both outbound and inbound connections to flow freely, making it ideal for applications that require direct communication.
With Open NAT, external servers and devices can initiate connections back to the internal device without being blocked. This behavior creates an environment where communication is fast, stable, and reliable. As a result, Open NAT is often considered the best option for performance-critical tasks.
This type of NAT is commonly used in scenarios where low latency and uninterrupted communication are essential. For example, online multiplayer games benefit greatly from Open NAT because they rely on constant data exchange between players and servers. Any delay or restriction in communication can negatively impact gameplay.
How Open NAT is Configured
Open NAT can be achieved through specific router configurations that reduce or eliminate restrictions on incoming traffic. One common method is port forwarding, which allows certain ports to remain open and directs incoming traffic to a specific device within the network.
Port forwarding works by mapping a particular port on the router to a private IP address inside the network. When data arrives at that port, the router knows exactly which device should receive it. This eliminates the need for dynamic translation in those cases, resulting in faster and more predictable communication.
Another method sometimes used is placing a device in a demilitarized zone, often referred to as a DMZ. In this setup, the selected device is exposed directly to the internet with minimal protection from the router. While this can achieve Open NAT, it significantly reduces security and should be used with caution.
Most users prefer port forwarding because it provides the benefits of Open NAT while still maintaining some level of control over which ports are accessible.
Advantages of Open NAT
The primary advantage of Open NAT is its ability to deliver optimal performance. Since there are minimal restrictions on data flow, communication between devices and external servers is smooth and efficient. This is especially important for applications that depend on real-time interaction.
Open NAT also improves compatibility with a wide range of services. Devices operating under this NAT type can connect easily with others, regardless of their network configurations. This makes it easier to establish peer-to-peer connections and reduces the likelihood of connectivity issues.
Another benefit is reduced latency. Because data does not need to pass through complex filtering or translation processes, it can travel more quickly between the device and the internet. This results in faster response times and a better overall user experience.
Security Considerations of Open NAT
While Open NAT offers excellent performance, it comes with certain security risks. By allowing incoming connections from external sources, it increases the exposure of the device to potential threats. Without proper safeguards, this openness can make the device more vulnerable to attacks.
For example, if a device is placed in a DMZ, it may not benefit from the router’s firewall or filtering mechanisms. This means that any malicious traffic from the internet could potentially reach the device directly.
Even with port forwarding, there is still some level of risk. Opening specific ports creates entry points that could be exploited if not properly managed. It is important to ensure that only necessary ports are opened and that devices are protected with up-to-date security measures.
Balancing performance and security is crucial when using Open NAT. While it provides significant advantages for certain applications, it should be configured carefully to minimize potential risks.
Use Cases for Open NAT
Open NAT is particularly useful in environments where performance and connectivity are top priorities. One of the most common use cases is online gaming, where players need to communicate with servers and other players in real time.
In gaming, Open NAT allows for smoother matchmaking, faster connection times, and fewer interruptions during gameplay. It also reduces the chances of being unable to join multiplayer sessions due to network restrictions.
Another use case is video conferencing and voice communication. These applications require consistent and reliable data exchange to maintain high-quality audio and video streams. Open NAT helps ensure that connections remain stable and free from interruptions.
Remote access tools can also benefit from Open NAT. When users need to connect to their devices from outside the network, having fewer restrictions makes the process more straightforward and efficient.
Limitations of Open NAT
Despite its advantages, Open NAT is not always the best choice for every situation. Its primary limitation is the reduced level of security compared to other NAT types. In environments where data protection is critical, a more restrictive approach may be necessary.
Open NAT also requires manual configuration in many cases. Setting up port forwarding or DMZ correctly can be complex, especially for users who are not familiar with networking concepts. Incorrect configurations can lead to connectivity issues or increased security risks.
Additionally, not all networks or service providers support full Open NAT configurations. In some cases, external factors such as upstream network restrictions may prevent users from achieving this NAT type.
Comparing Open NAT with Other NAT Types
Open NAT stands out for its accessibility and performance, but it differs significantly from Moderate and Strict NAT types. While Open NAT allows nearly unrestricted communication, the other types introduce varying levels of control and filtering.
Moderate NAT, for example, still allows outbound connections freely but restricts unsolicited incoming traffic. This creates a balance between usability and security. Strict NAT, on the other hand, enforces tight restrictions on both incoming and outgoing connections, prioritizing security over convenience.
Understanding these differences helps users choose the right NAT type based on their needs. For high-performance applications, Open NAT is often preferred. For general use, Moderate NAT provides a balanced approach. For sensitive environments, Strict NAT offers stronger protection.
Transition Toward Moderate NAT
After exploring Open NAT, it becomes clear that while it provides excellent performance, it may not always be the most practical or secure option. Many users require a balance between accessibility and protection, which is where Moderate NAT comes into play.
Moderate NAT represents a middle ground, offering reliable performance while maintaining a reasonable level of security. It is the most commonly used NAT type in everyday networks and serves as the default configuration for many routers.
What is Moderate NAT
Moderate NAT is the most commonly used NAT type and is considered the default configuration in many home and office networks. It provides a balanced approach between accessibility and security, allowing devices to communicate efficiently with the internet while still maintaining protective restrictions against unwanted incoming traffic.
In this setup, devices inside the network can freely initiate connections to external servers. When a request is sent, NAT translates the private IP address and assigns a mapped port, allowing the communication to proceed. When the response comes back, the router uses its translation table to deliver the data to the correct device. However, unlike Open NAT, Moderate NAT does not allow external devices to initiate connections unless a prior connection exists.
This behavior ensures that communication remains smooth for most everyday activities while preventing unauthorized access attempts from the outside. Because of this balance, Moderate NAT is widely used and recommended for general networking needs.
How Moderate NAT Handles Traffic
Moderate NAT operates by dynamically managing connections between internal devices and external servers. When a device sends a request, the router records the details of that connection, including the private IP address and port number. It then translates this information into the public IP and a corresponding port before forwarding the request to the internet.
When the external server responds, the router checks its internal records to match the incoming data with the original request. If a match is found, the data is translated back to the private IP address and delivered to the correct device. This process allows multiple devices to share a single public IP address without confusion.
However, if an external device attempts to initiate a connection without an existing record, the router typically blocks the request. This is because Moderate NAT does not automatically allow unsolicited inbound traffic. This restriction helps maintain security while still supporting most common applications.
Why Moderate NAT is Widely Used
Moderate NAT is popular because it offers a practical balance between performance and protection. Most internet activities, such as browsing, streaming, and downloading, rely on outbound connections initiated by the user. Moderate NAT handles these tasks efficiently without requiring additional configuration.
Another reason for its widespread use is simplicity. Most routers are preconfigured to operate in this mode, meaning users do not need to make manual adjustments to get started. This makes it an ideal choice for people who want reliable network performance without dealing with complex settings.
Moderate NAT also works well in environments with multiple devices. Whether it is a household with smartphones and laptops or an office with numerous workstations, this NAT type can manage simultaneous connections effectively.
Performance Characteristics of Moderate NAT
In terms of performance, Moderate NAT delivers consistent and reliable results for most applications. Since it allows outbound connections without restriction, users can access websites, stream media, and use online services without noticeable delays.
For applications that require two-way communication, such as online gaming or video calls, Moderate NAT generally performs well but may occasionally introduce limitations. For example, certain multiplayer games may require specific ports to be open for optimal connectivity. Without these configurations, users might experience longer matchmaking times or reduced compatibility with other players.
Despite these minor limitations, Moderate NAT is sufficient for the majority of users. It provides a stable connection without exposing devices to unnecessary risks.
Security Benefits of Moderate NAT
One of the key advantages of Moderate NAT is its ability to enhance network security. By blocking unsolicited incoming connections, it reduces the likelihood of unauthorized access attempts. External devices cannot directly connect to internal systems unless a connection has already been established from within the network.
This behavior acts as a basic filtering mechanism, preventing many types of unwanted traffic from reaching internal devices. While it is not a substitute for a dedicated firewall, it does provide an additional layer of protection.
Moderate NAT also helps isolate devices within the network. Since internal IP addresses are not exposed to the outside world, it becomes more difficult for attackers to identify and target specific devices. This level of privacy adds another layer of defense against potential threats.
Limitations of Moderate NAT
Although Moderate NAT is suitable for most scenarios, it does have some limitations. The primary drawback is that it can restrict certain types of incoming connections. Applications that rely on direct peer-to-peer communication may not function optimally without additional configuration.
For example, in online gaming, players using Moderate NAT may have difficulty connecting with others who are using Strict NAT. This can limit matchmaking options and affect the overall gaming experience.
Another limitation is that some advanced features, such as hosting servers or remote access services, may require manual port forwarding to work properly. Without these adjustments, the router will block incoming requests, preventing external users from connecting.
These limitations are generally manageable and do not affect everyday usage for most people. However, users with specific requirements may need to modify their network settings to achieve the desired functionality.
Moderate NAT in Real-World Scenarios
In a typical home network, Moderate NAT is more than sufficient for daily activities. Users can browse the internet, stream videos, participate in video calls, and play online games without significant issues. The built-in balance of accessibility and security makes it a practical choice for households with multiple devices.
In office environments, Moderate NAT also proves to be effective. Employees can access online resources, communicate with clients, and use cloud-based applications without interruption. At the same time, the network remains protected from unauthorized external access.
For users who occasionally need more open connectivity, such as gamers or remote workers, Moderate NAT can be adjusted with port forwarding to accommodate specific needs. This flexibility allows it to adapt to a wide range of use cases.
Comparing Moderate NAT with Open NAT
When compared to Open NAT, Moderate NAT offers a more secure but slightly less flexible approach. Open NAT allows unrestricted communication, making it ideal for performance-intensive applications. However, it exposes devices to greater risk.
Moderate NAT, on the other hand, limits incoming connections while still supporting most outbound communication. This makes it a safer option for general use. While it may not provide the same level of performance for certain applications, it strikes a better balance for everyday networking.
Users who prioritize security and simplicity often prefer Moderate NAT, while those who require maximum performance may opt for Open NAT with careful configuration.
Transition Toward Strict NAT
While Moderate NAT provides a balanced solution for most users, some environments require even tighter control over network traffic. In situations where security is a top priority, a more restrictive approach is necessary.
Strict NAT represents the highest level of restriction among the three NAT types. It is designed to limit communication to only what is explicitly allowed, ensuring that networks remain secure even in sensitive environments. In the next part, the focus will shift to understanding how Strict NAT works and when it should be used.
What is Strict NAT
Strict NAT is the most restrictive NAT type and is primarily designed for environments where security is the highest priority. In this configuration, the router enforces tight control over both incoming and outgoing traffic, allowing only very specific types of communication to pass through. Unlike Open and Moderate NAT, Strict NAT does not easily permit external devices to establish connections with internal systems.
With Strict NAT, a device can initiate outbound connections, but the response is only allowed if it strictly matches the original request and predefined rules. Any unexpected or unsolicited traffic is automatically blocked. This creates a highly controlled communication environment where only approved data flows are permitted.
This level of restriction makes Strict NAT suitable for networks that handle sensitive data or require strict compliance with security policies. While it may limit certain functionalities, it significantly reduces the risk of unauthorized access.
How Strict NAT Controls Network Traffic
Strict NAT works by applying strict filtering rules to all network traffic. When a device inside the network sends a request, the router creates a translation entry similar to other NAT types. However, the difference lies in how incoming responses are handled.
Only responses that exactly match the original request are allowed back into the network. If there is any deviation—such as a different port or an unexpected source—the router blocks the traffic. This ensures that only verified and expected communication is permitted.
Additionally, Strict NAT often restricts the range of ports that can be used for communication. Network administrators may define specific ports that are allowed, while all others remain closed. This approach minimizes the number of potential entry points for external threats.
Because of these controls, Strict NAT creates a tightly secured environment where every connection is carefully monitored and regulated.
Security Advantages of Strict NAT
The primary strength of Strict NAT lies in its enhanced security. By blocking nearly all unsolicited incoming traffic, it significantly reduces the attack surface of the network. External entities cannot easily initiate connections, making it more difficult for malicious actors to exploit vulnerabilities.
Strict NAT is particularly useful in environments where data protection is critical. Organizations that handle confidential information often rely on strict network controls to prevent unauthorized access. By limiting communication to only approved channels, Strict NAT helps maintain data integrity and confidentiality.
Another advantage is improved control over network usage. Administrators can define exactly which services and ports are allowed, ensuring that only necessary communication takes place. This level of control is essential for maintaining secure and compliant systems.
Limitations and Challenges of Strict NAT
While Strict NAT provides strong security benefits, it also introduces several limitations. The most noticeable drawback is reduced connectivity. Many modern applications rely on flexible communication methods, including peer-to-peer connections and dynamic port usage. Strict NAT can interfere with these processes, leading to connectivity issues.
For example, online gaming often requires devices to accept incoming connections from other players or servers. Under Strict NAT, these connections are typically blocked, resulting in difficulty joining games or communicating with other players.
Similarly, video conferencing and voice communication tools may experience disruptions if the required ports are not explicitly allowed. This can lead to reduced quality or failed connections.
Another challenge is the need for manual configuration. To enable certain applications, administrators may need to define specific rules or open particular ports. This process can be complex and requires a good understanding of networking concepts.
Because of these limitations, Strict NAT is not always suitable for general-purpose networks. It is best used in scenarios where security outweighs the need for unrestricted connectivity.
Strict NAT in High-Security Environments
Strict NAT is commonly used in environments where security is non-negotiable. This includes corporate networks, financial institutions, and systems that manage sensitive or regulated data. In such cases, the priority is to prevent unauthorized access, even if it means limiting certain functionalities.
In these environments, network administrators carefully design NAT rules to allow only essential communication. For example, web traffic may be restricted to secure ports, while all other connections are blocked. This ensures that the network remains protected from potential threats.
Strict NAT is also useful in controlled systems where devices have predefined roles and do not require extensive external communication. By limiting connectivity, organizations can maintain tighter control over how data is accessed and shared.
Comparing All Three NAT Types
When comparing Open, Moderate, and Strict NAT, it becomes clear that each type serves a different purpose. Open NAT prioritizes performance and accessibility, allowing devices to communicate freely with minimal restrictions. This makes it ideal for applications that require real-time interaction and low latency.
Moderate NAT provides a balance between performance and security. It allows outbound connections while restricting unsolicited inbound traffic, making it suitable for most everyday use cases. This balance is why it is the default configuration in many networks.
Strict NAT focuses on security above all else. By enforcing strict rules and limiting communication, it creates a highly controlled environment. While this approach enhances protection, it can also reduce compatibility with certain applications.
Choosing the right NAT type depends on the specific needs of the network. Users must consider factors such as performance requirements, security concerns, and the types of applications being used.
Choosing the Right NAT Type
Selecting the appropriate NAT type involves understanding how different configurations impact both usability and security. For most home users and general office environments, Moderate NAT is the best choice. It provides reliable performance while maintaining a reasonable level of protection.
Open NAT is suitable for situations where performance is critical, such as online gaming or real-time communication. However, it should be configured carefully to avoid exposing devices to unnecessary risks.
Strict NAT is best reserved for environments where security is the primary concern. It is ideal for protecting sensitive systems but may require additional configuration to support specific applications.
In many cases, networks can be adjusted dynamically to meet changing needs. For example, a user might enable port forwarding for a gaming session and then revert to a more secure configuration afterward. This flexibility allows users to optimize their network based on current requirements.
Conclusion
Network Address Translation remains a fundamental component of modern networking, enabling efficient communication between private networks and the internet. By allowing multiple devices to share a single public IP address, it solves the challenge of limited IP resources while simplifying network management.
Understanding the three NAT types—Open, Moderate, and Strict—provides valuable insight into how network traffic is handled. Each type offers a different balance between performance, accessibility, and security. Open NAT delivers maximum connectivity, Moderate NAT offers a practical middle ground, and Strict NAT ensures strong protection through tight control.
By choosing the right NAT type for a given situation, users can optimize their network experience while maintaining the desired level of security. Whether for gaming, everyday browsing, or high-security environments, NAT plays a crucial role in shaping how devices connect and communicate in today’s digital world.