Understanding how networks function at a foundational level requires a clear grasp of the lower layers of the OSI model. Layers 1 through 3 are especially critical because they handle how data is physically transmitted, organized, and routed between devices. These layers form the backbone of all communication across modern networks, yet they are often misunderstood due to their technical nature. When studied carefully and in context, however, they reveal a logical flow that explains how information travels from one system to another.
The Role of OSI Layers in Networking
The OSI model serves as a conceptual framework that standardizes how different networking functions interact. Each layer has a specific purpose, and together they ensure that data can move reliably between devices, regardless of the underlying hardware or software. Layers 1 through 3 focus on the movement of data from the physical medium up to logical addressing and routing.
These layers are not isolated in real-world implementations. Networking protocols often span multiple layers, blending responsibilities in ways that make practical communication more efficient. Because of this, it is helpful to study these layers not just theoretically, but also in terms of how protocols like Ethernet and IP actually operate within them.
Layer 1: Physical Layer Overview
The physical layer is the starting point of all network communication. It is responsible for transmitting raw bits across a physical medium. This includes defining electrical signals, voltage levels, timing, and the physical connectors used to establish communication between devices.
At this level, data has no structure or meaning beyond binary form. It is simply a sequence of ones and zeros transmitted as electrical pulses, light signals, or radio waves. The physical layer ensures that these signals can travel from one point to another without concern for what the data represents.
Because this layer is concerned with the mechanics of transmission, it includes standards that define how cables are wired and how signals are encoded. For example, Ethernet cabling standards determine how twisted pair wires are arranged, while fiber optics rely on light pulses to carry information over long distances.
Physical Transmission Media
The physical layer encompasses a wide range of transmission media. Wired connections include copper cables, such as twisted pair Ethernet, and fiber optic cables, which are used for high-speed and long-distance communication. Wireless technologies also fall under this layer, as they rely on radio frequencies to transmit signals through the air.
Each type of medium has its own characteristics, including bandwidth, signal range, and susceptibility to interference. Copper cables are cost-effective and widely used, but they are more prone to signal degradation over long distances. Fiber optics, on the other hand, offer higher speeds and longer transmission ranges, but at a higher cost.
Wireless communication introduces additional complexity, as signals must contend with environmental factors such as obstacles, interference, and signal attenuation. Despite these challenges, wireless technologies remain essential for modern networking due to their flexibility and convenience.
Data Representation at Layer 1
At the physical layer, data exists purely as bits. These bits are encoded into signals that can be transmitted over the chosen medium. The method of encoding varies depending on the technology being used. For example, electrical signals may use voltage changes to represent binary values, while fiber optics use light pulses.
The key responsibility of this layer is to ensure that bits are transmitted accurately and efficiently. It does not interpret the data or check for errors; those responsibilities are handled by higher layers. Instead, it focuses on maintaining signal integrity and synchronization between transmitting and receiving devices.
Devices Operating at Layer 1
Devices at the physical layer are simple in design and function. They do not analyze or interpret the data they transmit. Instead, they act as conduits that carry signals from one point to another.
Examples of such devices include cables, connectors, repeaters, and hubs. A hub, for instance, simply takes an incoming signal and broadcasts it to all connected devices without any filtering or decision-making. This lack of intelligence can lead to inefficiencies, but it reflects the simplicity of the physical layer’s role.
Repeaters are another example, as they regenerate signals to extend the distance over which data can travel. Without repeaters, signals would weaken over long distances and become unreadable.
Layer 2: Data Link Layer Introduction
Moving up from the physical layer, the data link layer introduces structure and organization to the raw bits transmitted across the network. Its primary role is to ensure reliable communication between directly connected devices.
At this layer, data is grouped into units called frames. These frames include not only the payload but also additional information that helps identify the source and destination of the data. This added structure allows devices to communicate more effectively and reduces the likelihood of errors during transmission.
The data link layer operates within a limited scope, typically handling communication between devices on the same network segment. Unlike higher layers, it does not deal with long-distance routing or global addressing.
Frames and Addressing
Frames are the fundamental data units at the data link layer. Each frame contains a header that includes important information such as the source and destination addresses. These addresses are known as MAC addresses and are unique identifiers assigned to network interfaces.
The use of MAC addresses allows devices to determine whether a frame is intended for them. When a device receives a frame, it checks the destination address and processes the data only if there is a match. This helps ensure that data reaches the correct endpoint within a local network.
In addition to addressing information, frames may include error detection mechanisms such as checksums. These mechanisms help identify corrupted data and improve the reliability of communication.
Layer 2 Devices and Their Intelligence
Devices operating at the data link layer are more intelligent than those at the physical layer. They can examine frame headers and make decisions based on the information they contain.
Switches are a primary example of Layer 2 devices. They maintain tables of MAC addresses and use this information to forward frames to the appropriate destination. This targeted approach reduces unnecessary traffic and improves network efficiency.
Bridges function similarly by connecting different network segments and filtering traffic between them. Network interface cards (NICs) also operate at this layer, providing devices with their unique MAC addresses and enabling communication on the network.
Medium Access Control and Communication
One of the key responsibilities of the data link layer is controlling how devices access the shared communication medium. This is handled by the Medium Access Control (MAC) sublayer.
In traditional Ethernet networks, mechanisms such as Carrier Sense Multiple Access with Collision Detection (CSMA/CD) were used to manage access and prevent data collisions. Although modern networks have largely eliminated collisions through full-duplex communication, the concept remains important for understanding how networks evolved.
Wireless networks use a similar approach known as Collision Avoidance, which helps reduce the likelihood of interference when multiple devices attempt to transmit data simultaneously.
Logical Link Control and Protocol Interaction
The Logical Link Control (LLC) sublayer acts as a bridge between the data link layer and the network layer. It enables multiple network layer protocols to coexist and operate over the same physical medium.
This sublayer provides a level of abstraction that simplifies communication between layers. It ensures that data from different protocols can be properly identified and processed, allowing networks to support a wide range of applications and services.
While some protocols rely heavily on LLC for error handling and flow control, others, such as Ethernet, delegate these responsibilities to higher layers.
Virtual LANs and Network Segmentation
An important concept within the data link layer is the use of Virtual LANs (VLANs). VLANs allow network administrators to segment a physical network into multiple logical networks, improving security and performance.
By assigning devices to specific VLANs, it is possible to isolate traffic and reduce broadcast domains. This helps prevent unnecessary data from reaching devices that do not need it and enhances overall network efficiency.
VLAN tagging is used to differentiate traffic from different VLANs when it passes through shared network infrastructure. This tagging ensures that data is delivered to the correct segment, even when multiple VLANs share the same physical connections.
Transition from Bits to Structured Communication
The progression from Layer 1 to Layer 2 represents a shift from raw transmission to structured communication. While the physical layer focuses on sending bits, the data link layer organizes those bits into meaningful units and ensures they are delivered accurately within a local network.
This transition is critical because it lays the groundwork for more advanced networking functions. Without the organization and reliability provided by the data link layer, higher-level processes such as routing and application communication would not be possible.
As data moves through these layers, it undergoes a process known as encapsulation. Each layer adds its own headers and information, building a structured package that can be transmitted across the network. This layered approach allows each part of the system to focus on its specific role while contributing to the overall communication process.
Layer 3: Network Layer Overview
The network layer builds upon the structure introduced by the data link layer and extends communication beyond directly connected devices. Its primary purpose is to enable data to travel across multiple interconnected networks, allowing systems that are geographically distant to communicate seamlessly. This is the layer where logical addressing and routing decisions take place, making it one of the most critical components of modern networking.
Unlike Layer 2, which focuses on local delivery, the network layer is concerned with end-to-end communication across potentially vast and complex infrastructures. It determines the best path for data to travel, even when that path involves multiple intermediate devices and network segments.
Logical Addressing and IP Communication
At the core of the network layer is logical addressing. Devices are assigned IP addresses, which uniquely identify them within a network and enable communication across different networks. These addresses can be assigned manually or automatically through dynamic configuration methods.
Logical addressing differs significantly from the physical addressing used in Layer 2. While MAC addresses are typically fixed and tied to hardware, IP addresses are flexible and can change depending on the network configuration. This flexibility is what allows devices to move between networks and still maintain connectivity.
IP addressing also introduces the concept of network and host portions within an address. This structure helps routers determine where a device is located and how to forward data toward its destination. Subnetting further refines this process by dividing networks into smaller, more manageable segments.
Packets and Data Handling at Layer 3
At the network layer, data is organized into units known as packets. These packets contain both the payload and the necessary addressing information required for routing. Unlike frames in Layer 2, packets are designed to travel across multiple networks without relying on direct physical connections between source and destination.
Packets are considered stateless, meaning that each one is treated independently. Network devices do not track the overall conversation or verify whether packets arrive successfully. Instead, they focus solely on forwarding packets toward their destination based on the information available in the packet header.
This stateless nature allows for efficient and scalable communication but also means that reliability must be handled by higher layers when necessary. Some protocols ensure delivery and order, while others prioritize speed and simplicity.
Routing and Path Selection
Routing is one of the defining functions of the network layer. Routers analyze packet headers to determine the most efficient path for data to reach its destination. This process involves consulting routing tables, which contain information about available networks and the best routes to reach them.
Routing decisions can be based on various factors, including distance, network congestion, and administrative policies. Advanced routing protocols dynamically update routing tables to reflect changes in the network, ensuring that data can still be delivered even when conditions change.
The ability to route data across multiple networks is what makes the internet possible. Without the network layer, communication would be limited to devices within the same local segment.
Devices Operating at Layer 3
Routers are the primary devices associated with the network layer. They connect different networks and direct traffic between them, acting as gateways for data traveling across complex infrastructures.
In addition to traditional routers, many modern switches include Layer 3 capabilities. These devices combine the speed of switching with the intelligence of routing, allowing for efficient communication within large networks.
Firewalls can also operate at this layer by filtering traffic based on IP addresses. While more advanced firewalls analyze higher-layer information, basic filtering at the network layer remains an important security measure.
Encapsulation and Data Flow Across Layers
As data moves through the network stack, it undergoes encapsulation. At the application level, data is created and passed down through the layers. Each layer adds its own header, providing the information needed for its specific function.
By the time data reaches the network layer, it is encapsulated into a packet with logical addressing information. This packet is then passed to the data link layer, where it is further encapsulated into a frame for local delivery. Finally, the physical layer transmits the data as bits across the medium.
When the data reaches its destination, the process is reversed through decapsulation. Each layer removes its header and passes the remaining data up the stack until it reaches the application.
Interaction Between Layer 2 and Layer 3
The relationship between the data link layer and the network layer is essential for effective communication. While Layer 3 determines the destination and path of a packet, Layer 2 is responsible for delivering that packet to the next hop along the route.
This interaction is evident in how routers operate. When a router receives a frame, it removes the Layer 2 header to access the packet inside. It then examines the packet’s destination IP address, determines the next hop, and encapsulates the packet into a new frame for transmission.
Each step along the path involves this process of decapsulation and re-encapsulation. The packet remains largely unchanged, but the frame headers are updated to reflect the local network segment being used.
Broadcast Domains and Network Boundaries
One important distinction between Layer 2 and Layer 3 is how they handle broadcast traffic. In Layer 2, broadcasts are sent to all devices within the same network segment. This can lead to inefficiencies if not properly managed.
The network layer helps control broadcast traffic by dividing networks into separate broadcast domains. Routers act as boundaries that prevent broadcasts from spreading across the entire network. This segmentation improves performance and reduces unnecessary traffic.
By using logical addressing and routing, Layer 3 ensures that data is delivered only where it is needed, rather than being indiscriminately broadcast to all devices.
Error Handling and Limitations
While the network layer plays a critical role in routing and addressing, it does not guarantee reliable delivery. Packets may be lost, duplicated, or delivered out of order due to network conditions.
This limitation is by design, as it allows the network layer to remain efficient and scalable. Higher layers, particularly the transport layer, are responsible for handling reliability through mechanisms such as acknowledgments and retransmissions.
Despite this, the network layer does include basic error handling features, such as time-to-live (TTL) values that prevent packets from circulating indefinitely. These features help maintain stability within the network.
Evolution of Network Layer Protocols
Over time, network layer protocols have evolved to meet the growing demands of modern communication. While earlier protocols served specific environments, today’s networks are dominated by IP-based communication.
The widespread adoption of IP has enabled the development of a global network that connects billions of devices. Enhancements such as IPv6 address the limitations of earlier versions and provide the scalability needed for future growth.
This evolution highlights the importance of the network layer as a foundation for innovation in networking technologies.
From Local Delivery to Global Communication
The transition from Layer 2 to Layer 3 represents a shift from local communication to global connectivity. While the data link layer ensures reliable delivery within a single network, the network layer enables data to traverse multiple networks and reach distant destinations.
This capability is what allows users to access websites, send emails, and communicate across continents. The network layer acts as the bridge that connects individual networks into a unified system.
Understanding this progression is key to grasping how modern networks operate. Each layer builds upon the previous one, adding new capabilities and expanding the scope of communication.
Setting the Stage for Higher Layers
With the network layer handling addressing and routing, the foundation is set for higher layers to manage end-to-end communication, reliability, and application interaction. While Layers 1 through 3 focus on moving data across the network, the upper layers ensure that the data is delivered correctly and used effectively.
This layered approach allows for flexibility and modularity, making it possible to develop new technologies without redesigning the entire system. It is this design philosophy that has enabled networking to evolve and adapt to changing needs over time.
Layer 4: Transport Layer and Its Connection to Lower Layers
After data successfully travels through the network layer, the responsibility shifts to ensuring that communication between devices is reliable and properly managed. This is where the transport layer comes into play. While Layers 1 through 3 focus on moving data across networks, the transport layer ensures that the data arrives in a usable and organized manner.
The transport layer introduces the concept of end-to-end communication. Unlike the lower layers, which only handle delivery between immediate devices or across networks, this layer is concerned with the complete journey from the source application to the destination application. It ensures that data is delivered correctly, in the right order, and without unnecessary loss.
Two primary protocols define how this layer operates: Transmission Control Protocol (TCP) and User Datagram Protocol (UDP). Each serves a different purpose, offering either reliability or speed depending on the requirements of the application.
Reliable vs Fast Communication
TCP is designed for reliability. It establishes a connection between devices before transmitting data, ensuring that both sides are ready to communicate. Once the connection is established, TCP breaks data into segments, numbers them, and tracks their delivery. If any segment is lost or corrupted, it is retransmitted. This guarantees that data arrives intact and in the correct order.
UDP, in contrast, is connectionless and prioritizes speed over reliability. It sends data without establishing a connection and does not verify whether the data reaches its destination. This makes UDP faster and more efficient for applications where speed is more important than accuracy, such as streaming or real-time communication.
The choice between TCP and UDP depends on the needs of the application. Reliable data transfer is essential for tasks like file downloads and web browsing, while fast, low-latency communication is critical for voice and video streaming.
Segmentation and Reassembly
One of the key functions of the transport layer is segmentation. Large pieces of data are divided into smaller segments before being transmitted. This makes it easier to manage data transfer and reduces the impact of errors.
Each segment is assigned a sequence number, which allows the receiving device to reassemble the data in the correct order. This process ensures that even if segments arrive out of order, the original message can still be reconstructed accurately.
Segmentation also improves efficiency by allowing multiple segments to be transmitted simultaneously. This parallelism speeds up data transfer and makes better use of available network resources.
Flow Control and Error Management
The transport layer is responsible for managing the flow of data between devices. Flow control mechanisms ensure that a sender does not overwhelm a receiver with too much data at once. This is particularly important in networks where devices may have different processing capabilities.
Error detection and correction are also handled at this layer. TCP uses acknowledgments to confirm that data has been received successfully. If an acknowledgment is not received within a certain timeframe, the data is retransmitted.
These mechanisms provide a level of reliability that is not present in the lower layers. While the network layer focuses on delivering packets, the transport layer ensures that those packets are complete and usable.
Ports and Application Identification
Another important feature of the transport layer is the use of port numbers. Ports allow multiple applications on a single device to communicate over the network simultaneously.
Each segment includes a source and destination port number, which identifies the application responsible for sending or receiving the data. This enables a single device to handle multiple network connections without confusion.
For example, web traffic typically uses one port, while email and file transfers use others. This separation ensures that data is directed to the correct application.
Layer 5: Session Layer Overview
The session layer builds on the reliability provided by the transport layer by managing communication sessions between applications. A session represents an ongoing exchange of data between two systems.
This layer is responsible for establishing, maintaining, and terminating these sessions. It ensures that communication remains organized and that data is exchanged in a structured manner.
While modern protocols often incorporate session management into other layers, the concept remains important for understanding how long-lived communications are handled.
Session Control and Synchronization
The session layer introduces mechanisms for controlling dialogue between devices. It determines whether communication occurs in one direction at a time or in both directions simultaneously.
Synchronization points, also known as checkpoints, are another key feature. These allow a session to resume from a specific point if it is interrupted. This is particularly useful for large data transfers, where restarting from the beginning would be inefficient.
By managing these aspects of communication, the session layer helps ensure that data exchanges are consistent and reliable.
Layer 6: Presentation Layer Functions
The presentation layer focuses on how data is formatted and represented. It acts as a translator between the application layer and the lower layers, ensuring that data is in a format that can be understood by both the sender and receiver.
This layer handles tasks such as data encoding, compression, and encryption. These processes transform raw data into a form suitable for transmission and then convert it back into its original format upon receipt.
Data Formatting and Compatibility
Different systems may use different data formats, which can create compatibility issues. The presentation layer resolves these differences by standardizing how data is represented.
For example, it may convert text between character encoding formats or adjust data structures to ensure consistency. This allows applications running on different platforms to communicate without errors.
Encryption and Security
Security is another important responsibility of the presentation layer. Encryption techniques are used to protect data as it travels across the network, ensuring that only authorized parties can access it.
When data is encrypted, it is transformed into an unreadable format. The receiving system then decrypts it, restoring the original information. This process helps safeguard sensitive data from unauthorized access.
Compression is also handled here, reducing the size of data to improve transmission efficiency. Smaller data sizes mean faster transfer times and reduced bandwidth usage.
Layer 7: Application Layer and User Interaction
The application layer is the highest level of the OSI model and is the closest to the end user. It provides the interface through which applications interact with the network.
This layer includes protocols that enable common network services, such as web browsing, email, and file sharing. It does not refer to the applications themselves, but rather to the protocols that support their communication.
Application Services and Protocols
Protocols at this layer define how data is requested and delivered. They provide the rules that applications follow when communicating over a network.
For example, when a user accesses a website, the application layer protocol handles the request and response process. Similarly, email and file transfer services rely on their own protocols to manage communication.
These protocols ensure that data is exchanged in a consistent and predictable manner, allowing different systems to work together seamlessly.
User Experience and Network Interaction
From the user’s perspective, the application layer is where networking becomes visible. It enables interactions such as loading web pages, sending messages, and accessing remote resources.
Despite its visibility, the application layer depends heavily on the lower layers to function correctly. Without the physical transmission, framing, routing, and transport mechanisms provided by Layers 1 through 4, application-level communication would not be possible.
This interdependence highlights the importance of the entire OSI model. Each layer contributes to the overall process, ensuring that data can move efficiently from one system to another.
Bringing All Layers Together
The OSI model is designed to break down complex networking processes into manageable components. Each layer has a specific role, and together they create a system that is both flexible and robust.
Layers 1 through 3 handle the movement of data across networks, while Layers 4 through 7 ensure that the data is delivered correctly and used effectively. This division of responsibilities allows for easier troubleshooting, development, and optimization.
Understanding how these layers interact provides valuable insight into how networks operate. It also helps in diagnosing issues, as problems can often be traced back to a specific layer.
As data travels from one device to another, it passes through each layer, undergoing encapsulation and decapsulation along the way. This process ensures that all necessary information is included and that data can be transmitted and received accurately.
By mastering these concepts, it becomes much easier to understand the complexities of modern networking and the technologies that rely on it.
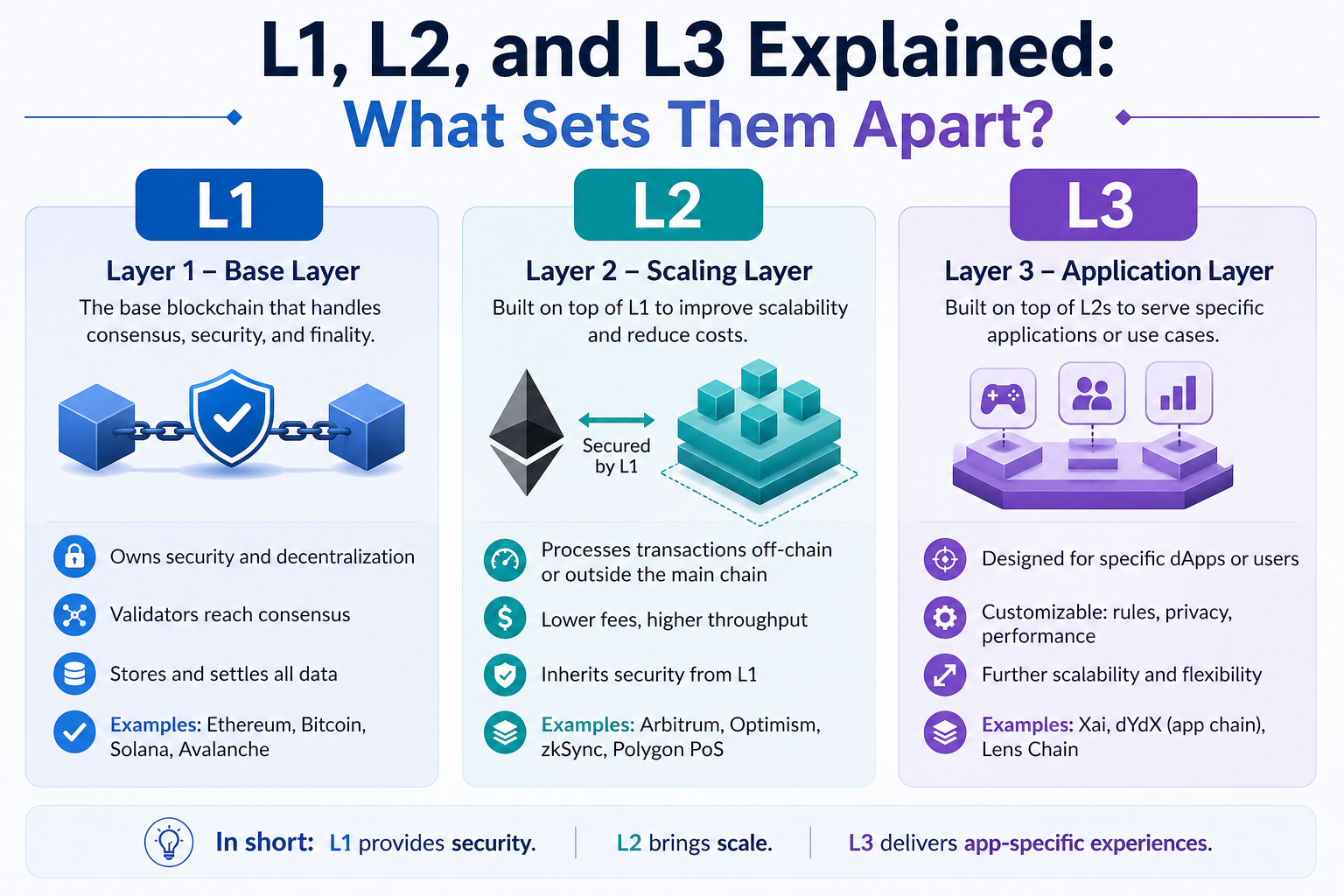
L1, L2 vs L3: Bringing It All Together
Understanding the differences between Layers 1, 2, and 3 becomes much easier when you view them as a continuous process rather than isolated concepts. Each layer plays a specific role, and together they create a complete system that allows data to travel from one device to another, whether across a room or across the world.
At the highest level of this comparison, Layer 1 is responsible for transmission, Layer 2 for local delivery, and Layer 3 for global routing. These three layers form the path that all data must follow, starting as raw bits and eventually reaching distant destinations through structured and intelligent handling.
How Data Moves Across Layers
When an application generates data, that information begins its journey down the networking stack. By the time it reaches Layer 3, it is packaged into a packet with logical addressing information. This packet identifies the source and destination using IP addresses, allowing it to travel across multiple networks.
As the packet moves down to Layer 2, it is encapsulated into a frame. This frame includes physical addressing information, such as MAC addresses, which are used for communication within a local network segment. The frame ensures that the data reaches the next immediate device on its path.
Finally, at Layer 1, the frame is broken down into bits and transmitted across a physical medium. These bits travel as electrical signals, light pulses, or radio waves until they reach the next device in the network.
This process repeats at every step along the path. Each intermediate device receives the bits, reconstructs the frame, extracts the packet, and then prepares it for the next hop. This constant cycle of encapsulation and decapsulation is what allows data to move seamlessly across complex networks.
The Journey of a Packet
A helpful way to understand this process is to imagine data as a traveler moving through a transportation system. The packet represents the traveler’s identity and final destination, while frames act like tickets for each leg of the journey.
At each stop, the traveler may change vehicles, but the destination remains the same. Similarly, as a packet moves through the network, its Layer 2 frame changes at every hop, but the Layer 3 packet continues toward its final destination.
This distinction is important because it highlights the different responsibilities of each layer. Layer 2 is concerned only with the next step, while Layer 3 keeps track of the overall journey.
Layer 1 vs Layer 2 vs Layer 3
The physical layer is the simplest of the three, focusing entirely on the transmission of bits. It does not interpret data or make decisions. Its role is to ensure that signals can move from one point to another without degradation.
The data link layer adds structure and intelligence. It organizes bits into frames, uses MAC addresses to identify devices, and ensures reliable communication within a local network. Devices at this layer, such as switches, can make forwarding decisions based on the information they analyze.
The network layer builds on this foundation by introducing logical addressing and routing. It determines how data travels across multiple networks, using IP addresses to identify endpoints and routers to guide packets along the best path.
Together, these layers create a progression from simple transmission to complex routing. Each layer adds new capabilities, enabling networks to scale and support a wide range of applications.
Key Differences in Functionality
One of the most important differences between these layers is their scope. Layer 1 operates at the level of physical connections, Layer 2 at the level of local networks, and Layer 3 at the level of interconnected networks.
Another key difference is the type of addressing used. Layer 2 relies on physical addresses that are typically fixed, while Layer 3 uses logical addresses that can be assigned and changed as needed. This distinction allows networks to be flexible and adaptable.
Decision-making also varies across these layers. Layer 1 devices do not make decisions, Layer 2 devices make local forwarding decisions, and Layer 3 devices make routing decisions that affect the entire path of data.
Why These Differences Matter
These distinctions are not just theoretical; they have practical implications for how networks are designed and managed. Understanding the roles of each layer helps in troubleshooting issues, optimizing performance, and implementing security measures.
For example, a problem at Layer 1 might involve faulty cables or signal interference. At Layer 2, issues could arise from incorrect MAC address tables or VLAN configurations. At Layer 3, routing errors or misconfigured IP addresses might prevent data from reaching its destination.
By identifying which layer is responsible for a problem, it becomes much easier to diagnose and resolve issues efficiently.
Encapsulation and Decapsulation Revisited
Encapsulation is the process that ties all these layers together. As data moves down the stack, each layer adds its own header, creating a structured package that can be transmitted across the network.
When the data reaches its destination, the process is reversed. Each layer removes its header and passes the remaining data up the stack. This ensures that the original information is delivered accurately and in the correct format.
This layered approach provides flexibility and modularity, allowing different technologies and protocols to coexist within the same network.
The Bigger Picture of Networking
While Layers 1 through 3 handle the movement of data, they are part of a larger system that includes higher layers responsible for reliability, formatting, and application interaction. Together, all seven layers of the OSI model create a comprehensive framework for communication.
However, the lower three layers remain the foundation upon which everything else is built. Without them, there would be no way to transmit, organize, or route data effectively.
Modern networks rely heavily on these layers, even as technologies continue to evolve. Whether using wired connections, wireless communication, or advanced routing protocols, the principles of Layers 1 through 3 remain central to how data moves across the world.
Final Perspective on L1, L2, and L3
In essence, Layer 1 is about sending signals, Layer 2 is about delivering data locally, and Layer 3 is about reaching distant destinations. Each layer builds upon the previous one, adding complexity and capability.
By understanding how these layers differ and how they work together, it becomes much easier to grasp the overall operation of networks. This knowledge is not only valuable for exams and certifications but also for real-world applications in designing, maintaining, and troubleshooting network systems.
The flow from bits to frames to packets represents the transformation of raw data into structured communication. This transformation is what enables everything from simple file transfers to global internet connectivity.
Mastering these concepts provides a strong foundation for further exploration into networking, opening the door to more advanced topics and deeper technical understanding.