Virtual Private Networks operate using different modes that define how data is protected and transmitted across networks. Among these, transport mode and tunnel mode are two fundamental approaches used within the IPsec framework. While both aim to secure communication between devices, they differ significantly in how they handle packet structure, encryption scope, and routing behavior. These differences are often not directly visible to end users, but for network engineers and IT professionals, understanding them is essential for designing secure and efficient infrastructures.
In practical environments, these modes determine how data travels between endpoints, whether it remains partially visible or fully encapsulated, and how flexible the VPN setup can be across different network architectures. Choosing the right mode is not just a technical preference but a decision that impacts security, performance, scalability, and troubleshooting complexity.
Transport mode and tunnel mode are both part of the IPsec protocol suite, which was designed to secure internet communication by encrypting IP packets. These standards were developed to ensure interoperability across different vendors and systems, making them widely applicable in both enterprise and service provider environments. Over time, improvements in networking technologies have expanded their usage, but their core principles remain largely unchanged.
Understanding how these two modes function provides clarity when working with VPN configurations, troubleshooting connectivity issues, or designing secure communication paths between systems. Although modern networks often default to tunnel mode, transport mode still has its place in specific scenarios where direct endpoint communication or minimal encapsulation is required.
What is a Virtual Private Network and Why It Matters
A Virtual Private Network is a mechanism used to create a secure and encrypted connection over an untrusted network, typically the internet. Its primary purpose is to ensure that data transmitted between two points remains confidential and protected from unauthorized access. By encrypting communication, VPNs prevent interception and modification of sensitive information.
Traditionally, VPNs were used to connect entire networks or remote sites, allowing organizations to securely extend their private infrastructure across public networks. This made it possible for branch offices, data centers, and remote users to communicate as if they were part of the same internal network.
Over time, VPN technology has evolved beyond simple site-to-site connections. Today, it is widely used for remote access, cloud connectivity, hybrid infrastructure integration, and secure application access. Even when private circuits such as MPLS or dedicated leased lines are used, VPN encryption can still be applied to ensure an additional layer of security.
The fundamental idea behind VPNs is not just connectivity but confidentiality, integrity, and authenticity of data. Encryption ensures that even if data is intercepted, it cannot be understood without the proper decryption keys. This is what makes VPNs a critical component of modern cybersecurity strategies.
Introduction to Transport Mode in IPsec
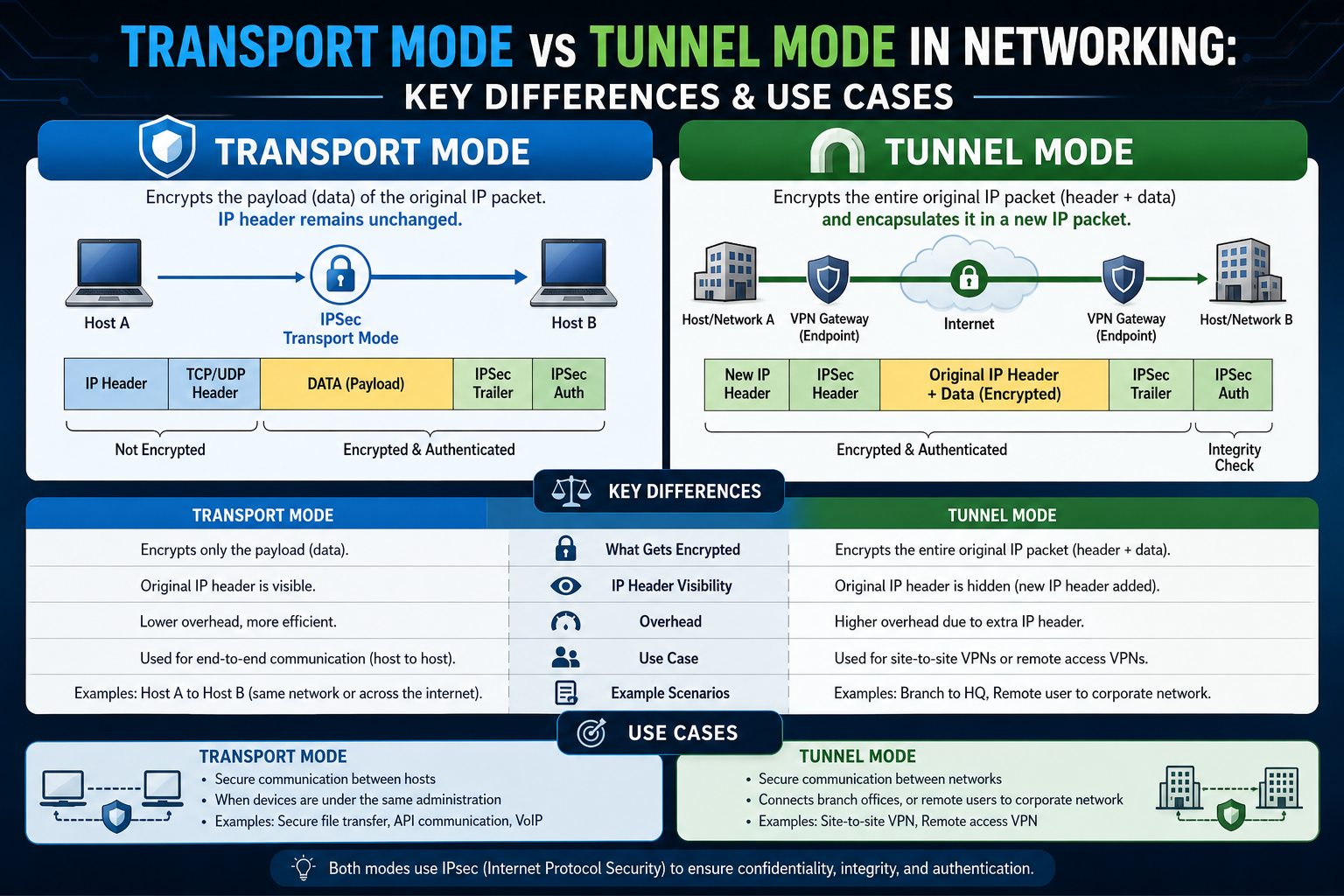
Transport mode is one of the two primary methods used in IPsec VPN communication. In this mode, only the payload of the IP packet is encrypted, while the original IP header remains intact and visible. This means that routing information, including source and destination IP addresses, can still be seen by intermediate devices such as routers.
Because the IP header is not encrypted, transport mode is primarily used in scenarios where direct communication exists between two endpoints without the need for additional encapsulation of routing information. This makes it more lightweight compared to tunnel mode, as it introduces less overhead.
Transport mode is often associated with point-to-point communication, where two devices communicate directly without involving multiple intermediate networks or complex routing paths. It is less commonly used in modern enterprise VPN architectures but still plays a role in specific technical scenarios where simplicity and efficiency are prioritized over full packet encapsulation.
From a structural perspective, transport mode modifies the original IP packet by inserting encryption headers while preserving the original IP header. This allows devices along the network path to route the packet normally while ensuring that the payload remains secure.
How Transport Mode Handles Data Transmission
In transport mode, the encryption process focuses exclusively on the payload portion of the packet. The data being transmitted is secured, but the surrounding routing information remains exposed. This design allows the packet to move through the network without requiring additional encapsulation layers.
Since routers depend on IP headers to determine the next hop, keeping this information visible ensures compatibility with standard routing mechanisms. This is particularly useful in environments where minimal disruption to existing network infrastructure is required.
However, this also means that transport mode does not provide full confidentiality of communication patterns. While the content of the message is protected, external observers can still infer who is communicating with whom based on the visible IP addresses. In some scenarios, this may not be a concern, but in more security-sensitive environments, it can be a limitation.
Transport mode is often considered efficient because it avoids the overhead associated with wrapping the entire original packet inside a new IP header. This can result in slightly better performance, especially in environments where bandwidth or processing resources are constrained.
Transport Mode in Point-to-Point Communication
One of the most common applications of transport mode is in point-to-point communication setups. In these scenarios, two endpoints communicate directly over a network without requiring complex routing across multiple sites.
In earlier networking environments, protocols such as GRE and L2TP were widely used to create tunnels between devices. These protocols provided encapsulation but often lacked built-in encryption. As a result, transport mode became a way to add security to existing tunneling mechanisms without redesigning the entire network architecture.
This allowed organizations to enhance security gradually rather than replacing established systems. Engineers could continue using familiar tunneling protocols while adding IPsec transport mode to encrypt the data payload.
In modern networks, however, this use case has become less common. Most environments now prefer tunnel mode because it provides both encapsulation and encryption in a single configuration, reducing complexity and improving security.
Transport Mode for Direct Endpoint Security
Another use case for transport mode is securing communication between two specific endpoints over the internet. In this scenario, only the data exchanged between these endpoints is encrypted, while the routing information remains visible.
This approach can be suitable when organizations are not concerned about hiding network topology but still require data confidentiality. For example, two servers exchanging data directly may use transport mode to secure their communication without introducing additional overhead.
However, as modern applications increasingly rely on built-in encryption protocols such as TLS, the need for transport mode in this context has diminished. Many applications now handle encryption at the application layer, reducing reliance on network-layer transport mode encryption.
Despite this, transport mode still serves as a valuable option in environments where lightweight encryption is needed without full tunnel encapsulation.
Transport Mode in Remote Access Scenarios
Transport mode can also be used in certain remote access configurations, although this is relatively rare in modern deployments. In these cases, a client device connects to a VPN concentrator using a transport mode tunnel.
This setup may be used when additional proprietary tunneling protocols are layered on top of the connection. However, most modern remote access VPN solutions now rely on tunnel mode or SSL-based VPN technologies instead.
In this configuration, transport mode behaves in a way similar to secure web communication, where the data payload is encrypted but the outer IP structure remains visible. This allows for compatibility with existing routing infrastructure while still protecting sensitive data.
Over time, this approach has largely been replaced by more robust and flexible VPN technologies that simplify configuration and enhance security.
Understanding Tunnel Mode in IPsec
Tunnel mode is the most widely used configuration in IPsec VPN deployments today. Unlike transport mode, it does not only encrypt the payload of a packet but encapsulates the entire original IP packet, including both header and data, inside a new encrypted packet. This means the original source and destination information are completely hidden from intermediate devices.
In this process, a new outer IP header is created to route the packet between VPN endpoints, while the original packet remains fully protected inside the encrypted payload. This layered structure allows secure communication between entire networks or between a user and a network without exposing internal addressing schemes.
Tunnel mode is designed to support broader networking requirements where multiple devices or entire subnets need to communicate securely over untrusted networks such as the internet. Because of this, it is the default choice in most modern VPN architectures.
Its ability to fully encapsulate traffic makes it more secure in terms of privacy and traffic analysis resistance. Anyone intercepting the data can only see the outer IP addresses of the VPN gateways, while the actual communication remains hidden.
How Tunnel Mode Encapsulation Works
In tunnel mode, the original IP packet is completely wrapped inside a new packet structure. This means the original header, including source and destination IP addresses, becomes part of the encrypted payload. A new external header is added for routing purposes.
This process creates two layers of IP information. The outer layer is used for routing across the public network, while the inner layer remains fully encrypted and inaccessible without proper decryption keys.
This encapsulation makes tunnel mode highly effective for secure communication between different networks. Even if attackers intercept the traffic, they cannot determine the internal network structure or the endpoints involved in the communication.
Because of this design, tunnel mode introduces slightly more overhead compared to transport mode. However, the trade-off is significantly improved security and flexibility in network design.
Tunnel Mode in Site-to-Site Communication
One of the most common use cases for tunnel mode is site-to-site communication. In this scenario, entire networks located in different geographic locations are connected securely over the internet.
Each site typically has a VPN gateway that handles encryption and decryption of traffic. When a device at one site sends data to another site, the VPN gateway encapsulates the entire packet and transmits it securely to the remote gateway.
This allows organizations to connect branch offices, data centers, and cloud environments as if they were part of a single unified network. Internal IP addressing remains private and hidden from external observers.
Tunnel mode essentially replaces older tunneling methods that required separate encapsulation and encryption mechanisms. It simplifies configuration by combining both functions into a single standardized protocol.
Tunnel Mode in Remote Access VPNs
Tunnel mode is also widely used in remote access VPN scenarios where individual users connect to a corporate network from external locations. In this case, the user’s device acts as a single endpoint that establishes a secure tunnel to the organization’s VPN gateway.
Once the tunnel is established, all traffic from the user device is encrypted and routed through the corporate network. The user appears to be operating as if they are directly connected to the internal infrastructure.
This setup is especially common in enterprise environments where employees need access to internal applications, databases, and services while working remotely.
The flexibility of tunnel mode allows it to handle both full network access and restricted access configurations depending on security policies. Firewall rules and access control lists can further define what resources the remote user can reach.
Why Tunnel Mode is More Secure
One of the primary advantages of tunnel mode is its ability to hide both data and network structure. Since the entire original packet is encrypted, attackers cannot see internal IP addresses, communication patterns, or payload data.
This level of protection is especially important in environments where traffic analysis could reveal sensitive business relationships or infrastructure design. By concealing both endpoints and data, tunnel mode significantly reduces exposure.
Additionally, tunnel mode reduces the risk of information leakage through IP headers. Even if encrypted payloads remain secure, exposed headers in transport mode can sometimes reveal useful metadata to attackers.
Tunnel mode eliminates this risk by replacing the original packet structure entirely during transmission.
Tunnel Mode and Network Addressing Challenges
While tunnel mode provides strong security benefits, it can introduce complexity in environments with overlapping IP address ranges. Since entire packets are encapsulated, conflicts between internal networks can cause routing issues.
To resolve this, techniques such as Network Address Translation (NAT) or subnet redesign may be required. These adjustments ensure that traffic can flow correctly between sites without IP conflicts.
Despite this challenge, tunnel mode remains the preferred choice because its benefits outweigh the configuration complexity in most modern environments.
Network engineers often design addressing schemes specifically to support tunnel mode VPN deployments, ensuring scalability and compatibility across distributed systems.
Tunnel Mode Compared to Traditional Tunneling Protocols
Before IPsec tunnel mode became standard, other tunneling protocols such as GRE were widely used. These protocols provided encapsulation but did not inherently include encryption.
In many cases, engineers had to combine GRE with separate encryption mechanisms to secure traffic. This created additional configuration overhead and increased the chance of misconfiguration.
Tunnel mode simplifies this process by integrating both encapsulation and encryption into a single mechanism. This standardization has made it easier to deploy secure VPNs across multi-vendor environments.
Because IPsec is widely supported, tunnel mode works across different hardware and software platforms, improving interoperability and reducing dependency on vendor-specific solutions.
Tunnel Mode in Modern Network Architectures
In modern infrastructures, tunnel mode plays a critical role in hybrid cloud environments, multi-cloud connectivity, and enterprise network expansion. It allows secure communication between on-premises systems and cloud platforms without exposing internal architectures.
It is also commonly used in software-defined networking (SDN) and SD-WAN solutions, where dynamic tunnel creation is required between distributed nodes.
As organizations continue to adopt cloud-first strategies, tunnel mode remains a foundational technology for secure connectivity across distributed environments.
Its ability to scale across complex networks while maintaining strong encryption makes it a preferred choice in enterprise-grade deployments.
Tunnel Mode in Security-Focused Environments
In industries where data protection is critical, such as finance, healthcare, and government systems, tunnel mode is often mandatory. Its ability to fully encrypt and encapsulate traffic ensures compliance with strict security regulations.
By hiding both content and structure of communication, it reduces attack surfaces and helps prevent unauthorized monitoring or interception.
Security policies in these environments often require VPN configurations that use tunnel mode exclusively, combined with additional layers of authentication and monitoring.
This layered approach strengthens overall network security and reduces the risk of data exposure.
Tunnel Mode in Performance Considerations
Although tunnel mode introduces additional overhead due to full packet encapsulation, modern network hardware is optimized to handle this efficiently. Encryption acceleration technologies and high-speed processors have minimized performance differences between tunnel and transport modes.
In most real-world scenarios, the performance impact is negligible compared to the security benefits provided.
As a result, tunnel mode remains the standard choice even in high-performance environments such as data centers and cloud infrastructures.
Key Differences Between Transport Mode and Tunnel Mode
Transport mode and tunnel mode may both belong to the same IPsec framework, but their internal behavior is fundamentally different. The main distinction lies in how each mode handles the original IP packet and what portion of it gets encrypted during transmission.
In transport mode, only the payload of the IP packet is encrypted while the original IP header remains visible. This allows intermediate routers to read routing information and forward packets as usual. In contrast, tunnel mode encrypts the entire original packet, including both header and payload, and then wraps it inside a new IP packet for transmission.
This difference has a direct impact on visibility. Transport mode exposes communication endpoints, while tunnel mode hides them completely behind VPN gateways. This makes tunnel mode more suitable for secure network-to-network communication, whereas transport mode is more focused on direct endpoint protection.
Another important difference is overhead. Transport mode introduces less additional data because it avoids full encapsulation. Tunnel mode adds extra headers, which slightly increases packet size but provides stronger isolation and security.
Security Comparison Between Both Modes
From a security standpoint, tunnel mode offers a higher level of protection. Since it encrypts the entire original packet, including IP addressing information, it prevents external observers from analyzing communication patterns between devices or networks.
Transport mode, on the other hand, still exposes source and destination IP addresses. While the content of the communication remains encrypted, metadata such as traffic flow and endpoint relationships can still be observed. This can be a potential risk in environments where traffic analysis is a concern.
Tunnel mode also provides better protection against certain types of network-based attacks that rely on packet inspection. By fully encapsulating traffic, it reduces the amount of information available to potential attackers.
However, transport mode is not inherently insecure. It still uses strong encryption for payload data and can be suitable in environments where endpoint visibility is not a concern. The choice depends more on the required level of network obscurity rather than encryption strength alone.
Performance Considerations in Real Networks
Transport mode generally has a slight performance advantage due to its reduced overhead. Since it does not encapsulate the entire packet, it requires fewer processing resources for encryption and decryption.
This can make it more efficient in environments where high-speed, low-latency communication between two endpoints is required. It is particularly relevant in older or resource-constrained systems.
Tunnel mode, while slightly heavier due to full packet encapsulation, has become highly optimized in modern hardware. Dedicated encryption engines and VPN accelerators reduce performance differences to a minimal level in most real-world deployments.
In modern enterprise environments, performance differences are rarely a deciding factor. Security requirements usually outweigh minor efficiency gains offered by transport mode.
Routing Behavior and Network Visibility
One of the most important differences between these modes is how they interact with network routing.
Transport mode relies on the original IP header for routing decisions. Since this header remains visible, intermediate devices can forward packets normally without needing additional encapsulation awareness.
Tunnel mode changes this behavior by replacing the original packet with a new outer IP header. Routing is performed based on this new header, while the original packet remains hidden inside the encrypted payload.
This means tunnel mode can create virtual point-to-point links between entire networks, effectively making separate locations behave like part of a single internal system.
Transport mode does not provide this abstraction. It maintains the original network structure and is therefore limited to endpoint-level encryption.
Use Case Suitability in Modern Environments
In modern networking, tunnel mode is the default choice for most VPN deployments. It is widely used for site-to-site connections, remote access VPNs, cloud integration, and hybrid infrastructure setups.
Its ability to securely connect entire networks makes it highly versatile in distributed systems. It also aligns well with modern security requirements where minimizing exposure of internal network structure is important.
Transport mode is now considered more of a specialized option. It is typically used in niche scenarios where direct endpoint communication is required without modifying the original packet structure.
Some legacy systems or specialized applications may still rely on transport mode, particularly where existing tunneling protocols are already in place and only encryption needs to be added.
Flexibility and Configuration Differences
Tunnel mode offers greater flexibility in network design. It allows organizations to connect different subnets, hide internal addressing schemes, and securely extend networks across untrusted environments.
It also supports complex routing scenarios where multiple networks must communicate through centralized VPN gateways. This makes it suitable for large-scale enterprise architectures.
Transport mode is simpler in structure but less flexible. It does not abstract network topology, which limits its use in multi-network environments. However, this simplicity can be beneficial in straightforward point-to-point setups.
Configuration complexity is often lower in transport mode when only two endpoints are involved, but tunnel mode provides more long-term scalability.
Troubleshooting and Operational Differences
From a troubleshooting perspective, transport mode can sometimes be easier to analyze because the original IP headers remain visible. This allows engineers to trace packet flow more directly through the network.
However, this visibility can also create confusion in complex environments where multiple security layers are involved.
Tunnel mode requires deeper inspection tools since traffic is fully encapsulated. Debugging often involves analyzing both outer and inner packets separately.
Despite this added complexity, modern network monitoring tools are well-equipped to handle tunnel mode analysis, making troubleshooting manageable in enterprise environments.
Choosing Between Transport Mode and Tunnel Mode
Selecting between transport mode and tunnel mode depends on the specific requirements of the network environment.
If the goal is to secure communication between two endpoints with minimal overhead and full visibility of routing information, transport mode can be appropriate. It works best in simple, direct communication scenarios.
If the requirement involves securing entire networks, hiding internal structure, or supporting remote access and distributed systems, tunnel mode is the better choice.
In most modern deployments, tunnel mode is preferred due to its stronger security model and broader compatibility with enterprise networking needs.
Transport mode remains useful in specialized cases but is no longer the default choice for general VPN architecture.
Real-World Decision Making in VPN Design
When choosing between transport mode and tunnel mode, real-world network requirements matter more than theoretical differences. In most enterprise environments, tunnel mode becomes the natural default because it aligns with how modern networks are structured. Organizations rarely operate as single point-to-point connections anymore. Instead, they manage distributed systems, cloud platforms, remote users, and interconnected branch offices, all of which require secure network abstraction rather than simple endpoint protection.
Tunnel mode fits this model because it allows entire networks to communicate securely without exposing internal IP structures. This makes it easier to scale infrastructure while maintaining consistent security boundaries. As organizations grow, the ability to extend secure communication across multiple sites becomes more important than minimizing packet overhead.
Transport mode, while technically efficient, does not provide this level of architectural flexibility. It is limited to direct communication scenarios where only two endpoints are involved. Because of this restriction, it is generally chosen only when there is a specific technical requirement that demands minimal encapsulation and full visibility of routing information.
In practical decision-making, engineers rarely start by choosing transport mode. Instead, they default to tunnel mode and only consider transport mode when a unique constraint forces them to do so.
When Transport Mode Becomes the Right Choice
Transport mode is most appropriate in environments where communication is strictly point-to-point and where network simplicity is a priority. If two devices need to communicate securely without altering the underlying network structure, transport mode can be a suitable solution.
It is also useful in situations where VPN overhead must be minimized. Since only the payload is encrypted, transport mode introduces slightly less processing load compared to tunnel mode. This can be relevant in legacy systems, embedded devices, or specialized infrastructure where resources are limited.
Another scenario where transport mode may still appear is when it is combined with existing tunneling protocols. In some older architectures, protocols like GRE or similar encapsulation methods are already in place, and transport mode is used simply to add encryption without redesigning the network.
Despite these niche cases, transport mode is increasingly rare in modern deployments because most of its advantages are outweighed by tunnel mode’s flexibility and stronger security model.
When Tunnel Mode is the Preferred Standard
Tunnel mode is the standard choice for nearly all modern VPN deployments. It is designed for environments where security, scalability, and network abstraction are important.
Site-to-site VPNs rely heavily on tunnel mode because they connect entire networks rather than individual devices. This allows organizations to link branch offices, data centers, and cloud environments as if they were part of the same internal network, while still maintaining encryption across public infrastructure.
Remote access VPNs also depend on tunnel mode. When an employee connects from an external location, tunnel mode ensures that all traffic between the device and corporate network is fully encapsulated and secured. This allows users to safely access internal systems without exposing sensitive infrastructure details.
Tunnel mode is also widely used in cloud computing environments. As organizations move workloads to hybrid or multi-cloud architectures, secure communication between on-premises systems and cloud services becomes essential. Tunnel mode provides a reliable method for creating secure network links across these distributed environments.
Because of its ability to hide internal addressing and structure, tunnel mode is also preferred in security-sensitive industries where reducing exposure is critical.
Operational Simplicity vs Architectural Strength
One way to understand the difference between transport mode and tunnel mode is to compare operational simplicity with architectural strength.
Transport mode is operationally simpler in terms of packet structure. It avoids full encapsulation, which reduces overhead and keeps routing information visible. This simplicity can make it easier to understand at a packet level and slightly more efficient in very specific scenarios.
Tunnel mode, however, offers stronger architectural benefits. It creates a clear separation between internal and external networks by fully encapsulating traffic. This allows organizations to build secure overlays on top of existing infrastructure without modifying internal addressing schemes.
In modern networking, architectural flexibility is far more valuable than minor efficiency gains. This is why tunnel mode has become the dominant standard.
Security Priority in Modern Networks
Security requirements in today’s networks are significantly more demanding than in earlier networking eras. Organizations must protect not only data content but also communication patterns, metadata, and network topology.
Tunnel mode directly addresses these requirements by hiding both payload and addressing information. This reduces the amount of information available to potential attackers and helps prevent traffic analysis.
Transport mode only protects the payload, which means that while data remains encrypted, communication patterns can still be observed. In environments where metadata sensitivity is important, this can be a disadvantage.
Because of increasing cybersecurity threats, regulatory requirements, and privacy concerns, tunnel mode has become the safer default in most environments.
Final Practical Guidance for Engineers
In practical terms, network engineers rarely need to overthink this decision. Tunnel mode is the standard option and is used in the majority of VPN deployments across industries.
Transport mode should be considered a specialized tool rather than a general-purpose solution. It is best reserved for specific technical requirements where direct endpoint encryption is needed without altering packet routing behavior.
When designing new VPN infrastructures, tunnel mode should almost always be selected unless there is a clear, justified reason to use transport mode. This ensures better scalability, stronger security, and easier integration with modern networking technologies.
Understanding both modes is still important, especially for troubleshooting legacy systems or interpreting packet behavior. However, in terms of design choice, tunnel mode represents the modern best practice.
Transport Mode vs Tunnel Mode: Which Should You Use?
Advanced Considerations in Transport Mode and Tunnel Mode Selection
Beyond the basic differences in encapsulation and encryption, real-world VPN design often requires deeper consideration of how each mode interacts with modern network architecture, application behavior, and security policy enforcement. While transport mode and tunnel mode may appear straightforward at a conceptual level, their impact becomes more complex when deployed at scale across hybrid environments, cloud infrastructure, and multi-vendor systems.
One important advanced factor is how each mode behaves in environments with multiple security layers. In modern networks, IPsec is rarely the only security mechanism in place. It often coexists with application-layer encryption, firewalls, intrusion detection systems, and zero-trust architectures. In such layered environments, tunnel mode tends to integrate more cleanly because it provides a clear boundary between encrypted and unencrypted segments of the network.
Transport mode, while still secure at the payload level, exposes metadata that may be consumed by monitoring or security systems. This can be beneficial in some environments where visibility is required for analytics or inspection. However, in highly secure environments, this same visibility may be considered unnecessary exposure.
Another advanced consideration is how each mode interacts with network segmentation strategies. Modern enterprise networks are typically divided into multiple zones such as internal networks, DMZs, cloud segments, and remote access domains. Tunnel mode aligns naturally with this segmentation approach because it can securely bridge entire network segments without exposing internal structures.
Transport mode does not provide this abstraction layer. It operates at the endpoint level, which means it does not inherently support broader segmentation strategies. As a result, it is less commonly used in environments where network zoning and isolation are critical design principles.
Impact on Cloud and Hybrid Infrastructure
Cloud computing has significantly influenced how VPN technologies are deployed. In hybrid environments, where on-premises infrastructure must communicate with cloud platforms, tunnel mode is almost always the preferred option.
This is because cloud environments require secure and scalable connectivity between distributed systems that may span multiple geographic regions and providers. Tunnel mode enables this by creating encrypted overlays that connect entire networks rather than individual endpoints.
Transport mode, in contrast, is less suited for cloud integration. Its endpoint-focused nature does not align well with dynamic scaling, distributed services, or multi-region architectures. While it can still function in specific cases, it lacks the flexibility required for modern cloud-native designs.
As organizations increasingly adopt microservices and container-based architectures, tunnel mode becomes even more relevant. These environments rely on secure communication between multiple services distributed across different nodes, which is more effectively supported by tunnel-based VPN structures.
Performance Optimization in High-Throughput Environments
In high-performance environments such as data centers, financial systems, and large-scale enterprise networks, VPN performance optimization becomes a key concern. While transport mode is often perceived as faster due to reduced encapsulation, the real-world difference is usually minimal when modern hardware acceleration is used.
Most enterprise-grade network devices include dedicated encryption processors that handle IPsec operations efficiently, significantly reducing the performance gap between transport and tunnel modes. As a result, tunnel mode can operate at near line-speed in many modern deployments.
However, in extremely latency-sensitive environments, transport mode may still offer marginal benefits due to its simpler packet structure. This is typically relevant only in specialized systems where microsecond-level performance differences matter.
Even in such cases, engineers must balance performance gains against the reduced security visibility provided by transport mode. In most scenarios, the trade-off does not justify deviating from tunnel mode.
Compatibility Across Vendors and Systems
One of the strengths of IPsec as a protocol suite is its vendor neutrality. Both transport mode and tunnel mode are defined in standardized specifications, ensuring interoperability across different hardware and software platforms.
However, tunnel mode tends to offer smoother compatibility in real-world deployments because it is more widely implemented in default configurations. Most VPN appliances, firewalls, and cloud networking services are optimized for tunnel mode as the primary operational standard.
Transport mode support is still present across most systems, but it is less frequently used in default templates or automated configurations. This means that in multi-vendor environments, tunnel mode reduces the likelihood of configuration mismatches or interoperability issues.
This practical advantage further reinforces tunnel mode as the preferred choice in enterprise deployments where consistency and reliability are critical.
Evolving Role of VPN Modes in Modern Security Models
As network security models evolve toward zero-trust architectures, the role of traditional VPN modes is also changing. Zero-trust principles emphasize continuous verification, minimal trust between network components, and strict access control at every layer.
In such environments, tunnel mode continues to play an important role by securely connecting network segments while enforcing encryption boundaries. However, it is often combined with identity-based access controls and application-level security mechanisms.
Transport mode, while still functional, plays a much smaller role in these modern architectures. Its limited scope makes it less suitable for environments where dynamic access control and full network abstraction are required.
Instead, its usage is typically confined to legacy systems or highly specific technical requirements where endpoint-level encryption remains sufficient.
Strategic Perspective for Network Design
From a strategic standpoint, choosing between transport mode and tunnel mode is less about technical capability and more about architectural intent. Transport mode represents a minimalistic approach focused on direct communication between endpoints, while tunnel mode represents a structural approach focused on secure network abstraction.
Modern network design increasingly favors abstraction, scalability, and security layering. These principles align closely with tunnel mode’s capabilities, making it the dominant choice in contemporary architectures.
Transport mode remains relevant as a specialized tool, but it is no longer central to mainstream VPN design strategies. Understanding both modes, however, is still essential for engineers working in environments that include legacy systems or hybrid infrastructures.
This deeper understanding ensures better decision-making when designing secure networks that must operate efficiently across diverse technologies and evolving security requirements.
Conclusion
Transport mode and tunnel mode serve different roles within IPsec VPN architecture. Transport mode focuses on lightweight encryption between two endpoints, preserving original IP headers and offering minimal overhead. Tunnel mode provides full encapsulation, stronger security, and broader networking capabilities by hiding entire packet structures and enabling secure communication between networks.
While both modes are technically valid and still supported, tunnel mode has become the dominant standard in modern networking due to its flexibility, scalability, and stronger protection of network information. Transport mode remains relevant only in specific, limited use cases where simplicity and direct endpoint communication are required.
In most real-world scenarios today, tunnel mode is the correct choice for secure and scalable VPN deployment.