The Certified Information Systems Security Professional (CISSP) certification is widely recognized as one of the most respected credentials in the cybersecurity industry. However, what often surprises candidates is that the real challenge is not only the exam itself but the strict experience requirements that come with it. Many professionals assume that passing the test is the hardest part, but in reality, proving eligible work experience is what determines whether someone can fully earn the certification or remain in an associate status for years.
To understand what truly counts as CISSP experience, it is important to move beyond job titles and focus on the nature of the actual work performed. The certification body looks for evidence that a candidate has engaged in meaningful security-related responsibilities across recognized domains of cybersecurity. This means that even roles without the word “security” in the title can still be considered valid, provided the duties align with established security practices.
The Real Nature of the CISSP Certification
The CISSP exam is not designed to test deep technical execution skills such as coding or system configuration. Instead, it evaluates a professional’s ability to think at a managerial and architectural level. It measures how well a person understands security principles, risk management, governance, and strategic decision-making in real-world environments.
This distinction is important because it directly influences what counts as valid experience. ISC2, the organization behind CISSP, is not simply looking for engineers who perform isolated technical tasks. Instead, it wants professionals who can design, oversee, and manage security programs within organizations. This broader perspective is why the certification is often associated with leadership roles in cybersecurity.
Minimum Experience Requirement and Its Purpose
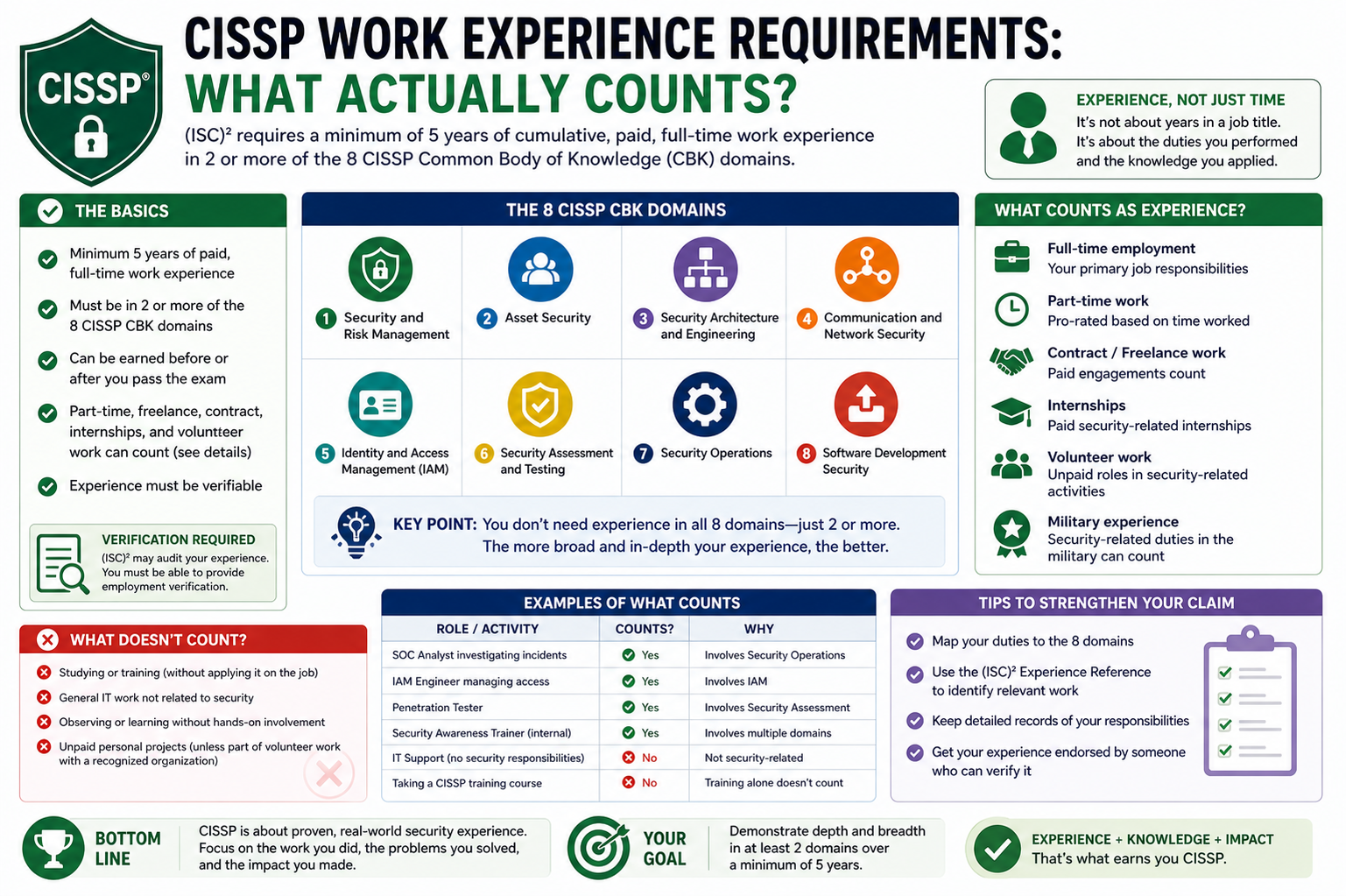
To earn full CISSP certification, a candidate must demonstrate a minimum of five years of cumulative paid work experience in at least two of the eight recognized security domains. This requirement exists to ensure that certified professionals have practical exposure to real security challenges rather than just theoretical knowledge.
The idea behind the experience requirement is to validate that candidates have been involved in decision-making processes that affect organizational security. It is not enough to understand concepts in theory; ISC2 expects candidates to have applied them in professional environments where security risks, vulnerabilities, and policies are actively managed.
Understanding the Meaning of Cumulative Experience
One of the most misunderstood aspects of CISSP eligibility is the term “cumulative experience.” This does not mean continuous employment in a single security-focused job for five straight years. Instead, it allows candidates to combine different roles, projects, and responsibilities over time, as long as they collectively meet the required experience threshold.
For example, someone might have worked in a system administration role for a few years, then transitioned into network support while still handling security responsibilities. If both roles involved relevant security work aligned with CISSP domains, they can be combined to fulfill the requirement. This flexible approach allows professionals from diverse IT backgrounds to qualify.
How ISC2 Evaluates Professional Experience
ISC2 does not rely solely on job titles when reviewing applications. Instead, it focuses on the actual tasks and responsibilities performed by the candidate. This means that even if a position does not explicitly mention security, the experience may still be valid if security-related duties were part of the role.
Candidates are expected to clearly document their experience, explaining how their daily responsibilities align with the CISSP domains. This includes describing tasks such as implementing access controls, managing risk frameworks, conducting security assessments, or maintaining secure network configurations. The clarity and depth of these descriptions play a key role in approval.
The Eight Security Domains That Define Experience
CISSP experience is measured against eight core domains that represent the full scope of cybersecurity knowledge. These domains help ISC2 determine whether a candidate has broad and balanced exposure to the field.
Security and Risk Management focuses on governance, compliance, and policy development. Asset Security deals with protecting organizational data and resources. Security Architecture and Engineering involves designing secure systems and infrastructure. Communication and Network Security focuses on protecting data in transit and securing network environments.
Identity and Access Management ensures proper authentication and authorization controls. Security Assessment and Testing involves evaluating systems for vulnerabilities. Security Operations focuses on monitoring, incident response, and ongoing protection. Software Development Security addresses secure coding practices and application security.
Candidates are not required to be experts in all eight domains, but they must demonstrate experience in at least two. This ensures that CISSP holders have a well-rounded understanding of cybersecurity practices.
How Everyday IT Roles Can Qualify
Many professionals underestimate the security aspects of their current roles. For instance, a system administrator in a small or mid-sized organization often handles tasks such as configuring firewalls, managing user permissions, applying security patches, and monitoring system logs. These responsibilities are directly aligned with CISSP domains, even if the job title does not reflect it.
Similarly, network engineers frequently deal with secure routing configurations, VPN setups, and intrusion prevention systems. These tasks fall under communication and network security. The key factor is not the job title itself but whether the individual actively participates in securing systems, data, or infrastructure.
Part-Time Experience and How It Is Calculated
CISSP recognizes that not all professionals work in traditional full-time security roles. For this reason, part-time experience is accepted, provided it meets certain conditions. The work must generally fall between 20 and 34 hours per week to qualify as valid part-time experience.
ISC2 converts part-time work into full-time equivalent experience using a standard calculation based on a 40-hour work week. This means that accumulated part-time hours are totaled and then translated into equivalent full-time experience. For example, a candidate who has completed 1,040 hours of relevant part-time work would be credited with approximately six months of full-time experience.
This approach allows flexibility for professionals who may be balancing multiple roles or gaining experience gradually over time.
Security Internships as Valid Experience
Internships can also contribute to CISSP eligibility if they involve meaningful security-related tasks. Both paid and unpaid internships may be considered, as long as they align with at least two of the CISSP domains.
However, internships require stronger documentation compared to full-time roles. Candidates must typically provide official confirmation on organizational letterhead verifying their role, responsibilities, and duration of involvement. In some cases, ISC2 may also contact supervisors directly to validate the experience.
This strict verification process ensures that internship experience is legitimate and relevant to cybersecurity practice rather than general IT exposure.
Academic Degrees and Certification Waivers
ISC2 provides an option to reduce the required experience by one year for candidates who hold certain academic degrees or recognized certifications. A four-year college degree or an advanced degree in a related field can be used to substitute for one year of experience. However, only one type of educational qualification can be applied for this reduction.
Similarly, holding specific industry-recognized certifications can also waive one year of experience. These certifications typically include well-known credentials in cybersecurity, networking, and systems administration. However, even with these waivers, a minimum of four years of professional experience is still required.
This rule ensures that academic knowledge and professional certifications supplement but do not replace real-world security experience.
Limitations on Combining Benefits
While ISC2 offers flexibility through degree and certification waivers, candidates cannot combine multiple reductions to eliminate more than one year of experience. This policy prevents over-crediting and maintains the integrity of the certification process.
For instance, a candidate cannot use both a degree and a certification to reduce experience by two years. Only one reduction is permitted, ensuring that all CISSP professionals still demonstrate substantial real-world exposure to cybersecurity work.
The Importance of Professional Endorsement
Beyond passing the exam and meeting experience requirements, candidates must also be endorsed by an existing CISSP-certified professional. This endorsement serves as a final validation step confirming that the candidate’s experience is legitimate and meets ISC2 standards.
The endorsement process reinforces the credibility of the certification. It ensures that experienced professionals within the cybersecurity community verify the readiness of new candidates before full certification is granted.
Mapping Real Job Responsibilities to CISSP Experience
One of the most important aspects of qualifying CISSP experience is understanding how everyday job responsibilities translate into recognized security work. ISC2 does not expect candidates to work in purely theoretical security roles. Instead, it evaluates whether routine professional tasks contribute to protecting systems, managing risk, or ensuring secure operations.
In many cases, professionals already perform CISSP-relevant work without realizing it. For example, configuring user permissions, enforcing password policies, monitoring system alerts, or managing backups all fall within recognized security domains. The key is identifying where security decisions are being made and demonstrating how those actions align with organizational protection goals.
When documenting experience, it is essential to clearly connect responsibilities to security outcomes. Simply listing job duties is not enough. The description must show how those duties contributed to confidentiality, integrity, and availability of systems and data.
Translating Technical Roles into Security Experience
Technical roles such as system administration, network engineering, database management, and cloud support often contain significant security components. However, many candidates fail to properly highlight these elements when applying for CISSP eligibility.
A system administrator, for example, may spend time patching servers, configuring access controls, and monitoring logs. Each of these tasks directly relates to security operations and identity management domains. Similarly, a network engineer may implement firewall rules, VPN configurations, and intrusion prevention systems, which map directly to communication and network security.
The challenge lies in framing these responsibilities correctly. ISC2 is not looking for job titles but for evidence of security thinking and execution. Proper framing ensures that otherwise standard IT work is recognized as valid security experience.
Security Domains in Everyday IT Environments
Even in organizations that do not have dedicated cybersecurity teams, security responsibilities are often distributed across general IT staff. This is particularly common in small and mid-sized companies where employees wear multiple hats.
In such environments, individuals often handle user access control, system hardening, patch management, and incident response without formal security titles. These tasks align closely with multiple CISSP domains, even if they are not labeled as security functions.
Understanding this overlap is critical. Many professionals underestimate their eligibility simply because their job title does not reflect security work, when in reality, their responsibilities strongly align with ISC2 expectations.
Security Operations in Practical Work Settings
Security operations form a large portion of CISSP-qualifying experience. This includes monitoring systems for threats, responding to incidents, analyzing logs, and maintaining security tools such as SIEM systems or antivirus platforms.
In real-world environments, security operations may not always be formalized. A technician might investigate unusual system behavior, restore compromised accounts, or respond to malware infections as part of general IT support. These activities are all valid security operations experience when properly documented.
What matters most is demonstrating involvement in identifying, responding to, and mitigating security risks in operational environments.
Identity and Access Management in Real Scenarios
Identity and Access Management is one of the most commonly encountered domains in everyday IT roles. It involves ensuring that the right individuals have appropriate access to systems and data while preventing unauthorized access.
Tasks such as creating user accounts, managing permissions, enforcing multi-factor authentication, and handling role-based access control all fall under this domain. Even helpdesk professionals often perform IAM-related tasks when onboarding or offboarding employees.
Proper documentation should highlight how access decisions are made and how policies are enforced. ISC2 places strong emphasis on ensuring that candidates understand the importance of controlling digital identities in organizational environments.
Security Architecture and Engineering Exposure
Security Architecture and Engineering focuses on designing secure systems and infrastructure. While this may sound advanced, many professionals contribute to this domain without realizing it.
For example, cloud engineers designing secure virtual networks, implementing encryption protocols, or configuring secure storage systems are actively participating in security architecture. Similarly, database administrators who design secure schemas and enforce encryption policies are contributing to this domain.
Even decisions about system design, redundancy, and secure communication protocols can qualify as architectural security experience. The key is demonstrating that security considerations influenced technical decisions.
Security Assessment and Testing in Practice
Security assessment and testing involves evaluating systems for vulnerabilities and ensuring that security controls are functioning correctly. This can include vulnerability scanning, penetration testing, audit support, and compliance checks.
In many organizations, IT professionals assist with security audits or run automated scanning tools to identify weaknesses. Even reviewing system configurations for compliance or verifying patch levels can contribute to this domain.
Candidates should emphasize any experience involving testing systems for weaknesses or validating security controls, even if these tasks were part of broader IT responsibilities.
Security Risk and Governance Responsibilities
Security and Risk Management is one of the most strategic CISSP domains. It focuses on policies, compliance, risk analysis, and governance structures within an organization.
Professionals involved in policy creation, risk assessments, regulatory compliance, or internal audits can count this experience toward CISSP eligibility. Even assisting in developing security guidelines or participating in compliance reviews is considered relevant.
This domain highlights the importance of understanding security from a business perspective rather than just a technical one. ISC2 values candidates who can connect technical controls with organizational risk management.
Common Mistakes When Documenting Experience
One of the most frequent issues candidates face is failing to properly describe their experience. Many applicants simply list job titles and responsibilities without connecting them to CISSP domains. This often leads to delays or rejections during the verification process.
Another common mistake is exaggerating responsibilities or including unrelated work. ISC2 carefully evaluates submissions, and inconsistencies can result in further scrutiny or rejection of experience claims.
Candidates also sometimes fail to specify time allocations for part-time or mixed roles, making it difficult for ISC2 to accurately calculate experience. Clear, detailed, and honest documentation is essential for smooth approval.
How ISC2 Verifies Submitted Experience
ISC2 does not rely solely on written submissions. In some cases, they may contact employers or supervisors to confirm the accuracy of experience claims. This verification process ensures that submitted information is legitimate and consistent.
Applicants should be prepared for possible follow-up questions or clarification requests. Having supervisors aware of the endorsement process can help avoid delays. In some cases, official letters or supporting documentation may be requested to validate roles and responsibilities.
This verification step reinforces the credibility of CISSP certification by ensuring that all certified professionals meet consistent global standards.
Borderline Roles and Acceptable Experience
Certain roles may not clearly appear to be security-focused but can still qualify if properly aligned with CISSP domains. For example, software developers who implement secure coding practices or cloud engineers who configure secure environments can often qualify.
Similarly, IT support professionals who handle account management, troubleshoot security issues, or enforce security policies may also meet eligibility requirements. The key factor is whether security is part of decision-making or operational responsibility.
Even if security is not the primary function of the role, consistent involvement in security-related tasks can contribute significantly to overall experience eligibility.
Military and Government Security Experience
Military and government roles often involve structured security responsibilities that align closely with CISSP domains. These may include information assurance, classified data handling, secure communications, and infrastructure protection.
Such experience is generally considered valid as long as it can be properly documented and mapped to recognized security domains. In many cases, these roles provide strong alignment with risk management, security operations, and communication security.
However, proper documentation remains essential, especially when roles are sensitive or classified in nature. ISC2 requires sufficient detail to evaluate relevance without compromising confidentiality.
Consulting and Multi-Project Experience
Professionals working in consulting roles often gain experience across multiple organizations and industries. This type of experience can be highly valuable for CISSP eligibility because it often exposes candidates to diverse security environments.
Consultants may perform risk assessments, design security frameworks, implement controls, or conduct audits across different clients. Each of these activities can contribute to CISSP domains if properly documented.
The challenge in consulting roles is ensuring clarity and consistency when describing varied experiences across multiple projects. Each project should clearly indicate the security relevance of the work performed.
Importance of Security Thinking in All Roles
Ultimately, what ISC2 is looking for is evidence of security thinking rather than strict job classification. Candidates who consistently consider risk, implement safeguards, and contribute to organizational protection are often already performing CISSP-level work.
Security thinking involves anticipating threats, understanding vulnerabilities, and applying controls to reduce risk. This mindset can exist in nearly any IT-related role when responsibilities are performed with security awareness.
Recognizing and articulating this mindset is often the key difference between approved and rejected experience submissions.
Understanding How Experience Must Be Written for Approval
When applying for CISSP eligibility, the way experience is written matters almost as much as the experience itself. ISC2 evaluates whether your description clearly demonstrates involvement in security-related activities across recognized domains. This means vague statements such as “handled IT tasks” are not sufficient. Instead, candidates must explain how their responsibilities directly contributed to protecting systems, managing risks, or implementing security controls. The focus is on clarity, relevance, and alignment with CISSP domains rather than general job summaries.
Transforming Job Descriptions into Security Evidence
A common mistake candidates make is copying generic job descriptions into their application. ISC2 does not evaluate job descriptions; it evaluates actual work performed. Each responsibility should be reframed to highlight its security relevance. For example, instead of stating “managed servers,” a stronger description would explain how server hardening, patch management, and access control enforcement were performed. This transformation is essential because it turns routine IT tasks into verifiable security experience that matches CISSP expectations.
How ISC2 Interprets Security vs Non-Security Roles
ISC2 does not require candidates to have “security” in their job title, but it does require evidence of security-related decision-making or execution. A professional working in IT support, for example, may still qualify if they regularly manage user authentication, respond to incidents, or enforce security policies. The distinction lies in whether security was part of the responsibilities, not whether the role was labeled as security. This flexible interpretation allows a wide range of IT professionals to qualify.
Requirement of Two or More Security Domains Per Role
Each role submitted for CISSP experience must align with at least two of the eight security domains. This ensures that candidates have broad exposure rather than isolated tasks. For instance, a network engineer might qualify through involvement in communication security and security operations. A system administrator might qualify through identity and access management and security operations. The key is demonstrating that responsibilities extend across multiple areas of security practice rather than a single narrow function.
Combining Multiple Roles to Meet Eligibility
CISSP experience does not need to come from a single job. Candidates can combine multiple roles across different organizations to meet the five-year requirement. This is particularly useful for professionals who have transitioned between IT positions over time. For example, someone might accumulate two years in system administration, one year in network support, and two years in cloud operations. If each role includes relevant security responsibilities, they can collectively satisfy the experience requirement.
Part-Time Work and Its Practical Interpretation
Part-time experience is often misunderstood, but it is fully accepted as long as it meets minimum hourly thresholds. ISC2 evaluates part-time work by converting total hours into full-time equivalents. This allows professionals working flexible schedules to still qualify. The key requirement is consistency and documentation. Candidates must clearly state their weekly hours and ensure that the work involves meaningful security tasks. Random or inconsistent hours without clear structure may not be accepted.
Blended Roles in Small Organizations
In small businesses, employees often handle multiple responsibilities, including security-related tasks without formal recognition. These blended roles are highly valuable for CISSP eligibility because they often provide exposure to multiple domains simultaneously. For example, a single IT administrator might manage backups, configure firewalls, handle user access, and monitor systems. This combination naturally aligns with several CISSP domains and is often considered strong qualifying experience when properly documented.
Freelance and Contract-Based Security Work
Freelancers and contractors can also qualify for CISSP experience if their work involves recognized security responsibilities. This may include implementing security solutions, conducting risk assessments, or managing infrastructure security for clients. The challenge in freelance work is documentation. Each project must clearly explain scope, responsibilities, duration, and security relevance. ISC2 evaluates the substance of the work rather than employment status, meaning contract professionals are fully eligible if their experience is properly structured.
Entrepreneurial and Self-Employed Experience
Self-employed professionals managing their own IT or security businesses can also claim CISSP experience. This may include running security audits, designing secure systems for clients, or managing enterprise security environments. However, ISC2 requires clear evidence that the work was paid and involved real clients or organizational impact. Personal projects without external clients typically do not qualify. The emphasis remains on professional, compensated security work that demonstrates real-world application.
Handling Employment Gaps in Experience History
Career gaps do not automatically disqualify candidates from CISSP eligibility. ISC2 evaluates cumulative experience, meaning breaks in employment are acceptable as long as total qualifying experience reaches five years. Candidates should ensure that each period of employment is clearly documented and that gaps are explained if necessary. What matters most is the total amount of relevant security experience, not continuous employment without interruption.
Overlapping Roles and Experience Calculation
In some cases, candidates may hold overlapping roles, such as part-time consulting while working full-time in another job. ISC2 evaluates these situations carefully to avoid double-counting the same time period. While overlapping roles can contribute to experience, they must represent distinct work hours and responsibilities. Proper documentation is essential to show that both roles independently contributed to security experience without duplication.
Importance of Quantifying Responsibilities
ISC2 places strong value on measurable experience descriptions. Instead of vague statements, candidates should include details about scope and scale of responsibilities. For example, managing access control for 50 users is more meaningful than simply stating “managed user accounts.” Quantifying responsibilities helps ISC2 understand the level of exposure and complexity involved in the work, making the experience more credible and verifiable.
Security Documentation and Internal Evidence
In many organizations, security work is not formally documented under “security” titles. Therefore, candidates may need to rely on internal evidence such as project reports, system logs, policy documents, or operational records. While ISC2 does not require submission of these documents upfront, having them available can support verification if needed. Strong documentation practices within a role can significantly strengthen an application.
Supervisor Verification and Its Importance
Every CISSP candidate must have their experience verified by a supervisor or an existing CISSP professional. This endorsement confirms that the claimed experience is accurate and aligns with ISC2 standards. The verifier does not need to be from the same organization for all roles, but they must be able to confirm the candidate’s responsibilities. This step adds credibility and ensures that experience claims are validated by industry professionals.
What Happens If Experience Is Rejected
If ISC2 finds that submitted experience does not meet requirements, candidates are not permanently disqualified. Instead, they may be asked to revise or clarify their submission. In some cases, additional documentation or rewording of responsibilities is sufficient. However, repeated inconsistencies or unsupported claims can delay approval significantly. Accuracy and honesty are essential throughout the process to avoid complications.
Security Awareness as a Key Evaluation Factor
One of the most overlooked aspects of CISSP experience is security awareness. ISC2 values candidates who demonstrate an understanding of risk, threat mitigation, and secure decision-making. Even in non-security roles, professionals who consistently apply security thinking in their work are more likely to qualify. This includes identifying vulnerabilities, suggesting improvements, and ensuring secure configurations in everyday tasks.
Aligning Experience with Organizational Security Goals
Experience is most valuable when it clearly supports organizational security objectives. ISC2 looks for evidence that candidates contributed to protecting data, systems, and infrastructure in a meaningful way. This may include reducing risk exposure, improving access control systems, or enhancing incident response processes. The stronger the alignment between individual responsibilities and organizational security outcomes, the more valuable the experience becomes.
Common Misinterpretation of “Security Work”
Many candidates assume that only specialized cybersecurity roles count toward CISSP experience. This is incorrect. ISC2 recognizes a wide range of IT and technical roles as valid if they involve security responsibilities. Misinterpreting this requirement often leads to underreporting eligible experience. Understanding that security work exists across many IT functions is essential for accurately documenting qualifications.
Preparing for ISC2 Review and Validation
Before submitting experience, candidates should carefully review each role to ensure clarity, consistency, and alignment with CISSP domains. The application should be structured in a way that allows ISC2 reviewers to easily identify security-related responsibilities. Well-prepared submissions reduce the likelihood of delays and increase the chances of smooth approval.
Building a Strong Experience Narrative Across Roles
A strong CISSP application tells a consistent story of growing security involvement over time. Even if roles differ, they should collectively demonstrate increasing responsibility in managing and securing systems. This narrative helps ISC2 understand how the candidate has developed professionally and whether they are ready for certification-level recognition.
Avoiding Overstatement and Ensuring Accuracy
One of the most important principles in CISSP experience submission is accuracy. Overstating responsibilities or claiming unrelated tasks can lead to rejection or further investigation. ISC2 values integrity highly, and applicants are expected to represent their experience truthfully. Even modest but accurate descriptions are more effective than exaggerated claims.
Preparing Experience for Long-Term Review Success
Successful CISSP candidates typically take time to carefully prepare their experience documentation. They ensure that every role is clearly aligned with security domains, responsibilities are well described, and supporting verification is available. This careful preparation reflects not only eligibility but also the professional discipline expected of CISSP-certified individuals.
Final Transition Toward Certification Readiness
At this stage of the CISSP journey, experience becomes more than just a requirement; it becomes proof of readiness for advanced security leadership. Each role, responsibility, and documented task contributes to demonstrating that the candidate is capable of managing complex security environments. Properly structured experience ensures a smooth transition from candidate to certified professional.
Final Validation of CISSP Experience and Eligibility Review
At the final stage of the CISSP experience process, ISC2 performs a comprehensive validation of all submitted information to confirm that the candidate meets the required standards. This step is not just a formality; it is a structured review designed to ensure that every applicant has genuine, verifiable, and relevant cybersecurity experience. The organization examines whether the documented work aligns with the eight CISSP domains and whether the cumulative experience reaches the minimum requirement.
What makes this stage important is that ISC2 is verifying not only time spent in roles but also the quality and relevance of the responsibilities performed. Even if a candidate meets the five-year threshold on paper, approval depends on whether the experience demonstrates real involvement in security practices such as risk management, access control, system protection, and operational security.
Role of the CISSP Endorsement Process
A key part of final validation is the endorsement requirement. Every candidate must be endorsed by a CISSP-certified professional or an ISC2-approved authority. This endorsement serves as a professional confirmation that the candidate’s experience is accurate and meets certification expectations.
The endorser reviews the submitted experience and confirms that the responsibilities described are truthful and aligned with security domains. This step adds an additional layer of credibility to the process, ensuring that candidates are not solely self-reporting their qualifications. It also reinforces the community-based integrity of the CISSP certification.
Importance of Consistency Across All Experience Entries
ISC2 carefully checks for consistency across all submitted roles and timelines. Any inconsistencies in job titles, dates, responsibilities, or claimed domains may lead to additional scrutiny. Consistency is important because it demonstrates that the candidate has a clear and accurate understanding of their professional history.
If multiple roles are included, they should collectively form a logical progression of experience in cybersecurity-related responsibilities. Disconnected or contradictory entries can create confusion during evaluation and may delay approval.
How ISC2 Evaluates Depth of Security Involvement
Beyond verifying job roles, ISC2 also evaluates the depth of security involvement in each position. This means understanding how frequently and significantly security tasks were performed. A role where security was a core responsibility carries more weight than one where it was only occasional or incidental.
Depth of involvement is assessed through task descriptions, project examples, and the complexity of responsibilities. For instance, designing security architecture for enterprise systems demonstrates deeper involvement than simply applying routine security patches. ISC2 uses this evaluation to determine whether candidates have meaningful hands-on or managerial exposure to security practices.
Common Reasons for Experience Delays
One of the most common reasons for delays in CISSP approval is insufficient detail in experience descriptions. When responsibilities are described in vague or generic terms, ISC2 may request clarification. Another frequent issue is misalignment with CISSP domains, where submitted experience does not clearly map to recognized security areas.
Incomplete documentation of part-time roles or unclear verification from supervisors can also cause delays. In some cases, ISC2 may reach out for additional information, which extends the review timeline. Ensuring clarity and completeness before submission significantly reduces these risks.
Clarifying the Difference Between Exposure and Responsibility
A critical distinction in CISSP evaluation is the difference between exposure to security tasks and actual responsibility for security outcomes. Simply being aware of security processes is not sufficient. Candidates must demonstrate active involvement in implementing, managing, or influencing security controls.
For example, observing a security team perform audits does not count as experience. However, participating in the audit process, analyzing findings, or implementing recommended changes does. ISC2 focuses on responsibility and contribution rather than passive exposure.
Validation of Mixed Technical and Security Roles
Many candidates have hybrid roles that combine general IT responsibilities with security-related tasks. ISC2 evaluates these roles by isolating the security components and determining whether they meet domain requirements. Even if only part of the role involves security, it can still be counted if it is significant and consistent.
For example, a cloud administrator may handle infrastructure deployment while also managing encryption policies and identity access controls. The security-related portion of this role is what contributes to CISSP eligibility. Properly separating and describing these components is essential during application submission.
Importance of Real-World Application of Security Knowledge
ISC2 places strong emphasis on real-world application rather than theoretical understanding. Candidates are expected to demonstrate that they have applied security principles in practical environments. This includes responding to incidents, designing secure systems, enforcing policies, or managing risk in operational settings.
The ability to translate knowledge into action is a defining characteristic of CISSP experience. It reflects readiness for leadership roles where security decisions impact entire organizations. This practical focus is what distinguishes CISSP from entry-level or purely academic certifications.
Handling Multi-Industry Experience Backgrounds
Candidates often come from diverse industries such as finance, healthcare, education, government, or technology. ISC2 does not limit eligibility based on industry type. Instead, it evaluates whether security responsibilities exist within that industry context.
Experience gained across multiple industries can actually strengthen an application, as it demonstrates adaptability and broad exposure to different security environments. However, each role must still clearly show alignment with CISSP domains, regardless of industry.
Evaluating Leadership and Decision-Making Roles
As CISSP is a management-focused certification, ISC2 values experience that involves decision-making and leadership in security contexts. This includes roles where candidates define policies, guide security strategies, or make architectural decisions.
Leadership experience does not necessarily mean holding a managerial title. Even technical professionals who influence security design or guide implementation decisions may qualify. The key factor is whether the candidate has played an active role in shaping security outcomes.
Final Experience Audit Before Certification Approval
Before granting full certification, ISC2 performs a final audit of all submitted experience, endorsements, and supporting details. This audit ensures that all requirements have been met consistently and that no discrepancies exist in the application.
At this stage, candidates who meet all criteria are approved for full CISSP certification. Those who fall short in experience are typically granted Associate of ISC2 status if they have passed the exam but lack full experience requirements. This allows them to continue gaining experience while already being recognized within the ISC2 framework.
Understanding the Associate of ISC2 Status
Candidates who pass the CISSP exam but do not yet meet the five-year experience requirement are granted Associate status. This designation allows them up to six years to complete the required experience. During this time, they can continue working in relevant roles and gradually build the necessary qualifications.
Associate status ensures that candidates remain engaged with the certification pathway while still developing their professional experience. Once the required experience is completed and validated, they can transition to full CISSP certification without retaking the exam.
Final Readiness for Certification Completion
Once ISC2 confirms that all requirements are satisfied, including exam success, experience validation, and endorsement approval, the candidate is officially awarded CISSP certification. At this stage, the individual joins a global community of certified cybersecurity professionals recognized for their expertise in security management and governance.
This final step represents the completion of a structured journey that combines technical exposure, professional experience, and ethical validation. It confirms that the candidate is prepared to operate at a senior level within cybersecurity environments.
Long-Term Value of Valid CISSP Experience
Beyond certification, the experience required for CISSP holds long-term professional value. It represents real-world exposure to security challenges, decision-making under risk, and the implementation of protective controls in operational environments. These experiences continue to benefit professionals throughout their careers.
CISSP-certified individuals are often trusted with higher-level responsibilities due to the proven depth of their experience. This includes roles in security architecture, governance, risk management, and executive-level decision-making.
Final Conclusion
At this stage, CISSP experience is no longer just a qualification requirement but a reflection of professional identity. It demonstrates a career built on consistent engagement with security principles and practical implementation of protective strategies. The process ensures that certified professionals are not only knowledgeable but also experienced in applying that knowledge effectively in real environments.
The completion of this validation marks the transition from candidate to certified professional, representing both achievement and responsibility within the global cybersecurity community.