Kerberos plays a central role in securing authentication processes within modern directory-based infrastructures, particularly those built on Windows-based identity management systems. Its primary objective is to ensure that users can prove their identity in a secure manner without exposing sensitive credentials such as passwords across the network. This becomes critically important in environments where authentication requests frequently travel between multiple systems, services, and endpoints. Without a secure protocol in place, these interactions could be intercepted, manipulated, or exploited by malicious actors. Kerberos addresses this challenge by introducing a ticket-based authentication mechanism that eliminates the need to repeatedly transmit passwords, thereby significantly reducing the attack surface.
The importance of Kerberos becomes more evident when considering how authentication traditionally worked in earlier systems. In older methods, credentials were often transmitted directly over the network, sometimes even in plaintext. Even when encrypted, repeated transmission of credentials increased the risk of interception and replay attacks. Kerberos changes this model entirely by relying on encrypted tickets that validate identity without exposing secrets. This design not only enhances security but also improves efficiency by allowing users to authenticate once and then access multiple services without needing to re-enter credentials. This concept is widely recognized as single sign-on, and it is one of the key advantages of Kerberos-based systems.
Another crucial aspect of Kerberos is its reliance on time-sensitive data. Each authentication request includes timestamps, which help prevent replay attacks where an attacker might attempt to reuse captured authentication data. Because tickets are only valid for a limited period, any attempt to reuse them outside that window will fail. This time-based validation adds an additional layer of protection, ensuring that even if data is intercepted, it cannot be reused indefinitely. However, this also means that time synchronization across systems is essential for Kerberos to function correctly.
In enterprise environments, where multiple users and services interact constantly, Kerberos provides a scalable and efficient solution for managing authentication. Instead of each service independently verifying user credentials, a centralized authority handles authentication and issues tickets that can be trusted across the network. This reduces redundancy and simplifies the overall security architecture. It also allows administrators to enforce consistent policies and controls, ensuring that access to resources is managed in a structured and secure way.
Why Secure Authentication Matters in Modern Networks
Modern networks are inherently complex and often extend beyond a single physical location. Users may connect from different devices, remote locations, or even external networks, all of which introduce potential security risks. In such an environment, the concept of a “trusted network” becomes less reliable. Even internal networks can be compromised, making it essential to treat all communication as potentially vulnerable. This is where secure authentication protocols like Kerberos become indispensable.
Authentication is not just about verifying identity; it is also about ensuring that access to resources is granted appropriately. Without strong authentication mechanisms, unauthorized users could gain access to sensitive data, leading to data breaches, financial loss, or reputational damage. Kerberos mitigates these risks by enforcing strict authentication procedures and ensuring that only verified users can obtain access tickets. These tickets act as proof of identity and authorization, allowing systems to trust the user without repeatedly checking credentials.
Another challenge in modern networks is the need for efficient access management. Users often require access to multiple services, applications, and resources throughout their workday. Constantly prompting users for credentials would not only be inefficient but also frustrating. Kerberos solves this problem by enabling seamless access through its ticketing system. Once a user is authenticated, they can access various services without needing to re-authenticate each time. This improves user experience while maintaining a high level of security.
The protocol also supports auditing and accountability. Since all authentication requests pass through a centralized system, it becomes easier to track who accessed what resources and when. This is particularly important for compliance and security monitoring. In the event of suspicious activity, administrators can analyze authentication logs to identify potential threats and take appropriate action. This level of visibility is essential for maintaining a secure and well-managed network environment.
Core Components Involved in Kerberos Authentication
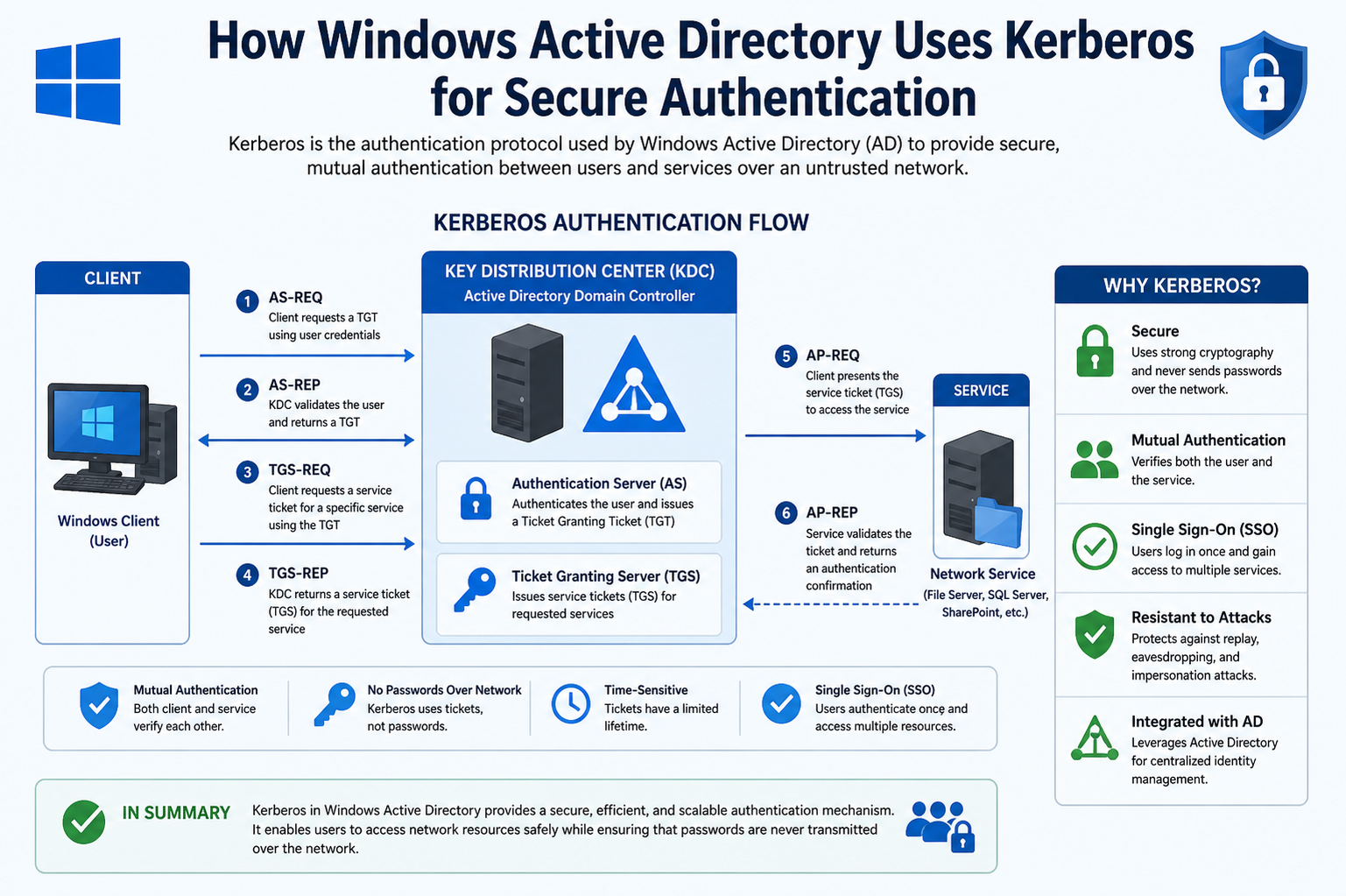
To understand how Kerberos operates, it is essential to become familiar with the key components involved in the authentication process. At a high level, there are three primary entities that participate in every Kerberos transaction: the client, the service, and the authentication authority. Each of these components plays a distinct role in ensuring that authentication is both secure and efficient.
The client represents the user or device that is attempting to access a resource. This could be a workstation, a mobile device, or any system that requires authentication. The client is responsible for initiating the authentication process and interacting with the central authority to obtain the necessary tickets. Unlike traditional systems where the server handles most of the authentication workload, Kerberos shifts a significant portion of this responsibility to the client. This distributed approach helps reduce the burden on centralized systems and improves overall performance.
The service, on the other hand, is the resource that the client ցանկանում access. This could be a file server, an application, or any network service that requires authentication. The service relies on Kerberos tickets to verify the identity of the client. Instead of directly handling credentials, the service trusts the tickets issued by the authentication authority. This trust relationship is a fundamental aspect of Kerberos and allows for secure communication between clients and services.
The authentication authority, often referred to as the Key Distribution Center, acts as the central hub for all authentication activities. It is responsible for verifying user identities and issuing tickets that grant access to services. The Key Distribution Center itself consists of two logical parts: one that handles initial authentication and another that issues service-specific tickets. This separation of responsibilities helps streamline the authentication process and ensures that each step is handled efficiently.
One of the most important features of this architecture is the use of shared secrets. Both the client and the service have their own secret keys, which are known to the authentication authority. These keys are used to encrypt and decrypt tickets, ensuring that only authorized parties can access the information contained within them. This encryption-based approach is what allows Kerberos to provide strong security without transmitting sensitive data in plaintext.
The Initial Authentication Process and Ticket Issuance
The authentication process in Kerberos begins when a user logs into their system. At this point, the client needs to prove its identity to the authentication authority. Instead of sending the user’s password directly over the network, the client uses it to generate a cryptographic key. This key is then used to encrypt certain information, which is sent to the authentication authority as part of the authentication request.
Upon receiving the request, the authentication authority verifies the user’s identity by decrypting the information using its own copy of the user’s secret key. If the decryption is successful, it confirms that the client possesses the correct credentials. At this stage, the authentication authority does not grant direct access to any services. Instead, it issues a special ticket known as a ticket-granting ticket. This ticket serves as proof that the user has been authenticated and can request access to other services without needing to re-enter credentials.
The ticket-granting ticket is encrypted in such a way that only the authentication authority can read it. The client stores this ticket securely in memory and uses it whenever it needs to request access to a service. Along with the ticket, the client also receives a session key, which is used to encrypt subsequent communications with the authentication authority. This ensures that all interactions remain secure and protected from interception.
When the client wants to access a specific service, it presents the ticket-granting ticket to the authentication authority and requests a service ticket. The authentication authority verifies the ticket and, if valid, issues a new ticket specifically for the requested service. This service ticket is then used by the client to authenticate itself to the service.
This multi-step process may seem complex at first, but it is designed to maximize security while minimizing the need for repeated authentication. By separating the initial authentication from service access, Kerberos ensures that user credentials are only used once and are never exposed unnecessarily. This approach not only enhances security but also improves efficiency, making it well-suited for large-scale network environments.
Service Ticket Requests and Secure Access to Resources
Once the client has successfully obtained the ticket-granting ticket, the authentication process moves into a more dynamic phase where access to individual services is requested. At this stage, the user has already proven their identity, so there is no need to resend credentials such as a password. Instead, the client leverages the previously issued ticket to request authorization for specific resources. This is a critical distinction in how Kerberos operates, as it separates identity verification from service authorization, making the entire process more secure and efficient.
When the client needs to access a particular service, it sends a request to the authentication authority that includes the ticket-granting ticket along with an authenticator. The authenticator is a small piece of data that contains identifying details such as the client’s identity and a timestamp. This information is encrypted using the session key that was issued alongside the ticket-granting ticket. The purpose of the authenticator is to prove that the request is fresh and originates from the legitimate client, not from someone attempting to reuse captured data.
The authentication authority validates the ticket-granting ticket and decrypts the authenticator. If both are valid and consistent, it proceeds to generate a service ticket. This service ticket is specifically tailored for the requested resource and includes details such as the client’s identity, authorization data, and a new session key that will be shared between the client and the service. The service ticket is encrypted using the secret key of the target service, ensuring that only the intended service can decrypt and interpret it.
After receiving the service ticket, the client stores it temporarily and prepares to communicate with the target service. This design ensures that the client does not need to repeatedly contact the authentication authority for every interaction with the same service. Instead, the service ticket can be reused for multiple requests within its validity period, reducing overhead and improving performance. This reuse capability is one of the reasons why Kerberos scales effectively in large environments with many users and services.
Mutual Authentication and Trust Establishment
A defining feature of Kerberos is its ability to perform mutual authentication. Unlike simpler authentication mechanisms where only the client proves its identity to the server, Kerberos ensures that both parties verify each other. This is particularly important in preventing scenarios where a user might unknowingly connect to a malicious or impersonated service. By requiring both sides to authenticate, Kerberos establishes a trusted communication channel before any sensitive data is exchanged.
When the client sends the service ticket to the target service, it also includes a new authenticator encrypted with the session key shared between them. The service decrypts the ticket using its own secret key and extracts the session key. It then uses this session key to decrypt the authenticator and verify the client’s identity and the timestamp. If everything checks out, the service can be confident that the request is legitimate.
To complete the mutual authentication process, the service responds to the client with a message that proves its own identity. This message is typically derived from the timestamp in the client’s authenticator and encrypted using the shared session key. When the client successfully decrypts and verifies this response, it confirms that the service is genuine. At this point, both the client and the service trust each other, and a secure session is established.
This mutual verification process is essential in environments where security threats are constantly evolving. It protects against man-in-the-middle attacks, where an attacker might attempt to intercept or alter communication between the client and the service. By ensuring that both parties are authenticated, Kerberos significantly reduces the risk of such attacks and provides a robust foundation for secure communication.
Session Keys and Secure Communication Channels
Once authentication is complete, the client and the service use the shared session key to secure their ongoing communication. This session key is unique to the interaction and is valid only for a limited time. It is used to encrypt and decrypt messages exchanged between the client and the service, ensuring confidentiality and integrity. Even if an attacker were able to intercept the communication, they would not be able to understand or modify it without access to the session key.
The use of session keys also enhances performance by avoiding the need for repeated encryption and decryption using long-term keys. Instead of relying on permanent secrets, Kerberos generates temporary keys that are used only for the duration of a session. This approach reduces the risk associated with key compromise, as the impact of any single key being exposed is limited in scope and duration.
Another advantage of session keys is their role in maintaining data integrity. In addition to encrypting messages, they can be used to generate cryptographic checksums that verify the authenticity of the data. This ensures that messages have not been altered during transmission. If any tampering is detected, the communication can be terminated immediately, preventing further compromise.
This secure communication model is particularly valuable in environments where sensitive data is transmitted regularly. Whether accessing files, running applications, or interacting with network services, the assurance that data remains protected throughout the session is a fundamental requirement. Kerberos achieves this by combining strong encryption with efficient key management practices.
Ticket Lifetimes, Renewal, and Expiration Handling
Tickets in Kerberos are not valid indefinitely. Each ticket is issued with a specific lifetime, after which it expires and can no longer be used. This limitation is a deliberate security measure designed to reduce the risk of ticket misuse. If a ticket were to be intercepted or stolen, its usefulness would be limited to a short time window, minimizing potential damage.
The lifetime of a ticket is determined by policy settings and can vary depending on the environment. Shorter lifetimes provide greater security but may require more frequent re-authentication, while longer lifetimes improve usability at the cost of increased risk. Striking the right balance is essential for maintaining both security and user convenience.
In addition to expiration, Kerberos also supports ticket renewal. If a user’s session is still active and valid, the client can request a renewal of the ticket without requiring the user to re-enter credentials. This is particularly useful in scenarios where users need to maintain long-running sessions, such as when working with complex applications or performing administrative tasks. The renewal process involves presenting the existing ticket along with proof of identity, allowing the authentication authority to issue a new ticket with an extended lifetime.
Another important concept is the distinction between renewable and non-renewable tickets. Renewable tickets can be extended within a certain timeframe, while non-renewable tickets must be replaced entirely once they expire. This distinction allows administrators to implement flexible policies that align with organizational security requirements.
Proper handling of ticket expiration and renewal is critical for maintaining a seamless user experience. If tickets expire unexpectedly, users may be prompted to re-authenticate, which can disrupt workflows. On the other hand, overly long ticket lifetimes can increase security risks. By carefully managing these parameters, organizations can ensure that Kerberos continues to provide both security and usability in a balanced manner.
Delegation and Access Across Multiple Services
In complex environments, users rarely interact with a single service in isolation. Instead, workflows often involve multiple interconnected services that must act on behalf of the user. Kerberos addresses this requirement through a concept known as delegation, which allows a service to request access to another service while preserving the user’s identity. This capability is essential for multi-tier applications, where a front-end service may need to communicate with a back-end database or another system to fulfill a user request.
Delegation works by allowing a service to obtain a service ticket to another resource on behalf of the user. Rather than prompting the user to authenticate again, the service uses the existing Kerberos tickets to request additional access. This process is carefully controlled to prevent abuse, as unrestricted delegation could allow a compromised service to impersonate users across the network. For this reason, delegation is typically governed by strict policies that define which services are allowed to delegate credentials and under what conditions.
There are different forms of delegation, each designed to meet specific security and operational requirements. Some approaches allow full delegation, where a service can act entirely on behalf of the user, while others restrict delegation to specific services or scenarios. These controlled methods ensure that even in complex workflows, user credentials remain protected and are only used in authorized contexts.
Delegation significantly enhances the usability of distributed systems. Without it, users would need to repeatedly authenticate as their requests move between services, leading to inefficiency and frustration. By enabling secure delegation, Kerberos ensures that authentication remains seamless while maintaining strict security controls. This balance between usability and security is one of the reasons why Kerberos remains a preferred choice in enterprise environments.
Inter-Realm Authentication and Cross-Environment Trust
As organizations grow, they often need to integrate multiple identity environments or domains. Kerberos supports this through inter-realm authentication, which allows users from one environment to access resources in another. This is achieved by establishing trust relationships between different authentication authorities, enabling them to recognize and validate each other’s tickets.
In this model, when a user attempts to access a resource in a different environment, their local authentication authority issues a special ticket that can be trusted by the remote system. This ticket is then exchanged for a service ticket within the target environment. The process may involve multiple steps, especially if there are several intermediate trust relationships, but the underlying principle remains the same: each system trusts the authentication decisions of the others based on pre-established agreements.
This capability is particularly valuable in large organizations, mergers, or partnerships where resources need to be shared across boundaries. It allows for a unified authentication experience without requiring all users and services to exist within a single centralized system. At the same time, it maintains strong security by ensuring that all authentication requests are validated through trusted channels.
However, inter-realm authentication also introduces additional complexity. Trust relationships must be carefully configured and maintained, and any misconfiguration can lead to authentication failures or security vulnerabilities. Proper planning and management are essential to ensure that cross-environment access remains both secure and reliable.
Time Synchronization and Its Critical Role in Kerberos
One of the less obvious but critically important aspects of Kerberos is its dependence on accurate timekeeping. Every ticket and authenticator includes timestamps that are used to verify the freshness of authentication requests. If the time difference between systems exceeds an acceptable threshold, authentication attempts may fail. This requirement ensures that replay attacks are effectively mitigated, as outdated authentication data will be rejected.
To maintain synchronization, all systems participating in Kerberos authentication must rely on a consistent time source. This is typically achieved through network time synchronization mechanisms that ensure clocks remain aligned across the environment. Even small discrepancies can cause issues, making it essential to monitor and maintain accurate time settings.
The reliance on time introduces both benefits and challenges. On one hand, it provides a powerful defense against replay attacks by ensuring that authentication data cannot be reused outside its valid timeframe. On the other hand, it requires careful management of system clocks to prevent unintended authentication failures. Administrators must ensure that all systems are properly synchronized and that any deviations are quickly corrected.
In practice, time synchronization is often one of the first areas to check when troubleshooting Kerberos-related issues. If authentication requests are being rejected unexpectedly, a mismatch in system time is a common cause. Understanding this dependency helps administrators quickly identify and resolve such problems, ensuring that the authentication process remains smooth and reliable.
Common Challenges and Troubleshooting Kerberos Authentication
Despite its robust design, Kerberos can present challenges when issues arise. Because the protocol involves multiple components and steps, identifying the root cause of a problem can sometimes be complex. However, a solid understanding of how Kerberos works makes it much easier to diagnose and resolve these issues effectively.
One common challenge is related to ticket expiration. If a user’s ticket expires while they are still working, they may lose access to services and be required to re-authenticate. While this is a normal part of the security model, it can sometimes be confusing for users. Ensuring that ticket lifetimes are configured appropriately can help minimize disruptions while maintaining security.
Another frequent issue involves service configuration. If a service is not properly registered or configured to work with Kerberos, authentication attempts may fail. This can occur if the service does not have the correct keys or if there is a mismatch between expected and actual configuration settings. Careful attention to service setup and configuration is essential to avoid such problems.
Network-related issues can also impact Kerberos authentication. Since the protocol relies on communication between the client, the authentication authority, and the service, any disruption in network connectivity can lead to failures. Ensuring reliable network infrastructure and proper connectivity is therefore a key requirement for successful Kerberos operation.
Additionally, problems with time synchronization, as discussed earlier, are a common source of authentication errors. Even a small difference in system clocks can cause requests to be rejected. Regular monitoring and maintenance of time synchronization services can help prevent these issues.
Effective troubleshooting often involves examining logs and analyzing the sequence of events during authentication. By understanding each step of the Kerberos process, administrators can pinpoint where things are going wrong and take corrective action. This systematic approach not only resolves issues more quickly but also helps prevent similar problems in the future.
Security Strengths and Design Advantages of Kerberos
Kerberos is widely recognized for its strong security model, which is built on well-established cryptographic principles and a carefully structured authentication process. One of its most significant strengths is that it avoids transmitting passwords across the network. Instead, it relies on encrypted tickets that prove identity without exposing sensitive credentials. This design dramatically reduces the risk of credential theft, especially in environments where network traffic could potentially be intercepted.
Another important advantage is the use of symmetric key cryptography combined with trusted third-party verification. The authentication authority acts as a central point of trust, ensuring that both clients and services can rely on the authenticity of issued tickets. Because each ticket is encrypted using keys known only to the intended parties, unauthorized entities cannot read or modify the contents. This guarantees both confidentiality and integrity throughout the authentication process.
Kerberos also minimizes repeated authentication steps through its ticket-based system. Once a user is authenticated, they can access multiple services without re-entering credentials. This not only improves user experience but also reduces the likelihood of insecure practices, such as writing down passwords or reusing weak credentials. By limiting the exposure of authentication data, Kerberos strengthens overall security posture while maintaining operational efficiency.
Additionally, the protocol incorporates protections against replay attacks through the use of timestamps and short-lived tickets. Each authentication request is time-bound, ensuring that captured data cannot be reused indefinitely. This layered approach to security makes Kerberos resilient against a wide range of attack vectors, from simple interception attempts to more sophisticated intrusion techniques.
Limitations and Practical Considerations in Real Environments
Despite its strengths, Kerberos is not without limitations. One of the primary challenges is its reliance on a centralized authentication authority. If this central component becomes unavailable, authentication across the environment can be disrupted. This makes high availability and redundancy essential for maintaining uninterrupted access to resources. Organizations must ensure that their authentication infrastructure is resilient and capable of handling failures without impacting users.
Another consideration is the dependency on accurate time synchronization. Since Kerberos relies heavily on timestamps, any discrepancy between system clocks can lead to authentication failures. While this requirement enhances security, it also introduces an operational dependency that must be carefully managed. Administrators need to ensure that all systems remain synchronized and that time services are functioning correctly at all times.
Kerberos can also be complex to configure and manage, particularly in large or distributed environments. Proper setup requires careful coordination of keys, policies, and trust relationships. Misconfigurations can lead to authentication issues or even security vulnerabilities. As a result, administrators must have a solid understanding of the protocol and its components to ensure successful implementation.
Another limitation involves compatibility with certain legacy systems or applications that may not fully support Kerberos. In such cases, alternative authentication methods may need to be used, which can introduce inconsistencies in security. Integrating these systems while maintaining a strong security posture requires careful planning and, in some cases, additional tools or configurations.
Best Practices for Managing Kerberos Authentication Effectively
To maximize the benefits of Kerberos, organizations should follow best practices that enhance both security and reliability. One of the most important practices is maintaining accurate and consistent time synchronization across all systems. This ensures that authentication requests are processed correctly and reduces the likelihood of errors related to timestamp validation.
Another key practice is implementing strong password policies. Although Kerberos does not transmit passwords directly, the strength of user credentials still plays a crucial role in overall security. Weak passwords can be exploited through offline attacks, so enforcing complexity and regular updates is essential.
Monitoring and logging are also critical components of effective Kerberos management. By analyzing authentication logs, administrators can detect unusual activity and respond to potential threats بسرعة. This proactive approach helps identify issues before they escalate and ensures that the environment remains secure.
Regular maintenance of the authentication infrastructure is equally important. This includes updating systems, rotating keys when necessary, and reviewing configuration settings to ensure they align with current security requirements. Keeping the environment up to date reduces the risk of vulnerabilities and ensures that Kerberos continues to function as intended.
Organizations should also carefully manage delegation settings and trust relationships. Limiting delegation to only what is necessary reduces the risk of misuse, while properly configured trust relationships ensure secure communication between different environments. These controls help maintain a balance between flexibility and security.
Encryption Types and Cryptographic Foundations in Kerberos
A deeper understanding of Kerberos requires looking at the cryptographic mechanisms that power its authentication model. At its core, Kerberos relies on symmetric encryption, where the same key is used for both encryption and decryption. This approach is efficient and well-suited for environments where performance and scalability are important. Each entity involved in the authentication process—whether a client, service, or authentication authority—possesses secret keys that are used to secure communication and validate identity.
When a user logs in, their password is transformed into a cryptographic key through a one-way function. This derived key becomes the foundation for securing the initial authentication exchange. Because the password itself is never transmitted, the risk of exposure is minimized. Instead, encrypted data is exchanged, and only parties with the correct keys can interpret it. This ensures that even if network traffic is intercepted, it cannot be easily decrypted or misused.
Kerberos supports multiple encryption types to accommodate different security requirements and system capabilities. Over time, stronger algorithms have replaced older ones to address evolving threats. Modern implementations favor robust encryption standards that provide higher levels of protection against brute-force attacks and cryptographic weaknesses. Maintaining up-to-date encryption types is essential, as outdated algorithms can introduce vulnerabilities that undermine the security of the entire authentication process.
Another important concept is the separation between long-term keys and session keys. Long-term keys are derived from user credentials or service secrets and are used sparingly, primarily during initial authentication. Session keys, on the other hand, are temporary and generated for specific interactions. By limiting the use of long-term keys and relying on short-lived session keys for ongoing communication, Kerberos reduces the potential impact of key compromise. This layered approach strengthens the overall security model while maintaining efficiency.
Ticket Structure and Internal Data Components
Kerberos tickets are more than simple access tokens; they are carefully structured data objects that contain multiple pieces of information required for secure authentication. Each ticket includes details such as the client’s identity, the target service, validity timestamps, and a session key. This information is packaged and encrypted to ensure that it remains confidential and tamper-proof.
The ticket-granting ticket and service tickets share a similar structure but serve different purposes. The ticket-granting ticket is used to request additional tickets, while service tickets are used to access specific resources. Both types of tickets include validity periods that define when they can be used, reinforcing the time-based security model that Kerberos يعتمد عليه.
One of the key elements within a ticket is the session key. This key is shared between the client and the service and is used to secure their communication. Because the session key is embedded within the ticket and encrypted using the service’s secret key, only the intended service can retrieve it. This ensures that even if a ticket is intercepted, it cannot be used without access to the corresponding secret key.
Tickets also include flags and attributes that define their behavior. For example, certain flags may indicate whether a ticket can be renewed, forwarded, or used for delegation. These attributes provide flexibility in how tickets are used while maintaining strict control over their capabilities. Understanding these internal components helps clarify how Kerberos enforces security policies at a granular level.
Kerberos Caching and Memory Handling on the Client Side
Once tickets are issued, they must be stored securely on the client system for future use. Kerberos achieves this through a specialized memory area often referred to as the credential cache. This cache holds the ticket-granting ticket, service tickets, and associated session keys, allowing the client to reuse them without needing to repeat the authentication process.
The use of a credential cache significantly improves performance and user experience. Instead of contacting the authentication authority for every request, the client can quickly retrieve the necessary ticket from memory and present it to the service. This reduces network traffic and speeds up access to resources, especially in environments where users frequently interact with multiple services.
However, storing authentication data in memory also introduces security considerations. If an attacker gains access to the client system, they may attempt to extract tickets from the cache and use them to impersonate the user. To mitigate this risk, operating systems implement various protections, such as isolating the cache and restricting access to authorized processes only. These safeguards help ensure that cached tickets remain secure.
The lifecycle of cached tickets is closely tied to their validity period. Expired tickets are automatically removed or ignored, and new tickets must be requested when needed. This automatic management helps maintain a balance between usability and security, ensuring that users can work efficiently without compromising protection. Proper handling of the credential cache is an essential aspect of maintaining a secure Kerberos environment.
Performance Considerations and Scalability in Large Environments
Kerberos is designed to operate efficiently even in large-scale environments with thousands of users and services. Its ticket-based approach reduces the need for repeated authentication, which in turn lowers the load on central authentication systems. By distributing much of the processing workload to clients, Kerberos avoids becoming a bottleneck and can scale effectively as the environment grows.
One of the factors that contribute to its scalability is the reuse of tickets. Once a ticket is issued, it can be used multiple times within its validity period, minimizing the number of requests sent to the authentication authority. This reduces network congestion and improves overall system performance. In high-demand environments, this efficiency is critical for maintaining responsiveness and reliability.
Another important consideration is the placement and capacity of authentication infrastructure. Since the authentication authority plays a central role, it must be capable of handling a large volume of requests without delays. This often involves deploying multiple servers and balancing the load between them. Proper planning ensures that authentication services remain available even during peak usage or unexpected spikes in demand.
Caching mechanisms, both on the client and service sides, further enhance performance. By storing frequently used data, these mechanisms reduce the need for repeated computations and network communication. Combined with efficient encryption algorithms, this allows Kerberos to deliver strong security without sacrificing speed.
Scalability also depends on careful configuration and monitoring. Administrators must regularly assess system performance, identify potential bottlenecks, and make adjustments as needed. By optimizing ticket lifetimes, managing resources effectively, and maintaining a robust infrastructure, organizations can ensure that Kerberos continues to perform reliably as their environment evolves.
Final Thoughts
Developing a clear understanding of how Kerberos works provides valuable insight into the broader authentication process within directory-based environments. By visualizing the flow of tickets, the role of the authentication authority, and the interactions between clients and services, it becomes much easier to diagnose issues and maintain a secure infrastructure.
Kerberos may appear complex at first glance, but its design is built around straightforward principles: verify identity securely, minimize exposure of sensitive data, and enable efficient access to resources. When these principles are understood, the protocol becomes far more approachable and practical to work with.
In real-world scenarios, this understanding translates directly into improved troubleshooting and system management. Administrators who grasp the fundamentals of Kerberos can quickly identify where authentication is failing and take targeted action to resolve the issue. This not only reduces downtime but also enhances the overall reliability of the environment.
Ultimately, Kerberos remains a cornerstone of secure authentication in modern network infrastructures. Its combination of strong encryption, centralized trust, and efficient ticketing makes it a powerful tool for protecting access to resources while maintaining a seamless user experience. By applying best practices and maintaining a solid understanding of its operation, organizations can fully leverage its capabilities to build secure and resilient systems.